A VoIP phone system is not just an internet-based phone line. It is a software-driven communications platform that depends entirely on your network’s stability, security, and configuration.
When businesses struggle with VoIP, it is rarely the phone service itself. It is the network underneath it.
At Mindcore Technologies, we see organizations migrate to VoIP expecting instant savings, only to discover dropped calls, audio lag, or security concerns because infrastructure was never assessed properly.
If you are evaluating VoIP, you need to understand how it actually works and what it demands from your environment.
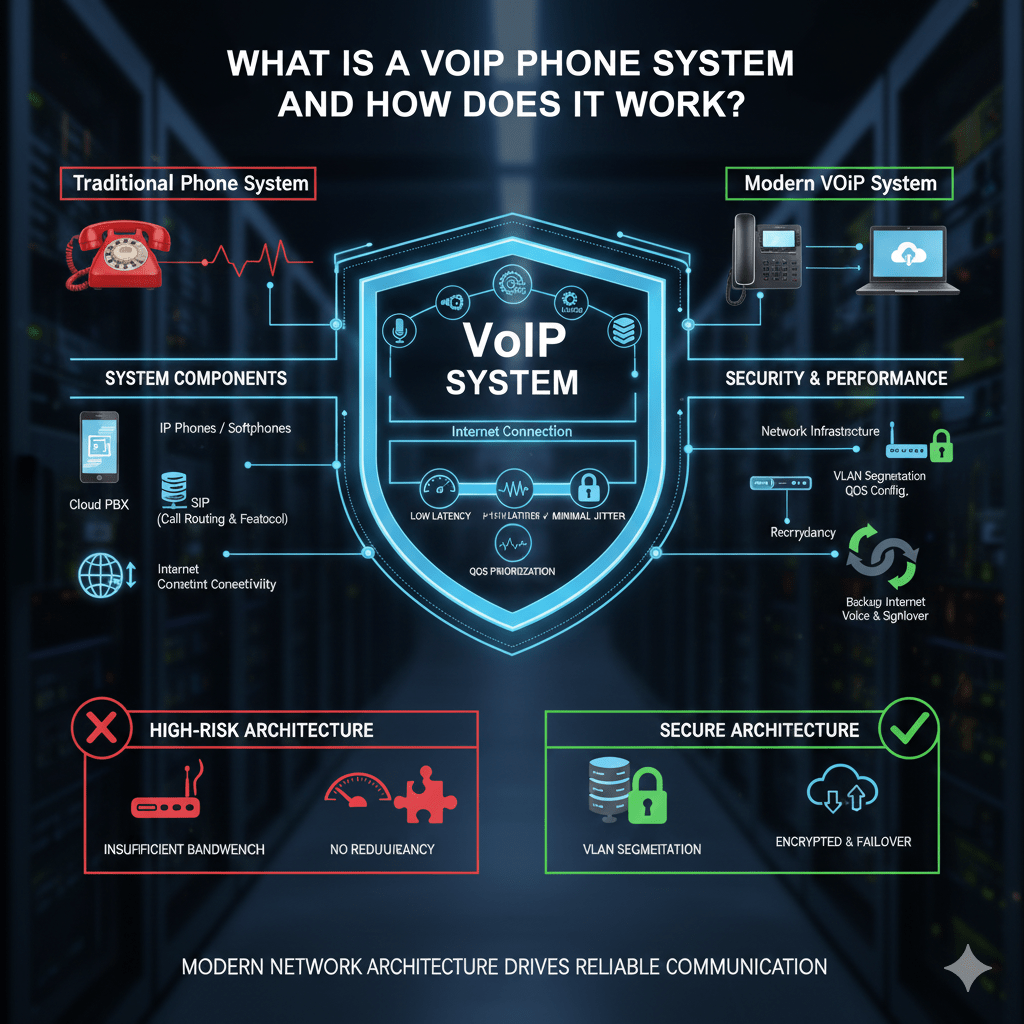
What Is a VoIP Phone System?
A VoIP phone system, short for Voice over Internet Protocol, allows voice calls to travel over an IP network instead of traditional copper phone lines.
It typically includes:
- IP desk phones or softphones
Physical phones or apps on computers and mobile devices. - A cloud or on-premise PBX system
The “brain” that manages call routing, voicemail, extensions, and auto-attendants. - An internet connection
Voice data travels across your business network. - Networking hardware
Routers, switches, and firewalls that move and protect traffic.
Instead of analog signals on dedicated lines, voice becomes digital data packets.
How a VoIP Phone System Actually Works
VoIP systems convert voice into digital packets and transmit them across networks in real time.
Here’s the technical flow simplified:
- Voice capture
The microphone converts sound waves into digital signals. - Compression via codecs
Audio is compressed to reduce bandwidth usage while preserving clarity. - Packetization
The conversation is split into small data packets. - Transmission across the IP network
Packets travel through your router, firewall, and internet provider. - Reassembly at the destination
The recipient’s system reconstructs the packets into audible speech.
This happens in milliseconds, but only if the network is properly configured.
What Makes VoIP Call Quality Good or Bad
VoIP is extremely sensitive to network performance.
Call quality depends on:
- Low latency
High delay causes overlapping conversations. - Minimal jitter
Inconsistent packet timing results in robotic or choppy audio. - Low packet loss
Lost packets lead to missing words or clipped speech. - Adequate bandwidth
Voice traffic must not compete with heavy downloads or streaming. - Quality of Service (QoS) configuration
Voice traffic should be prioritized above non-critical traffic.
If your network struggles with video conferencing, VoIP will reveal those weaknesses quickly.
VoIP Phone System Components Explained
A complete VoIP deployment includes multiple moving parts.
IP Phones or Softphones
- Hardware desk phones connect directly to your network.
- Softphones run on desktops, laptops, or smartphones.
- Devices must be configured securely and kept updated.
PBX (Private Branch Exchange)
- Routes calls internally and externally.
- Handles voicemail, call forwarding, auto-attendants.
- Can be cloud-hosted or on-premise.
- Must be secured with strong authentication.
SIP (Session Initiation Protocol)
- Manages call setup and termination.
- Requires proper firewall configuration.
- Commonly targeted if left exposed or misconfigured.
Internet Connectivity
- Determines uptime and performance.
- Requires sufficient upload and download capacity.
- Should include redundancy planning.
Each component affects reliability and security.
Business Benefits of VoIP Systems
When implemented properly, VoIP provides:
- Scalability
Adding or removing users does not require new phone lines. - Mobility
Employees can work remotely while maintaining business extensions. - Advanced features
Call analytics, auto-attendants, CRM integration, voicemail-to-email. - Cost efficiency
Reduced traditional carrier expenses. - Centralized management
Simplified multi-location operations.
Flexibility is the core advantage.
Security Risks of VoIP Systems
VoIP systems are internet-connected and must be secured accordingly.
Common risks include:
- Toll fraud
Attackers generate unauthorized international calls through compromised systems. - SIP scanning and brute-force attacks
Exposed ports attract automated attacks. - Eavesdropping
Unencrypted voice traffic can be intercepted. - Denial-of-service attacks (DoS)
Flooding VoIP servers to disrupt operations. - Weak administrator passwords
Exposing the PBX management interface.
VoIP security cannot be treated as optional.
How To Secure a VoIP Phone System Properly
Security requires structured configuration.
1. Harden the Network
You must:
- Upgrade to business-grade routers and switches
Consumer hardware often lacks stability and QoS capability. - Segment voice traffic using VLANs
Separating voice from general data traffic reduces congestion and risk. - Implement QoS rules
Prioritize voice packets over non-essential traffic. - Ensure bandwidth headroom during peak hours
Avoid saturation that degrades calls.
Network readiness determines success.
2. Secure the VoIP Platform
Protect the PBX and endpoints by:
- Enforcing strong authentication and MFA for administrators
Preventing management console compromise. - Restricting international dialing permissions
Limiting toll fraud exposure. - Encrypting signaling and media traffic
Protecting call confidentiality. - Closing unused SIP ports and limiting external exposure
Reducing attack surface.
Default configurations are rarely secure.
3. Plan for Redundancy and Uptime
VoIP depends on connectivity.
Resilience planning should include:
- Secondary internet connections
Automatic failover prevents phone outages. - Cloud call routing failover
Calls rerouted to mobile devices during disruption. - UPS battery backup for networking equipment
Preventing brief power interruptions from killing phones. - Routine failover testing
Ensuring redundancy actually works.
Phone outages directly affect revenue and customer experience.
Cloud VoIP vs On-Premise VoIP
Cloud VoIP
- Hosted by a provider.
- Lower infrastructure maintenance.
- Dependent on internet reliability.
- Requires strong vendor security evaluation.
On-Premise VoIP
- Greater internal control.
- Requires in-house maintenance.
- Higher upfront hardware investment.
- Increased internal security responsibility.
Both models require strong network design.
Is Your Business Ready for VoIP?
You are ready if:
- Your internet connection is stable and fast.
- Networking hardware is modern and properly configured.
- You have QoS implemented.
- You have redundancy planning in place.
- Security controls are enforced.
You are not ready if:
- Internet outages are frequent.
- Network devices are outdated.
- No VLAN segmentation exists.
- Firewall rules are loosely managed.
- No failover plan exists.
VoIP performance reflects infrastructure maturity.
How Mindcore Technologies Supports VoIP Deployments
Mindcore helps businesses deploy VoIP systems by:
- Assessing network readiness before migration
Identifying bottlenecks and vulnerabilities. - Designing segmented voice architectures
Improving performance and security. - Configuring firewalls and QoS policies properly
Ensuring consistent call quality. - Securing administrative interfaces and SIP exposure
Reducing attack surface. - Implementing redundancy planning and testing
Protecting uptime.
VoIP should modernize communications, not introduce instability.
Final Takeaway
A VoIP phone system converts voice into digital packets and delivers it across your IP network. Its success depends entirely on network stability, bandwidth management, and security configuration.
Businesses that prepare infrastructure properly gain flexibility, mobility, and efficiency. Those that migrate without planning experience degraded call quality, outages, and security risk.
VoIP is not just a phone upgrade. It is a network architecture decision.