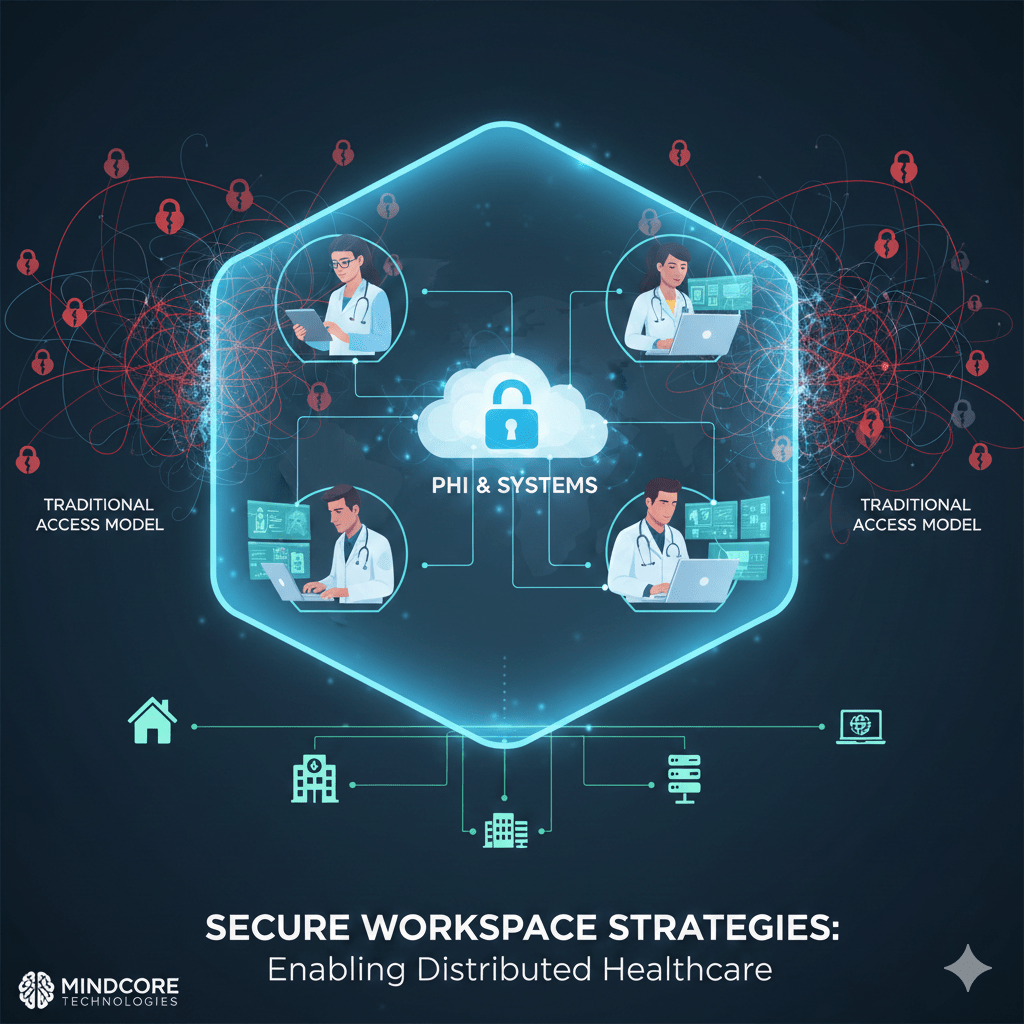
Distributed healthcare teams do not fail because staff work remotely. They fail because traditional access models assume location-based trust in a locationless world. VPNs, endpoint-dependent controls, and flat networks collapse when clinicians, administrators, and vendors work across homes, clinics, and partner sites.
Secure workspace strategies exist to fix this by removing network trust entirely and delivering access that is identity-driven, contained, and auditable.
At Mindcore Technologies, healthcare environments that adopt secure workspace architectures consistently show fewer access-related incidents, faster containment during events, and significantly lower HIPAA exposure across distributed teams.
Why Distributed Healthcare Teams Increase Risk by Default
Healthcare operations are increasingly distributed across:
- Remote clinicians and care coordinators
Accessing EHR and clinical tools from non-clinical locations. - Hybrid administrative and billing teams
Working across office, home, and shared environments. - Telehealth providers and support staff
Requiring constant, real-time access to patient systems. - Vendors and third parties
Supporting systems remotely with elevated privileges.
Traditional security models were not designed for this level of dispersion.
Where Traditional Access Models Break Down
Most healthcare organizations rely on access models that fail under distribution.
Common breakdowns include:
- VPNs that extend full network trust
One compromised credential exposes internal systems. - Endpoint-dependent security controls
Protection assumes devices are fully managed and compliant. - Static access permissions
Roles change, but access rarely shrinks. - Fragmented visibility
Activity is spread across tools and teams.
Distribution amplifies these weaknesses instead of hiding them.
What Secure Workspace Strategy Actually Means
A secure workspace strategy is not a tool. It is an access architecture.
It means:
- Users never join internal networks
They access applications, not infrastructure. - Access is delivered through isolated environments
PHI and systems remain inside controlled workspaces. - Trust is identity-based and session-limited
Not tied to device or location. - Visibility is centralized and consistent
Every session is auditable.
This model scales cleanly as teams spread geographically.
Containing PHI for Remote and Hybrid Teams
PHI sprawl is the biggest risk in distributed environments.
Secure workspaces reduce it by:
- Keeping PHI inside the workspace
Data is not downloaded or cached locally. - Restricting copy, paste, and export actions
Data movement is controlled and logged. - Decoupling data security from endpoint security
Even unmanaged devices cannot store PHI. - Preventing shadow IT data creation
Files do not leak into personal systems.
This containment holds regardless of where users work.
Eliminating VPN Risk Across Distributed Teams
VPNs create more problems than they solve in healthcare.
Secure workspace strategies eliminate VPN risk by:
- Removing network-level access entirely
Users never see internal IP space. - Delivering application-specific access
Only approved systems are reachable. - Using ephemeral sessions
Access ends automatically when work stops. - Reducing credential blast radius
Compromise affects one workspace, not the network.
Remote access becomes safer and simpler.
Supporting Clinical Productivity Without Sacrificing Security
Security often fails when it slows care delivery.
Secure workspaces support productivity by:
- Providing consistent access from any location
Users do not troubleshoot VPNs or network issues. - Reducing login friction through identity-based access
Authentication is strong but predictable. - Preserving application performance
Workspaces are optimized for clinical workloads. - Allowing fast access revocation without disruption
Sessions can be ended without shutting down systems.
Security stops being an obstacle to care.
Reducing Insider Risk in Distributed Teams
Distributed teams increase insider risk unintentionally.
Secure workspaces reduce this by:
- Aligning access strictly to role and task
Users cannot reach unrelated systems. - Eliminating standing privileges
Access exists only when needed. - Providing session-level accountability
Activity is clearly attributed and logged. - Preventing data exfiltration paths
PHI cannot be quietly copied or synced.
Opportunity for misuse is removed by design.
Securing Vendor and Third-Party Access Remotely
Third-party access becomes more dangerous when teams are distributed.
Secure workspace strategies protect against this by:
- Replacing vendor VPN access with workspace-based access
Vendors never join internal networks. - Scoping access to specific applications or devices
No lateral movement is possible. - Enforcing time-bound access automatically
Access expires when work is complete. - Maintaining full audit trails
Vendor activity is visible and reviewable.
Vendor enablement no longer equals vendor risk.
Maintaining HIPAA Alignment Across Locations
HIPAA does not change because teams are remote.
Secure workspace strategies support compliance by:
- Enforcing minimum necessary access automatically
Permissions are narrow and provable. - Containing PHI inside approved environments
Data location is controlled. - Providing defensible audit evidence
Access records are clear and centralized. - Reducing breach scope
Incidents affect fewer systems and records.
Compliance becomes easier as teams distribute.
Why Detection-Only Approaches Fail for Distributed Teams
Monitoring tools struggle in distributed environments because:
- Alerts trigger after access already occurred
- Normal remote behavior blends with misuse
- Response time depends on human action
Secure workspaces reduce reliance on detection by preventing widespread access in the first place.
How Mindcore Technologies Implements Secure Workspace Strategies for Distributed Healthcare Teams
Mindcore helps distributed healthcare teams by:
- Assessing current access models and trust assumptions
Identifying where distribution increases risk. - Replacing VPN and network-based access with secure workspaces
Removing internal exposure. - Designing role-based, session-limited access
Aligning access with real workflows. - Containing PHI inside controlled environments
Preventing data sprawl across locations. - Centralizing visibility and audit readiness
Supporting security and compliance teams.
The goal is enabling distributed work without distributed risk.
A Simple Distributed Team Risk Check
Your distributed healthcare environment remains high-risk if:
- VPNs provide internal network access
- PHI exists on endpoints
- Vendor access is persistent
- Access permissions rarely expire
- Audit evidence is manual
These conditions do not scale safely.
Final Takeaway
Distributed healthcare teams are here to stay. Security models built on location-based trust are not.
Secure workspace strategies give healthcare organizations the ability to protect PHI, reduce ransomware and insider risk, and maintain HIPAA alignment no matter where teams work. Organizations that adopt them scale safely. Those that do not inherit risk with every new remote user.