Remote access is now permanent in healthcare. What should not be permanent is the risk that comes with VPN-based access. VPNs do not just enable connectivity, they extend trust far beyond what modern healthcare environments can safely support.
Most healthcare breaches tied to remote access do not involve sophisticated exploits. They involve legitimate credentials used exactly as designed.
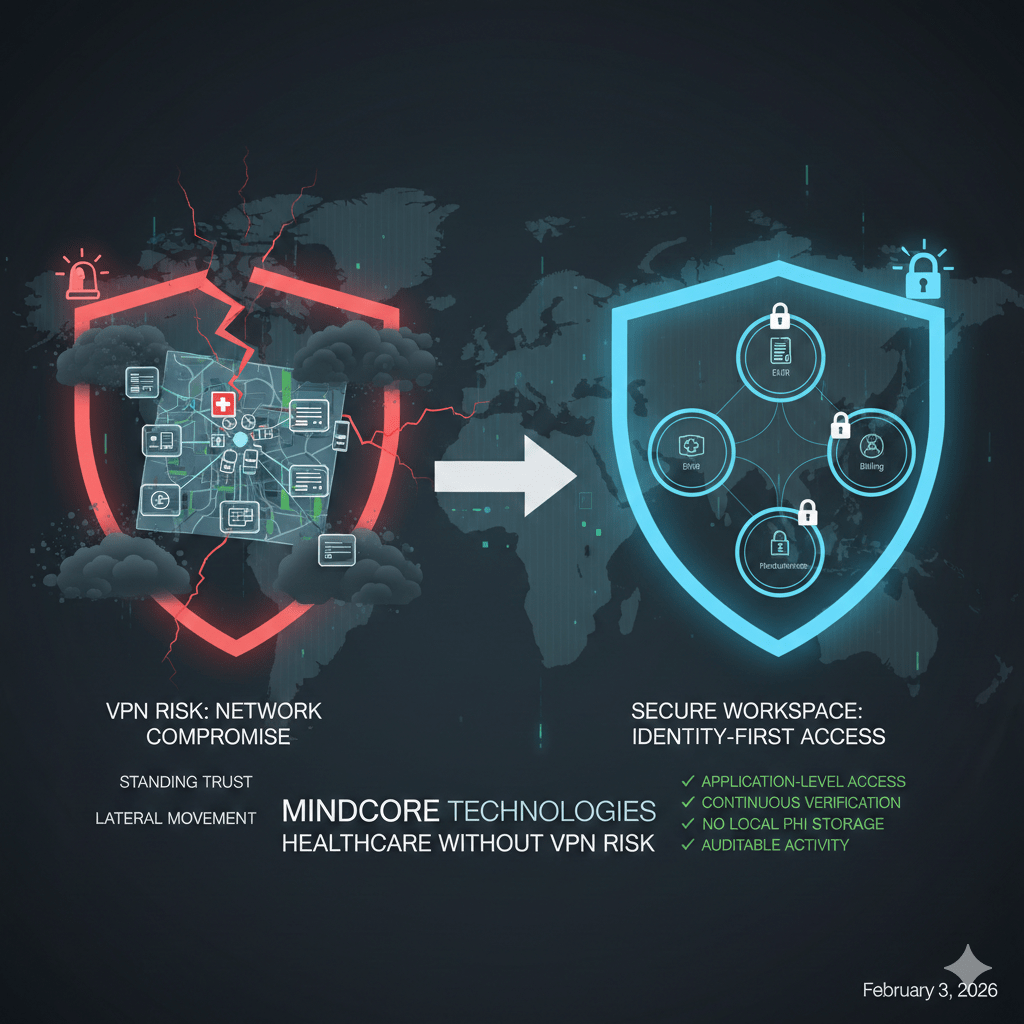
At Mindcore Technologies, healthcare security reviews repeatedly confirm the same issue: VPNs turn identity compromise into network compromise. Secure remote access without VPN risk requires a fundamentally different access model.
Why VPN-Based Remote Access Fails in Healthcare
VPNs were designed to connect offices, not clinicians, vendors, and cloud platforms at scale.
They fail in healthcare because:
- VPNs extend the internal network to external devices
Clinicians and staff effectively operate inside the hospital network from home, hotels, or shared locations, environments IT cannot fully control. - Authentication creates standing trust
Once connected, users retain broad access for long periods, even as risk conditions change. - Credentials and sessions are reusable
Stolen VPN credentials or session tokens provide repeatable access, not a single-use window. - Visibility is network-centric, not data-centric
Security teams see that a user connected, not what PHI they accessed.
This model assumes trust where healthcare cannot afford it.
How Attackers Exploit VPN Remote Access
Attackers rarely “break into” healthcare networks. They log in.
Common attack paths include:
- Infostealer malware harvesting VPN credentials
Malware collects saved credentials and active sessions long before attackers touch the network. - Phishing-based session hijacking
Attackers steal authenticated sessions, bypassing password strength and basic MFA. - Excessive access after login
VPN users often inherit access to systems far beyond their role. - Lateral movement across flat networks
Once inside, attackers map systems and spread rapidly.
VPNs collapse remote access risk into enterprise-wide exposure.
What Secure Remote Access Looks Like Without VPNs
Secure remote access without VPNs removes network trust entirely.
Instead of extending the network, it:
- Delivers access at the application level
Users connect only to approved applications, not subnets or servers. - Uses identity-first, session-based access
Every session is verified, scoped, and continuously evaluated. - Creates ephemeral access paths
Connectivity exists only while access is approved and active. - Keeps infrastructure invisible
Systems do not respond to scans or probes from unauthorized users.
This approach prevents compromise from escalating.
How Secure Workspaces Enable VPN-Free Remote Access
Secure workspaces are the practical enforcement layer for zero trust remote access.
They provide:
- Application isolation inside a controlled workspace
EHRs, billing systems, and clinical apps remain protected from direct endpoint access. - PHI containment by design
Data stays inside the workspace and does not reach unmanaged devices. - No lateral movement paths
Compromised access cannot pivot across systems. - Centralized visibility and governance
All access and activity is logged and auditable.
Remote access becomes contained instead of expansive.
Why Secure Workspaces Are Better for Clinicians and Staff
VPN-free access is not just more secure, it is more reliable.
Secure workspaces improve operations by:
- Reducing connection failures and latency
Access does not depend on fragile network tunnels. - Eliminating VPN client issues
Fewer updates, fewer conflicts, fewer support tickets. - Supporting remote and hybrid workflows naturally
Clinicians access systems securely from anywhere without friction.
Security improves without adding operational burden.
Protecting PHI During Remote Access
Remote access is one of the highest-risk vectors for PHI exposure.
Secure workspaces reduce this risk by:
- Preventing local storage of PHI
Data is not downloaded, cached, or synced to endpoints. - Restricting copy, export, and transfer actions
Data movement is controlled and observable. - Limiting access scope automatically
Users cannot reach data outside their role or purpose.
This directly reduces breach severity and audit findings.
Remote Access, Ransomware, and Containment
Ransomware thrives on visibility and movement.
Secure remote access without VPNs disrupts both:
- No access to internal file systems or servers
Ransomware cannot encrypt what it cannot reach. - No discovery of additional targets
Infrastructure remains invisible after access. - Immediate session termination
Access can be revoked instantly without reconfiguring networks.
Containment replaces cleanup as the primary defense.
HIPAA Alignment Through Architecture
HIPAA expects healthcare organizations to minimize exposure and prove control.
Secure remote access without VPNs supports this by:
- Enforcing minimum necessary access automatically
Users see only what they are authorized to access. - Providing application-level audit trails
Logs show exactly which PHI systems were accessed and when. - Reducing reliance on unmanaged endpoints
Devices become access terminals, not data stores.
Compliance becomes an outcome of design, not documentation.
How Mindcore Technologies Implements VPN-Free Remote Access
Mindcore enables secure remote access for healthcare organizations by:
- Mapping clinical, administrative, and vendor workflows
Access reflects real operational needs. - Replacing VPNs with secure workspace access
Network exposure is removed from the equation. - Defining role-based access to PHI systems
Permissions align with responsibility. - Enforcing device and session posture checks
Access adapts dynamically to risk. - Providing centralized monitoring and governance
Security and compliance teams gain continuous visibility.
The focus is measurable risk reduction without disrupting care.
A Simple Remote Access Reality Check
Your remote access model is still risky if:
- VPN access is required
- Sessions persist indefinitely
- Users can access systems beyond their role
- PHI reaches unmanaged devices
- Remote access audits are manual
These are architectural issues, not training failures.
Final Takeaway
Secure remote access in healthcare no longer means securing a VPN. It means eliminating network trust, containing access at the application level, and protecting PHI by design. Secure workspaces deliver this without disrupting clinicians or operations.
For healthcare organizations facing ransomware, credential theft, and compliance pressure, VPN-free remote access is not a future goal. It is the most practical path forward.