Remote and hybrid work changes the VoIP security model completely. Your phone system is no longer confined to an office network. It now operates across home Wi-Fi, public networks, mobile devices, and unmanaged endpoints.
If your VoIP deployment was designed for a single office and later extended to remote staff without architectural changes, your risk profile increased immediately.
At Mindcore Technologies, we see VoIP environments become vulnerable not because of the technology itself, but because perimeter-based assumptions no longer apply.
Remote VoIP security requires intentional design.
Why Remote And Hybrid Teams Increase VoIP Risk
When employees work outside the office, several new exposure points appear.
Unmanaged Home Networks
- Consumer-grade routers often lack proper firewall configuration, increasing interception risk.
- Default Wi-Fi passwords and outdated firmware create weak entry points.
- Shared home networks increase lateral exposure risk.
Public Wi-Fi Usage
- Open networks can expose unencrypted signaling traffic.
- Rogue access points can intercept traffic if encryption is not enforced.
- Man-in-the-middle attacks become more feasible.
Softphone Usage on Personal Devices
- Personal devices may lack endpoint protection.
- Insecure applications may conflict with VoIP services.
- Compromised devices can expose credentials.
Remote access expands the attack surface significantly.
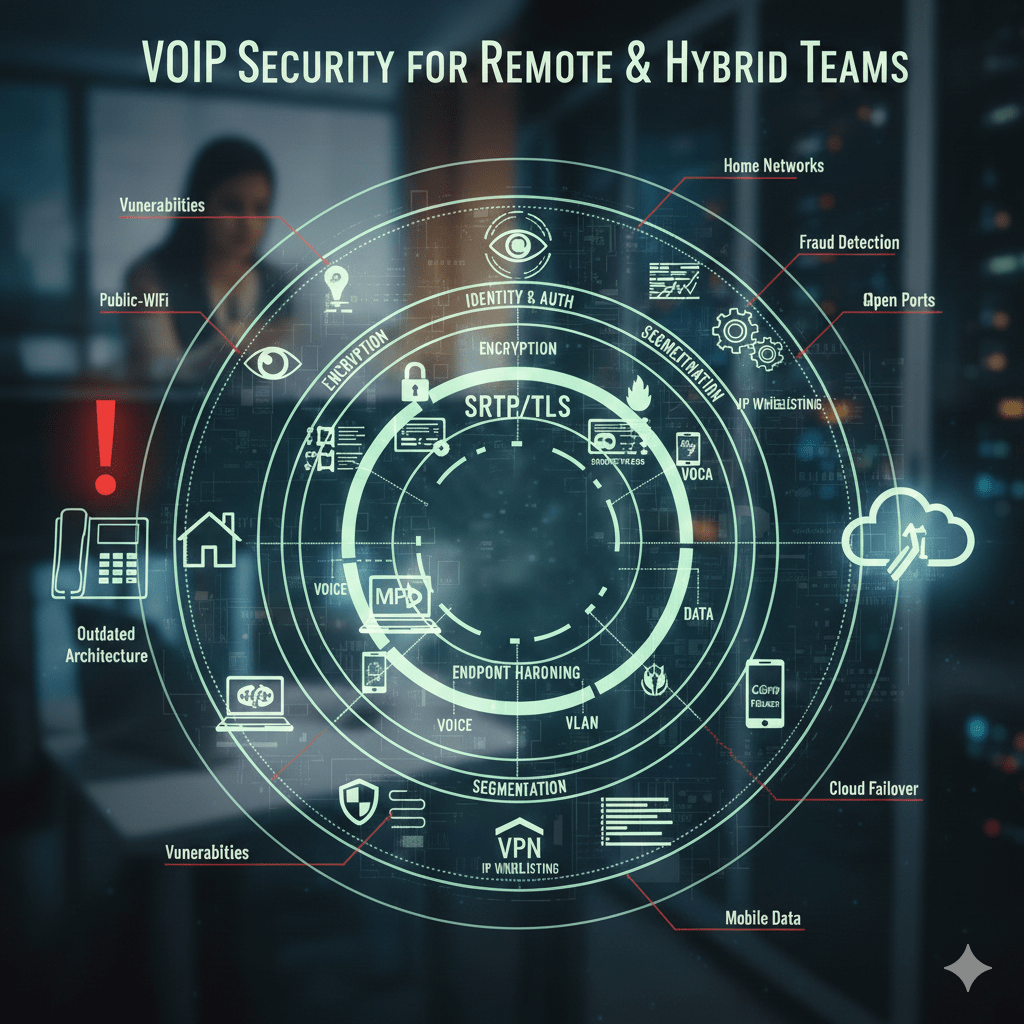
Core Principles For Securing VoIP In Distributed Environments
Securing VoIP for remote teams requires layered controls across identity, network, endpoint, and monitoring.
1. Enforce Strong Identity And Authentication Controls
Identity is the primary security boundary in remote environments.
You should:
- Require multi-factor authentication for VoIP administrative portals to prevent credential compromise.
- Enforce strong SIP authentication credentials to reduce brute-force exposure.
- Disable unused extensions to eliminate unnecessary access points.
- Restrict device registration to approved geographic regions or IP ranges when possible.
Credential compromise is one of the most common VoIP attack vectors.
2. Encrypt All Signaling And Voice Traffic
Encryption becomes critical when traffic leaves your internal network.
Ensure that:
- TLS is enabled for SIP signaling to protect call setup data.
- SRTP is enabled for voice streams to prevent interception.
- Insecure fallback protocols are disabled to eliminate downgrade attacks.
- Certificates are properly maintained and not expired.
Without encryption, remote VoIP traffic can be intercepted on unsecured networks.
3. Segment And Isolate Voice Traffic
Remote teams still connect into your internal systems.
You should:
- Place VoIP infrastructure on a dedicated voice VLAN within your core network.
- Restrict cross-network communication between voice and user subnets.
- Prevent VoIP devices from communicating directly with sensitive internal systems.
- Monitor voice VLAN traffic for unusual outbound behavior.
Segmentation limits lateral movement if an endpoint is compromised.
4. Harden Remote Endpoints
Remote VoIP security depends on device security.
Require:
- Business-managed devices for softphone access whenever possible.
- Endpoint protection software on all systems running VoIP applications.
- Regular patching of operating systems and VoIP clients.
- Encrypted storage on devices handling call logs or recordings.
Unmanaged devices increase breach likelihood.
5. Implement Secure Remote Access Methods
If VoIP systems require remote management or on-premise connectivity:
- Avoid exposing SIP services directly to the public internet.
- Use secure VPN tunnels with strong authentication where necessary.
- Limit administrative access to specific IP ranges.
- Monitor failed login attempts aggressively.
Direct exposure without controls invites automated attacks.
6. Monitor For Fraud And Anomalies
Remote environments increase the need for visibility.
You should:
- Monitor call detail records for unusual international activity.
- Set alerts for abnormal call volume spikes.
- Track login attempts and registration anomalies.
- Review administrative changes to VoIP configurations regularly.
Fraud detection must be continuous, not reactive.
7. Plan For Redundancy And Uptime
Remote teams rely heavily on stable communication.
Implement:
- Secondary internet connections for office-based VoIP infrastructure.
- Cloud failover routing that redirects calls to mobile devices automatically.
- UPS battery backup for core networking equipment.
- Regular failover testing to confirm continuity works under pressure.
Security includes availability.
Common Remote VoIP Security Mistakes
Organizations frequently make these errors:
- Allowing softphones on unmanaged personal devices.
- Leaving SIP ports publicly exposed without restriction.
- Failing to encrypt voice traffic.
- Ignoring firmware updates on IP phones.
- Skipping fraud monitoring because “we’re too small to be targeted.”
Remote teams magnify these weaknesses.
How Mindcore Technologies Secures VoIP For Hybrid Workforces
Mindcore supports secure VoIP deployments by:
- Conducting network readiness assessments for remote scalability.
- Designing segmented voice architectures that reduce lateral exposure.
- Hardening firewall and SIP configurations to reduce attack surface.
- Enforcing strong identity controls and multi-factor authentication.
- Implementing call monitoring and fraud detection mechanisms.
- Designing redundancy strategies to protect uptime across distributed teams.
VoIP must evolve with your workforce model.
Final Takeaway
VoIP can be secure for remote and hybrid teams, but only when identity controls, encryption, segmentation, endpoint hardening, and monitoring are enforced consistently.
The risk is not remote work itself. The risk is extending an office-based VoIP system into a distributed workforce without adjusting architecture.
Frequently Asked Questions
How can businesses secure their VoIP phone systems for remote teams?
Secure VoIP systems by implementing strong authentication, encrypted SIP/TLS connections, VPN access, firewall rules, and regularly patching endpoints. This ensures calls and data remain protected across home and hybrid networks Cybersecurity Services.
Why is VoIP security important for hybrid teams?
Remote and hybrid workers access systems over untrusted networks. Without encryption, strong credentials, and monitoring, attackers can eavesdrop, hijack calls, or compromise sensitive communications Phishing Awareness.
What are common VoIP security threats?
Common threats include SIP account hijacking, eavesdropping, toll fraud, phishing over VoIP, endpoint malware, weak passwords, and misconfigured call routing. Understanding these risks helps teams prioritize protections Cybersecurity Services.
How can businesses monitor VoIP security effectively?
Monitor VoIP security by tracking call logs, using intrusion detection systems, reviewing firewall events, and deploying analytics that detect abnormal call patterns or unauthorized access Cloud & Infrastructure Management.
What best practices should organizations follow for VoIP compliance?
Follow encrypted communications, multi-factor authentication, centralized management, regular updates, employee training, network segmentation, and continuous auditing. These steps reduce risk for sensitive corporate conversations and data Managed IT Services.
Matt Rosenthal’s Expertise in VoIP Security for Hybrid Teams
Matt Rosenthal, CEO of Mindcore Technologies, brings decades of IT, cybersecurity, cloud, and communications infrastructure experience. He helps organizations secure remote and hybrid VoIP systems through encryption, authentication, endpoint protection, monitoring, and compliance. Under his leadership, businesses implement VoIP solutions that protect sensitive communications, reduce risk, and maintain operational continuity across distributed teams Cybersecurity Services.