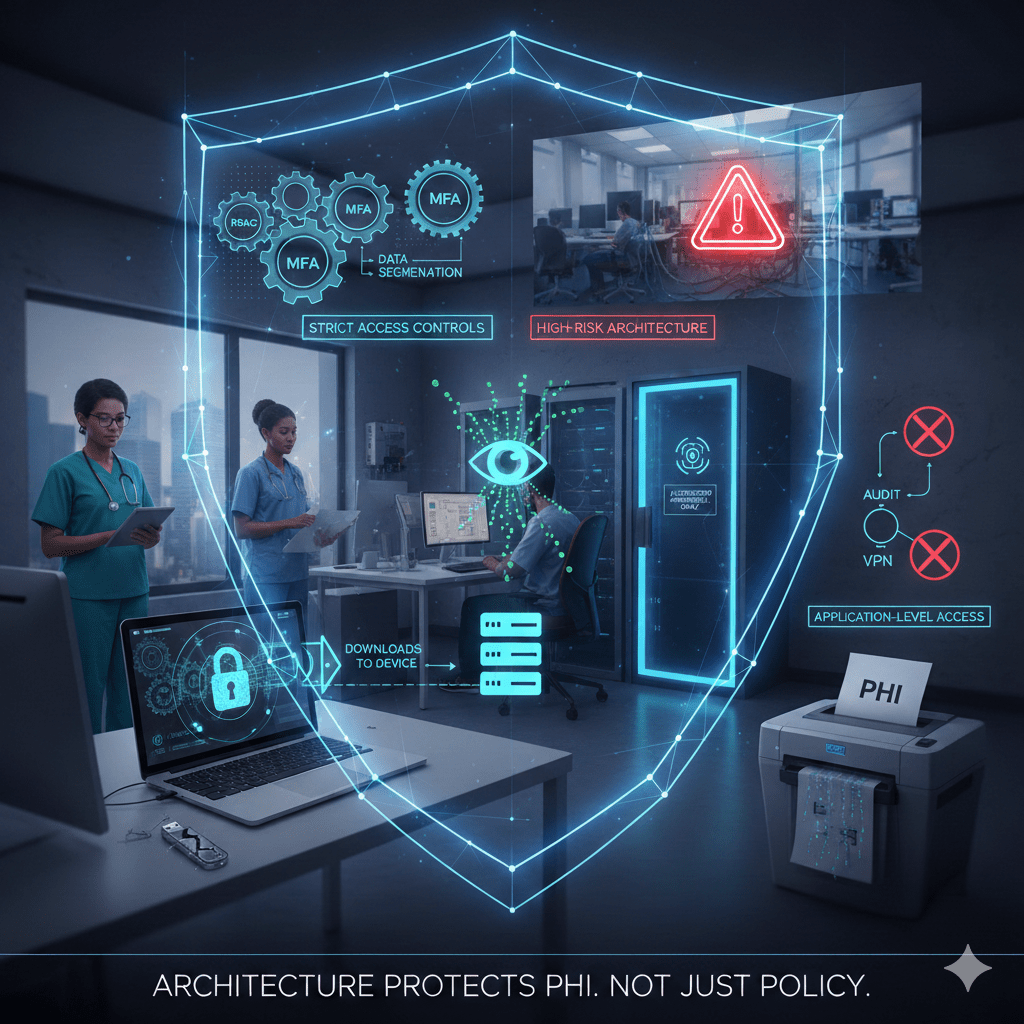
Patient Health Information is rarely exposed because of sophisticated hacking alone. It is exposed because workplace access is too broad, devices are loosely controlled, and internal trust is assumed.
Most healthcare breaches begin with valid credentials used in the wrong way. Protecting PHI in the workplace means designing controls that assume mistakes and compromise will happen, and limiting what damage can follow.
At Mindcore Technologies, workplace PHI risk assessments consistently show that exposure is driven by architecture, not intent. Employees are not the problem. Weak access models are.
1. Enforce Strict Role-Based Access Control (RBAC)
The foundation of PHI protection in the workplace is limiting who can see what.
Workplaces must:
- Define access strictly by job function
Nurses, billing staff, HR, and IT should have clearly separated data scopes. - Eliminate “department-wide” access permissions
Broad group access increases unnecessary exposure. - Review access regularly
Role drift occurs when employees change responsibilities without permission updates. - Automatically remove access upon termination or transfer
Delays in revocation are a common breach factor.
Minimum necessary access must be enforced technically, not just written in policy.
2. Prevent PHI From Spreading to Endpoints
PHI is most vulnerable once it leaves controlled systems.
Workplaces should:
- Restrict downloads of PHI to local devices
Export capabilities should be limited and monitored. - Disable automatic file syncing to personal storage
Consumer cloud services increase exposure risk. - Use secure workspace models for remote access
Keeping PHI inside controlled environments rather than on laptops. - Enforce full-disk encryption on all work devices
Lost or stolen laptops remain a major risk.
If PHI lives on endpoints, the organization has already expanded its attack surface.
3. Eliminate VPN-Based Network Exposure
VPN access expands workplace risk significantly.
To reduce exposure:
- Replace network-level VPN access with application-level access
Employees should connect only to the systems they need. - Limit internal network visibility
Compromised credentials should not unlock infrastructure. - Terminate sessions automatically after inactivity
Persistent sessions create opportunity. - Avoid shared VPN accounts for teams or vendors
Shared credentials destroy accountability.
Access to PHI systems should not mean access to the network.
4. Strengthen Identity and Authentication Controls
Credential compromise is the dominant breach vector.
Workplaces must:
- Enforce multi-factor authentication (MFA) universally
Especially for remote and administrative users. - Implement strong password policies with monitoring for reuse
Password reuse across systems increases risk. - Limit privileged accounts aggressively
Administrative access should be rare and justified. - Monitor for abnormal login patterns
Off-hours access or unusual locations require review.
Identity enforcement is the control plane of workplace PHI security.
5. Secure Physical Workspaces
Workplace PHI protection includes physical safeguards.
Facilities should:
- Position screens away from public view
Reception and shared spaces are high-risk. - Enable automatic screen locks
Idle systems should not remain accessible. - Secure printed documents
Shred PHI immediately after use. - Restrict server room access
Only authorized personnel should access infrastructure.
Physical oversight remains a frequent audit finding.
6. Monitor and Log PHI Access
Visibility is essential for accountability.
Organizations should:
- Log every access event tied to patient records
Including user identity and timestamp. - Centralize log storage securely
Fragmented logs hinder investigation. - Review anomalies proactively
Large data exports or unusual record access require scrutiny. - Test audit retrieval processes regularly
Evidence must be defensible during review.
If access cannot be traced clearly, compliance is fragile.
7. Secure Third-Party and Vendor Access in the Workplace
Vendors often operate inside clinical environments.
To reduce risk:
- Provide vendors with unique credentials
Never shared access. - Scope vendor access narrowly
Vendors should only reach supported systems. - Enforce time-bound access
Temporary engagement should not create permanent exposure. - Audit vendor session activity
Vendor access must be as visible as employee access.
Third-party access should never bypass workplace controls.
8. Prepare for Ransomware and Breach Containment
Workplace PHI protection must assume compromise.
Organizations should:
- Segment critical systems
EHR, billing, and backup systems isolated from general workstations. - Protect backup repositories separately
Backup deletion is common in ransomware attacks. - Enable rapid session termination capability
Compromised accounts must be isolated instantly. - Test incident response scenarios regularly
Practice reduces response delays.
Containment speed determines regulatory and operational impact.
9. Align Technical Controls With HIPAA Requirements
Workplace PHI protection must meet HIPAA standards.
IT teams must ensure:
- Access control enforcement
- Audit control implementation
- Transmission security
- Integrity protection
- Incident response readiness
HIPAA compliance is achieved through enforced technical discipline, not documentation alone.
How Mindcore Technologies Strengthens Workplace PHI Protection
Mindcore supports healthcare organizations by:
- Assessing workplace access architecture for implicit trust gaps
Identifying exposure points before incidents occur. - Implementing identity-driven access models
Eliminating broad network-level permissions. - Deploying secure workspace containment strategies
Preventing PHI sprawl across devices. - Centralizing audit visibility and compliance reporting
Making PHI interaction defensible. - Designing ransomware containment architectures
Protecting clinical operations during incidents.
The objective is operational resilience, not reactive patching.
A Practical Workplace PHI Risk Check
Your workplace environment is high-risk if:
- Employees can download PHI freely
- VPN access exposes internal systems
- Access permissions rarely expire
- Vendor access is persistent
- Audit logs are incomplete
- Ransomware response requires shutting down departments
These are architectural weaknesses, not employee failures.
Final Takeaway
Protecting patient health information in the workplace requires disciplined access control, endpoint containment, identity enforcement, segmentation, and continuous visibility. Policies alone do not protect PHI. Architecture does.
Organizations that redesign workplace access around least privilege and structural containment significantly reduce breach scope and regulatory exposure. Those that rely on perimeter defenses and employee awareness alone remain vulnerable to the credential-based attacks that dominate healthcare today.