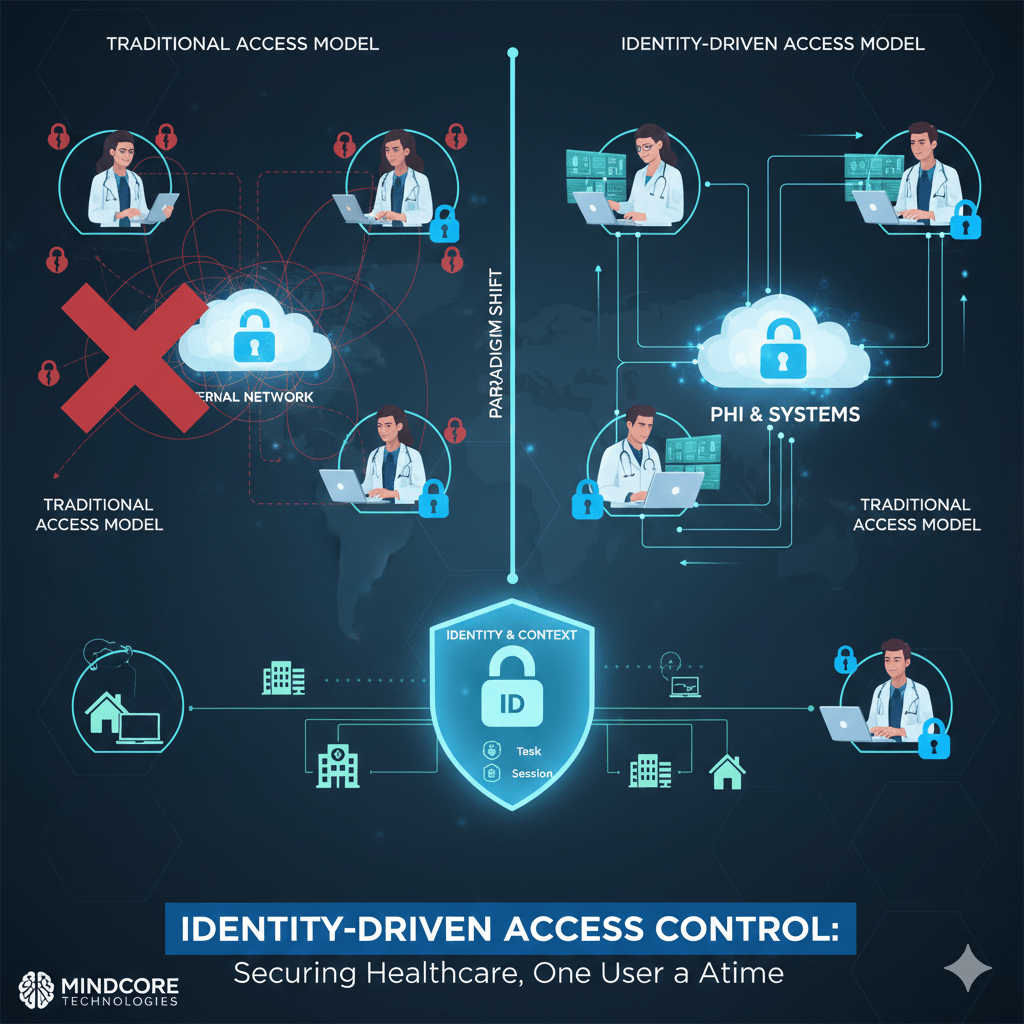
Healthcare security fails when access is granted based on where someone connects from instead of who they are and what they are authorized to do. Networks, VPNs, and static permissions assume trust too early and revoke it too late.
Identity-driven access control fixes this by making identity the only trust anchor, not location, device, or network presence.
At Mindcore Technologies, healthcare breach analysis consistently shows that organizations relying on identity-based access experience smaller incidents, faster containment, and fewer HIPAA findings because access is precise, temporary, and provable.
What Identity-Driven Access Control Actually Means
Identity-driven access control enforces access decisions based on verified identity, role, and context, not network placement.
In practice, this means:
- Access is tied to a unique user identity
Every action maps to a real person, not a shared account. - Permissions are role- and task-specific
Users see only what they are authorized to use. - Access is session-based, not persistent
Trust expires automatically when work ends. - Location and device do not grant trust
Being “inside the network” means nothing.
Identity becomes the control plane.
Why Traditional Access Models Fail Healthcare Organizations
Most healthcare environments still rely on outdated trust assumptions.
Common failures include:
- VPN-based access models
Once connected, users inherit broad network visibility. - Static role assignments
Access grows over time and rarely shrinks. - Shared or generic credentials
Accountability disappears. - Network segmentation without identity enforcement
Segments slow attackers but do not stop misuse.
These models make containment difficult and audits painful.
How Identity-Driven Access Reduces Breach Impact
Breaches often begin with valid credentials.
Identity-driven access reduces impact by:
- Limiting what compromised accounts can reach
Stolen credentials do not unlock the environment. - Preventing lateral movement by default
Access does not extend beyond approved systems. - Enabling instant access revocation
Sessions can be terminated immediately. - Reducing attacker dwell time
Temporary access expires before damage spreads.
Containment is automatic, not reactive.
Supporting Minimum Necessary Access Under HIPAA
HIPAA’s minimum necessary standard is difficult to enforce manually.
Identity-driven access enforces it automatically by:
- Mapping permissions strictly to job function
Clinicians, billing staff, and IT each have scoped access. - Removing standing privileges
Temporary needs do not become permanent exposure. - Blocking access outside approved workflows
Curiosity cannot turn into violations. - Providing clear justification for access
Every permission aligns with a defined role.
Compliance becomes an outcome of design.
Reducing Insider Risk Without Slowing Care
Most insider incidents are accidental, not malicious.
Identity-driven access reduces risk by:
- Eliminating unnecessary visibility
Users cannot see systems unrelated to their role. - Restricting PHI access paths
Data is accessible only within approved contexts. - Providing session-level accountability
Activity is traceable without intrusive monitoring. - Preventing privilege creep
Access does not silently expand over time.
Opportunity for misuse is removed without policing behavior.
Securing Third-Party and Vendor Access
Third-party access is one of the highest-risk areas in healthcare.
Identity-driven access secures vendors by:
- Assigning unique identities to every vendor user
No shared or generic accounts. - Scoping access to specific systems or applications
Vendors cannot explore the environment. - Enforcing time-bound access automatically
Access expires when work is complete. - Maintaining centralized audit logs
Vendor activity is always reviewable.
Vendors are enabled without inheriting their risk.
Improving Audit Readiness Through Identity
Audits fail when access cannot be explained clearly.
Identity-driven access improves audit readiness by:
- Providing clear identity-to-access mapping
Auditors see who accessed what and why. - Logging sessions with defined start and end times
No ambiguity about duration. - Centralizing access evidence
Logs are not scattered across tools. - Reducing audit scope
Fewer systems and users are exposed.
Audits become predictable instead of disruptive.
Why Identity Must Replace Network Trust
Network-based trust assumes:
- Internal equals safe
- Location equals legitimacy
- Devices remain compliant
These assumptions no longer hold.
Identity-driven access replaces them with:
- Explicit authorization for every session
- Continuous validation instead of one-time login
- Access tied to purpose, not proximity
This model scales as healthcare becomes more distributed.
How Mindcore Technologies Implements Identity-Driven Access Control
Mindcore helps healthcare organizations adopt identity-driven access by:
- Assessing current trust assumptions and access paths
Identifying where network trust still exists. - Replacing VPN and network-based access models
Removing implicit trust. - Designing role-based, session-limited access policies
Aligning access with real workflows. - Containing PHI within secure environments
Preventing data sprawl. - Centralizing visibility for security and compliance teams
Making access defensible and auditable.
The focus is architectural control, not policy enforcement alone.
A Simple Identity Risk Reality Check
Your healthcare environment remains high-risk if:
- VPN access exposes internal networks
- Shared credentials exist
- Access permissions rarely expire
- Users can reach systems outside their role
- Audit evidence requires reconstruction
These are identity failures, not tooling gaps.
Final Takeaway
Healthcare security does not fail because of weak tools. It fails because access is granted too broadly and revoked too slowly.
Identity-driven access control restores balance by ensuring every connection is deliberate, limited, and accountable. Healthcare organizations that adopt it reduce breach impact, simplify HIPAA compliance, and protect patient trust at scale. Those that do not continue to rely on assumptions attackers already exploit.