CMMC is not a future requirement. It is already being introduced into Department of Defense contracts, and enforcement is increasing. The confusion comes from the phased rollout. Many organizations assume they have time, but the reality is that requirements can appear as soon as they bid on or renew a contract.
We see companies delay preparation until a contract requires certification. At that point, timelines become compressed, costs increase, and the risk of losing contracts rises.
The key is understanding that CMMC is being implemented in phases, not all at once. The requirement depends on when your contracts include it.
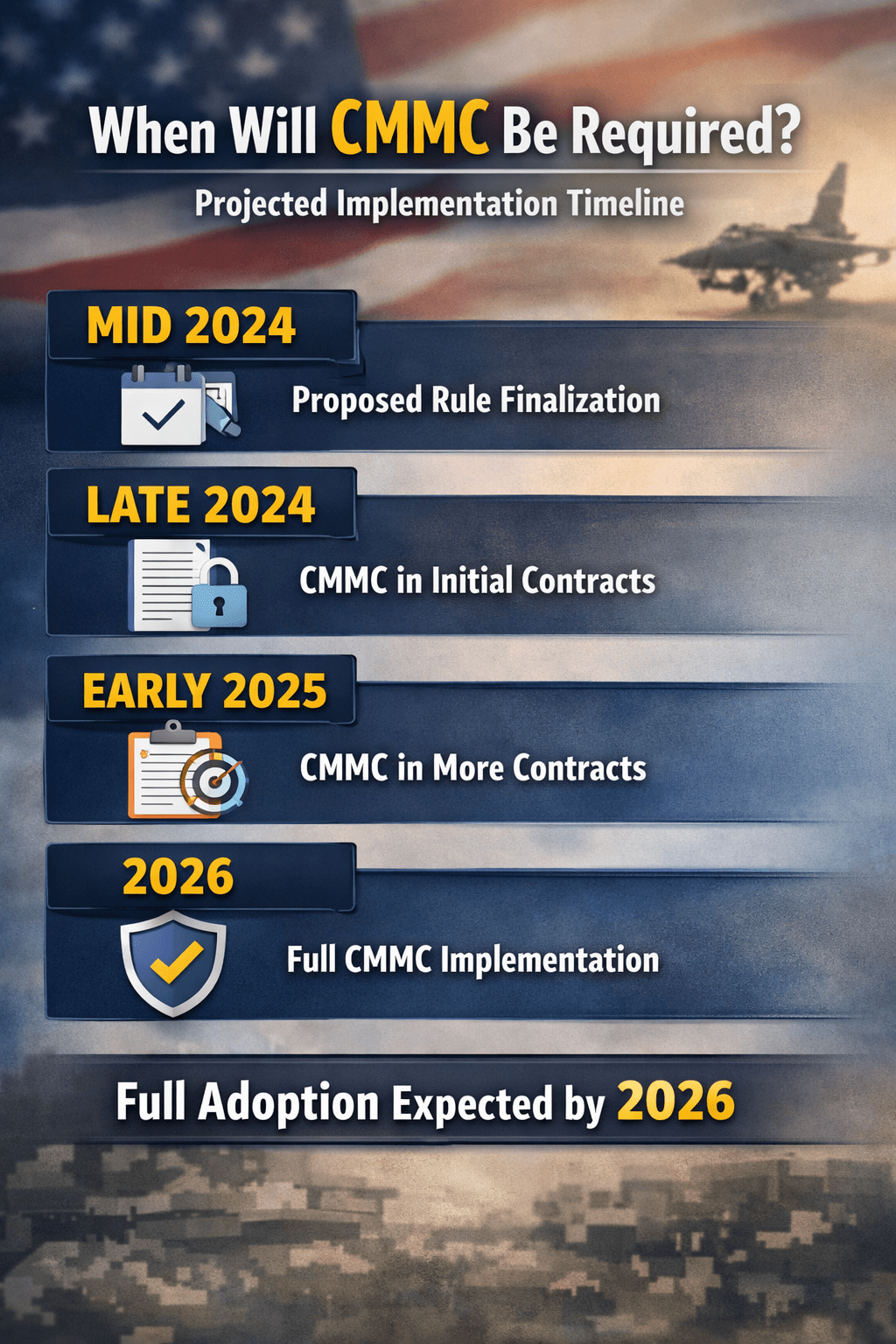
CMMC Rollout Timeline
The Department of Defense is implementing CMMC through a structured, phased approach.
• Initial rulemaking phase, defining requirements and framework updates
• Pilot program inclusion, introducing CMMC requirements in select contracts
• Gradual contract integration, expanding requirements across DoD contracts
• Full implementation, requiring CMMC certification for all applicable contractors
This phased rollout allows organizations time to prepare, but not to delay indefinitely.
When CMMC Becomes Mandatory for Your Organization
CMMC becomes mandatory when it is included in your contract.
• New contracts, requiring certification at the time of award
• Contract renewals, introducing CMMC requirements during extension
• Subcontract agreements, flowing requirements down from prime contractors
If your contract includes CMMC, certification is required before you can perform the work.
Expected Timeline for Full Enforcement
The DoD is moving toward full enforcement over the next few years.
• Early adoption phase, where select contracts require CMMC
• Expansion phase, increasing the number of contracts with requirements
• Full enforcement phase, where all applicable contracts require certification
Organizations should expect increasing enforcement rather than a single deadline.
Why Waiting Creates Risk
Delaying preparation creates operational and financial risk.
We see organizations wait until requirements are enforced, then struggle to meet deadlines.
This leads to:
• Inability to bid on contracts, due to lack of certification
• Increased cost of rapid compliance efforts, requiring accelerated implementation
• Operational disruption, as systems must be updated quickly
• Higher audit failure risk, due to incomplete control enforcement
Preparation must happen before the requirement appears.
What Triggers Immediate CMMC Requirements
Certain conditions accelerate the need for compliance.
• Handling Controlled Unclassified Information, requiring Level 2 certification
• Working as a subcontractor, inheriting requirements from prime contractors
• Participating in new DoD contract bids, where CMMC is included
• Renewing existing contracts, where requirements are added
If any of these apply, CMMC may already be required.
How to Prepare Before CMMC Is Required
Preparation should begin before contracts mandate certification.
Identify Your Required CMMC Level
• Determine if you handle FCI or CUI, defining your compliance scope
• Review contracts and data flows, identifying exposure to DoD information
• Align with Level 1, 2, or 3 requirements, based on data sensitivity
Assess Your Current Environment
• Identify gaps in access control, ensuring least privilege enforcement
• Evaluate monitoring capabilities, confirming visibility into system activity
• Review data protection measures, verifying encryption and storage controls
Implement Enforceable Controls
• Apply identity-driven access control, ensuring strong authentication
• Centralize monitoring, improving visibility and audit readiness
• Isolate sensitive systems, reducing exposure and improving containment
Preparation is not about documentation. It is about enforcement.
How ShieldHQ Helps You Prepare for CMMC Now
ShieldHQ Powered by Dispersive® Stealth Networking enables organizations to meet CMMC requirements before they are mandated.
• Secure workspaces isolate FCI and CUI, ensuring controlled access
• Stealth networking removes infrastructure from discovery, reducing attack surface
• Identity-driven access enforces strict authentication, aligning with compliance requirements
• Centralized monitoring provides audit-ready visibility, supporting assessments
This allows organizations to be ready before contracts require certification.
How Mindcore Technologies Prepares You for CMMC Deadlines
Mindcore Technologies helps organizations align with CMMC timelines and requirements.
• Assess current readiness, identifying gaps in controls and enforcement
• Determine required certification level, based on contracts and data
• Design architecture aligned with CMMC and NIST frameworks
• Implement ShieldHQ, reducing exposure and improving compliance
• Prepare for audits, ensuring readiness for certification
• Provide ongoing support, maintaining compliance over time
Execution determines whether deadlines are met or missed.
Final Takeaway
CMMC is being rolled out in phases, but for individual organizations, it becomes mandatory as soon as it is included in a contract, whether through new awards, renewals, or subcontractor requirements. There is no single universal deadline, which creates confusion, but also means that organizations must be prepared before requirements appear rather than reacting after. Companies that delay preparation risk losing contracts, increasing costs, and failing audits, while those that align their security architecture early can meet requirements without disruption.
If your organization is evaluating when CMMC will apply and how to prepare before deadlines impact your business, schedule a free strategy call with Mindcore Technologies to assess your readiness and define a path forward.