Healthcare enterprises do not suffer from a lack of security tools. They suffer from fragmented architecture. Firewalls, endpoint agents, VPNs, MFA apps, SIEM dashboards, and compliance spreadsheets exist in most organizations. What is missing is structural containment, enforcement discipline, and governance integration.
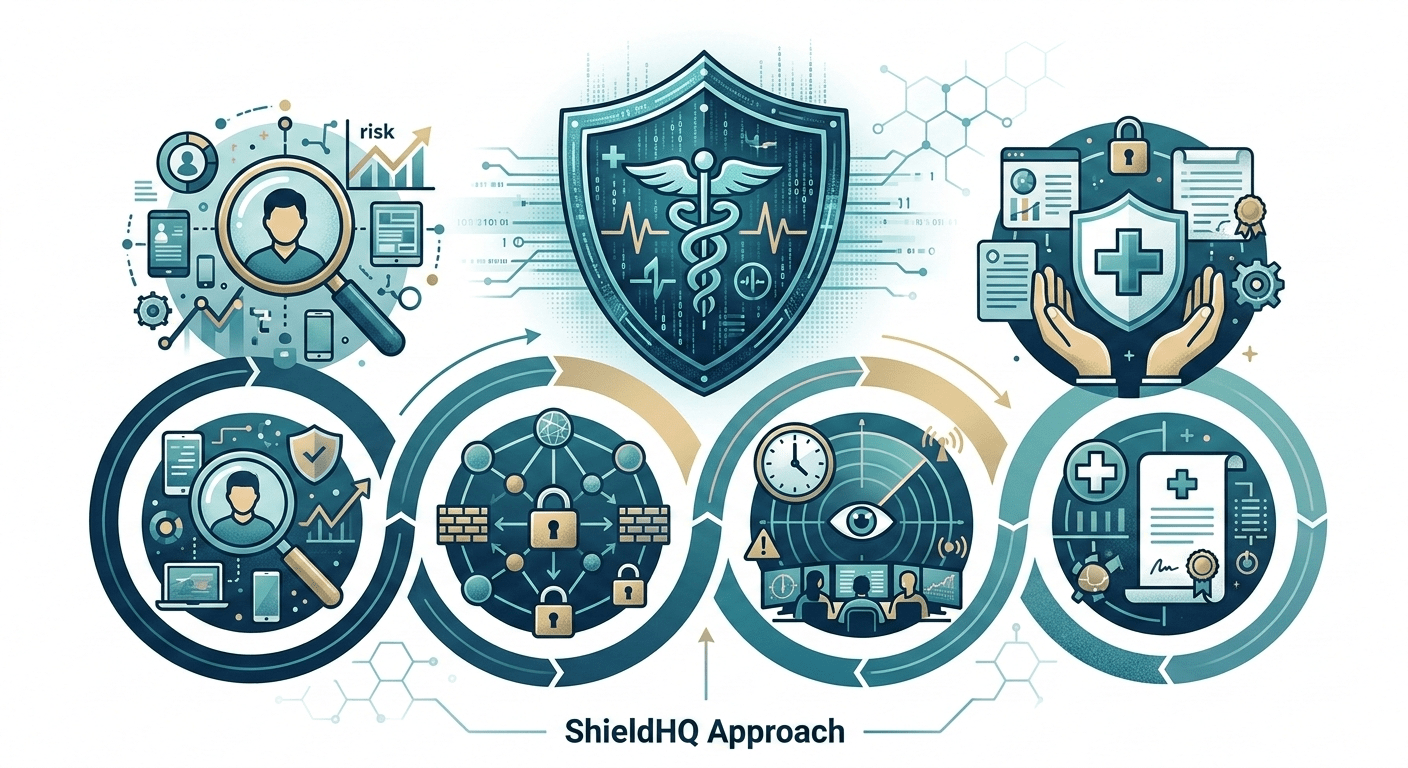
The ShieldHQ for Enterprise Healthcare: Complete Compliance and Security Platform was designed for organizations that understand cybersecurity is not a checklist. It is infrastructure. It is governance. It is executive accountability.
Serious healthcare organizations require serious architecture.
Principle 1: Containment Before Detection
Traditional security attempts to detect threats after perimeter entry. ShieldHQ Powered by Dispersive® Stealth Networking begins by limiting blast radius.
• Segment sensitive clinical workloads into secure enclaves
Prevent lateral spread.
• Isolate backup environments from production networks
Protect recovery continuity.
• Create dedicated vendor access zones
Restrict third-party visibility.
• Separate administrative, research, and operational systems
Minimize cross-department exposure.
Architectural comparison with legacy perimeter models is detailed in ShieldHQ vs. Traditional Healthcare Security: Enterprise Comparison.
Containment reduces severity even when intrusion occurs.
Principle 2: Identity Is the Primary Control Layer
Healthcare breaches most often originate from compromised credentials.
ShieldHQ enforces:
• Enterprise-wide phishing-resistant MFA
Eliminate replay and token fatigue exposure.
• Automated Role-Based Access Control (RBAC)
Align privileges with job responsibility.
• Privilege lifecycle automation
Remove access immediately upon role change.
• Continuous login anomaly detection
Identify abnormal authentication behavior in real time.
Workforce-scale enforcement is structured through ShieldHQ Implementation Guide for Healthcare Organizations Over 500 Employees.
Identity governance discipline is non-negotiable in enterprise healthcare.
Principle 3: Visibility Must Be Centralized and Actionable
Fragmented logs create blind spots.
ShieldHQ consolidates visibility through:
• Enterprise-wide SIEM integration
Centralize hybrid system logs.
• AI-driven anomaly detection engines
Detect abnormal behavior instantly.
• Executive compliance dashboards
Provide board-level transparency.
• Automated documentation workflows
Simplify audit defensibility.
These visibility improvements address executive uncertainty described in Healthcare Compliance Challenges ShieldHQ Solves for Executives.
Principle 4: Vendor Risk Is Structural Risk
Third-party exposure cannot be treated as secondary.
ShieldHQ enforces:
• Structured Business Associate Agreement oversight
Maintain contractual compliance alignment.
• Segmented vendor network pathways
Limit systemic exposure.
• Continuous vendor session monitoring
Detect suspicious activity.
• Annual vendor risk reassessment cycles
Identify evolving vulnerabilities.
Vendor governance strengthens executive confidence themes described in How Healthcare Executives Build Trust with ShieldHQ Professional Solutions.
Principle 5: Compliance Is Architectural, Not Administrative
Compliance fails when it depends on spreadsheets.
ShieldHQ integrates compliance into infrastructure:
• Automated log retention enforcement
Maintain timestamp integrity.
• Encryption enforcement verification workflows
Confirm PHI protection.
• Quarterly compliance reporting cycles
Support governance rhythm.
• Incident response documentation automation
Strengthen regulatory defensibility.
These enforcement mechanisms align with the broader framework defined in ShieldHQ Enterprise Solutions: Comprehensive Healthcare Security Guide.
Designed for Enterprise Healthcare Scale
Serious healthcare organizations managing 500+ employees require:
• Multi-facility segmentation consistency
• Hybrid cloud monitoring integration
• Workforce-wide identity governance coverage
• High-volume log ingestion scalability
• Governance-aligned reporting automation
These scalability standards guide evaluation decisions in How to Choose ShieldHQ for Your Healthcare Organization’s Compliance Needs.
Operational Outcomes of the ShieldHQ Approach
Healthcare enterprises implementing the ShieldHQ model observe:
• Reduced lateral movement exposure
• Faster anomaly detection cycles
• Lower audit preparation strain
• Increased regulatory defensibility
• Stronger board reporting clarity
• Improved cyber insurance positioning
The approach transforms cybersecurity from reactive IT maintenance into structured enterprise architecture.
Common Weaknesses the ShieldHQ Approach Eliminates
• Flat network architecture
• Perimeter-only defense strategies
• Inconsistent MFA enforcement
• Manual compliance documentation
• Broad vendor VPN access
• Fragmented monitoring systems
Replacing these weaknesses with structural enforcement reduces executive uncertainty.
Sustaining Serious Security Discipline
Long-term resilience requires institutional rhythm.
• Quarterly executive cybersecurity briefings
• Annual infrastructure modernization assessments
• Quarterly access governance audits
• Continuous AI-driven anomaly monitoring
• Annual vendor reassessment cycles
When discipline becomes systemic, compliance becomes sustainable.
Key Takeaways
The ShieldHQ Powered by Dispersive® Stealth Networking approach replaces fragmented security tooling with containment-driven architecture, phishing-resistant identity governance, centralized AI-powered anomaly detection, structured vendor risk discipline, and governance-aligned compliance automation. Designed specifically for enterprise healthcare environments, ShieldHQ transforms cybersecurity into enforceable infrastructure that reduces systemic exposure, strengthens regulatory defensibility, and sustains executive-level confidence for serious organizations facing serious risk.