CMMC compliance is not a policy exercise. It is a requirement to enforce security controls across systems that handle Federal Contract Information and Controlled Unclassified Information. Most organizations focus on documentation, but assessors are evaluating whether controls are operational, consistent, and enforceable.
We see companies struggle when controls exist on paper but fail in execution. Access is too broad, monitoring is incomplete, and systems remain exposed. CMMC is designed to eliminate that gap by requiring organizations to demonstrate that controls are actively enforced.
The requirement is not to describe security. It is to prove it.
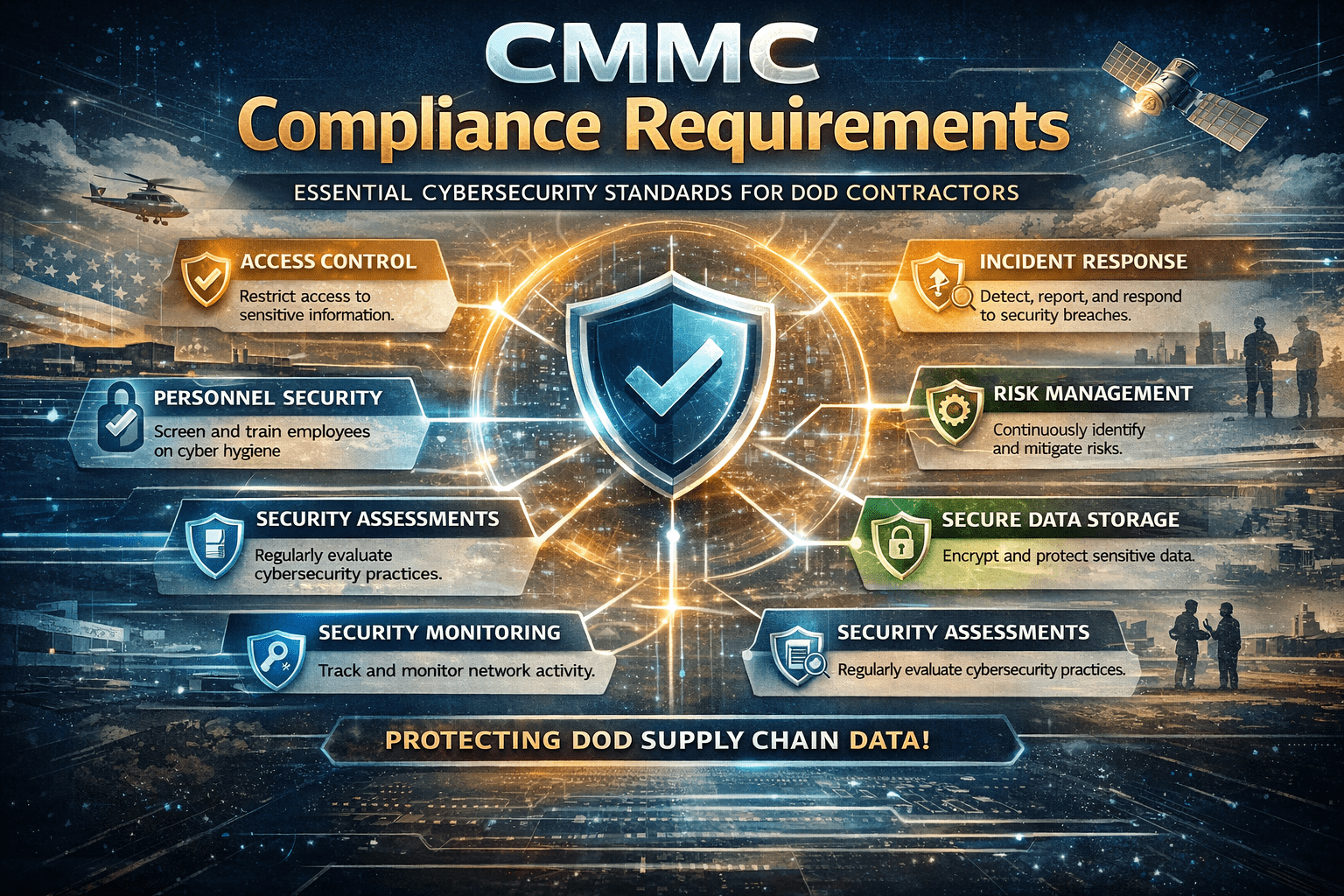
Core Categories of CMMC Requirements
CMMC requirements are grouped into domains that define how security must be implemented and maintained.
• Access control, ensuring only authorized users can access systems and data
• Identification and authentication, verifying user identity before access is granted
• System and communications protection, securing data in transit and across networks
• Configuration management, maintaining secure system settings and baselines
• Incident response, detecting and responding to security events
• Audit and accountability, tracking all system activity for visibility and compliance
• Risk management, identifying and addressing vulnerabilities proactively
These domains align with NIST SP 800-171 and form the foundation of Level 2 compliance.
Access Control Requirements
Access control is one of the most critical areas of CMMC compliance.
• Enforce least privilege, limiting users to only the access required for their role
• Restrict system access, ensuring only authorized users can connect to systems
• Control remote access, securing connections from external environments
• Separate duties, reducing risk by dividing responsibilities across users
Weak access control is one of the most common causes of compliance failure.
Identification and Authentication Requirements
Identity must be verified consistently across all systems.
• Multi-factor authentication, requiring more than one verification factor
• Unique user identification, ensuring accountability for all actions
• Credential management, protecting and rotating passwords and keys
• Session controls, limiting and monitoring active user sessions
Authentication is not a one-time event. It must be enforced continuously.
System and Communications Protection
Sensitive data must be protected at all times.
• Encrypt data in transit, preventing interception during communication
• Encrypt data at rest, protecting stored information from unauthorized access
• Secure network communications, limiting exposure of systems
• Control data flow, restricting how information moves between systems
Data protection is a core requirement across all CMMC levels.
Configuration Management Requirements
Systems must be configured and maintained securely.
• Establish secure baselines, defining approved system configurations
• Control configuration changes, preventing unauthorized modifications
• Patch vulnerabilities, addressing known security issues promptly
• Manage system inventories, tracking all devices and software
Misconfiguration is one of the most common sources of exposure.
Incident Response Requirements
Organizations must be able to detect and respond to security events.
• Develop incident response plans, defining how incidents are handled
• Detect security events, identifying potential threats quickly
• Contain and remediate incidents, limiting impact and restoring systems
• Document incidents, providing records for compliance and improvement
Response capability is evaluated based on execution, not just planning.
Audit and Accountability Requirements
All activity must be tracked and traceable.
• Generate audit logs, capturing user and system activity
• Protect log integrity, ensuring logs cannot be altered
• Review logs regularly, identifying suspicious behavior
• Retain logs for compliance, supporting audits and investigations
Visibility is critical for both security and compliance.
Risk Management Requirements
Organizations must continuously evaluate and reduce risk.
• Conduct risk assessments, identifying vulnerabilities and threats
• Implement mitigation strategies, addressing identified risks
• Monitor risk over time, ensuring controls remain effective
• Update controls as needed, adapting to new threats
Risk management is an ongoing process, not a one-time task.
What Organizations Get Wrong About CMMC Requirements
Most compliance failures are not due to missing controls, but weak enforcement.
We see organizations:
• Over-relying on policies instead of technical controls, creating gaps in enforcement
• Allowing broad access across systems, increasing risk exposure
• Operating with fragmented monitoring, reducing visibility
• Leaving infrastructure exposed, creating attack surface
CMMC is designed to identify these gaps.
Infrastructure Requirements Behind CMMC Compliance
Meeting CMMC requirements requires architectural alignment.
Identity-Centered Access Control
• Multi-factor authentication, ensuring strong user verification
• Role-based access control, limiting access based on job function
• Least privilege enforcement, reducing unnecessary permissions
Controlled and Isolated Environments
• Protects sensitive data, keeping it within secure systems
• Limits lateral movement, reducing breach impact
• Improves containment, isolating incidents effectively
Centralized Monitoring and Visibility
• Consolidates logs, providing a single source of truth
• Improves detection, identifying threats faster
• Supports compliance, enabling audit-ready reporting
How ShieldHQ Supports CMMC Compliance Requirements
ShieldHQ Powered by Dispersive® Stealth Networking enforces the controls required for CMMC at the architectural level.
• Secure workspaces isolate FCI and CUI, preventing unauthorized access and data leakage
• Stealth networking removes infrastructure from discovery, reducing attack surface
• Identity-driven access enforces strict authentication, aligning with Zero Trust principles
• Centralized monitoring provides audit-ready visibility, supporting compliance requirements
This bridges the gap between compliance requirements and operational enforcement.
How Mindcore Technologies Helps You Achieve CMMC Compliance
Mindcore Technologies helps organizations move from documentation to enforceable compliance.
• Assess current environment, identifying gaps in controls and exposure
• Map requirements to systems, aligning architecture with CMMC domains
• Design secure environments, ensuring enforceable access and data protection
• Implement ShieldHQ, reducing exposure and improving control
• Prepare for audits, ensuring readiness for assessment
• Provide ongoing support, maintaining compliance over time
Execution determines whether compliance is sustainable.
Final Takeaway
CMMC compliance requires organizations to implement and enforce security controls across access, identity, data protection, monitoring, and risk management, with requirements increasing based on the sensitivity of the information handled. The framework is designed to ensure that controls are operational and consistently applied, not just documented, which means organizations must align their architecture with compliance requirements rather than relying on policies alone. Companies that treat CMMC as a checklist will face gaps during assessment, while those that enforce controls at the architectural level achieve both compliance and stronger security.
If your organization is preparing for CMMC certification or needs to align its environment with compliance requirements, schedule a free strategy call with Mindcore Technologies to assess your current systems and define a path forward.