Data governance is not a policy document. It is how your business decides who can access data, how it is used, how it is protected, and how long it exists. When governance is weak, data sprawl grows, access becomes uncontrolled, and breaches become inevitable.
At Mindcore Technologies, most data breaches and compliance failures we investigate do not start with attackers. They start with organizations that lost track of their own data.
This guide explains data governance in practical terms, without theory or fluff.
The Hard Truth About Data Governance
Growing businesses usually believe:
- Governance is for large enterprises
- Tools alone will control data
- Compliance equals governance
- Policies fix behavior
None of that holds up in the real world.
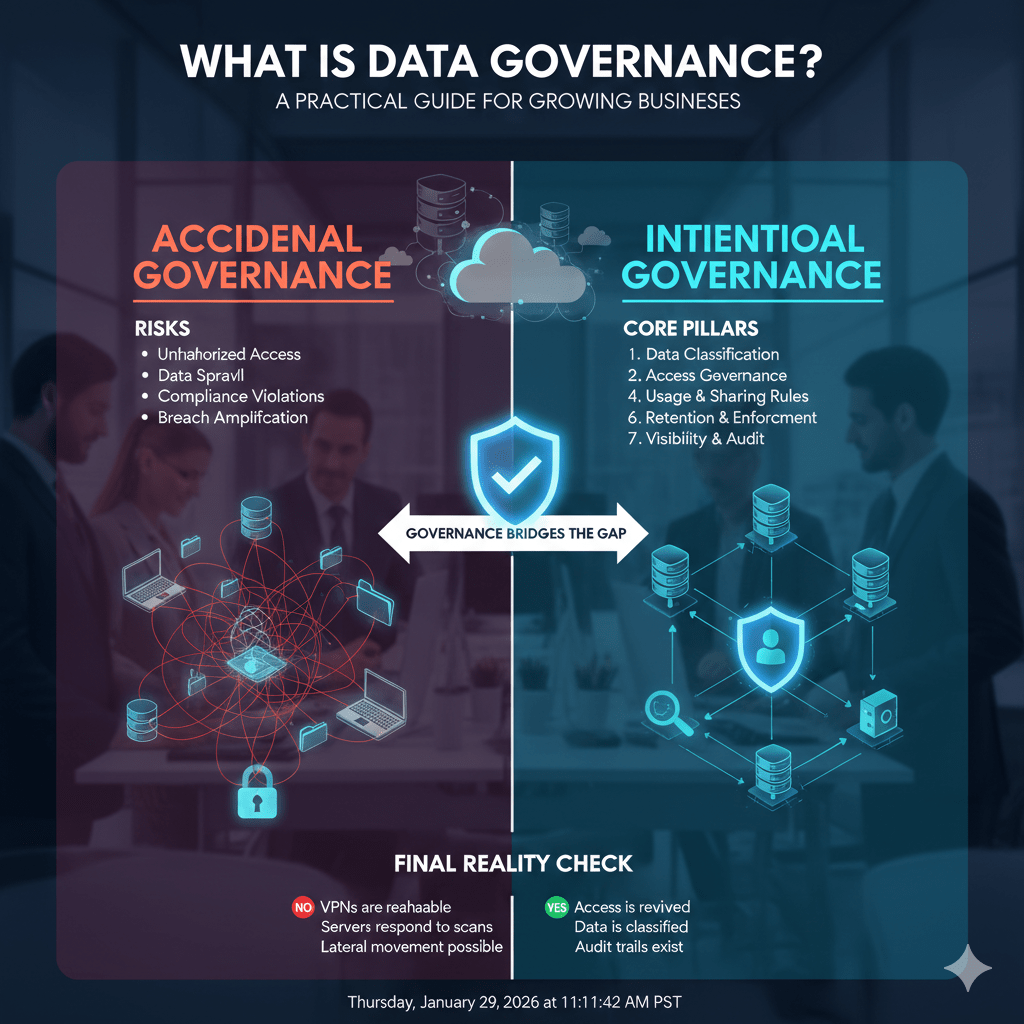
Data governance exists whether you design it or not. The only question is whether it is intentional or accidental.
What Data Governance Actually Means (Plain English)
Data governance is the framework that defines:
- Who owns data
- Who can access it
- How it can be used or shared
- Where it can live
- How long it is retained
- How it is protected and monitored
If you cannot answer those questions consistently, you do not have data governance.
Why Growing Businesses Struggle With Data Governance
Growth introduces risk faster than controls mature.
Common triggers include:
- Rapid cloud adoption
- Multiple SaaS platforms
- Remote and hybrid work
- Shared drives and ad hoc file sharing
- Vendors and integrations multiplying
Without governance, data spreads faster than visibility.
The Real Risks of Poor Data Governance
Weak data governance leads directly to:
- Unauthorized data access
- Accidental data exposure
- Compliance violations
- Breach amplification
- Inability to prove what was accessed
Most “security incidents” are actually governance failures.
Core Pillar 1: Data Ownership
The failure we see:
No one owns the data, so everyone can access it.
What governance requires:
- Assign clear data owners by dataset or system
- Owners approve access and retention
- Owners are accountable for data accuracy and exposure
Ownership creates accountability. Without it, data becomes unmanaged.
Core Pillar 2: Data Classification
The failure we see:
All data is treated the same, so sensitive data is everywhere.
What governance requires:
- Identify sensitive, regulated, and business-critical data
- Classify data based on impact, not convenience
- Apply stronger controls to higher-risk data
You cannot protect what you have not identified.
Core Pillar 3: Access Governance
The failure we see:
Access accumulates and is never removed.
What governance requires:
- Role-based access tied to job function
- Least-privilege by default
- Regular access reviews
- Immediate access removal on role change or exit
Access is the primary breach vector. Governance controls it.
Core Pillar 4: Data Usage and Sharing Rules
The failure we see:
Data is shared informally through links, exports, and personal accounts.
What governance requires:
- Defined rules for internal and external sharing
- Approved sharing mechanisms
- Monitoring of data movement
Uncontrolled sharing bypasses every security tool you deploy.
Core Pillar 5: Data Retention and Disposal
The failure we see:
Data is kept forever “just in case.”
What governance requires:
- Defined retention periods
- Automated or enforced deletion
- Secure disposal of expired data
You cannot breach data that no longer exists.
Core Pillar 6: Security Controls That Enforce Governance
Policies without enforcement fail.
Effective governance uses:
- Identity-based access controls
- Conditional access and device posture checks
- Session controls
- Network segmentation
- Monitoring and logging
Security tools should enforce governance decisions, not replace them.
Core Pillar 7: Visibility and Auditability
The failure we see:
Organizations cannot answer “who accessed what and when.”
What governance requires:
- Centralized logging
- Audit trails for access and sharing
- Regular review of access behavior
If you cannot audit it, you cannot govern it.
Data Governance vs Data Security (Important Distinction)
- Data security protects systems
- Data governance controls data itself
You can have strong security tools and still fail governance. Most breaches occur inside secure systems, through legitimate access that was never governed properly.
What Data Governance Looks Like in Practice
Well-governed environments have:
- Clear data ownership
- Limited and reviewed access
- Defined sharing paths
- Reduced data sprawl
- Faster breach response
- Easier compliance audits
Poorly governed environments rely on trust and luck.
Why Data Governance Becomes Critical as You Scale
As businesses grow:
- Employees change roles frequently
- Vendors gain access
- Data volume multiplies
- Regulatory scrutiny increases
Governance is what keeps growth from becoming chaos.
How Mindcore Technologies Helps Implement Practical Data Governance
Mindcore helps growing businesses implement data governance that works in real environments by:
- Defining data ownership and classification
- Designing identity-based access models
- Enforcing least privilege and access reviews
- Securing cloud and SaaS data flows
- Implementing monitoring and audit visibility
- Aligning governance with compliance requirements
We focus on operational governance, not paperwork.
A Simple Governance Reality Check
You lack effective data governance if:
- No one owns your critical data
- Access is granted “just in case”
- Sharing links are uncontrolled
- Data is retained indefinitely
- You cannot audit access confidently
These conditions are common—and correctable.
Final Takeaway
Data governance is not optional once a business begins to scale. It is the discipline that keeps data controlled, auditable, and defensible as systems, users, and vendors multiply. Without it, even the best security tools fail to prevent exposure.
Organizations that implement practical data governance reduce breach risk, simplify compliance, and gain operational clarity. Those that ignore it usually discover its importance only after data is already exposed.