Healthcare enterprises that rely on traditional perimeter defenses are operating with outdated assumptions. Firewalls, antivirus platforms, and VPN-based remote access were built for centralized environments. Enterprise healthcare today is distributed, hybrid, and deeply integrated with third-party vendors. The attack surface is no longer at the perimeter. It is everywhere.
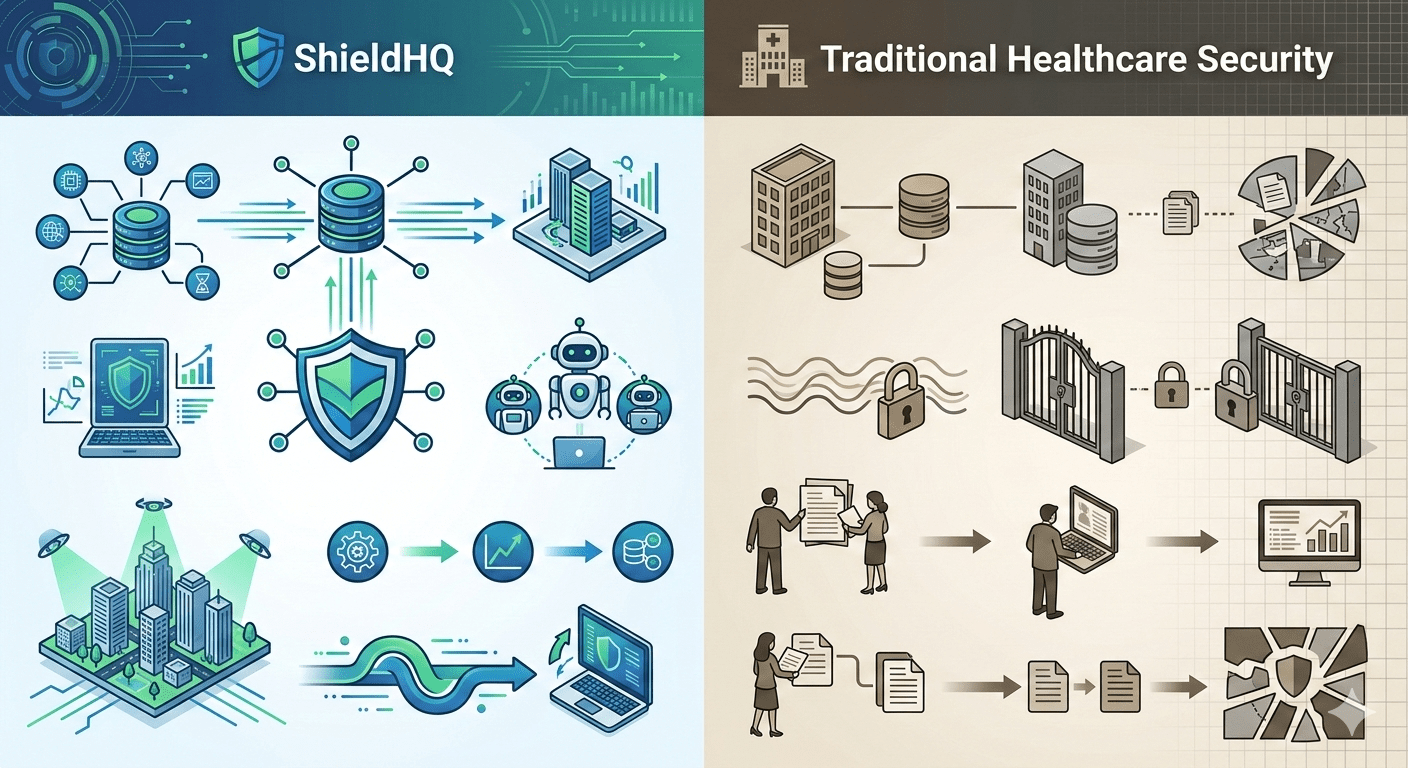
The distinction between ShieldHQ Enterprise Solutions: Comprehensive Healthcare Security Guide and traditional healthcare security models is architectural. ShieldHQ Powered by Dispersive® Stealth Networking is designed around containment, zero-trust enforcement, identity governance automation, and centralized executive visibility. Traditional models focus primarily on boundary defense and reactive monitoring.
Understanding this difference is critical for leadership evaluating modernization decisions within ShieldHQ for Enterprise Healthcare: Complete Compliance and Security Platform.
Traditional Healthcare Security Model
Traditional approaches rely on boundary-based defense strategies.
• Perimeter firewall reinforcement
Focuses on blocking external threats.
• Flat internal network design
Allows unrestricted lateral movement once access is gained.
• VPN-based remote access
Extends internal trust beyond the network edge.
• Password-based authentication with optional MFA
Leaves credential compromise exposure.
• Manual compliance documentation workflows
Create reporting delays and inconsistencies.
These weaknesses often contribute to the executive stress detailed in Healthcare Compliance Challenges ShieldHQ Solves for Executives.
ShieldHQ Enterprise Architecture Model
ShieldHQ replaces perimeter assumptions with containment architecture.
• Segmented secure enclaves for sensitive workloads
Limit breach blast radius.
• Zero-trust access enforcement for every session
Eliminate implicit trust.
• Phishing-resistant MFA enforcement across workforce
Reduce credential compromise.
• Automated Role-Based Access Control (RBAC)
Align privileges with job responsibilities.
• Centralized AI-driven anomaly detection monitoring
Identify suspicious activity in real time.
• Executive compliance dashboards
Provide board-ready reporting visibility.
This structural shift reflects serious modernization standards described in The ShieldHQ Approach: Serious Healthcare Security for Serious Organizations.
Lateral Movement Risk Comparison
Traditional flat networks create systemic vulnerability.
Traditional model:
• Compromised credentials move freely across departments.
• Backup environments are often reachable from production systems.
• Vendor access pathways are broadly defined.
ShieldHQ model:
• Clinical and administrative systems are segmented.
• Backup infrastructure is isolated.
• Vendor access is restricted to controlled zones.
• Lateral movement is structurally limited.
Containment dramatically reduces breach severity and regulatory impact.
Identity Governance Comparison
Credential compromise is the most common entry point.
Traditional identity model:
• Password-heavy authentication
• Inconsistent MFA enforcement
• Manual privilege revocation
ShieldHQ identity model:
• Enterprise-wide phishing-resistant MFA
• Automated RBAC enforcement
• Immediate privilege removal upon role change
• Continuous login anomaly monitoring
Identity discipline strengthens workforce-scale security described in ShieldHQ Implementation Guide for Healthcare Organizations Over 500 Employees.
Monitoring and Compliance Reporting Comparison
Traditional monitoring environments are fragmented.
Traditional approach:
• Logs stored across multiple platforms
• Manual report generation
• Delayed anomaly identification
ShieldHQ approach:
• Centralized SIEM integration
• AI-powered anomaly detection
• Real-time executive dashboards
• Automated audit documentation workflows
Monitoring automation strengthens executive reporting clarity and governance confidence.
Vendor Risk Governance Comparison
Vendor integration is often overlooked in traditional models.
Traditional vendor exposure:
• Broad VPN access
• Limited session monitoring
• Irregular reassessment cycles
ShieldHQ vendor governance:
• Segmented vendor access pathways
• Continuous vendor activity monitoring
• Structured Business Associate Agreement oversight
• Annual vendor risk reassessments
Vendor discipline reduces third-party exposure and reinforces compliance posture.
Enterprise Scalability Comparison
Healthcare organizations over 500 employees face unique challenges.
Traditional security struggles with:
• High-volume log management
• Workforce-wide MFA enforcement
• Multi-facility network segmentation
• Hybrid cloud integration
ShieldHQ architecture is designed specifically for:
• Multi-location healthcare enterprises
• Hybrid cloud visibility
• Workforce-wide identity governance
• High-volume anomaly detection processing
These scalability requirements are central to the evaluation process in How to Choose ShieldHQ for Your Healthcare Organization’s Compliance Needs.
Key Takeaways
Traditional healthcare security models rely on perimeter defenses and flat network assumptions that cannot contain modern enterprise threats. ShieldHQ Powered by Dispersive® Stealth Networking replaces reactive security with containment-driven architecture, phishing-resistant identity governance, AI-powered anomaly detection, structured vendor risk discipline, and centralized executive reporting dashboards. For healthcare organizations operating at scale, ShieldHQ provides structural resilience, regulatory defensibility, and leadership-level visibility that traditional models cannot sustain.