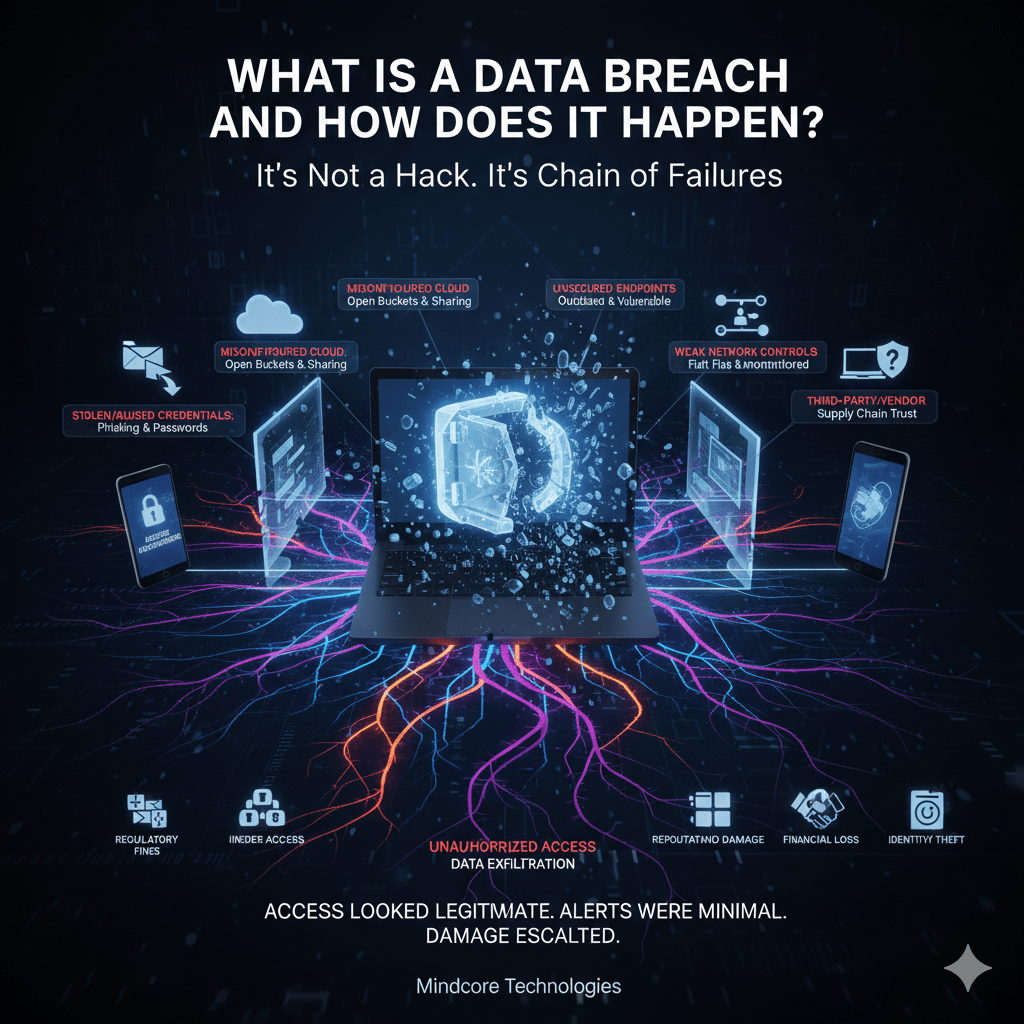
A data breach is not a single event. It is a sequence of failures that allows unauthorized access to sensitive information. Most breaches don’t start with “hacking.” They start with trust, convenience, or visibility gaps that attackers exploit quietly.
At Mindcore Technologies, breach investigations almost always reveal the same pattern: access looked legitimate, alerts were minimal, and the damage escalated over time. Understanding how breaches actually happen is the first step to stopping them.
What Is a Data Breach (Plain English)
A data breach occurs when:
- Sensitive data is accessed, viewed, copied, or exfiltrated
- The access is unauthorized or exceeds intended permission
- The organization loses control over that data
Data breaches can involve:
- Customer records
- Financial information
- Login credentials
- Intellectual property
- Medical or regulated data
Encryption, firewalls, and compliance do not prevent breaches by themselves. Control and monitoring do.
What Counts as a Data Breach (Even If Nothing Is “Stolen”)
A breach does not require public leaks or ransom notes.
These still count:
- An attacker viewing data without exporting it
- A compromised account accessing files it shouldn’t
- Misconfigured storage exposed to the internet
- Data emailed or shared with the wrong party
Loss of confidentiality is the breach.
How Data Breaches Actually Happen (Real-World Paths)
1. Stolen or Abused Credentials
The most common breach vector.
How it happens:
- Phishing emails capture logins
- Password reuse exposes multiple systems
- Session tokens are hijacked
Why it works:
Access looks legitimate. Security tools trust it.
2. Phishing That Leads to Cloud Access
Modern breaches rarely involve malware first.
What attackers do:
- Compromise email or cloud accounts
- Create inbox rules to hide activity
- Access file storage and shared documents
Result:
Weeks of silent data exposure before detection.
3. Misconfigured Cloud Storage or SaaS
Speed beats security during growth.
Common mistakes:
- Publicly accessible storage buckets
- Over-permissive sharing links
- No monitoring of access logs
Impact:
Data exposure without any intrusion at all.
4. Unsecured Endpoints
One device is enough.
Attack path:
- Outdated laptop or weak local controls
- Credential or session theft
- Pivot into cloud and internal systems
Endpoints inherit trust across the environment.
5. Insider Access (Malicious or Accidental)
Not all breaches involve outsiders.
Examples:
- Excessive access granted “temporarily”
- Data shared with personal accounts
- Departing employees retaining access
Intent doesn’t matter. Exposure does.
6. Weak Network Controls
Flat networks amplify damage.
What attackers exploit:
- Unrestricted internal access
- No segmentation
- Minimal monitoring
Once inside, data discovery is easy.
7. Third-Party or Vendor Breaches
Your security depends on others.
Common scenario:
- Vendor account compromised
- Trusted integrations abused
- Data accessed through legitimate channels
Supply chain trust is frequently exploited.
Why Breaches Often Go Undetected
Most breaches:
- Use valid credentials
- Operate during business hours
- Avoid malware and noisy activity
- Blend into normal traffic
Detection fails when visibility and behavior monitoring are weak.
The Real Impact of a Data Breach
Breaches are not just IT problems.
They trigger:
- Regulatory reporting and fines
- Legal exposure
- Customer trust erosion
- Business disruption
- Long-term brand damage
The cost is often measured in months, not days.
What Prevents Breaches (In Practice)
Prevention is about reducing exposure and limiting blast radius.
Effective controls include:
- Phishing-resistant MFA
- Identity-based access with least privilege
- Short-lived sessions and revalidation
- Network segmentation
- Monitoring access behavior, not just malware
- Restricting outbound data movement
Perfect prevention is unrealistic. Controlled impact is achievable.
What Turns an Incident Into a Major Breach
Small incidents become major breaches when:
- Access is overly broad
- Monitoring is weak
- Response is slow
- Data can move freely
Architecture determines outcomes.
How Mindcore Technologies Helps Reduce Breach Risk
Mindcore helps organizations reduce data breach risk by focusing on how breaches actually occur:
- Identity-centric security architecture
- Cloud and SaaS access controls
- Endpoint hardening and posture enforcement
- Network segmentation and visibility
- Data access monitoring and response
- Incident readiness and containment planning
We design environments where one mistake doesn’t expose everything.
A Simple Reality Check
Your breach risk is high if:
- Credentials unlock too much access
- Cloud sharing is uncontrolled
- Endpoints lag on updates
- Network traffic isn’t monitored
- Data can leave freely
These conditions exist in most environments today.
Final Takeaway
A data breach is rarely a single failure. It is the result of layered trust without layered controls. Attackers exploit credentials, sessions, misconfigurations, and visibility gaps to access data quietly and persistently.
Organizations that understand how breaches really happen can design security that contains damage, detects abuse early, and protects what matters most. Those that rely on tools alone often discover the breach only after exposure has already occurred.