CMMC is not a single standard. It is a tiered framework designed to match cybersecurity requirements to the sensitivity of the data an organization handles. The mistake we see most often is treating it as a checklist. It is not. Each level represents a different level of risk, enforcement, and verification.
If your organization is working within the Department of Defense supply chain, your required level is determined by the type of information you handle. The structure is intentional. It ensures that organizations protecting more sensitive data are held to higher standards.
Understanding how the levels are structured is critical because the controls, assessments, and expectations change significantly between them.
Overview of the CMMC Structure
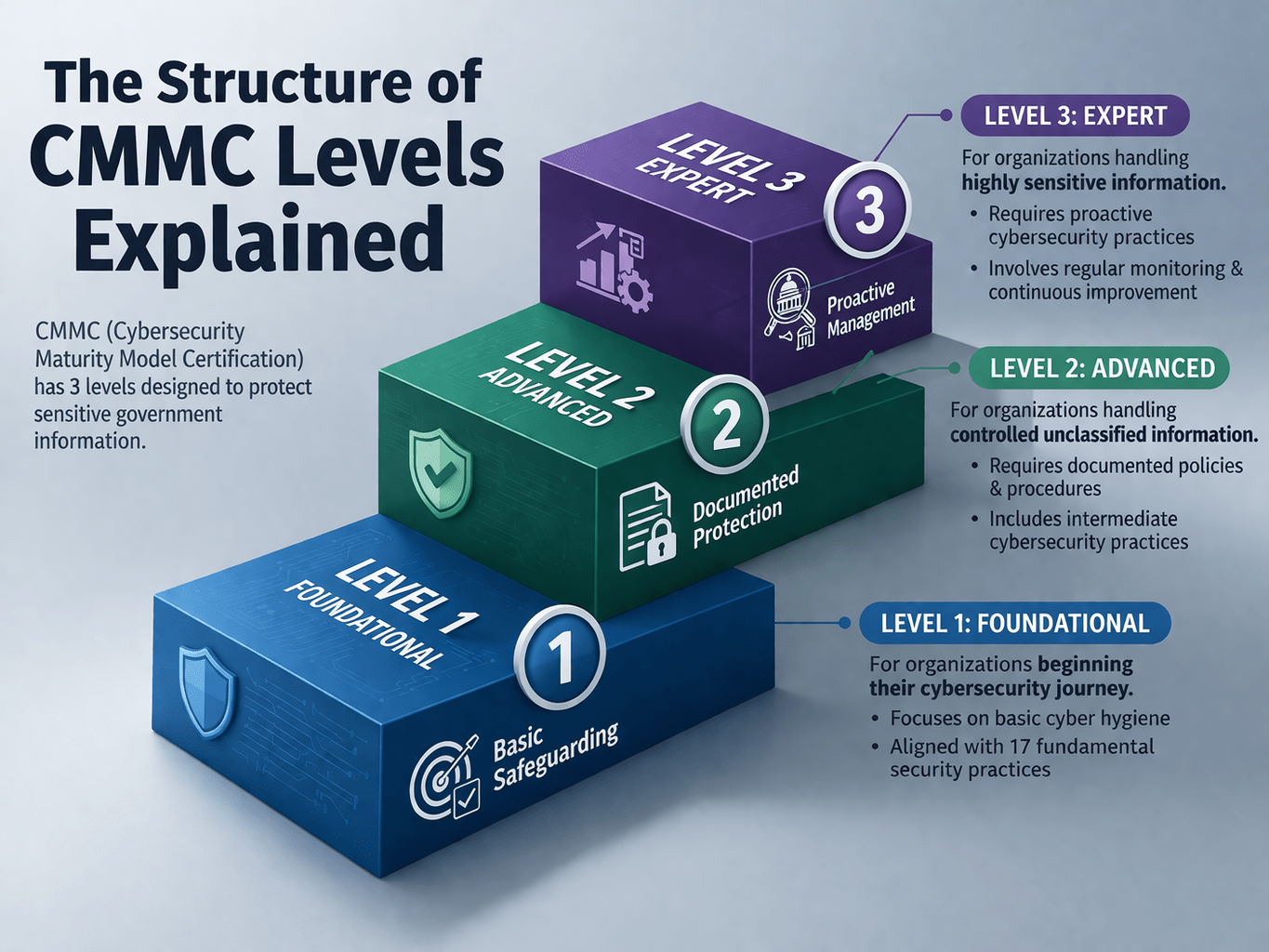
CMMC is divided into three levels, each aligned with increasing security requirements.
• Level 1 focuses on basic safeguarding of Federal Contract Information, FCI
• Level 2 focuses on protecting Controlled Unclassified Information, CUI
• Level 3 focuses on advanced protection against sophisticated threats
Each level builds on the previous one, increasing both control requirements and assessment rigor.
Level 1: Foundational Security (FCI Protection)
Level 1 is the baseline. It applies to organizations that handle Federal Contract Information.
This level focuses on basic cybersecurity practices designed to protect information that is not classified but still sensitive.
Core Requirements
• 17 security practices based on FAR 52.204-21
• Basic access control and system protection
• Protection against unauthorized disclosure of FCI
Assessment Model
• Annual self-assessment
• No third-party certification required
What We See in Practice
Organizations at Level 1 often underestimate the importance of enforcement. Basic controls such as access restriction and system protection must still be consistently applied.
Level 2: Advanced Security (CUI Protection)
Level 2 is where most organizations fall. It applies to those handling Controlled Unclassified Information.
This level aligns directly with NIST SP 800-171 and introduces significantly more stringent requirements.
Core Requirements
• 110 security practices based on NIST SP 800-171
• Strong identity and access control
• Continuous monitoring and logging
• Encryption and data protection
Assessment Model
• Third-party certification through a C3PAO for most contractors
• Some limited cases allow self-assessment
What We See in Practice
This is where gaps become visible. Many organizations have policies in place but lack consistent enforcement. Access is too broad, monitoring is fragmented, and systems remain exposed.
Level 3: Expert Security (Critical Protection)
Level 3 is designed for organizations handling highly sensitive information that could impact national security.
This level builds on Level 2 and incorporates advanced practices from NIST SP 800-172.
Core Requirements
• Advanced threat detection and response capabilities
• Enhanced monitoring and anomaly detection
• Strong system isolation and segmentation
Assessment Model
• Government-led assessments
• Higher scrutiny and validation requirements
What We See in Practice
Level 3 requires mature security architecture. Organizations must demonstrate not just controls, but resilience against advanced threats.
How the Levels Build on Each Other
CMMC levels are cumulative.
• Level 2 includes all Level 1 requirements plus additional controls
• Level 3 includes Level 2 requirements plus advanced protections
This means organizations cannot skip foundational practices. Each level requires full implementation of the previous one.
Key Differences Between the Levels
Scope of Data
• Level 1: FCI only
• Level 2: CUI
• Level 3: Highly sensitive national security data
Control Complexity
• Level 1: Basic safeguards
• Level 2: Comprehensive security controls
• Level 3: Advanced threat protection
Assessment Rigor
• Level 1: Self-assessment
• Level 2: Third-party certification
• Level 3: Government assessment
Why Understanding the Structure Matters
Many organizations approach CMMC without fully understanding where they fall within the structure.
We see companies over-prepare for the wrong level or under-prepare for the required one. Both create risk.
Common issues include:
• Misidentifying whether CUI is present
• Underestimating Level 2 requirements
• Treating compliance as documentation rather than enforcement
• Delaying preparation until contracts require certification
Understanding the structure allows organizations to align their efforts correctly.
What CMMC Requires Beyond the Levels
CMMC is not just about meeting a level. It is about maintaining enforceable controls.
Identity and Access Control
Access must be strictly governed.
• Multi-factor authentication
• Role-based access control
• Least privilege enforcement
System Protection
Data and systems must be secured.
• Encryption at rest and in transit
• Controlled data environments
• Protection against unauthorized access
Monitoring and Visibility
Activity must be tracked and analyzed.
• Centralized logging
• Continuous monitoring
• Incident detection and response
Environment Segmentation
Systems must be isolated.
• Limits exposure of sensitive data
• Prevents lateral movement
• Improves containment
How ShieldHQ Aligns with CMMC Levels
ShieldHQ Powered by Dispersive® Stealth Networking supports organizations across all CMMC levels by enforcing architecture-level controls.
• Secure workspaces isolate FCI and CUI within controlled environments
• Stealth networking removes infrastructure from discovery
• Identity-driven access enforces strict authentication and authorization
• Centralized monitoring provides audit-ready visibility
This aligns compliance requirements with operational enforcement.
How Mindcore Technologies Helps You Navigate CMMC Levels
Mindcore Technologies helps organizations understand their required level and implement the necessary controls.
• Determine which CMMC level applies to your organization
• Identify gaps between current systems and required practices
• Design architecture aligned with NIST and CMMC frameworks
• Implement ShieldHQ for secure environments and controlled access
• Prepare for assessments and certification
• Provide ongoing compliance and security support
Execution ensures that compliance is achieved and maintained.
Final Takeaway
The structure of CMMC is designed to align cybersecurity requirements with the sensitivity of the data an organization handles, with Level 1 focusing on basic protection of Federal Contract Information, Level 2 addressing Controlled Unclassified Information with comprehensive controls, and Level 3 introducing advanced protections for critical national security data. Each level builds on the previous one, increasing both the complexity of controls and the rigor of assessment, which means organizations must fully implement foundational practices before advancing. Understanding where your organization fits within this structure is critical to avoiding gaps in compliance and ensuring that controls are enforceable, not just documented. If your organization is preparing for CMMC certification or needs clarity on which level applies, schedule a free strategy call with Mindcore Technologies to assess your current environment and define a path forward.