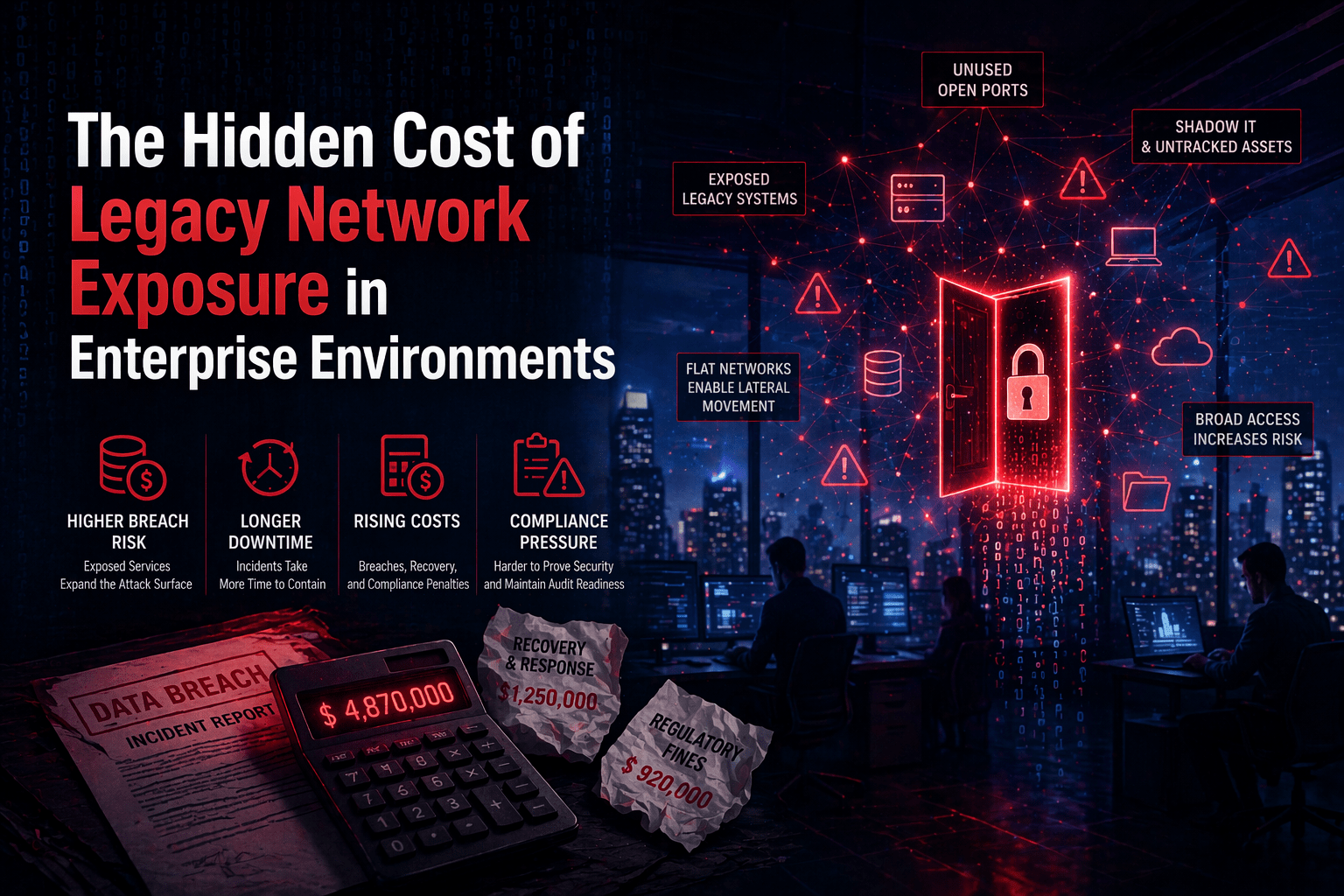
The visible cost of legacy network security is easy to identify: breach incidents that produce direct financial losses, regulatory fines, and recovery expenses. Organizations that have experienced a significant ransomware event or data breach know exactly what the visible cost is, because it shows up in the incident response invoice, the cyber insurance claim, and the revenue lost during recovery.
The hidden costs are different. They accumulate slowly, appear in budget lines that are not labeled “legacy security cost,” and are easy to accept as normal operational overhead because they have always been there. IT support costs that trace to VPN architecture. Compliance preparation costs that trace to audit evidence that was never designed to generate itself. Productivity losses that trace to connectivity friction that no one escalated because everyone assumed it was unavoidable. Insurance premiums that price in risk that better architecture would eliminate.
These hidden costs are real, they are significant at enterprise scale, and they are directly attributable to architectural decisions that modern alternatives resolve.
Overview
Legacy network exposure creates five categories of hidden costs in enterprise environments: operational IT overhead from infrastructure management and user support, compliance friction from evidence compilation that was never designed to be automatic, productivity loss from connectivity friction that distributed workforces absorb daily, insurance premium loading from risk profiles that legacy architecture creates, and opportunity cost from security constraints that prevent operational models a better architecture would enable. Each category represents real budget impact that organizations can quantify against the cost of architectural modernization.
- IT overhead: VPN infrastructure management, certificate lifecycle, connectivity support load
- Compliance friction: pre-assessment evidence compilation, access control verification, policy-to-implementation reconciliation
- Productivity loss: VPN connectivity issues, reconnection events, high-latency remote access
- Insurance premium loading: risk profile pricing from VPN architecture, flat network, absence of containment capability
- Opportunity cost: operational models that legacy security architecture cannot safely enable
This aligns with modern cybersecurity strategies and enterprise cost optimization initiatives.
The 5 Why’s
Why are legacy network security costs typically underestimated in security architecture investment decisions?
Security architecture investment decisions are evaluated against the direct cost of the new architecture — licenses, implementation, ongoing support. Legacy architecture costs are distributed across budget lines that are not labeled as security architecture costs: IT support staffing, compliance preparation labor, productivity tools purchased to work around VPN friction, and insurance premiums that contain security risk loadings that are not broken out separately. The comparison is between a clearly visible new investment and an invisible collection of existing costs.
Why does VPN infrastructure create IT overhead costs that scale with enterprise growth?
VPN infrastructure requires capacity planning as users grow — additional concentrators, additional bandwidth, additional licenses. Certificate lifecycle management requires ongoing IT attention regardless of user count. VPN connectivity support scales with user count because each user represents potential VPN friction events. As the enterprise grows, VPN overhead grows proportionally — it is a cost that compounds with scale rather than benefiting from economies.
Why does pre-assessment compliance evidence compilation represent a significant hidden cost that organizations accept as normal?
Organizations that have been through multiple compliance assessment cycles normalize the pre-assessment sprint — the weeks of log compilation, access control verification, and documentation reconciliation that precede each assessment. That labor cost is real; it represents IT and security staff time that has a fully loaded cost that is rarely attributed to the security architecture that requires it. Architectures that generate evidence continuously eliminate that cost — but organizations that have never experienced continuous evidence generation do not know they are paying for its absence.
Why does distributed workforce connectivity friction represent quantifiable productivity loss that accumulates invisibly?
Individual VPN friction events — reconnections, certificate prompts, performance degradation on high-latency connections — are minor. They are not escalated as productivity issues because they are treated as normal. Aggregated across a distributed workforce at enterprise scale, those minor events represent significant daily productivity loss. The cost is invisible at the individual level, real at the aggregate level, and directly attributable to a VPN architecture that could be replaced.
Why does legacy network architecture load cyber insurance premiums in ways that better architecture reduces?
Cyber insurance underwriters price security architecture characteristics into premiums — VPN-based remote access, flat network architecture, absence of lateral movement containment, and limited breach containment capability are all risk factors that increase premium calculations. Organizations with legacy architecture pay a security risk premium that is embedded in their insurance costs. That premium is a hidden ongoing cost of the architecture; reducing it through architectural improvement produces ongoing savings that reduce the net cost of the architectural investment.
Quantifying the Hidden Cost Categories
IT Overhead Quantification
Calculate annually:
- VPN infrastructure management labor (hours × staff cost per hour)
- Certificate lifecycle management labor
- VPN connectivity support tickets × average ticket cost (fully loaded IT staff cost)
- VPN hardware refresh cost (amortized annual)
- VPN license cost
Compliance Friction Quantification
Calculate per compliance cycle:
- Pre-assessment evidence compilation labor (hours × staff cost) × number of assessments annually
- Access control verification labor (hours × staff cost per cycle)
- Policy-to-implementation reconciliation labor
- Finding remediation cost from access control gaps that better architecture would prevent
Productivity Loss Quantification
Calculate annually:
- Average VPN friction events per user per day × minutes per event × users × working days × average hourly cost
- High-latency performance loss for international users (measurable in productivity surveys)
- IT escalation time for VPN issues that were not resolved by user self-service
Insurance Premium Loading Estimation
Request from insurer:
- Current premium breakdown with security architecture risk factors identified
- Quote comparison for equivalent coverage with improved security architecture documentation
- Coverage gap or exclusion cost attributable to legacy architecture risk factors
The Full Cost Comparison
When hidden costs are fully loaded against legacy architecture and compared to the total cost of ShieldHQ deployment and operation:
- Legacy architecture total cost (visible + hidden) significantly exceeds the commonly cited “we already have VPN” framing
- ShieldHQ total cost of ownership is lower than legacy architecture total cost for most large enterprises when hidden costs are included
- The architectural transition that appears to add cost is actually cost-neutral or cost-positive when the comparison is complete
Final Takeaway
Legacy network exposure has a visible cost and a hidden one. The visible cost shows up in breach incidents that organizations hope to avoid. The hidden cost shows up in budget lines that organizations have accepted as fixed — IT overhead, compliance preparation, productivity loss, insurance premiums, and the opportunity cost of operational models the current architecture cannot safely enable. Making those hidden costs visible is the analysis that converts “we already have something that works” into “we are paying more than we realize for something that is costing us in ways we are not counting.”
This reflects the shift toward modern enterprise security architecture focused on efficiency and risk reduction.
Uncover and Eliminate Legacy Network Costs With Mindcore Technologies
Mindcore Technologies works with enterprise finance, IT, and security teams to quantify the full cost of legacy network architecture — hidden IT overhead, compliance friction, productivity loss, and insurance premium loading — and build the complete cost comparison that accurately frames ShieldHQ investment against the architecture it replaces.
Learn how ShieldHQ reduces hidden operational costs.
Schedule your free strategy call to uncover the true cost of your current architecture.