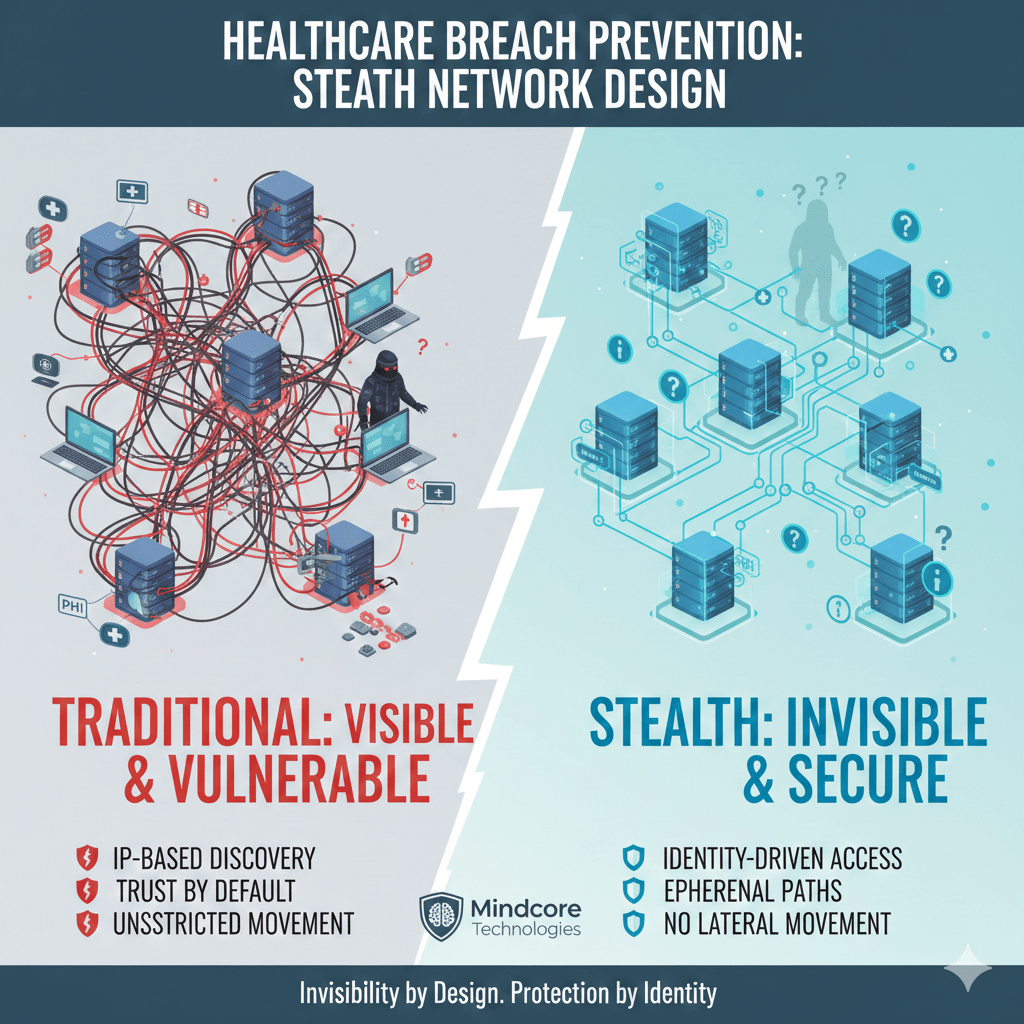
Most healthcare breaches do not happen because attackers defeat security controls. They happen because internal systems are visible, reachable, and trusted by default. Once attackers gain any foothold, traditional networks give them everything they need to move, escalate, and extract data.
Stealth network design prevents breaches by removing visibility and reachability entirely, not by trying to detect attackers after access already exists.
At Mindcore Technologies, healthcare incident reviews consistently show that environments using stealth principles experience fewer successful breaches and dramatically smaller blast radiuses when incidents occur.
Why Traditional Network Design Enables Breaches
Most healthcare networks are designed for connectivity first, security second.
They fail because:
- Internal systems are discoverable by default
IP-based networks expose servers, devices, and services to anyone with access. - Trust is granted once and rarely reevaluated
VPNs and internal access assume legitimacy after login. - Lateral movement is unrestricted
Flat or loosely segmented networks allow attackers to pivot quickly. - Visibility exists without control
Monitoring detects activity but does not prevent reach.
Once attackers enter, the network helps them.
What Stealth Network Design Actually Means
Stealth networking is not segmentation alone. It is network invisibility enforced by identity.
In a stealth network:
- Systems do not respond to scans or probes
Unauthorized users cannot see targets. - Connectivity is created only after identity verification
Access is explicit, not assumed. - Access paths are ephemeral
Sessions disappear when work ends. - Network location provides no trust
Being “inside” grants nothing.
Attackers cannot target what they cannot find.
How Stealth Design Prevents Breaches at Every Stage
Stealth networking breaks the breach lifecycle early.
It prevents:
- Initial reconnaissance
Attackers cannot map internal systems. - Credential abuse
Stolen credentials do not unlock networks. - Lateral movement
Systems are isolated and unreachable by default. - Privilege escalation
Access does not expand automatically.
Breaches stall before damage occurs.
Reducing Ransomware Risk Through Invisibility
Ransomware depends on speed and spread.
Stealth networks disrupt both by:
- Hiding file servers and backup systems
Attackers cannot locate encryption targets. - Blocking pivot paths between systems
One compromise cannot spread. - Preventing mass encryption events
Attackers lack reach. - Allowing instant session shutdown
Access is revoked without reconfiguring networks.
Ransomware becomes containable instead of catastrophic.
Protecting PHI by Limiting Exposure
PHI exposure often happens unintentionally.
Stealth networking reduces exposure by:
- Making PHI systems unreachable by default
Access exists only when explicitly approved. - Separating users from infrastructure
Applications are accessed without exposing networks. - Preventing data discovery and scraping
Attackers cannot locate repositories. - Reducing reliance on endpoint security
Data protection does not depend on device hygiene.
Less visibility means less exposure.
Securing Medical Devices Without Modifying Them
Medical devices are difficult to secure traditionally.
Stealth networking protects them by:
- Hiding devices from network scans
Devices do not advertise their presence. - Eliminating direct network access
Only approved workflows connect. - Preventing device-to-device communication
Compromise does not spread. - Avoiding agents or patches
Device integrity remains intact.
Legacy devices become safer without changes.
Stopping Third-Party Breach Paths
Third parties are a common breach vector.
Stealth networking reduces this risk by:
- Eliminating VPN-based vendor access
Vendors never join internal networks. - Scoping access to specific systems only
No browsing or exploration is possible. - Enforcing time-bound access automatically
Access expires when work is complete. - Logging all sessions centrally
Activity is fully auditable.
Third-party access becomes controlled instead of trusted.
Why Stealth Design Improves HIPAA Outcomes
HIPAA expects healthcare organizations to limit exposure and enforce access intentionally.
Stealth networking supports this by:
- Enforcing minimum necessary access by default
Systems are unreachable unless required. - Reducing breach scope
Fewer systems and records are exposed. - Providing clear audit evidence
Access is identity-verified and session-based. - Minimizing PHI sprawl
Data stays inside protected environments.
Compliance improves when architecture limits reach.
Why Detection Alone Is Not Breach Prevention
Many healthcare organizations rely heavily on monitoring tools.
That approach fails because:
- Alerts occur after access exists
- Attackers blend into normal traffic
- Response time determines damage
Stealth networking removes the conditions attackers need to operate, reducing reliance on rapid detection.
How Mindcore Technologies Designs Stealth Networks for Healthcare
Mindcore helps healthcare organizations prevent breaches by:
- Identifying exposed systems and trust assumptions
Mapping where visibility exists today. - Removing IP-level reachability
Systems are hidden by default. - Implementing identity-driven, session-based access
Access is deliberate and temporary. - Securing remote and vendor workflows without VPNs
Eliminating inherited trust. - Centralizing visibility and audit readiness
Security and compliance teams share clarity.
The goal is prevention through invisibility, not reaction through alerts.
A Simple Breach Prevention Reality Check
Your healthcare environment remains high-risk if:
- Internal systems are discoverable
- VPNs provide network-level access
- Lateral movement is possible
- Vendors have persistent access
- Breach containment requires shutdowns
These are design failures, not tooling gaps.
Final Takeaway
Healthcare breach prevention does not come from more alerts or faster responses. It comes from architectures that deny attackers visibility and reach from the start.
Stealth network design prevents breaches by removing discovery, blocking movement, and enforcing access only when explicitly authorized. Healthcare organizations that adopt it stop attacks early and protect patient trust by design. Those that do not continue to rely on defenses attackers already know how to bypass.