Ransomware is no longer an IT problem. It is a business survival problem.
In 2026, attackers are not brute-forcing firewalls. They are stealing credentials, exploiting misconfigurations, moving laterally, and encrypting data after quietly exfiltrating it.
Greenville CEOs cannot delegate ransomware awareness entirely to IT. Leadership decisions directly influence exposure, response speed, and financial impact.
At Mindcore Technologies, we see one clear pattern: companies that treat ransomware as a board-level risk recover faster and suffer less damage.
Below are the practical defense principles every Greenville CEO should understand.
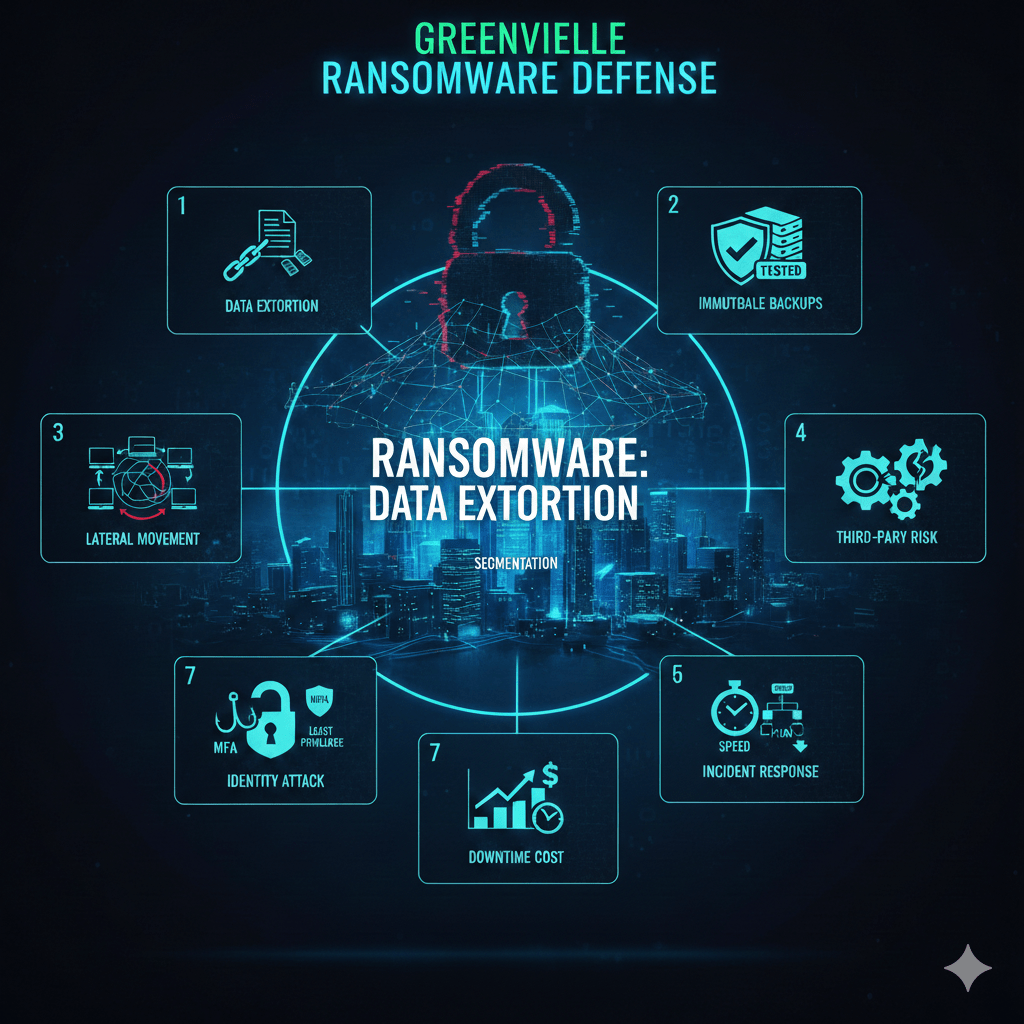
1. Ransomware Is Now Data Extortion, Not Just Encryption
The Reality
- Attackers exfiltrate data before encrypting systems
This creates leverage even if backups exist. - Double extortion tactics are common
Threat actors threaten public data release. - Regulatory consequences compound the impact
Data leaks trigger compliance investigations.
Ransomware now targets reputation as much as operations.
CEO-Level Action
- Require data classification and access control reviews.
- Ensure logging and monitoring are active across critical systems.
- Verify that breach response plans include data exfiltration scenarios.
Backups alone are not sufficient.
2. Identity Is The Primary Attack Vector
The Reality
- Phishing and credential theft dominate initial access
Email compromise often precedes ransomware deployment. - Multi-factor authentication gaps remain common
Password-only systems are easily breached. - Over-permissioned accounts increase blast radius
Compromised admin credentials accelerate lateral movement.
Attackers move through identity, not perimeter.
CEO-Level Action
- Mandate multi-factor authentication across all systems.
- Limit global administrator privileges.
- Enforce least-privilege access models.
Identity governance is non-negotiable.
3. Lateral Movement Is What Turns Incidents Into Crises
The Reality
- Flat networks allow rapid spread
Once inside, attackers move freely. - Unsegmented environments increase exposure
Sensitive systems become reachable. - Unmonitored internal traffic hides attacker movement
Breaches go undetected for days or weeks.
Ransomware damage depends on architecture.
CEO-Level Action
- Require network segmentation between users, servers, and backups.
- Ensure endpoint detection tools are actively monitored.
- Demand visibility into internal network traffic patterns.
Containment must be built into design.
4. Backups Must Be Immutable And Tested
The Reality
- Attackers target backup systems first
If backups are accessible, they are often deleted or encrypted. - Untested backups fail under pressure
Recovery procedures may not work in real conditions. - Cloud backups without immutability are vulnerable
Misconfigured storage increases risk.
Backup strategy determines recovery viability.
CEO-Level Action
- Implement immutable backups that cannot be altered.
- Test restoration procedures quarterly.
- Separate backup credentials from daily admin credentials.
Recovery must be verified, not assumed.
5. Incident Response Speed Determines Business Impact
The Reality
- Delayed detection increases financial loss
The longer attackers remain undetected, the more damage occurs. - Unclear response roles cause confusion
Teams waste time deciding who is responsible. - No executive communication plan worsens reputation damage
Messaging becomes reactive and inconsistent.
Preparedness reduces chaos.
CEO-Level Action
- Establish a documented incident response plan.
- Assign executive-level accountability during cyber events.
- Conduct tabletop exercises annually.
Response discipline protects operational continuity.
6. Third-Party Risk Is Often Overlooked
The Reality
- Vendors can introduce ransomware exposure
Compromised suppliers become entry points. - Shared credentials increase risk
External access often lacks strict governance. - Limited vendor oversight reduces visibility
Organizations assume security without validation.
Supply chain risk is growing.
CEO-Level Action
- Require vendor security assessments.
- Enforce identity-based vendor access controls.
- Review third-party access quarterly.
Shared responsibility must be enforced.
7. Downtime Costs More Than The Ransom Demand
The Reality
- Lost productivity multiplies quickly
Idle teams create cascading operational delays. - Customer trust erodes during service disruption
Reputation damage lingers. - Regulatory reporting increases exposure
Financial and legal consequences escalate.
The ransom is rarely the largest cost.
CEO-Level Action
- Quantify downtime cost per hour.
- Align cybersecurity investment with business risk exposure.
- Treat cybersecurity spending as risk management, not overhead.
Financial clarity improves decision-making.
How Mindcore Technologies Supports Greenville Ransomware Defense
Mindcore helps Greenville organizations strengthen ransomware defense by:
- Conducting ransomware risk assessments to identify architectural gaps.
- Implementing identity-driven access controls and multi-factor authentication.
- Designing segmented network environments to limit lateral movement.
- Deploying advanced endpoint detection and response tools.
- Implementing immutable backup and recovery strategies.
- Developing executive-level incident response frameworks.
Defense requires structured architecture and continuous oversight.
Final Takeaway
Ransomware is no longer a technical inconvenience. It is a strategic business threat that targets identity, architecture, and operational resilience.
Greenville CEOs who prioritize identity governance, segmentation, immutable backups, and incident response planning reduce both the probability and impact of ransomware events.
Cyber resilience begins at the executive level.