Cloud-first did not break data governance. Implicit trust did.
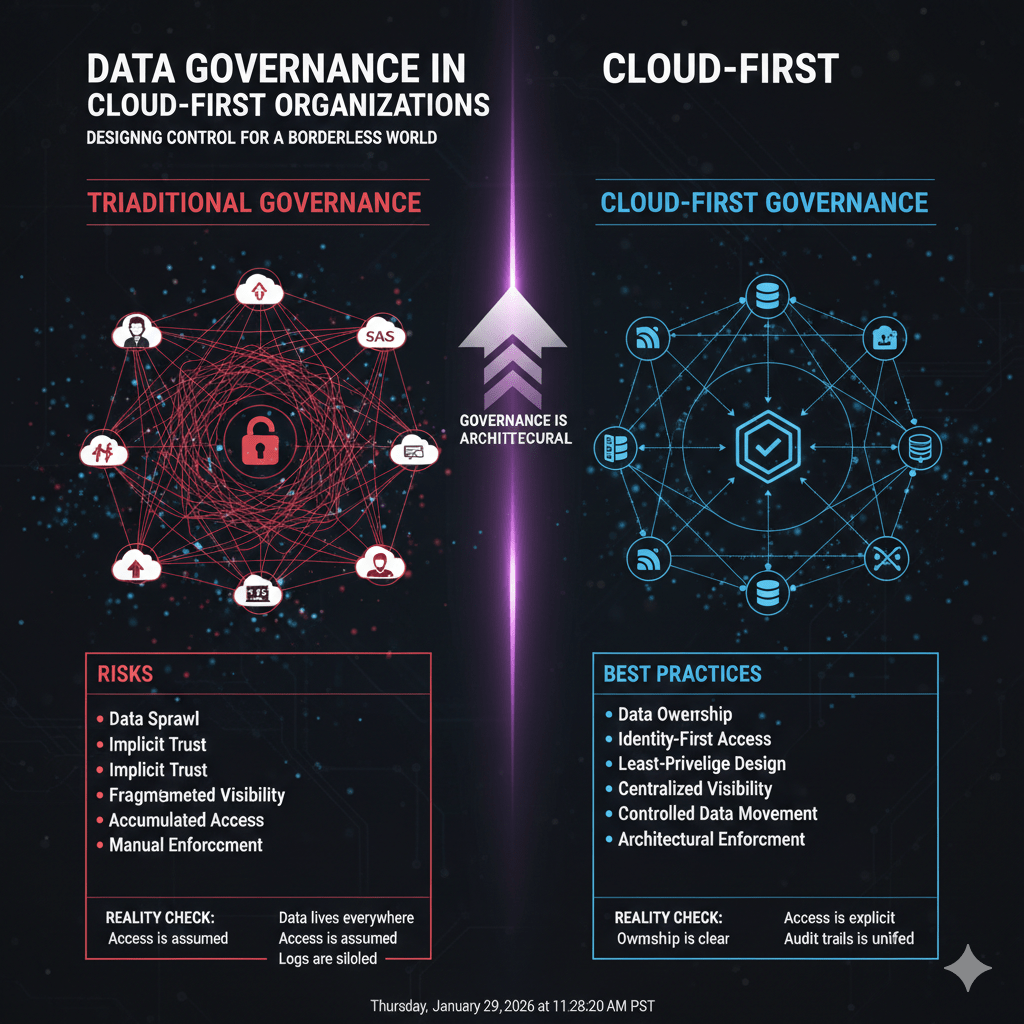
Most organizations moved workloads to SaaS, IaaS, and PaaS faster than they redesigned how data should be governed. The result is predictable: sensitive data scattered across platforms, inconsistent access controls, and compliance teams chasing visibility after the fact.
At Mindcore Technologies, cloud security and governance assessments consistently reveal the same issue. Data exists everywhere, but ownership, access boundaries, and accountability do not.
Effective data governance in cloud-first environments requires architectural discipline, not more policy documents.
Why Traditional Data Governance Fails in the Cloud
Legacy governance models were built for centralized systems.
They break down in cloud-first environments because:
- Data no longer lives in one place
Information spans SaaS platforms, cloud storage, collaboration tools, analytics systems, and third-party integrations. - Access is identity-based, not network-based
Users authenticate directly to applications, often bypassing traditional perimeter controls. - Shadow IT grows faster than governance
Teams spin up tools and integrations without security or compliance review. - Permissions accumulate and rarely shrink
Roles change, projects end, but access often remains.
Cloud-first governance fails when it assumes visibility and control still exist by default.
The Real Risk: Overexposed Data, Not Lost Data
Most governance failures are not caused by breaches.
They are caused by:
- Excessive access to sensitive data
Users can see more data than their role requires. - Untracked data movement
Files are copied, synced, and shared across platforms without clear ownership. - Inconsistent classification and labeling
Sensitive data is treated the same as low-risk information. - Limited auditability across systems
Logs exist, but they are fragmented and hard to correlate.
Governance fails quietly long before an incident occurs.
Best Practice 1: Establish Clear Data Ownership
Data governance collapses without accountability.
Cloud-first organizations must:
- Assign data owners by business function
Owners are responsible for access decisions, classification, and lifecycle management. - Define stewardship responsibilities clearly
Stewards manage day-to-day data handling, not just policy enforcement. - Tie ownership to systems, not departments
Governance follows the data, even as teams change.
Ownership creates enforceable decision-making authority.
Best Practice 2: Classify Data Based on Risk, Not Location
Cloud platforms blur physical boundaries.
Effective governance focuses on sensitivity:
- Define clear data classification tiers
For example: public, internal, confidential, regulated. - Apply classification consistently across platforms
SaaS, file storage, analytics, and backups must follow the same rules. - Align controls with classification level
Higher sensitivity requires stronger access restrictions and monitoring.
Classification drives meaningful control.
Best Practice 3: Enforce Least-Privilege Access by Design
Cloud access is easy to grant and hard to revoke.
Strong governance requires:
- Role-based access aligned to job functions
Access reflects real responsibilities, not convenience. - Regular access reviews tied to data sensitivity
High-risk data requires more frequent review cycles. - Automated deprovisioning when roles change
Access removal should not rely on manual follow-up. - Application-level access instead of broad permissions
Users access what they need, nothing more.
Least privilege limits blast radius when credentials are compromised.
Best Practice 4: Centralize Visibility Across Cloud Platforms
Governance fails when visibility is fragmented.
Cloud-first organizations should:
- Aggregate access and activity logs centrally
Governance depends on understanding how data is used. - Monitor data access patterns, not just login events
Who accessed what data matters more than when they logged in. - Correlate activity across SaaS and cloud services
Isolated logs hide misuse and policy drift.
Visibility turns governance from theory into practice.
Best Practice 5: Control Data Movement, Not Just Storage
Data governance must follow data in motion.
Effective controls include:
- Restrictions on downloads and local storage
Sensitive data should not freely reach endpoints. - Monitoring sharing and external access
Third-party access requires explicit approval and review. - Limiting API and integration permissions
Integrations often have broader access than users. - Auditing exports and bulk data access
Large transfers should be visible and justified.
Data movement is where governance most often fails.
Best Practice 6: Design Governance for Cloud Reality
Governance must adapt to how cloud environments operate.
This means:
- Identity-first governance models
Policies follow users and roles, not networks. - Session-based access enforcement
Long-lived access increases risk unnecessarily. - Application-level controls over network trust
Users interact with data, not infrastructure. - Architectural enforcement instead of policy reliance
Governance should be enforced automatically, not manually.
Design matters more than documentation.
How Secure Workspaces Strengthen Cloud Data Governance
Secure workspace models enhance governance by:
- Containing sensitive data inside controlled environments
Data does not sprawl across unmanaged devices. - Limiting access to approved applications only
Users cannot browse data repositories freely. - Providing clear session-level audit trails
Governance teams gain precise visibility. - Reducing reliance on endpoint trust
Compliance does not depend on perfect devices.
Governance becomes enforceable, not aspirational.
How Mindcore Technologies Helps Cloud-First Organizations Govern Data
Mindcore supports cloud-first data governance by:
- Mapping data flows across cloud platforms
Governance aligns with real usage, not assumptions. - Defining ownership, classification, and access models
Roles and responsibilities are clearly enforced. - Implementing identity-driven access controls
Least privilege is applied consistently. - Reducing data exposure through secure workspace models
Sensitive data stays contained. - Centralizing visibility and audit readiness
Compliance teams gain a single source of truth.
The goal is sustainable governance without slowing the business.
A Simple Cloud Governance Reality Check
Your data governance is weak if:
- Sensitive data lives across tools without clear ownership
- Access reviews are infrequent or manual
- Users can download or share regulated data freely
- Logs exist but are not correlated
- Governance depends on policy reminders
These are structural gaps, not awareness failures.
Final Takeaway
Data governance in cloud-first organizations is no longer about controlling where data lives. It is about controlling who can access it, how it can move, and how that access is verified and recorded.
Organizations that succeed design governance into their architecture. Those that do not spend their time reacting to exposure they never intended to allow.
Frequently Asked Questions
Why is data governance important in cloud-first organizations?
Data governance helps organizations control how sensitive data is accessed, shared, monitored, and protected across cloud platforms. Strong governance reduces data exposure risks, improves compliance readiness, and strengthens operational accountability.
Why do traditional data governance models fail in cloud environments?
Traditional governance models were designed for centralized systems and perimeter-based security. Cloud environments distribute data across multiple platforms, applications, and integrations, making visibility, ownership, and access control more complex.
What is least-privilege access in cloud data governance?
Least-privilege access limits users to only the data and systems necessary for their job responsibilities. This reduces unnecessary exposure and minimizes the impact of compromised credentials or insider misuse.
How can organizations improve visibility across cloud platforms?
Organizations can centralize access logs, monitor data usage patterns, correlate activity across SaaS and cloud services, and track data movement between systems. Centralized visibility improves audit readiness and helps detect governance gaps faster.
Why is controlling data movement important in cloud governance?
Data movement often creates hidden governance risks through downloads, file sharing, integrations, and bulk exports. Monitoring and restricting how sensitive data moves across platforms helps reduce unauthorized exposure and compliance violations.
Cloud Data Governance Expertise from Matt Rosenthal
Matt Rosenthal, CEO of Mindcore Technologies, has extensive experience helping organizations strengthen cloud security, identity governance, and data protection strategies in complex cloud-first environments. His expertise in access control architecture, secure workspace design, compliance readiness, centralized monitoring, and operational risk management helps businesses reduce data exposure and improve governance accountability across SaaS, cloud, and hybrid infrastructures. His leadership focuses on designing governance frameworks that align security controls, visibility, and access management with modern cloud operations.