Most healthcare breaches do not originate from internal staff. They originate from trusted third parties with excessive, persistent access. Vendors, billing partners, IT providers, and device manufacturers often have more network visibility than they need, and attackers know this.
Third-party risk is not a vendor problem. It is an access architecture problem.
At Mindcore Technologies, healthcare breach reviews consistently show that third-party access paths are one of the fastest ways attackers bypass perimeter defenses and move laterally into PHI systems.
What Third-Party Risk Really Means in Healthcare
Third-party risk is any situation where external users can access internal healthcare systems in ways that increase exposure, reduce visibility, or bypass controls.
This includes:
- IT vendors with VPN access
Broad network access granted for convenience, not necessity. - Medical device manufacturers and support teams
Persistent access to device networks and management interfaces. - Billing, coding, and revenue cycle partners
Access to PHI systems beyond scoped workflows. - Cloud and SaaS administrators
Elevated permissions with limited oversight.
The risk is rarely malicious intent. It is unbounded trust.
Why Healthcare Third-Party Risk Is So High
Healthcare environments amplify third-party risk because:
- Operations depend heavily on vendors
Clinical, administrative, and technical workflows rely on outside support. - Access is granted once and rarely reviewed
Temporary needs turn into permanent permissions. - VPN-based access extends full network trust
Vendors see more than they should. - Audit oversight focuses on contracts, not access paths
Compliance reviews often miss technical exposure.
This creates invisible risk that grows over time.
How Attackers Exploit Third-Party Access
Attackers target third parties because they are efficient entry points.
Common exploitation paths include:
- Credential theft from vendor accounts
Phishing and infostealers target external users with elevated access. - Session hijacking of VPN connections
Persistent sessions are abused quietly. - Pivoting through trusted vendor networks
Third-party access bypasses many internal controls. - Lateral movement into EHR and file systems
Vendors often sit close to sensitive systems.
Once inside, attackers inherit vendor trust automatically.
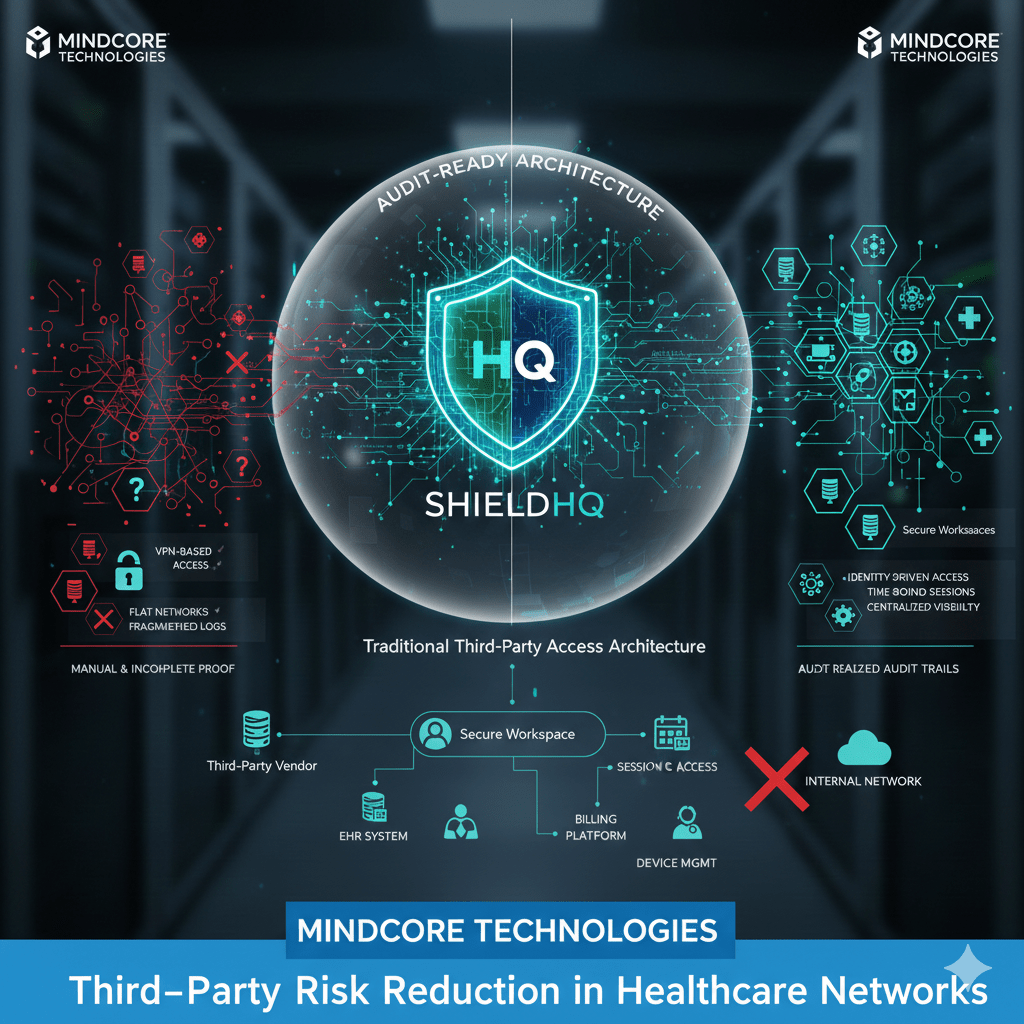
Why Traditional Third-Party Controls Fail
Many organizations rely on paperwork instead of architecture.
Common failures include:
- Vendor risk questionnaires without enforcement
Policies do not restrict real access paths. - Flat or loosely segmented networks
Once connected, vendors can move freely. - Shared or generic vendor accounts
Accountability is lost. - Monitoring without containment
Alerts trigger after damage occurs.
Governance without technical restriction does not reduce risk.
Reducing Third-Party Risk Through Access Containment
Effective third-party risk reduction focuses on limiting reach, not monitoring behavior.
Key principles include:
1. Eliminating VPN-Based Vendor Access
VPNs create excessive trust.
Reducing risk requires:
- Removing vendor VPN access entirely
Vendors should not join internal networks. - Delivering application-level access only
Vendors access specific systems, not infrastructure. - Using session-based connectivity
Access exists only when approved and needed.
This immediately reduces exposure.
2. Scoping Vendor Access to Exact Workflows
Third parties should only access what they support.
This means:
- Restricting access to named applications or devices
No general system visibility. - Preventing lateral movement
Vendors cannot pivot across environments. - Aligning access duration with task completion
Access expires automatically.
Scope control removes opportunity for abuse.
3. Isolating Third Parties from PHI Where Possible
Many vendors do not need direct PHI access.
Risk is reduced by:
- Providing indirect or mediated access
Vendors support systems without touching data. - Containing PHI inside secure environments
Data does not leave controlled workspaces. - Blocking data export paths
Copy, download, and sync actions are restricted.
Less PHI access means less regulatory exposure.
4. Enforcing Strong Identity and Accountability
Third-party access must be attributable.
This requires:
- Unique identities for every vendor user
No shared credentials. - Strong authentication tied to identity
Access depends on verified users. - Clear session logging
Who accessed what and when is always visible.
Accountability deters misuse and simplifies audits.
5. Centralizing Visibility Across All Third-Party Access
Fragmented visibility hides risk.
Healthcare organizations need:
- One control plane for all vendor access
Not separate tools for each partner. - Consistent access policies across environments
Rules do not change by location. - Real-time session oversight
Risk can be addressed immediately.
Visibility supports enforcement, not just review.
Reducing Ransomware Risk from Third Parties
Third-party access is a common ransomware vector.
Containment reduces impact by:
- Preventing attackers from using vendors as pivot points
Lateral movement is blocked. - Limiting access to critical systems
Encryption scope is reduced. - Allowing instant session revocation
Compromised access is shut down immediately.
Ransomware becomes containable instead of catastrophic.
HIPAA Alignment Through Third-Party Risk Reduction
HIPAA expects healthcare organizations to control access and minimize exposure, regardless of who the user is.
Third-party risk reduction supports this by:
- Enforcing minimum necessary access
Vendors see only what they need. - Improving audit clarity
Vendor access is clearly logged and reviewable. - Reducing breach scope
Fewer systems and records are exposed.
Third-party access becomes defensible under audit.
How Mindcore Technologies Reduces Third-Party Risk in Healthcare
Mindcore reduces third-party risk by:
- Mapping all existing vendor access paths
Revealing hidden exposure. - Replacing VPN access with secure workspace models
Removing network trust. - Designing scoped, session-based vendor access
Access is deliberate and temporary. - Containing PHI inside controlled environments
Data does not sprawl to vendor systems. - Providing centralized visibility and audit readiness
Compliance and security teams share one view.
The objective is enabling vendors without inheriting their risk.
A Simple Third-Party Risk Reality Check
Your third-party risk remains high if:
- Vendors use VPNs
- Vendor access is persistent
- Vendors can browse internal networks
- Shared credentials exist
- Audit evidence is manual
These are architectural weaknesses, not vendor failures.
Final Takeaway
Third-party risk in healthcare cannot be solved with contracts or questionnaires alone. It must be addressed through access architecture that limits reach, enforces accountability, and contains exposure automatically.
Healthcare organizations that redesign third-party access reduce ransomware risk, simplify HIPAA compliance, and protect patient trust. Those that do not remain vulnerable through their most trusted connections.