For healthcare CIOs, the problem is no longer whether breaches will happen. The problem is whether the organization is architected to contain them without disrupting care, compliance, or operations. Secure workspaces are emerging as the practical answer, not as a new tool, but as a new access model.
CIOs are adopting secure workspaces because legacy access architectures are now operational liabilities, not just security risks.
At Mindcore Technologies, healthcare transformation projects consistently show that secure workspace adoption succeeds when CIOs treat it as an architectural shift, not a point solution.
Why Secure Workspaces Are Now a CIO-Level Priority
Secure workspace adoption has moved from security teams to the CIO agenda because it impacts core business outcomes.
CIOs are driving adoption because:
- Ransomware now disrupts patient care directly
Downtime affects clinical outcomes, not just IT metrics. - Remote and hybrid access is permanent
VPN-based models do not scale safely. - Third-party dependency is unavoidable
Vendors, partners, and telehealth providers require access. - Audit pressure is increasing
HIPAA audits demand clarity, not assumptions.
Secure workspaces address all four simultaneously.
What CIOs Get Wrong About Secure Workspaces
Secure workspace adoption fails when it is misunderstood.
Common misconceptions include:
- Treating secure workspaces as a VPN replacement only
The real value is containment, not connectivity. - Assuming endpoint security is still the control plane
Secure workspaces reduce reliance on device trust. - Deploying without redefining access models
Old permissions inside new tools recreate the same risk. - Rolling out without executive alignment
Adoption stalls without clinical and operational buy-in.
Secure workspaces are architectural, not cosmetic.
What Secure Workspace Adoption Actually Changes
For CIOs, secure workspace adoption changes how access works across the organization.
It replaces:
- Network-based trust
- Persistent access
- Broad visibility
- Endpoint-dependent security
With:
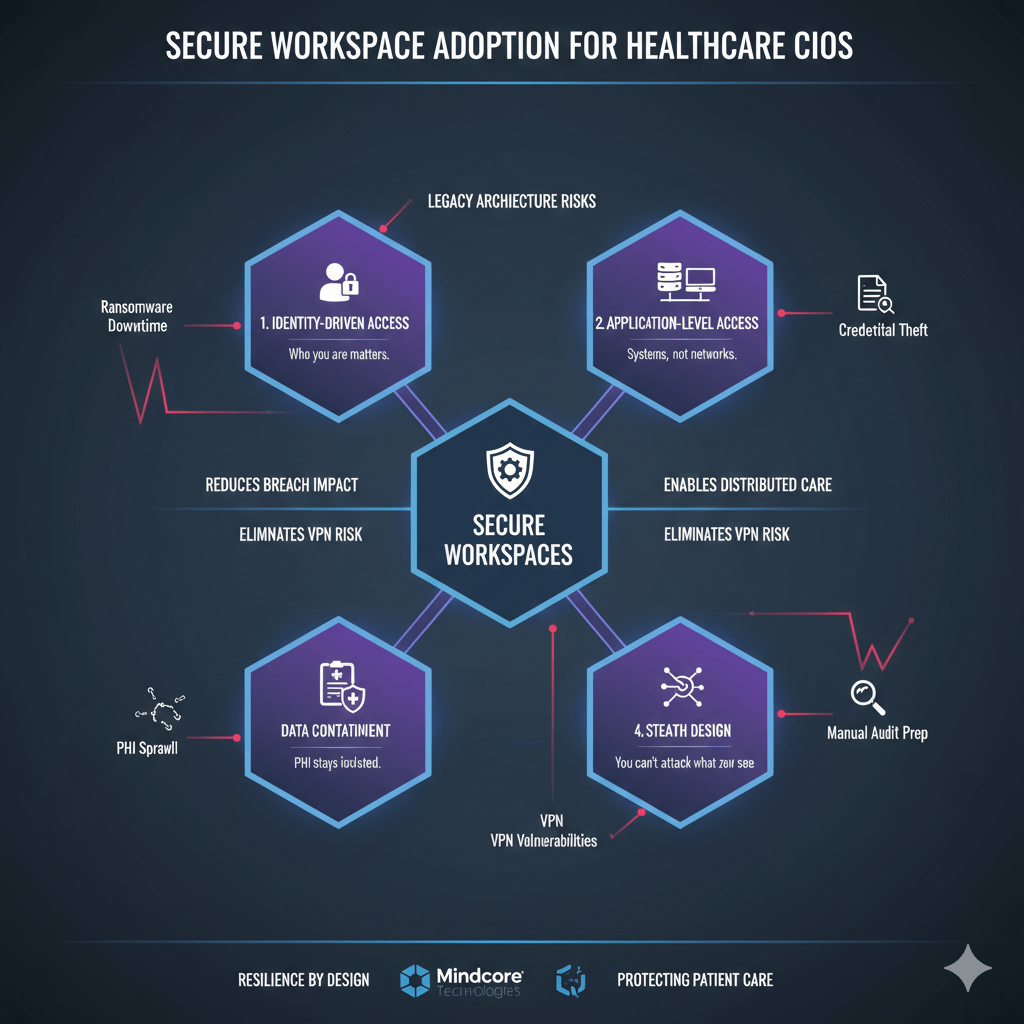
- Identity-driven access
Who the user is matters more than where they connect from. - Application-level connectivity
Users access systems, not networks. - Session-based trust
Access expires automatically. - Data containment by design
PHI stays inside controlled environments.
This fundamentally reduces operational risk.
Reducing Breach Impact Without Slowing Care
CIOs are judged on uptime as much as security.
Secure workspaces protect both by:
- Containing compromise to individual sessions
Breaches do not spread across environments. - Preventing lateral movement
Attackers cannot pivot between systems. - Allowing instant access revocation
Security teams act without shutting down operations. - Preserving clinical access during incidents
Care delivery continues while issues are isolated.
Security stops competing with availability.
Eliminating VPN Risk at Scale
VPN management has become a CIO pain point.
Secure workspace adoption removes that burden by:
- Eliminating internal network exposure
Users never join the network. - Reducing appliance maintenance and patching
Fewer emergency updates and outages. - Simplifying remote access workflows
Fewer support tickets and failures. - Reducing credential blast radius
Compromised accounts affect one workspace, not everything.
CIOs gain stability as well as security.
Supporting Distributed Healthcare Teams Consistently
Healthcare work is no longer location-bound.
Secure workspaces support distribution by:
- Delivering identical access everywhere
Clinic, home, or vendor location behaves the same. - Removing dependency on local network quality
Access is application-centric. - Standardizing security controls across locations
No policy drift. - Simplifying onboarding and offboarding
Access changes are immediate and centralized.
This reduces operational friction across the enterprise.
Improving Audit Readiness Without Manual Effort
Audit readiness often drains CIO resources.
Secure workspaces improve it by:
- Producing session-level access records automatically
Who accessed what and when is always visible. - Aligning access to defined roles and workflows
Justification is built in. - Reducing PHI sprawl
Data does not live on endpoints. - Limiting audit scope during incidents
Fewer systems are involved.
Compliance becomes predictable instead of disruptive.
Managing Third-Party Access Without Inheriting Risk
Vendor access is a CIO concern, not just a security one.
Secure workspaces reduce third-party risk by:
- Eliminating vendor VPN access
Vendors never join internal networks. - Scoping access to exact systems
No exploration or lateral movement. - Enforcing time-bound access automatically
Access expires without manual cleanup. - Centralizing vendor visibility
Activity is auditable and defensible.
Vendors remain productive without expanding attack surface.
What CIOs Should Measure During Adoption
Successful adoption is measurable.
CIOs should track:
- Reduction in VPN usage and dependency
Fewer active tunnels and credentials. - Access scope per role
Fewer systems reachable per user. - Incident containment time
Faster isolation, less downtime. - Audit preparation effort
Reduced manual evidence gathering. - User experience metrics
Fewer access-related support tickets.
These metrics reflect real progress, not marketing claims.
How Mindcore Technologies Guides Secure Workspace Adoption for CIOs
Mindcore supports healthcare CIOs by:
- Assessing existing access architecture and trust assumptions
Identifying where risk is structural. - Designing secure workspace strategies aligned to clinical workflows
Security without disruption. - Phasing adoption to minimize operational impact
No big-bang cutovers. - Replacing VPN and network-based access incrementally
Reducing risk safely. - Aligning architecture with HIPAA and audit expectations
Compliance by design.
The focus is sustainable modernization, not rushed deployment.
A Simple CIO Readiness Check
Secure workspace adoption is overdue if:
- VPNs expose internal networks
- Breaches require shutdowns to contain
- PHI exists on endpoints
- Vendor access is persistent
- Audit preparation is manual
These are architectural liabilities.
Final Takeaway
For healthcare CIOs, secure workspace adoption is not a security trend. It is a necessary architectural evolution driven by modern threats, distributed care delivery, and regulatory pressure.
CIOs who adopt secure workspaces reduce breach impact, stabilize operations, simplify compliance, and future-proof access. Those who delay remain dependent on access models attackers already understand and exploit.
Frequently Asked Questions
What is a secure workspace in healthcare?
A secure workspace is a controlled digital environment that provides healthcare professionals with secure access to applications, patient data, and systems while enforcing identity verification, monitoring, and access restrictions through zero-trust secure workspace technology.
Why are healthcare CIOs adopting secure workspace models?
Healthcare CIOs are adopting secure workspaces to improve cybersecurity resilience, protect protected health information (PHI), support remote access, strengthen compliance readiness, and reduce operational risk across distributed healthcare environments.
How do secure workspaces improve healthcare cybersecurity?
Secure workspaces improve cybersecurity through identity-based access controls, session monitoring, zero-trust architecture, endpoint isolation, continuous verification, and reduced exposure of sensitive healthcare systems using layered cybersecurity protections.
What challenges do healthcare organizations face when adopting secure workspaces?
Common challenges include legacy infrastructure integration, user adoption, compliance alignment, access management complexity, operational disruption concerns, and balancing security with clinical workflow efficiency.
Why is zero-trust architecture important for healthcare environments?
Zero-trust architecture limits unauthorized access, reduces lateral movement, strengthens identity verification, and helps contain cyber threats before they impact patient care systems or sensitive healthcare data.
Healthcare Secure Workspace and Cybersecurity Strategy Expertise from Matt Rosenthal
Matt Rosenthal, CEO of Mindcore Technologies, has extensive experience helping healthcare organizations strengthen cybersecurity resilience, secure remote access, and operational continuity through zero-trust secure workspace strategies. His expertise in identity governance, session-based access controls, healthcare compliance readiness, threat monitoring, endpoint protection, and operational risk management helps healthcare systems reduce exposure to evolving cyber threats while protecting sensitive patient information. Matt’s leadership focuses on building proactive healthcare security frameworks that improve visibility, strengthen compliance alignment, reduce operational risk, and support scalable secure digital healthcare environments through strategic ShieldHQ secure workspace solutions.