Anti Ransomware Resources
Ransomware is the number one cyber security concern for any organization. That’s why we’ve built a library of trusted Ransomware Resources to help businesses, critical infrastructures, and individuals understand cyber risks and stay protected. The impacts of ransomware can range from loss of data and productivity to expensive recovery processes and damage to your company’s reputation.
What is a Ransomware Attack?
Ransomware is a form of malware that employs encryption to hold a victim’s information for ransom. An attacker will usually lock users’ systems or prevent them from accessing files until they pay a ransom. A ransomware infection can paralyze an entire organization if it spreads across a network and targets a company’s databases and file servers.
Even though ransomware has consistently been in the headlines over the past five years, the idea behind it is quite old. The earliest variants of ransomware were developed in the late 1980s when criminals would hold encrypted files hostage in exchange for cash sent via the postal service.
In 1989, the “AIDS Trojan” (PC Cyborg Trojan Virus) was the first ransomware attack in computer history, released via floppy disk. Victims needed to send $189 to a PO Box in Panama to restore access to their systems. Since then, ransomware has become a lucrative criminal business, making Ransomware Resources essential for companies preparing against these attacks.
Types of Ransomware
The first step in preventing a ransomware attack is to understand the different types of ransomware that exist. Historically, the two main types of ransomware are crypto and locker, and there are also ransomware strains that follow under each type. However, in recent years, double extortion and ransomware as a service (RaaS) have become popular threat actors. You can explore additional Ransomware Resources.
Screen Lockers (Locker Ransomware)
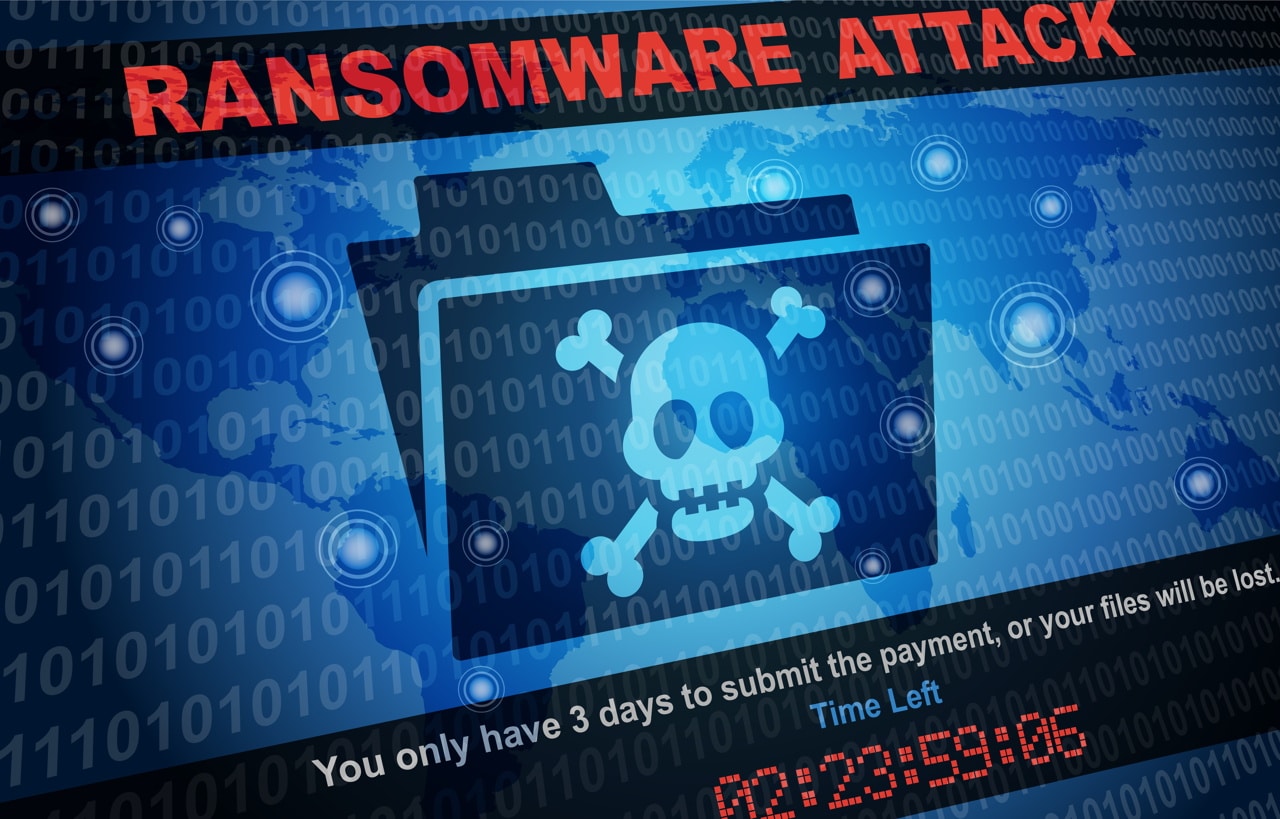
When locker ransomware gets onto your computer, you’re frozen out of your PC entirely. In most cases, the user can only view the lock screen or interact with a screen containing the ransom demand. A pop-up window may appear saying, “Your computer has been infected with a virus. Click here to resolve the issue.” The screen may have a countdown timer designed to scare the victim into paying before they lose all of their files.
Crypto Ransomware
Crypto ransomware is more widespread than locker ransomware. In this attack, the perpetrator encrypts a user’s data so that it is unreadable and then demands a ransom in exchange for a key to decrypt it. Some newer variants also infect shared, networked, and cloud drives. All encrypted data is permanently deleted if the user misses the deadline to pay the ransom.

Scareware
Scareware generally tries to freak a user out by displaying an alarming message and tricking them into downloading malware. It displays a pop-up message, often with the logo of legitimate security software, instructing the user to purchase or install software to resolve the problem. Scareware will urge users to act fast without giving them much time to think or analyze the situation.

Leakware
Leakware, also known as Doxware, occurs when a malicious actor steals data and threatens to release it on public domains. Attackers often carry out data theft and encryption in conjunction with each other. This way, the victim feels increased pressure to pay the ransom. These attacks usually target organizations like banks and other entities that handle confidential or sensitive information.

Ransomware as a Service (RaaS)
RaaS is where threat actors embrace a SaaS-like business model to carry out ransomware attacks. RaaS creators host ransomware on the dark web and allow cybercriminals to purchase it as a subscription. The fees depend on the ransomware’s complexity and features, and there is generally an entry fee. Members of the affiliate return a percentage of the ransom payment to the creator.
How to Identify Ransomware
Ransomware creators will target any size company and even individuals to maximize their profits. That’s why it’s necessary to implement security awareness training for all employees to help them learn how to identify a potential ransomware threat. Below, we’ve outlined the top five signs of ransomware and how to spot them – so your organization doesn’t fall victim to an attack.
When your computer or other devices on your network are running slowly, you may think it’s because there are too many users exhausting bandwidth. However, ransomware works by scanning networks for file storage locations. This process slows down traffic, disrupting your productivity. Any slowdown should be flagged as a cyber security event because it’s a potential indicator of a larger issue.
If you notice any sudden changes to the appearance of files or entire folders in your organization, this may be a sign of ransomware. Common file extensions for routine processes include .pdf, .doc or .docx, and .jpeg. If you come across a file without a common extension, this may be a sign of a cyber attack. Suspicious file changes should be detected and examined as soon as they occur.
Have you noticed several of your company’s files go missing over time? If so, a ransomware attack is likely at play. Malicious actors attempt to move through a network undetected for as long as it takes to remove the critical data they’re seeking to exploit. They might start with fewer or less critical files at first, then move on to bigger targets when it’s safe.
File encryption is performed by an authorized user within your organization and is applied only to files that need encryption for regulatory purposes. Misapplication of encryption can be a sign of ransomware. While managing an encryption program, it’s important to prioritize data and ensure cryptography is applied appropriately. Pay close attention to files with .crypted or .cryptor extensions — if you detect these files, report them immediately.
The most obvious indicator of ransomware is the splash screen message — an explicit message announcing that files critical to your business have been stolen, encrypted, deleted, or otherwise compromised. Usually, this same screen will instruct users to pay a certain amount of money to the attacker(s) to release the files within a short timeframe.
How to Prevent Ransomware
In a ransomware attack, reaction time matters. You must pay attention to the warning signs and take proper action immediately. You should also use appropriate software, such as virus scanners and content filters on your mail servers. In addition, our Ransomware Resources provide best practices that help protect organizations and users from ransomware threats and operational disruption.
Refrain from clicking on links on unknown websites or opening suspicious email attachments. An automatic download could start, and your computer may become infected with ransomware if you click the link. Check that the sender and email address match before you open an email to ensure it is trustworthy. Never open attachments that require you to run macros to view them.
If you receive a phone call, text, or email from an untrusted source requesting personal information, do not respond. Cybercriminals will try to collect information about their target before executing an attack. If you have any doubts about the legitimacy of a message, contact the sender directly for confirmation.
It’s crucial to update your programs and operating system regularly to protect you and your data from malware. Although it may be tempting to ignore those updates, security patches find and fix any vulnerabilities in your programs and systems. As soon as an update is released, download and install it.
Public Wi-Fi networks make it easy for hackers to get into your computer and perform a ransomware attack. Whenever you work remotely at a public library or local coffee shop, you are connected to a public Wi-Fi network. Try to avoid public networks if possible, and if you cannot, use a secure VPN service to protect you from a ransomware infection.
Never download software or media files from unknown websites. Only trust verified sites for downloads, which you can identify in a few ways. Make sure that the address bar of the page you visit uses “HTTPS” instead of “HTTP.” A lock or shield symbol also displays that the page and site are secure.
Ransomware Frequently Asked Questions
The most common type of ransomware is crypto-ransomware or encryptors. This attack locks you out of important files and data on your computer by encrypting them. While you’re still able to see the files stored on your device, you’re unable to access them. To recover the files, perpetrators will demand a ransom payment.
A VPN cannot stop ransomware, but it can make you less vulnerable to an attack. Because a VPN hides your IP address and encrypts your traffic and data, it’s harder for ransomware creators to find and target you. A premium VPN is legal, safe, and highly recommended as part of a larger anti-malware strategy.
Ransomware recovery timeframes can vary greatly depending on the type of ransomware you were infected with, the size of your IT infrastructure, and the experience level and maturity of your IT team. For most companies, the recovery period is between two and four weeks. It’s important to have the right tools and techniques in place to ensure business continuity in the event of an attack.
While every company should evaluate its cyber security risks and regularly update its defenses, a few industry sectors should be especially vigilant in their daily activities. The top five targets for ransomware attacks include health care, higher education, retail stores, small businesses, and finance.
Yes, ransomware can spread through Wi-Fi networks to infect multiple computers and devices. Because users are unable to access their files or applications, this can cause significant disruptions to business operations. In some cases, ransomware can even render entire networks unusable.