An agent that works is not the same as an agent that is enterprise-grade. The difference is governance — the architecture that defines what the agent can do, what it cannot, what requires human approval, and how every action it takes is logged, attributed, and auditable.
Enterprise-grade is not a marketing designation. It is a design standard that determines whether an AI agent is deployable in production environments where autonomous actions have real operational consequences, where audit evidence is required for compliance purposes, and where governance failures produce regulatory exposure rather than just operational inconvenience.
This is what enterprise-grade governance design looks like for Claude Agents.
Overview
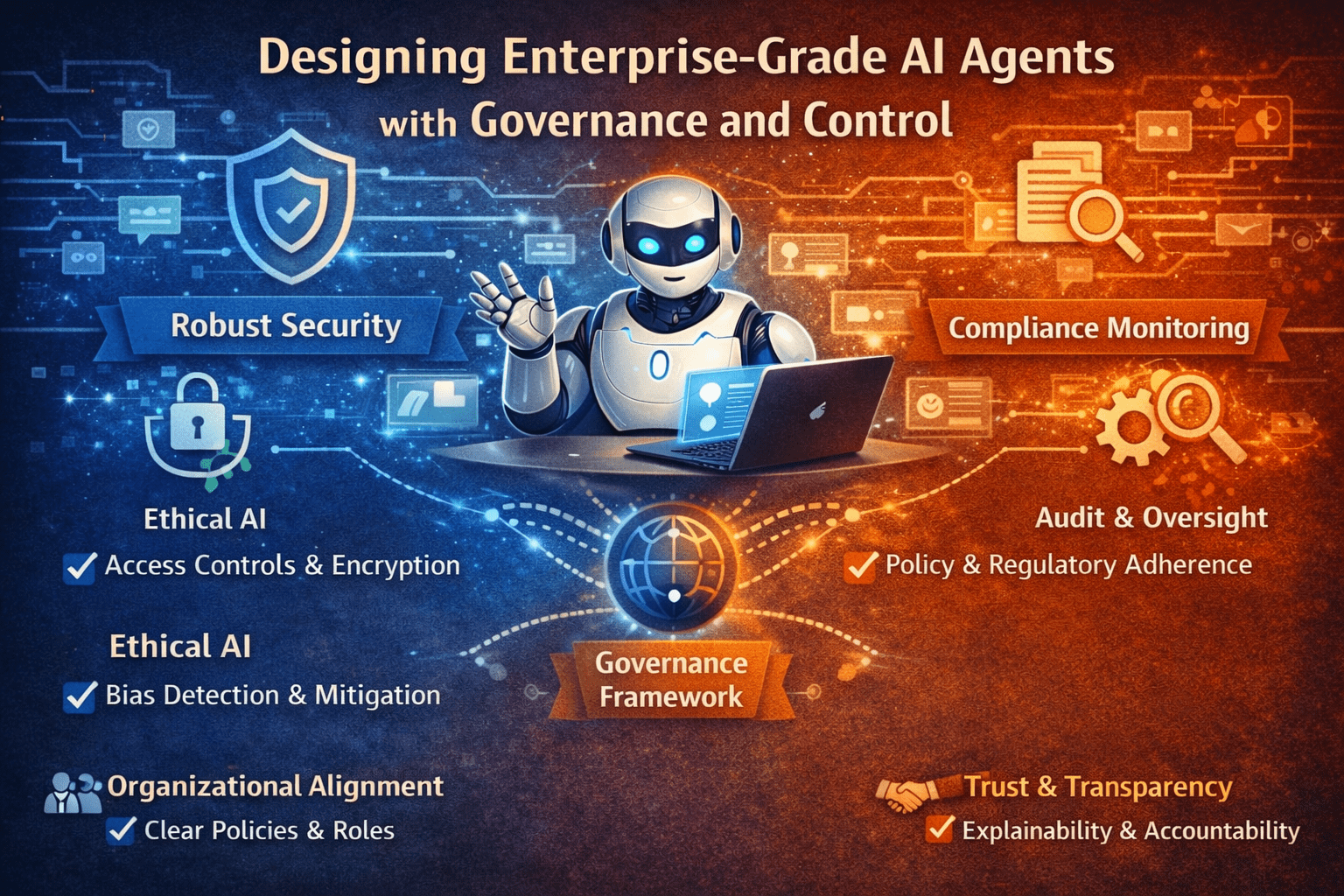
Enterprise-grade AI agent governance covers five design domains: capability governance (what the agent can do), access governance (what it can reach), action governance (what controls apply to its actions), audit governance (what evidence its operations produce), and lifecycle governance (how it is maintained, updated, and deprovisioned). Each domain requires explicit design decisions before deployment. Organizations that make those decisions deliberately build agents that are trustworthy, auditable, and maintainable. Those that skip them build technical debt that surfaces as compliance findings.
- Capability governance defines the scope of what agents are authorized to do — and what is explicitly out of scope
- Access governance applies least-privilege principles to agent system and data access
- Action governance applies tiered authorization to ensure appropriate human oversight for consequential actions
- Audit governance ensures every agent operation produces the evidence that compliance and security require
- Lifecycle governance ensures agents remain correct, current, and appropriately deprovisioned as requirements evolve
The 5 Why’s
- Why is governance design a precondition for enterprise agent deployment, not a post-deployment addition? Governance that is added to an already-deployed agent requires retrofitting controls onto an implementation that was not designed for them — creating gaps, conflicts, and incomplete coverage. Governance designed before implementation is integrated into the agent’s behavior from the first execution. The design sequence is the quality determinant.
- Why does capability scope definition matter beyond access controls? Access controls define what systems and data the agent can reach. Capability scope defines what the agent is authorized to do — which workflows it handles, which action types it takes, and which scenarios it refers to human judgment. An agent that can reach a system but is not authorized to take certain actions in it requires both layers of control to be properly governed.
- Why is tiered action authorization the correct governance model rather than uniform approval requirements? Uniform approval requirements for all agent actions reduce the agent to a recommendation engine — it cannot execute anything without human approval, eliminating the autonomous execution value. Tiered authorization reserves human approval for the action types where it adds genuine governance value — consequential, irreversible, or high-risk actions — while allowing autonomous execution for the routine actions where the approval overhead exceeds the governance benefit.
- Why does audit governance require specification of what the audit record must contain, not just that a record be kept? An audit record that exists but does not contain the information required for compliance review, security investigation, or operational accountability is not a governance control — it is a compliance checkbox. Audit governance specifies the content requirements for each event type so that the records produced meet the actual evidence requirements of the compliance and security functions that will use them.
- Why is lifecycle governance as important as deployment governance? An agent that was correctly governed at deployment becomes incorrectly governed as workflows change, systems update, and organizational requirements evolve — unless lifecycle governance processes update the agent’s configuration, access, and authorization in response to those changes. Lifecycle governance is what keeps the deployment governance correct over time.
The Enterprise-Grade Governance Design Framework
Capability Governance
Capability governance documents what the agent is authorized to do before any implementation begins:
- Authorized workflow list — the specific workflows the agent is authorized to execute, with the triggering conditions for each
- Out-of-scope declarations — explicit statements of what the agent is not authorized to do, even if technically capable
- Escalation criteria — the conditions that trigger human escalation regardless of agent confidence
- Capability change process — the process by which the authorized workflow list can be extended, requiring governance review and approval for each addition
Access Governance
- Workflow access map — documentation of the specific data and system access each authorized workflow requires
- Provisioned access inventory — the access granted, mapped to the workflow requirements that justify it
- Access review schedule — periodic reviews that verify access remains aligned with current workflow requirements
- Access revocation process — the process for revoking access that is no longer required by current workflows
Action Governance
- Action classification inventory — every action type the agent may take, classified by authorization tier
- Tier boundary definitions — explicit criteria for each tier boundary — not general principles but specific definitions of what moves an action from Tier 1 to Tier 2 or Tier 2 to Tier 3
- Approval workflow design — for Tier 3 actions, the approval workflow: who receives the approval request, what information they receive, what their approval window is, and what happens if approval is not received within the window
- Tier 4 action handling — explicit handling for action types that are always outside agent authorization, including logging requirements for any attempt to execute them
Audit Governance
For each event type in agent operations, the audit governance specifies:
- Required fields — the specific data elements that must be captured in the log entry
- Retention period — how long the log entry must be retained, aligned with applicable regulatory and policy requirements
- Access controls — who can access the audit log and under what authorization
- Review requirements — what audit log review is required, on what schedule, by what function
Lifecycle Governance
- Workflow change management — the process by which changes to authorized workflows are reviewed, approved, and implemented — including the access and authorization review that each workflow change triggers
- Performance monitoring — the metrics tracked for agent performance and the thresholds that trigger governance review
- Deprecation process — the process for deprovisioning agents that are no longer required, including access revocation, credential deletion, and audit log retention management
What Enterprise-Grade Governance Produces
- Regulatory defensibility — agent operations are documented, controlled, and auditable against the evidence requirements of applicable regulatory frameworks
- Operational accountability — every agent action is attributable to a defined authorization and a specific triggering event
- Change resilience — lifecycle governance processes keep the deployment governance current as requirements evolve
- Security posture alignment — agent governance integrates with existing enterprise security governance frameworks rather than creating a parallel, separately governed channel
- Trust at scale — governance architecture that makes autonomous operation trustworthy enables agent deployment at the scale the enterprise automation opportunity warrants
Final Takeaway
Enterprise-grade AI agents are defined by governance design as much as by capability design. The capability determines what the agent can do. The governance determines whether it can be trusted to do it in production environments where autonomous actions have real consequences and where audit evidence is a regulatory requirement.
Organizations that design governance alongside capability build agents that are deployable in regulated enterprise environments and maintainable as the environments evolve. Those that treat governance as a post-deployment problem build agents that are limited by the governance debt they accumulate from the first production execution.
Design Enterprise-Grade Claude Agents With Mindcore Technologies
Mindcore Technologies works with enterprise teams to design Claude Agents with full governance architecture — capability scope definition, access governance, action authorization tiers, audit governance specifications, and lifecycle management processes that produce enterprise-grade agents from the first deployment.
Talk to Mindcore Technologies About Enterprise-Grade Claude Agent Design →
Contact our team to assess your agent governance requirements and build the architecture that meets them.