HIPAA compliance is not a policy binder. For IT and security teams, it is an operational discipline that governs how access is granted, how PHI is protected, and how breaches are contained. Most audit failures happen not because organizations ignore HIPAA, but because their technical architecture does not enforce it consistently.
For IT leaders, HIPAA is about implementing safeguards that work under real-world conditions, not during audit week.
At Mindcore Technologies, healthcare assessments repeatedly show that organizations struggle most with access control, audit evidence, and breach containment, not with documentation. Compliance lives in architecture.
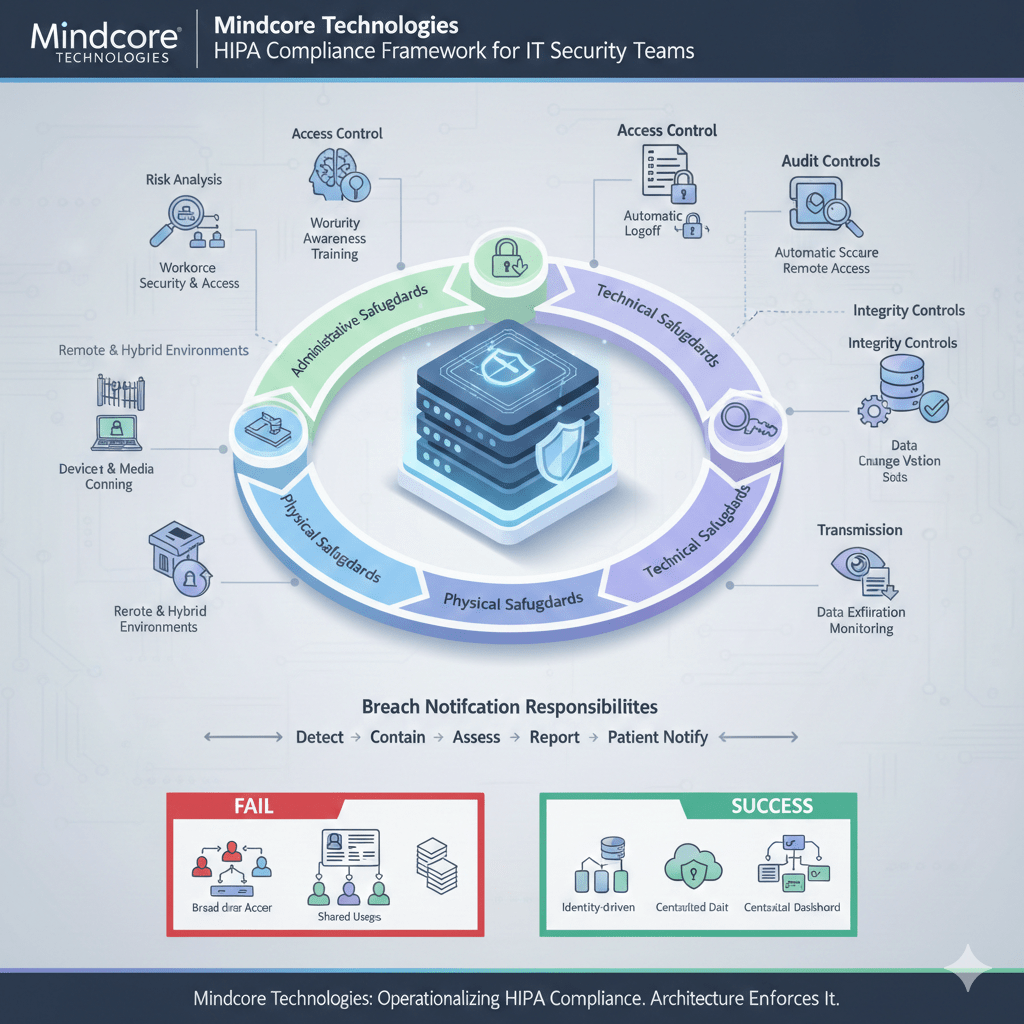
The Core HIPAA Framework IT Must Understand
HIPAA compliance for IT and security teams primarily revolves around the HIPAA Security Rule, supported by the Privacy Rule and Breach Notification Rule.
From a technical standpoint, IT teams must implement and maintain:
- Administrative safeguards
- Physical safeguards
- Technical safeguards
Each directly affects how systems are designed and operated.
1. Administrative Safeguards
Administrative safeguards define how organizations manage risk and govern access.
For IT and security teams, this includes:
- Risk Analysis and Risk Management
Conducting formal assessments of where PHI is stored, transmitted, and accessed, then implementing mitigation plans aligned to real exposure. - Workforce Security and Access Management
Defining who can access PHI systems and ensuring permissions reflect job roles, not convenience. - Security Awareness and Training
Ensuring staff understand phishing, credential theft, and data handling risks. - Incident Response Planning
Maintaining documented and tested procedures for detecting, containing, and reporting breaches.
Administrative safeguards fail when they exist only on paper without technical enforcement.
2. Physical Safeguards
Physical safeguards address environmental and facility controls.
For IT teams, this includes:
- Facility Access Controls
Restricting physical access to servers, network equipment, and backup systems. - Workstation Security
Ensuring devices accessing PHI are protected from unauthorized physical access. - Device and Media Controls
Managing the disposal, reuse, and tracking of hardware storing PHI.
In modern healthcare, physical safeguards must extend to remote and hybrid environments.
3. Technical Safeguards
Technical safeguards are where IT and security teams carry the most responsibility.
These include:
Access Control
IT must enforce:
- Unique User Identification
Every user accessing PHI must have a unique account to preserve accountability. - Role-Based Access Control (RBAC)
Permissions align strictly with job functions. - Automatic Logoff and Session Controls
Access must expire when not actively in use. - Emergency Access Procedures
Controlled mechanisms for urgent care situations.
Access control is where most compliance failures originate.
Audit Controls
Organizations must:
- Log system access and activity involving PHI
Including user identity, time, and scope. - Retain logs securely and consistently
Evidence must be retrievable. - Review logs regularly
Not just store them.
Audit logs must be clear enough to defend access decisions during investigations.
Integrity Controls
IT teams must ensure:
- PHI is not altered improperly
Through access restrictions and monitoring. - Change management processes are enforced
Especially for systems storing PHI. - Data validation mechanisms exist
To detect unauthorized modification.
Integrity failures often occur during ransomware events.
Transmission Security
PHI must be protected when transmitted.
This requires:
- Encryption in transit
Secure communication channels for data exchange. - Secure remote access mechanisms
VPN alternatives or secure workspace models that limit exposure. - Monitoring for unauthorized data exfiltration
Detecting abnormal outbound activity.
Transmission security must assume distributed workforces.
Breach Notification Responsibilities
HIPAA compliance does not end with prevention.
IT and security teams must:
- Detect potential breaches quickly
Through monitoring and anomaly detection. - Contain incidents immediately
Limiting exposure scope. - Assess impact accurately
Determining affected records and systems. - Support legal and compliance reporting timelines
Including patient notification requirements.
Containment speed directly influences regulatory exposure.
Where IT and Security Teams Commonly Fail
Common technical failures include:
- Overly broad VPN access
- Static permissions that never expire
- Shared or generic user accounts
- PHI stored on endpoints
- Manual audit log reconstruction
- Vendor access without scope limitation
These are architectural weaknesses, not policy gaps.
How Modern Architecture Strengthens HIPAA Compliance
Compliance improves when access is enforced structurally.
Modern IT teams reduce HIPAA risk by:
- Replacing network-based trust with identity-driven access
Access is scoped per role and session. - Containing PHI inside controlled environments
Data does not sprawl to endpoints. - Eliminating standing vendor access
Third-party connectivity is time-bound. - Centralizing access visibility and audit trails
Evidence is consistent and immediate.
Architecture reduces reliance on perfect human behavior.
The Operational Reality of HIPAA Compliance
HIPAA compliance for IT and security teams means:
- Designing systems to enforce minimum necessary access
- Maintaining real-time visibility into PHI interactions
- Containing breaches before they escalate
- Producing audit-ready evidence at any time
- Aligning security controls with clinical workflows
Compliance is not about tools. It is about disciplined access design.
How Mindcore Technologies Helps IT and Security Teams Operationalize HIPAA
Mindcore supports healthcare IT teams by:
- Conducting technical risk assessments aligned to HIPAA requirements
Identifying real architectural gaps. - Redesigning access models to enforce least privilege automatically
Removing implicit trust. - Implementing secure workspace containment strategies
Protecting PHI structurally. - Centralizing audit visibility and reporting workflows
Simplifying compliance readiness. - Strengthening breach containment capabilities
Reducing regulatory exposure during incidents.
The focus is making compliance sustainable, not stressful.
A Practical HIPAA Readiness Check for IT Teams
Your environment is likely non-compliant or high-risk if:
- VPN access exposes internal systems
- PHI resides on unmanaged endpoints
- Access permissions rarely expire
- Audit logs require manual reconstruction
- Vendor access is persistent and broad
- Breach response depends on shutting down systems
These are technical failures that auditors consistently flag.
Final Takeaway
For IT and security teams, HIPAA compliance consists of structured access control, controlled data handling, continuous visibility, and rapid breach containment. Policies support it, but architecture enforces it.
Organizations that align their IT architecture with HIPAA safeguards reduce audit stress, limit breach scope, and protect patient trust under real-world conditions. Those that treat compliance as documentation alone remain one incident away from regulatory exposure.