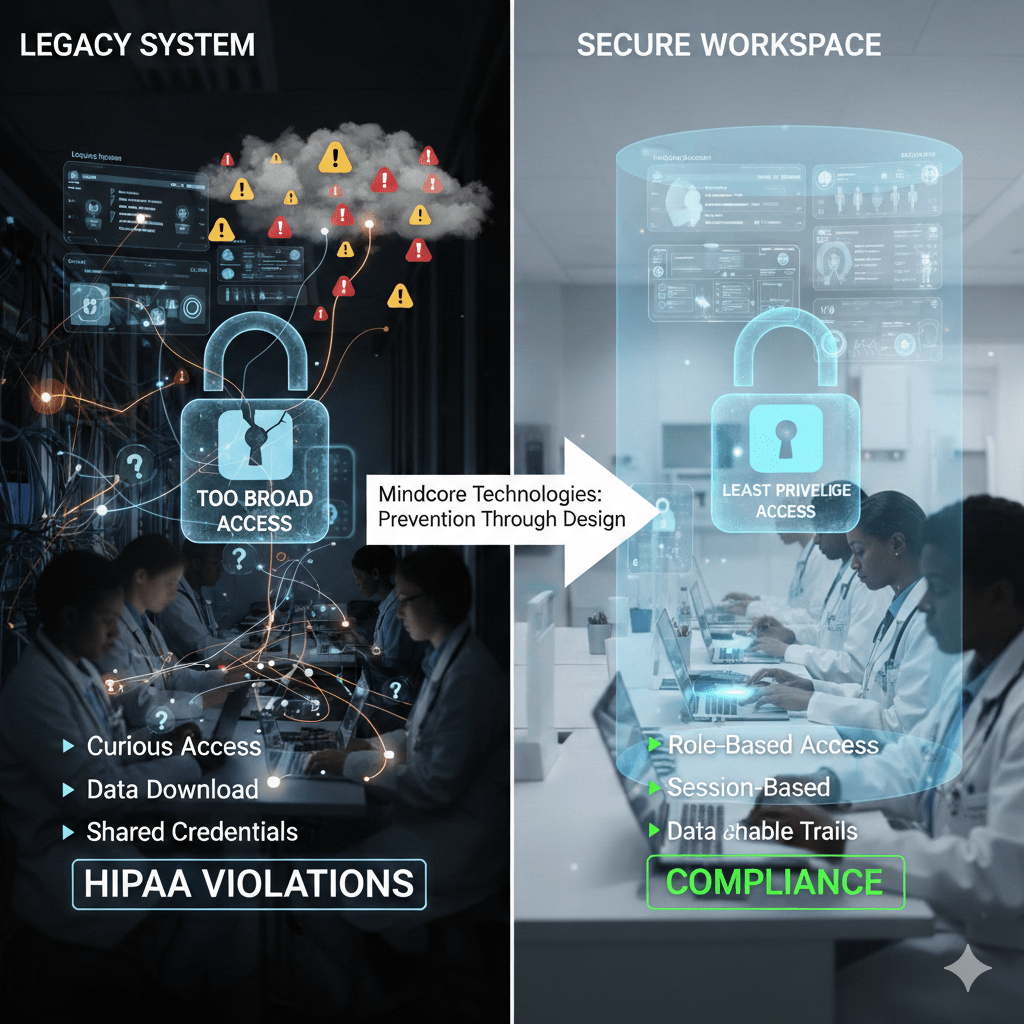
Most insider incidents in healthcare are not malicious. They are structural failures. Access is too broad, sessions last too long, and PHI reaches places it never needed to go. Secure workspaces exist to fix that by removing opportunity, not by policing intent.
At Mindcore Technologies, insider-risk assessments show a consistent pattern: when access is contained and auditable, insider incidents drop sharply without slowing care delivery.
What “Insider Threat” Actually Means in Healthcare
Insider threat is any authorized access that results in unauthorized exposure or misuse of PHI. That includes:
- Curious access
Staff viewing records unrelated to their role or patient assignment. - Convenience-driven workarounds
Downloading data locally, sharing credentials, or bypassing controls to save time. - Privilege misuse
Administrative access used outside of approved purpose. - Compromised insiders
Valid accounts abused after credential theft or session hijacking.
Most of these happen during normal operations, not during attacks.
Why Healthcare Is Especially Vulnerable to Insider Risk
Healthcare environments amplify insider risk because:
- Access must be fast and frequent
Clinicians and staff need continuous availability. - Roles overlap across care, billing, and administration
Permissions accumulate and rarely shrink. - Legacy access models assume trust after login
VPNs and flat networks expose too much. - Audit reviews are periodic, not continuous
Improper access can go unnoticed for months.
Secure workspaces reduce risk by constraining what insiders can do, not by relying on perfect behavior.
How Secure Workspaces Reduce Insider Threat by Design
Secure workspaces change the access model so insider risk is minimized automatically.
They do this by:
- Isolating applications and data inside controlled environments
Users access systems without direct data exposure. - Delivering application-level access only
Insiders cannot browse networks or file systems. - Enforcing session-based access
Access exists only for the duration and purpose approved. - Removing endpoint trust assumptions
Devices become access terminals, not data stores.
This shifts insider threat from a people problem to an architectural one.
Limiting Access Scope to Reduce Misuse
Excessive access is the root of most insider incidents.
Secure workspaces enforce least privilege by:
- Aligning access strictly to job function
Users see only the applications required for their role. - Preventing lateral access to unrelated systems
Curiosity cannot turn into exposure. - Eliminating standing access
Temporary needs do not become permanent permissions.
When access is narrow, misuse opportunities disappear.
Containing PHI to Prevent Accidental Exposure
Accidental exposure is one of the most common insider failures.
Secure workspaces prevent this by:
- Keeping PHI inside the workspace
Data is not downloaded, cached, or synced locally. - Restricting copy, export, and transfer actions
Data movement is controlled and observable. - Reducing reliance on endpoint configuration
Protection does not depend on perfect devices.
This dramatically reduces unintentional HIPAA violations.
Improving Accountability Without Surveillance
Insider threat programs often fail when they feel punitive.
Secure workspaces improve accountability by:
- Providing clear session-level audit trails
Who accessed what, when, and for how long is visible. - Separating intent from opportunity
Controls limit exposure without assuming bad faith. - Supporting defensible investigations
Evidence is consistent and centralized.
Transparency replaces suspicion.
Reducing Vendor and Contractor Insider Risk
Third-party access is a major insider risk vector.
Secure workspaces help by:
- Scoping vendor access to specific applications
Vendors cannot explore internal environments. - Enforcing time-bound access
Access expires automatically when work is complete. - Preventing data extraction to vendor devices
PHI remains inside controlled environments. - Maintaining full auditability
Vendor activity is visible and reviewable.
This limits shared risk without blocking necessary access.
Insider Threat Reduction and HIPAA Alignment
HIPAA expects organizations to minimize exposure and prove control.
Secure workspaces support this by:
- Enforcing minimum necessary access automatically
Access aligns with role and purpose. - Preventing uncontrolled PHI duplication
Data stays in approved environments. - Providing clear audit evidence
Activity is traceable without manual reconstruction.
Insider risk reduction becomes a compliance outcome, not an extra program.
Why Detection Alone Is Not Enough
Many organizations rely on monitoring tools to catch insiders.
That approach fails because:
- Alerts trigger after access already occurred
- Normal activity blends with misuse
- Investigations are slow and subjective
Secure workspaces remove the conditions that make insider misuse possible, reducing the need for reactive detection.
How Mindcore Technologies Implements Secure Workspaces to Reduce Insider Risk
Mindcore reduces insider threat exposure by:
- Mapping real-world access needs
Controls reflect how healthcare teams actually work. - Replacing VPN-based access with secure workspaces
Network exposure is removed. - Defining role-based, session-based access
Permissions are narrow and temporary. - Containing PHI inside controlled environments
Data does not sprawl to endpoints or vendors. - Centralizing visibility for audit and response
Security and compliance teams share a single view.
The goal is prevention through design, not punishment through policy.
A Simple Insider Risk Reality Check
Your insider risk remains high if:
- Users can access PHI outside their role
- Data can be downloaded freely
- VPNs provide broad internal access
- Vendor access is persistent
- Audit evidence is manual
These are architectural risks, not behavior problems.
Final Takeaway
Insider threats in healthcare are rarely about bad actors. They are about bad access models. Secure workspaces reduce insider risk by limiting scope, containing data, and enforcing accountability automatically.
Healthcare organizations that adopt secure workspaces reduce HIPAA exposure, simplify audits, and protect patient trust without disrupting care. Those that rely on policy and monitoring alone leave too much to chance.