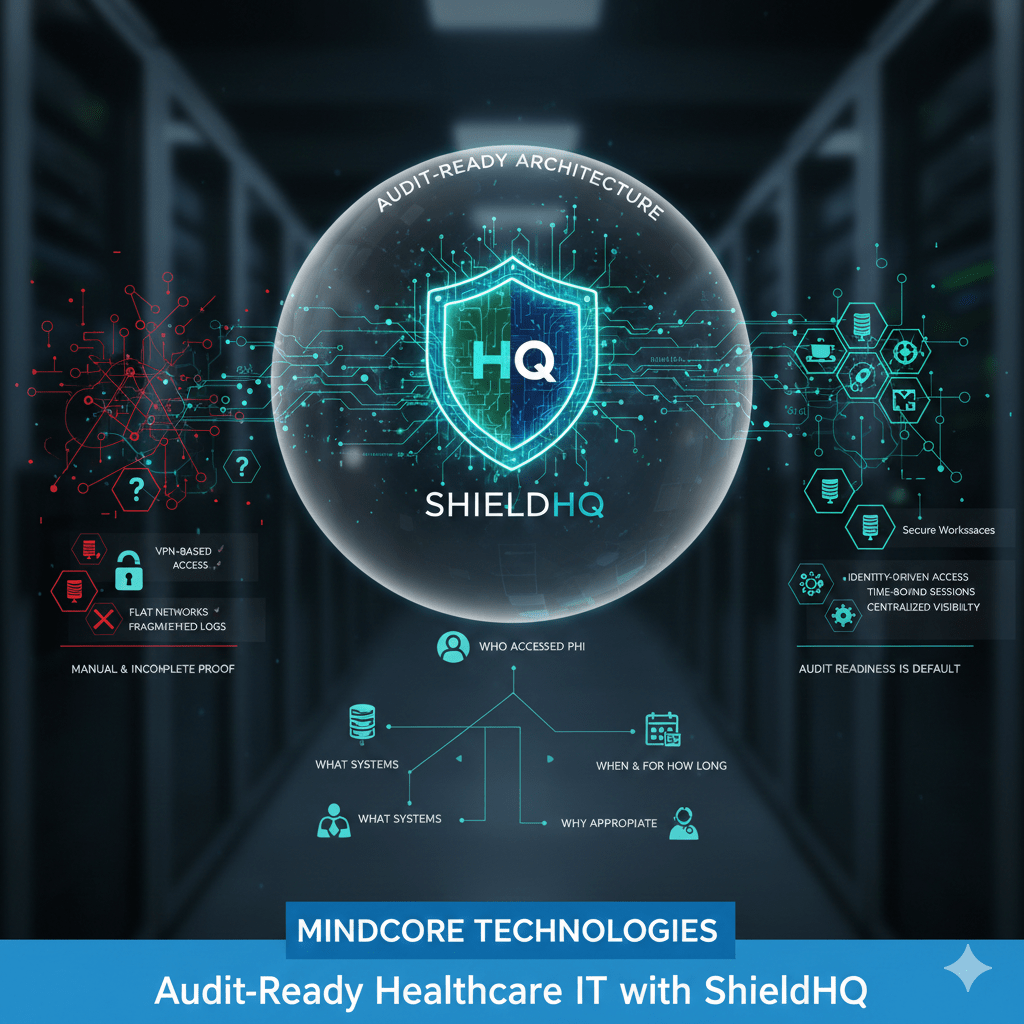
Most healthcare organizations do not fail audits because they lack security tools. They fail because they cannot clearly prove who accessed PHI, why access was granted, and how exposure was prevented. Audit readiness is not about documentation. It is about architecture.
ShieldHQ Powered by Dispersive® Stealth Networking was designed to make audit readiness inherent, not reactive.
At Mindcore Technologies, audit reviews repeatedly show that organizations using secure workspace models spend less time preparing for audits and face fewer findings because access, containment, and visibility are built in.
What “Audit-Ready” Actually Means in Healthcare IT
Being audit-ready means you can answer compliance questions immediately, accurately, and consistently.
That includes proving:
- Who accessed PHI
Access is tied to verified identity, not shared credentials. - What systems were accessed
Scope is clearly defined and limited. - When and for how long access occurred
Sessions are time-bound and logged. - Why access was appropriate
Access aligns with role and clinical or operational need.
If these answers require reconstruction, spreadsheets, or assumptions, the environment is not audit-ready.
Why Traditional Healthcare IT Struggles with Audits
Most healthcare IT environments are built for availability, not audit clarity.
Common audit pain points include:
- VPN-based access models
Once connected, users can reach more than intended. - Flat or loosely segmented networks
Access paths are unclear and difficult to justify. - Endpoint-dependent controls
Auditors must trust device hygiene and policy enforcement. - Fragmented logging systems
Evidence lives across multiple tools and teams.
Audits become stressful because proof is manual and incomplete.
How ShieldHQ Makes Audit Readiness Structural
ShieldHQ replaces network-based trust with identity-driven, workspace-based access.
It achieves audit readiness by:
- Isolating users inside secure workspaces
Users never connect directly to internal networks. - Delivering application-level access only
PHI systems are accessed without exposing infrastructure. - Enforcing session-based access
Access automatically expires when sessions end. - Centralizing access control and visibility
Evidence is consistent and immediately available.
Audit readiness becomes the default state.
Enforcing Minimum Necessary Access Automatically
HIPAA requires minimum necessary access, but enforcement is often manual.
ShieldHQ enforces it by:
- Mapping access strictly to roles
Clinicians, billing staff, and vendors see only what they need. - Preventing lateral system access
Users cannot explore unrelated systems. - Eliminating standing privileges
Temporary needs do not become permanent risk. - Removing shared credentials entirely
Accountability is preserved at all times.
Auditors see access control that is deliberate and provable.
Containing PHI to Simplify Audit Scope
PHI sprawl is a major audit risk.
ShieldHQ reduces scope by:
- Keeping PHI inside secure workspaces
Data is not stored on endpoints. - Restricting download, copy, and export paths
Data movement is controlled and logged. - Reducing reliance on endpoint compliance
Security does not depend on device configuration. - Preventing shadow data creation
PHI does not leak into unmanaged locations.
Fewer locations mean fewer audit findings.
Providing Clean, Defensible Audit Trails
Auditors do not want logs. They want clarity.
ShieldHQ provides this through:
- Session-level access records
Every interaction has a start, end, and scope. - Clear identity-to-access correlation
No ambiguity about who did what. - Centralized visibility across users and vendors
Evidence is not scattered across tools. - Consistent enforcement across environments
Rules do not change based on location.
Audit conversations become straightforward instead of adversarial.
Securing Vendor and Third-Party Access for Audits
Vendor access is a frequent audit finding.
ShieldHQ addresses this by:
- Replacing VPN access with workspace-based access
Vendors never join internal networks. - Scoping access to specific applications or devices
No unnecessary exposure. - Enforcing time-bound access automatically
Access ends when work is complete. - Logging all vendor activity centrally
Evidence is readily available.
Third-party risk becomes auditable, not assumed.
Audit Readiness During Incidents
Audits often follow incidents.
ShieldHQ improves post-incident audits by:
- Limiting breach scope
Fewer systems and records are affected. - Preserving clean environments
Not everything needs rebuilding. - Providing immediate access records
Incident timelines are clear. - Reducing notification complexity
Impact is easier to define.
This reduces regulatory exposure and response stress.
Why Audit Readiness Improves Security Outcomes
Audit-ready environments are safer environments.
They benefit from:
- Reduced attack surface
Less access means less opportunity. - Faster incident containment
Access can be revoked instantly. - Stronger accountability culture
Users understand boundaries. - Simplified compliance operations
Less time spent preparing evidence.
Security and compliance reinforce each other.
How Mindcore Technologies Delivers Audit-Ready Healthcare IT with ShieldHQ
Mindcore enables audit-ready healthcare IT by:
- Assessing current access and audit gaps
Identifying where proof breaks down. - Implementing ShieldHQ secure workspace architecture
Removing network-based trust. - Designing role-based, session-limited access models
Aligning access with HIPAA expectations. - Containing PHI inside controlled environments
Reducing scope and exposure. - Aligning security design with audit requirements
Making audits predictable and defensible.
The goal is fewer findings, faster audits, and stronger security.
A Simple Audit Readiness Reality Check
Your environment is not audit-ready if:
- VPN access provides broad network visibility
- PHI exists on endpoints
- Vendor access is persistent
- Audit evidence is manual
- Access justification is unclear
These are architectural weaknesses, not policy failures.
Final Takeaway
Audit readiness in healthcare is not achieved through checklists or last-minute preparation. It is achieved through architecture that enforces control, limits exposure, and produces evidence automatically.
ShieldHQ Powered by Dispersive® Stealth Networking makes audit readiness a byproduct of secure design. Healthcare organizations that adopt it reduce audit stress, improve security posture, and protect patient trust. Those that do not remain one audit away from disruption.