Telehealth did not weaken healthcare security. Traditional access models did. Virtual care expanded faster than architectures could adapt, leaving PHI exposed through VPNs, unmanaged endpoints, and long-lived sessions that assume trust after login.
That trust is exactly what attackers exploit.
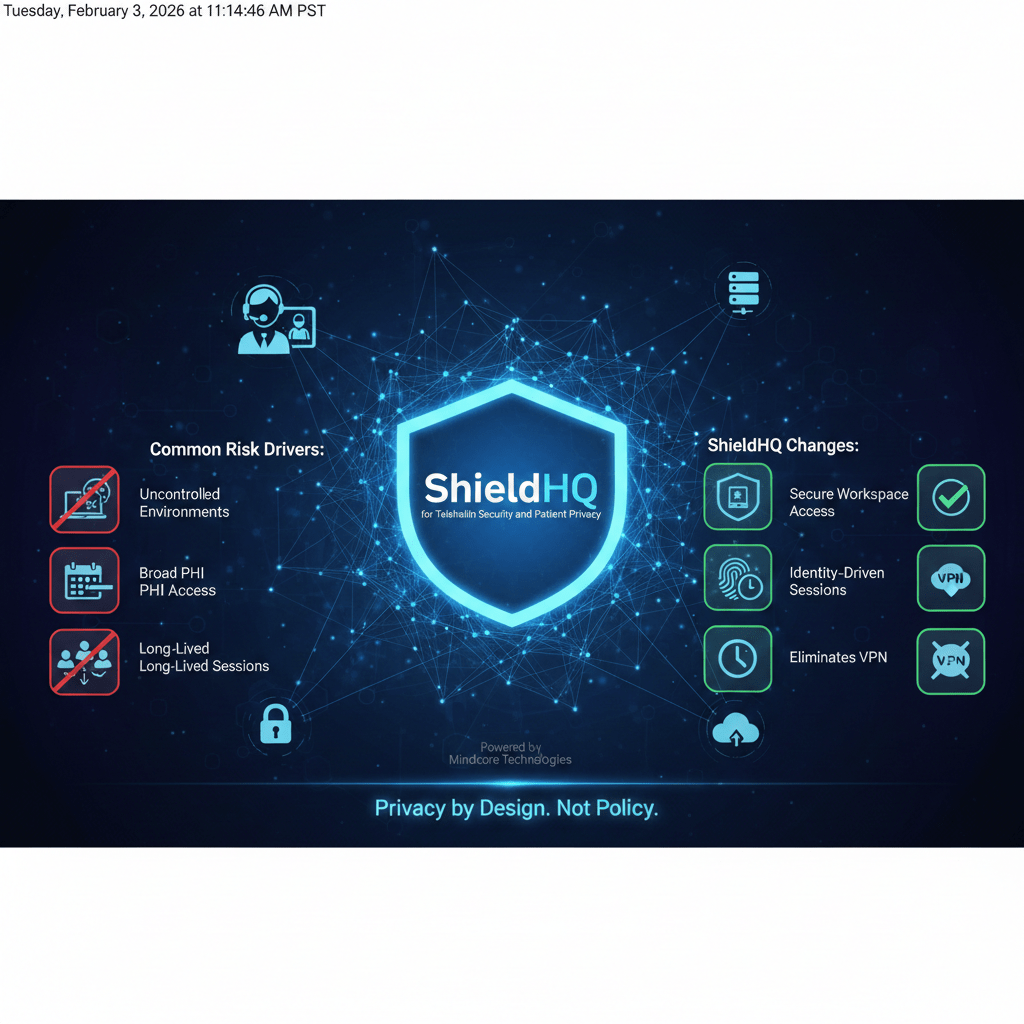
At Mindcore Technologies, telehealth risk assessments show the same pattern: access is legitimate, exposure is unnecessary, and privacy depends on endpoints that cannot be fully controlled. ShieldHQ Powered by Dispersive® Stealth Networking addresses this by redesigning how telehealth access is delivered, verified, and contained.
Why Telehealth Increases Privacy Risk by Default
Telehealth multiplies access paths without shrinking exposure.
Common risk drivers include:
- Care delivered from uncontrolled environments
Clinicians and staff connect from home offices, shared spaces, or mobile networks that IT cannot harden to healthcare standards. - Broad access to PHI across roles
Scheduling, billing, care coordination, and clinical teams all touch telehealth platforms, increasing over-permissioning risk. - Dependence on VPN-based remote access
VPNs extend internal networks to endpoints, exposing systems beyond what telehealth workflows require. - Long-lived sessions during patient care
Sessions often remain active across multiple appointments, increasing the value of stolen access.
Telehealth does not require more trust. It requires tighter containment.
How Telehealth Breaches Actually Happen
Most telehealth-related incidents do not involve platform exploits.
They involve:
- Credential theft via infostealers
Malware harvests saved credentials and active sessions from clinician endpoints. - Phishing and session hijacking
Attackers steal authenticated sessions, bypassing passwords and basic MFA. - Excessive access after login
Once connected, users often retain access to systems unrelated to telehealth care. - Endpoint-based PHI exposure
Data is cached, copied, or synced locally during virtual visits.
From a monitoring perspective, everything appears normal until data is exposed.
What ShieldHQ Changes for Telehealth Security
ShieldHQ secures telehealth by replacing network-based trust with a secure workspace model.
Instead of extending the network outward, ShieldHQ:
- Contains telehealth applications inside a protected workspace
Platforms are accessed without exposing underlying systems. - Delivers access at the application level
Users interact only with approved telehealth and PHI systems, not networks or servers. - Enforces identity-driven, session-based access
Each session is verified, scoped, and continuously evaluated. - Eliminates VPN dependency entirely
Network exposure is removed from the telehealth access path.
This architecture prevents small failures from becoming privacy incidents.
Protecting Patient Privacy Through Workspace Containment
Patient privacy fails when PHI reaches places it should not.
ShieldHQ protects privacy by:
- Keeping PHI inside the secure workspace
Data is not downloaded, cached, or stored on endpoints during virtual visits. - Restricting copy, export, and transfer actions
Data movement is controlled and observable. - Preventing lateral access to unrelated systems
Telehealth access does not expose broader clinical environments. - Allowing instant session termination
Access can be revoked immediately if risk changes mid-session.
Privacy becomes an architectural outcome, not a policy promise.
Zero Trust for Telehealth Without Workflow Disruption
Zero trust often fails in healthcare when it adds friction.
ShieldHQ applies zero trust in a way clinicians can operate:
- Identity-based access instead of network trust
Access decisions are based on verified identity and role, not location. - Per-session verification instead of persistent connections
Sessions expire automatically and cannot be reused broadly. - Application-level isolation
Clinicians access telehealth tools without inheriting system-level access. - Centralized visibility
Security teams gain consistent insight without interrupting care.
Security improves without disrupting patient interactions.
Reducing Ransomware Risk in Telehealth Environments
Telehealth access is frequently used as a foothold for ransomware.
ShieldHQ disrupts this by:
- Blocking access to file systems and servers
Ransomware cannot encrypt what it cannot reach. - Eliminating lateral movement paths
Compromised access is confined to a single workspace session. - Keeping PHI off endpoints
Even infected devices cannot encrypt protected data. - Supporting immediate access revocation
Sessions can be terminated without network changes.
Containment replaces cleanup as the primary defense.
HIPAA Alignment for Virtual Care
HIPAA expects organizations to minimize exposure and prove control, regardless of care delivery method.
ShieldHQ supports this by:
- Enforcing minimum necessary access automatically
Telehealth users see only what their role requires. - Providing application-level audit trails
Logs show which PHI systems were accessed and when. - Reducing endpoint reliance
Compliance does not depend on perfect devices. - Simplifying audit evidence collection
Session and access data is centralized and consistent.
Telehealth compliance becomes sustainable, not stressful.
Why Secure Workspaces Are Better Than “Securing Endpoints”
Endpoint hardening alone cannot protect telehealth privacy because:
- Devices are diverse and frequently unmanaged
- Users move between networks constantly
- Session theft bypasses local controls
ShieldHQ shifts protection away from endpoints and into controlled access environments, where risk is easier to contain.
How Mindcore Technologies Deploys ShieldHQ for Telehealth
Mindcore secures telehealth environments by:
- Mapping virtual care workflows end to end
Access aligns with how care is actually delivered. - Replacing VPN-based telehealth access
Network exposure is removed entirely. - Defining role-based access to telehealth and PHI systems
Permissions align with responsibility. - Enforcing device and session posture checks
Access adapts dynamically to risk. - Providing centralized monitoring and audit readiness
Security, IT, and compliance teams share a single source of truth.
The focus is measurable privacy protection without slowing care delivery.
A Simple Telehealth Privacy Check
Your telehealth environment remains high-risk if:
- VPNs are required for virtual care access
- PHI reaches clinician endpoints
- Sessions persist across multiple visits
- Users can access systems beyond telehealth needs
- Audit evidence is manually reconstructed
These are architectural risks, not training gaps.
Final Takeaway
Telehealth security and patient privacy cannot rely on trust-based access models built for a different era. ShieldHQ Powered by Dispersive® Stealth Networking secures telehealth by containing PHI, eliminating VPN risk, enforcing zero trust access, and reducing exposure by design.
For healthcare organizations delivering virtual care at scale, ShieldHQ is not an add-on. It is the architecture that makes secure, private telehealth possible.