If you suspect you’ve been hacked, speed and order matter more than certainty. Most damage occurs after the initial compromise, when attackers expand access, persist quietly, and abuse trust. The goal is to stop access, preserve evidence, and prevent recurrence, in that order.
At Mindcore Technologies, incident response shows the same pattern: people rush to “fix” systems and accidentally make things worse. Follow the steps below exactly.
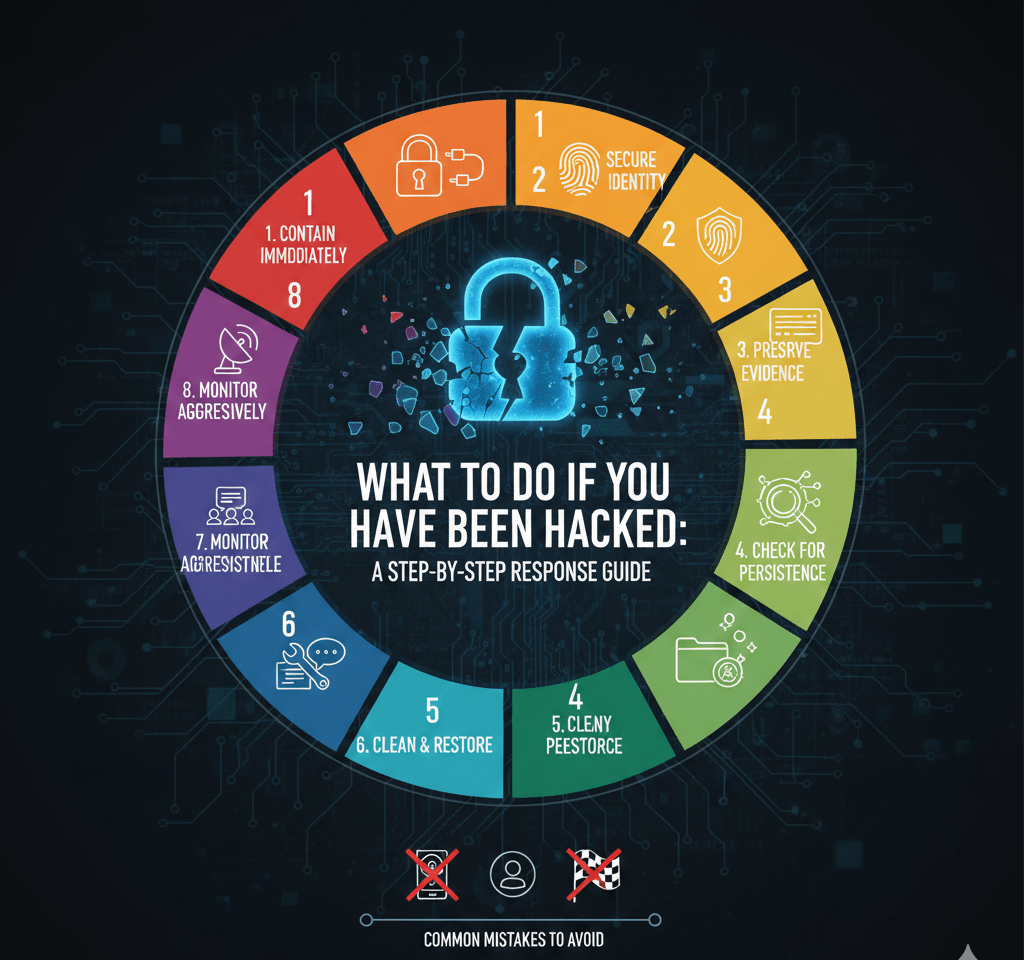
Step 1: Assume Compromise and Contain Immediately
Do not wait for proof. Treat indicators as real.
Do this now:
- Disconnect the affected device from Wi-Fi/Ethernet (leave it powered on)
- Disable suspected compromised accounts
- Revoke all active sessions and tokens
- Block suspicious IPs or locations if visible
Do not: wipe, reset, or restore yet. Containment stops expansion.
Step 2: Secure Your Identity First (This Stops Lateral Spread)
Most hacks are identity-based.
Immediately:
- Change passwords on affected accounts from a known-clean device
- Force sign-out on all sessions
- Enable or tighten MFA (prefer phishing-resistant options)
- Check account recovery settings (backup emails, phone numbers)
Start with email. Email control enables resets everywhere else.
Step 3: Preserve Evidence (You’ll Need It)
Evidence determines scope, recovery accuracy, and legal position.
Preserve without altering:
- Login and access logs
- Email rules and forwarding settings
- Cloud/SaaS audit logs
- Endpoint activity records and timestamps
Avoid reimaging until evidence is captured.
Step 4: Check for Persistence and Secondary Access
Attackers rarely leave cleanly.
Look for:
- New admins or users
- OAuth apps or API keys you didn’t create
- Email inbox rules/forwarding
- Scheduled tasks or startup items
- Security settings changed or disabled
Remove anything unauthorized.
Step 5: Determine What Was Accessed (Not Just What’s Broken)
Focus on exposure, not symptoms.
Assess:
- Which accounts were accessed
- Which files, mailboxes, or systems were viewed
- Whether data was downloaded or shared
- Whether regulated data is involved (PII/PHI/PCI)
If you can’t prove it wasn’t accessed, assume potential exposure.
Step 6: Clean and Restore Safely
Restoration without remediation invites repeat compromise.
Before restoring:
- Patch exploited vulnerabilities
- Remove excessive permissions
- Update configurations and policies
Then:
- Rebuild or restore from known-good backups
- Monitor closely during and after restoration
Restore in phases, not all at once.
Step 7: Notify the Right People (At the Right Time)
Don’t broadcast prematurely.
Notify as appropriate:
- Internal IT/Security leadership
- Legal/compliance (if business data is involved)
- Affected platforms or vendors
- Customers or regulators only with guidance
Accuracy and timing reduce liability.
Step 8: Monitor Aggressively for Recurrence
Post-incident activity is common.
For at least 30 days:
- Watch for abnormal logins
- Alert on new admin creation
- Monitor outbound data movement
- Review email and cloud audit logs
Most re-compromises happen quickly.
Common Mistakes to Avoid
- Resetting everything at once
- Ignoring email and cloud logs
- Assuming “one account only”
- Letting users self-remediate
- Declaring victory too early
Discipline beats urgency.
If You’re an Individual (Personal Accounts)
Prioritize:
- Email, banking, and primary cloud accounts
- Password manager security
- Device OS and browser updates
- Credit monitoring if personal data may be exposed
Identity recovery is a marathon, not a sprint.
If You’re a Business
Treat this as a business risk event:
- Centralize response authority
- Document timelines and decisions
- Coordinate IT, legal, and communications
- Fix root causes, not just symptoms
Architecture determines outcomes.
How Mindcore Technologies Helps During a Hack
Mindcore supports rapid, correct response by providing:
- Immediate containment and scoping
- Identity and access lockdown
- Evidence preservation and investigation
- Endpoint, network, and cloud remediation
- Post-incident hardening to prevent recurrence
We focus on control, clarity, and containment.
Final Takeaway
Being hacked is not defined by broken systems. It’s defined by unauthorized access. The right response stops expansion, preserves evidence, and redesigns weak trust paths. Organizations and individuals who follow a disciplined, step-by-step approach dramatically reduce damage and recovery time. Those who rush often invite the same attacker back.