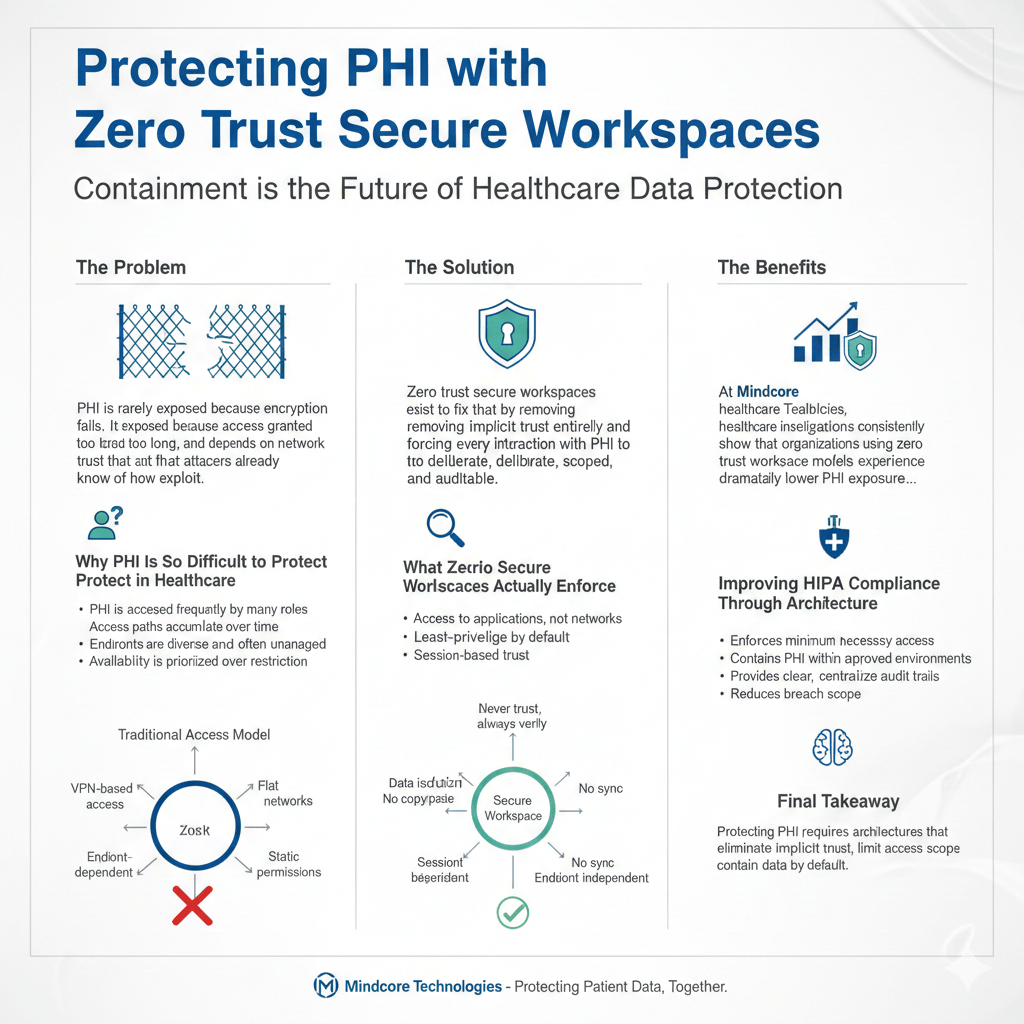
PHI is rarely exposed because encryption fails. It is exposed because access is granted too broadly, persists too long, and depends on network trust that attackers already know how to exploit. Once access exists, traditional environments struggle to contain misuse, mistakes, or compromise.
Zero trust secure workspaces exist to fix that by removing implicit trust entirely and forcing every interaction with PHI to be deliberate, scoped, and auditable.
At Mindcore Technologies, healthcare breach investigations consistently show that organizations using zero trust workspace models experience dramatically lower PHI exposure, even when credentials are compromised or endpoints fail.
Why PHI Is So Difficult to Protect in Healthcare
Healthcare environments face unique challenges that make PHI protection difficult:
- PHI is accessed frequently by many roles
Clinicians, billing teams, administrators, and vendors all touch sensitive systems. - Access paths accumulate over time
Temporary access often becomes permanent. - Endpoints are diverse and often unmanaged
Home devices, shared workstations, and legacy systems increase risk. - Availability is prioritized over restriction
Care delivery cannot stop for security friction.
Traditional security models trade control for convenience, and PHI pays the price.
How Traditional Access Models Expose PHI
Most PHI exposure happens after authentication.
Common failure points include:
- VPN-based access models
Once connected, users inherit broad internal visibility. - Flat or loosely segmented networks
PHI systems are reachable from many locations. - Endpoint-dependent controls
Data protection assumes devices are secure and compliant. - Static permissions
Access rarely expires automatically.
These models assume trust instead of enforcing it continuously.
What Zero Trust Secure Workspaces Actually Enforce
Zero trust secure workspaces apply zero trust principles at the access and data layer, not just identity.
They enforce:
- Never trust, always verify
Every session requires identity validation and authorization. - Access to applications, not networks
Users never see infrastructure or IP space. - Least-privilege by default
Access is scoped to exact roles and tasks. - Session-based trust
Access expires automatically.
Trust is earned per session, not inherited.
Containing PHI Inside Secure Workspaces
PHI exposure drops sharply when data stops leaving controlled environments.
Secure workspaces protect PHI by:
- Keeping data inside isolated environments
PHI is not stored on endpoints. - Restricting copy, paste, download, and export actions
Data movement is controlled and logged. - Preventing background syncing or shadow copies
PHI does not leak into personal storage or email. - Reducing reliance on endpoint security posture
Protection does not depend on perfect devices.
Containment turns data access into data protection.
Stopping Lateral Movement Toward PHI Systems
Once attackers reach PHI systems, damage escalates quickly.
Zero trust workspaces stop this by:
- Eliminating internal network visibility
Systems cannot be discovered or scanned. - Preventing pivoting between applications
Access is isolated per workflow. - Blocking privilege escalation paths
Credentials do not unlock additional systems. - Allowing instant session termination
Access can be revoked immediately.
Attackers lose the ability to move and expand.
Reducing Insider and Accidental PHI Exposure
Most PHI violations are accidental.
Zero trust secure workspaces reduce this risk by:
- Aligning access strictly to job function
Users cannot access unrelated patient records. - Removing standing access privileges
Temporary needs do not become permanent risk. - Providing session-level accountability
Activity is traceable without intrusive monitoring. - Preventing local data handling
PHI never touches unmanaged environments.
Opportunity for mistakes is removed by design.
Securing PHI Access for Remote and Distributed Teams
Remote access is now standard in healthcare.
Zero trust secure workspaces protect PHI remotely by:
- Eliminating VPN-based network access
Remote users never join internal networks. - Delivering consistent access from any location
Security does not depend on geography. - Enforcing the same controls everywhere
Home, clinic, or vendor location makes no difference. - Reducing credential blast radius
One compromise affects one workspace, not the enterprise.
Remote work stops increasing PHI risk.
Improving HIPAA Compliance Through Architecture
HIPAA requires minimum necessary access and demonstrable safeguards.
Zero trust secure workspaces support this by:
- Enforcing minimum necessary access automatically
Permissions are narrow and provable. - Containing PHI within approved environments
Data location is controlled. - Providing clear, centralized audit trails
Access is identity-verified and time-bound. - Reducing breach scope and notification complexity
Fewer systems and records are involved.
Compliance becomes a natural outcome, not a manual effort.
Why Detection Alone Cannot Protect PHI
Monitoring tools alert after PHI has already been accessed.
They fail because:
- Alerts trigger post-access
- Normal user behavior masks misuse
- Response depends on human speed
Zero trust secure workspaces reduce reliance on detection by preventing uncontrolled access in the first place.
How Mindcore Technologies Protects PHI with Zero Trust Secure Workspaces
Mindcore protects PHI by:
- Identifying excessive access paths and trust assumptions
Mapping where PHI is reachable today. - Implementing zero trust secure workspace architecture
Removing network-based trust. - Designing role-based, session-limited access models
Aligning access with healthcare workflows. - Containing PHI inside controlled environments
Preventing sprawl and misuse. - Centralizing visibility and audit readiness
Supporting compliance and security teams together.
The objective is PHI protection through containment, not restriction through policy.
A Simple PHI Protection Reality Check
Your PHI remains high-risk if:
- VPNs provide access to PHI systems
- PHI exists on endpoints
- Access permissions rarely expire
- Users can reach multiple PHI systems
- Audit evidence requires reconstruction
These are architectural failures, not training gaps.
Final Takeaway
Protecting PHI requires more than encryption and awareness training. It requires architectures that eliminate implicit trust, limit access scope, and contain data by default.
Zero trust secure workspaces give healthcare organizations the ability to protect patient data even when credentials are compromised or devices fail. Organizations that adopt them reduce breach impact, simplify HIPAA compliance, and protect patient trust at scale. Those that do not remain exposed through access models attackers already understand.