Data loss does not happen because companies lack tools. It happens because controls are incomplete, misaligned, or trusted too broadly. Most breaches succeed without advanced exploits, by abusing access that already exists.
At Mindcore Technologies, real-world incident response shows the same truth over and over: organizations that apply a small set of foundational controls consistently stop the majority of data exposure events. Those that don’t rely on luck.
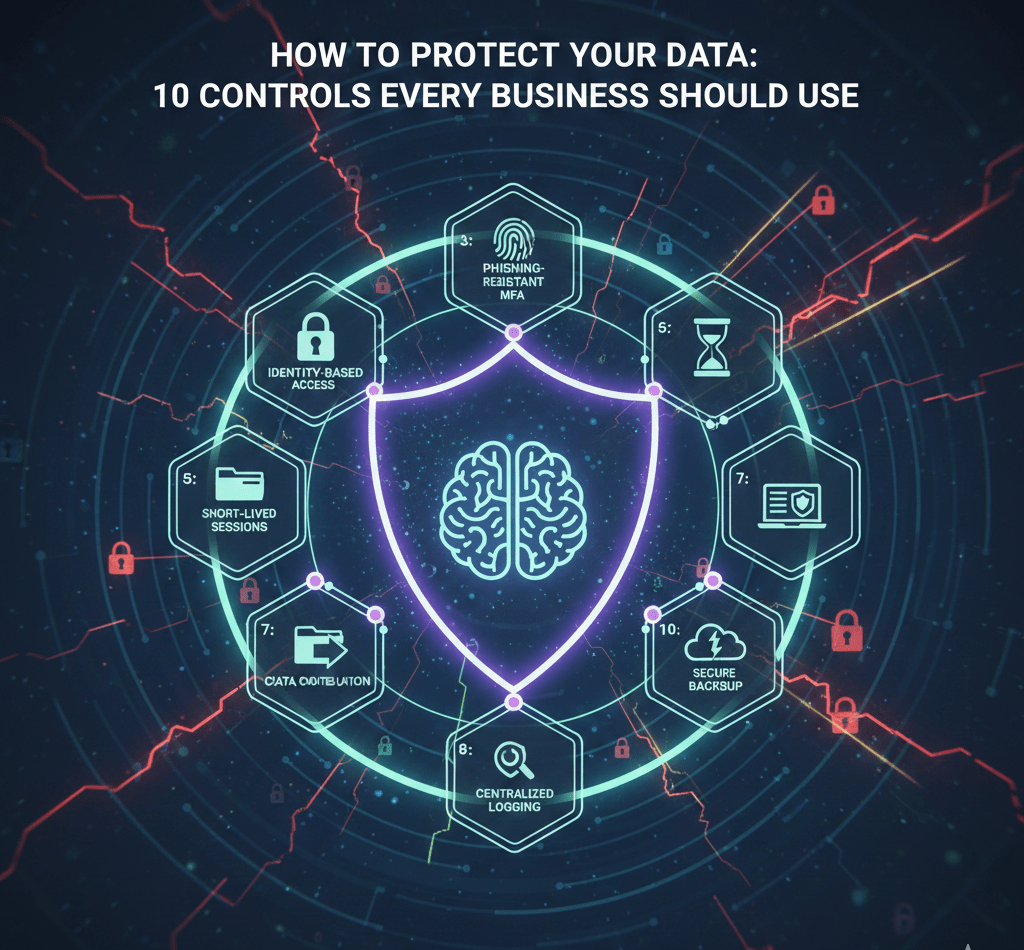
These are the 10 controls that actually protect business data in practice, not in theory.
Control 1: Identity-Based Access With Least Privilege
The failure we see:
Users and service accounts have far more access than required.
The control:
- Grant access strictly by role
- Remove standing access where possible
- Review permissions regularly
Data should only be reachable by those who absolutely need it.
Control 2: Phishing-Resistant Multi-Factor Authentication
The failure we see:
Passwords and push-based MFA are bypassed through phishing and session theft.
The control:
- Enforce phishing-resistant MFA (FIDO2, hardware-backed keys)
- Require MFA for email, cloud platforms, VPNs, and admin access
MFA must resist phishing, not just exist.
Control 3: Short-Lived Sessions and Continuous Validation
The failure we see:
Sessions remain valid for days or weeks after login.
The control:
- Limit session lifetimes
- Revalidate access based on context
- Terminate sessions on risk signals
If sessions never expire, attackers don’t need passwords.
Control 4: Data Classification and Access Boundaries
The failure we see:
All data is treated the same, so everything is exposed.
The control:
- Identify sensitive and regulated data
- Restrict access paths explicitly
- Separate critical data from general storage
You cannot protect what you haven’t defined.
Control 5: Network Segmentation and Data Zoning
The failure we see:
Flat networks allow unrestricted lateral movement.
The control:
- Segment users, servers, and data stores
- Enforce access between segments
- Log and alert on cross-zone movement
Segmentation limits blast radius when access is abused.
Control 6: Endpoint Hardening and Posture Enforcement
The failure we see:
Outdated or unmanaged devices inherit trust.
The control:
- Enforce OS and patch compliance
- Remove unnecessary local admin rights
- Restrict data access from non-compliant devices
Endpoints are data access gateways. Treat them accordingly.
Control 7: Controlled Outbound Data Movement
The failure we see:
Data can leave the environment freely once accessed.
The control:
- Restrict outbound traffic from sensitive systems
- Monitor for abnormal data transfers
- Block known exfiltration paths
Stopping exfiltration reduces breach severity dramatically.
Control 8: Secure Backup and Recovery Architecture
The failure we see:
Backups are accessible from compromised systems.
The control:
- Use immutable or offline backups
- Separate backup credentials and access
- Test restoration regularly
Backups must survive compromise to matter.
Control 9: Centralized Logging and Behavior Monitoring
The failure we see:
Logs exist but are not reviewed or correlated.
The control:
- Centralize identity, cloud, endpoint, and network logs
- Monitor for abnormal access patterns
- Alert on behavior, not just malware
Most data breaches use legitimate access. Visibility is critical.
Control 10: Incident Response Readiness and Access Revocation
The failure we see:
No clear plan when access is abused.
The control:
- Maintain a documented response plan
- Practice account and session revocation
- Assign clear decision authority
Speed and coordination reduce exposure.
Why These 10 Controls Work Together
Each control compensates for the failure of another:
- MFA fails, but sessions expire
- Access is abused, but segmentation contains it
- Data is touched, but exfiltration is blocked
Security works when no single failure equals total exposure.
What Most Businesses Miss
Data protection fails when:
- Identity equals unlimited trust
- Sessions last forever
- Networks are flat
- Monitoring is reactive
- Response plans exist only on paper
These are architectural issues, not awareness issues.
How Mindcore Technologies Helps Protect Business Data
Mindcore helps organizations implement these controls through:
- Identity-first security design
- Secure access architecture
- Endpoint and network hardening
- Cloud and data access governance
- Monitoring and incident readiness
We focus on reducing exposure and limiting blast radius, not just deploying tools.
A Quick Self-Assessment
Your data is at high risk if:
- Access is broad and static
- MFA is optional or easily phished
- Sessions persist indefinitely
- Sensitive data is not segmented
- Monitoring is minimal
These conditions are common—and fixable.
Final Takeaway
Protecting business data is not about adding more products. It is about enforcing the right controls consistently. The ten controls outlined here stop the majority of real-world data breaches by removing implicit trust and increasing visibility.
Organizations that implement them deliberately protect their data even when something goes wrong. Those that don’t often learn their importance only after exposure has already occurred.