Implementing enterprise-grade cybersecurity inside a healthcare organization with more than 500 employees is not a software deployment. It is an infrastructure transformation. Large healthcare environments include multiple facilities, hybrid cloud systems, imaging platforms, billing systems, EHR integrations, and extensive vendor connections. Each component must be evaluated, segmented, and governed systematically.
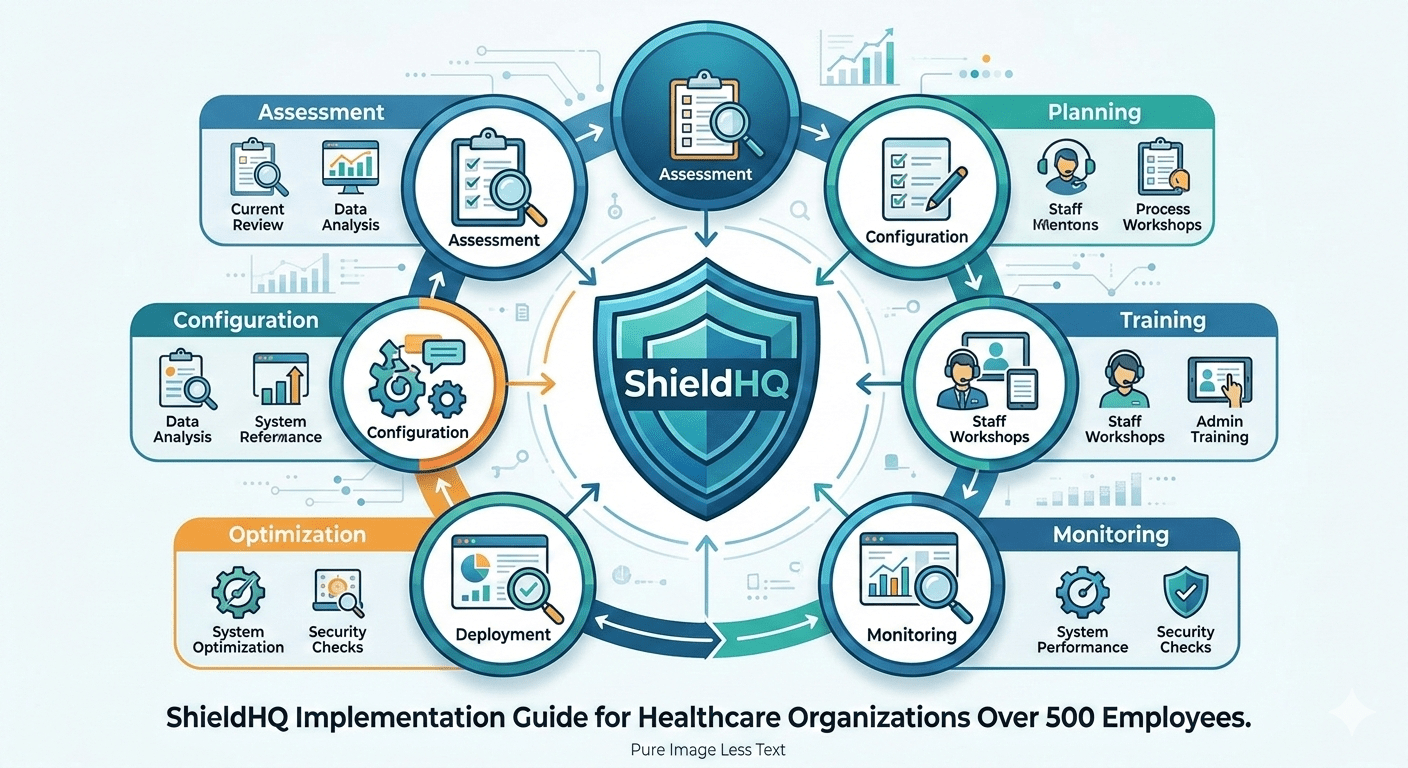
ShieldHQ for Enterprise Healthcare: Complete Compliance and Security Platform is designed for structured rollout across complex environments. Successful implementation requires sequencing, governance alignment, and executive oversight.
Phase 1: Infrastructure Assessment and Risk Mapping
Before deployment begins, organizations must understand exposure points.
• Map all PHI data flows across departments
Identify sensitive workload concentration.
• Audit existing network segmentation gaps
Detect lateral movement risk.
• Review vendor access pathways
Assess third-party exposure.
• Evaluate identity governance enforcement coverage
Identify MFA and RBAC inconsistencies.
This foundational assessment aligns with evaluation principles described in How to Choose ShieldHQ for Your Healthcare Organization’s Compliance Needs.
Phase 2: Segmentation and Containment Architecture Deployment
Containment must precede visibility enhancements.
• Establish secure enclaves for clinical workloads
Isolate high-risk systems.
• Segment administrative and research environments
Prevent cross-department compromise.
• Isolate backup infrastructure from production systems
Protect disaster recovery integrity.
• Create segmented vendor access zones
Restrict unnecessary visibility.
This architectural shift differentiates ShieldHQ from legacy perimeter models discussed in ShieldHQ vs. Traditional Healthcare Security: Enterprise Comparison.
Phase 3: Enterprise-Wide Identity Governance Enforcement
Identity discipline must scale across the workforce.
• Deploy phishing-resistant MFA for all employees
Eliminate credential replay exposure.
• Implement automated Role-Based Access Control (RBAC)
Align access with job responsibilities.
• Automate privilege lifecycle management workflows
Remove orphaned credentials instantly.
• Enable continuous login anomaly monitoring
Detect suspicious authentication behavior.
Workforce-scale enforcement strengthens resilience themes detailed in ShieldHQ Enterprise Solutions: Comprehensive Healthcare Security Guide.
Phase 4: Centralized Monitoring and AI Integration
Visibility must operate in real time.
• Integrate logs into centralized SIEM environment
Consolidate hybrid system activity.
• Activate AI-powered anomaly detection engines
Identify abnormal file transfers and configuration drift.
• Enable executive compliance dashboards
Provide board-ready reporting.
• Automate documentation workflows for audit readiness
Reduce manual reporting burden.
These improvements directly address leadership concerns highlighted in Healthcare Compliance Challenges ShieldHQ Solves for Executives.
Phase 5: Vendor Governance Integration
Third-party exposure requires structured control.
• Validate all Business Associate Agreements
Confirm regulatory alignment.
• Restrict vendor session privileges to segmented zones
Reduce systemic exposure.
• Enable continuous vendor session monitoring
Detect abnormal activity.
• Establish annual vendor reassessment cycle
Identify evolving vulnerabilities.
Vendor discipline reinforces the serious modernization philosophy in The ShieldHQ Approach: Serious Healthcare Security for Serious Organizations.
Phase 6: Executive Governance and Reporting Integration
Implementation must align with leadership oversight.
• Establish quarterly cybersecurity briefings
Review anomaly trends and safeguard coverage.
• Integrate compliance metrics into board reporting
Strengthen governance transparency.
• Validate encryption enforcement coverage quarterly
Confirm PHI protection consistency.
• Conduct annual enterprise-wide risk reassessments
Sustain modernization momentum.
Executive reporting clarity supports trust-building themes described in How Healthcare Executives Build Trust with ShieldHQ Professional Solutions.
Scalability Considerations for 500+ Employee Environments
Large healthcare enterprises must account for:
• Multi-facility deployment synchronization
• High-volume log ingestion scalability
• Hybrid cloud infrastructure compatibility
• Workforce-wide MFA enforcement logistics
• Cross-department RBAC consistency
ShieldHQ’s architecture is engineered to scale without compromising containment integrity or visibility discipline.
Common Implementation Pitfalls to Avoid
• Deploying segmentation after identity enforcement
• Failing to isolate backup systems early
• Allowing vendor access during transition without segmentation
• Delaying executive reporting integration
• Underestimating workforce-wide MFA rollout planning
Structured sequencing prevents operational disruption.
Operational Outcomes After Full Implementation
Healthcare enterprises typically observe:
• Reduced lateral movement exposure
• Faster anomaly detection
• Simplified audit preparation
• Increased executive reporting clarity
• Lower cyber insurance friction
• Stronger regulatory defensibility
Implementation transforms compliance from documentation into architecture.
Key Takeaways
Implementing ShieldHQ Powered by Dispersive® Stealth Networking in healthcare organizations with over 500 employees requires structured sequencing across containment architecture, phishing-resistant identity governance, centralized AI-driven monitoring, vendor risk discipline, and executive reporting integration. When deployed methodically, ShieldHQ modernizes infrastructure, reduces systemic exposure, strengthens audit defensibility, and delivers scalable compliance enforcement aligned with enterprise healthcare complexity.