An IT assessment is not a checklist. It is a structured examination of how your technology actually operates under real-world conditions, not how it is supposed to work on paper.
Most organizations believe they understand their IT environment until an incident proves otherwise. At that point, the gaps are obvious, expensive, and avoidable.
At Mindcore Technologies, IT assessments consistently reveal the same pattern. Systems technically function, but risk accumulates quietly through misconfigurations, outdated assumptions, and access models that no longer match how the business operates.
An IT assessment exists to surface those issues before they turn into outages, breaches, or compliance failures.
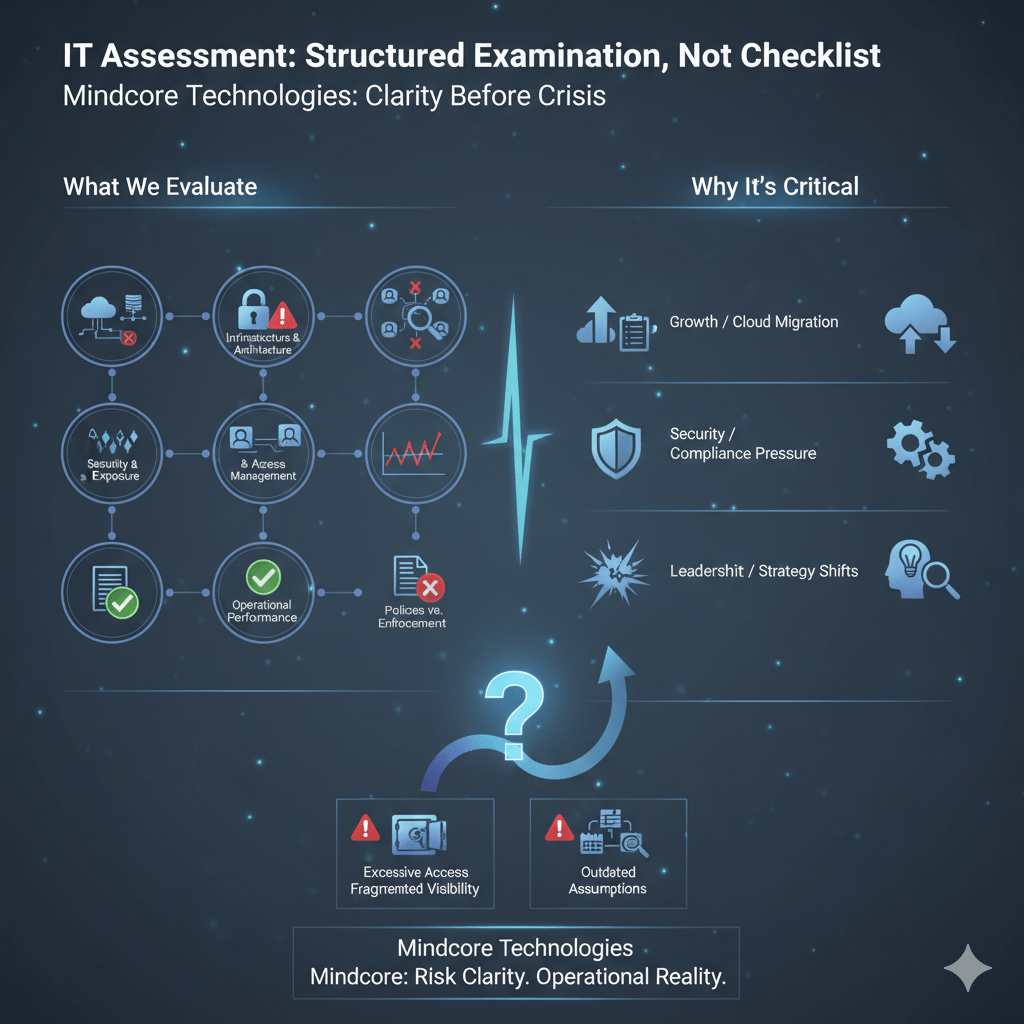
What an IT Assessment Actually Evaluates
A proper IT assessment looks beyond surface-level tools and focuses on how systems, access, and processes interact.
It typically evaluates:
- Infrastructure and architecture
How servers, cloud services, networks, and endpoints are designed, connected, and maintained, including where single points of failure exist. - Security controls and exposure
How access is granted, monitored, and restricted, and whether controls actually limit real-world risk. - Identity and access management
Who can access what systems, for how long, and under what conditions, including excessive or forgotten permissions. - Operational performance and reliability
Whether systems support business workloads without creating instability, downtime, or hidden bottlenecks. - Policies versus enforcement
Whether documented policies are technically enforced or merely advisory.
The goal is to measure reality, not intent.
Why Organizations Conduct IT Assessments
IT assessments are not just for companies in trouble. They are used when leadership needs clarity.
Common drivers include:
- Preparing for growth or cloud migration
Expansion magnifies existing weaknesses. - Responding to security or compliance pressure
Insurance renewals,audits, or regulatory scrutiny often expose gaps. - Recurring performance or reliability issues
Slow systems, outages, and inconsistent access are symptoms, not root causes. - Post-incident validation
After a breach or outage, organizations need to understand what failed and why. - Leadership turnover or strategy shifts
New CIOs, CISOs, or executives need an accurate baseline.
An assessment provides a factual starting point for decision-making.
What an IT Assessment Is Not
This distinction matters.
An IT assessment is not:
- A vulnerability scan alone
Scans identify technical flaws but do not explain systemic risk. - A sales pitch disguised as analysis
Findings should stand independently of tools or vendors. - A compliance checklist
Passing controls does not mean risk is controlled. - A one-time event
IT environments evolve constantly, assessments must reflect that.
When assessments are treated as paperwork, risk remains hidden.
The Most Common Issues Found During IT Assessments
Across industries, the same issues appear repeatedly.
These include:
- Excessive access permissions
Users retain access far beyond their role or business need. - Flat or overexposed network architectures
Lateral movement is possible once access is gained. - Outdated assumptions about trust
VPNs, long-lived sessions, and implicit internal trust remain common. - Inconsistent monitoring and visibility
Logs exist, but they are fragmented and rarely reviewed holistically. - Operational shortcuts that became permanent
Temporary fixes quietly become part of the environment.
These issues rarely trigger alarms until something goes wrong.
How a Good IT Assessment Is Performed
Effective IT assessments follow a structured approach.
They typically include:
- Discovery and documentation
Inventory of systems, users, access paths, and integrations. - Architecture and access review
Analysis of how users and systems interact, not just where they exist. - Risk prioritization
Identification of issues based on impact and likelihood, not volume. - Operational alignment review
Evaluation of whether IT supports how the business actually operates. - Actionable recommendations
Clear steps that reduce risk and improve stability, not abstract guidance.
The outcome should be clarity, not confusion.
IT Assessments and Cybersecurity Risk
Most cybersecurity failures begin as IT failures.
IT assessments uncover:
- Where trust is assumed instead of verified
Especially around remote access and cloud systems. - How attackers could move after initial access
Lateral paths are often obvious once mapped. - Which controls fail silently
Tools may be deployed but poorly configured. - Where detection would be delayed or missed
Visibility gaps often exist between platforms.
Security posture improves when these issues are addressed structurally.
How IT Assessments Support Compliance
Compliance frameworks expect control, not intention.
An IT assessment helps by:
- Identifying gaps between policy and enforcement
Many failures occur where controls exist only on paper. - Clarifying access to regulated data
Especially important for healthcare, finance, and legal environments. - Improving audit readiness
Evidence becomes easier to produce when systems are understood. - Reducing reactive compliance work
Issues are fixed proactively, not during audits.
Compliance becomes manageable when environments are understood.
How Mindcore Technologies Conducts IT Assessments
Mindcore approaches IT assessments with a focus on risk clarity and operational reality.
This includes:
- Evaluating how access is actually used
Not how it is intended to be used. - Reviewing identity, session, and data exposure models
Especially in cloud and remote environments. - Identifying architectural risks, not just tool gaps
Structure matters more than product count. - Prioritizing findings based on business impact
Not all issues carry equal risk. - Delivering clear, actionable remediation paths
Recommendations align with real-world constraints.
The objective is decision-ready insight, not a technical report that sits unread.
When an IT Assessment Should Trigger Action
An IT assessment should lead to change if it reveals:
- Broad access to sensitive systems or data
- Flat networks with unrestricted lateral movement
- Reliance on VPNs or long-lived sessions
- Limited visibility into user activity
- Repeated operational issues without clear root cause
These are indicators of structural risk, not minor misconfigurations.
Final Takeaway
An IT assessment is not about finding everything that is wrong. It is about understanding where risk, inefficiency, and exposure quietly accumulate over time.
Organizations that use IT assessments strategically gain control before incidents force it. Organizations that avoid them usually learn the same lessons under far worse conditions.