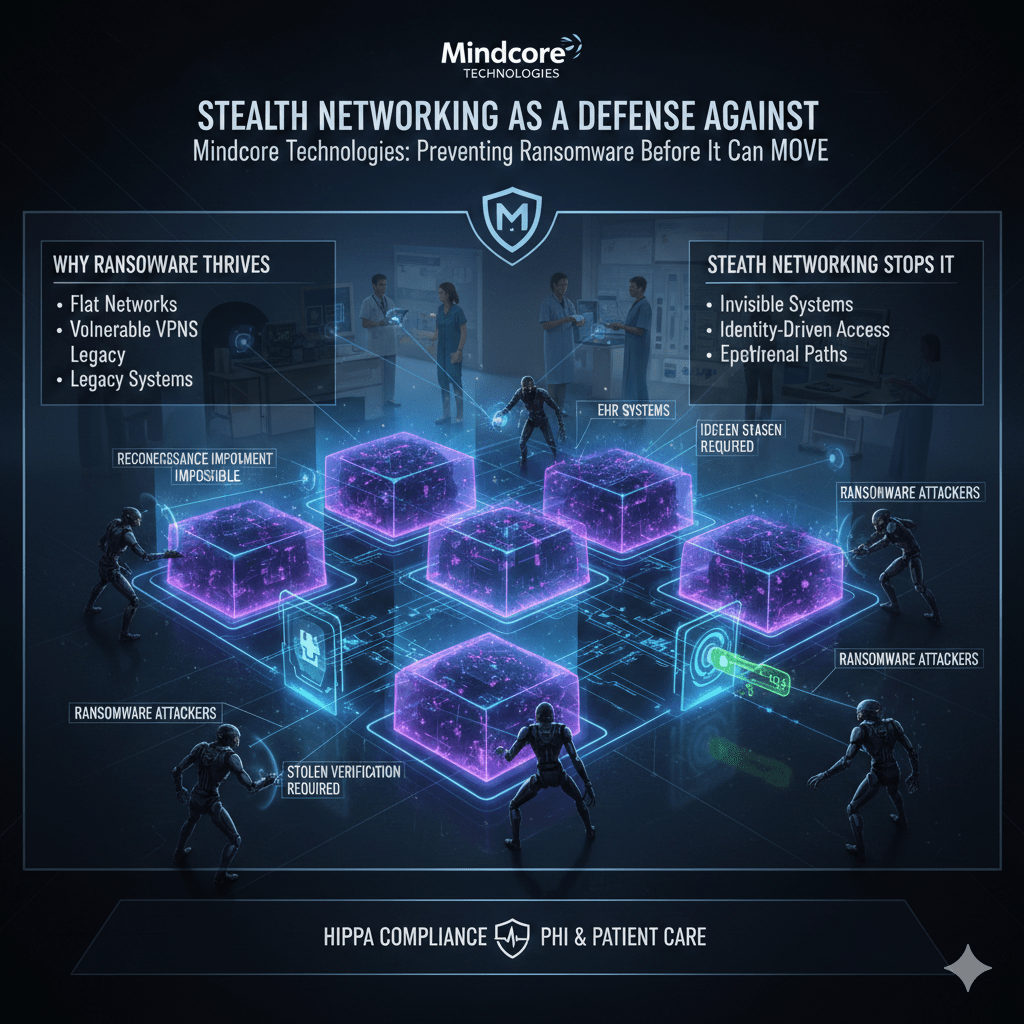
Ransomware does not succeed because encryption is powerful. It succeeds because attackers can see, reach, and move across healthcare networks with ease. Once inside, traditional architectures give them everything they need to spread fast and cause maximum disruption.
Stealth networking breaks this pattern by removing visibility and reachability entirely, not by trying to detect ransomware after it has already landed.
At Mindcore Technologies, healthcare incident analysis shows that environments using stealth networking principles consistently limit ransomware spread, reduce downtime, and avoid the cascading failures that shut down clinical operations.
Why Ransomware Thrives in Healthcare Networks
Healthcare environments are ideal ransomware targets because:
- Networks are flat or loosely segmented
Once attackers gain access, they can scan and pivot quickly. - VPNs extend internal visibility to compromised credentials
Valid logins provide broad access without resistance. - Legacy systems and medical devices are highly reachable
Many cannot be patched or monitored effectively. - Availability pressures delay containment
Security teams hesitate to isolate systems that support care delivery.
Ransomware does not need sophistication when architecture enables speed.
How Ransomware Actually Spreads in Healthcare
Most ransomware campaigns follow a predictable path:
- Initial access through stolen credentials
Phishing, infostealers, or MFA fatigue attacks provide legitimate entry. - Internal reconnaissance
Attackers scan for file servers, EHR systems, backups, and admin tools. - Lateral movement using standard protocols
Activity blends into normal traffic. - Pre-encryption staging
Backups are disabled and recovery paths are removed. - Coordinated encryption and extortion
Damage is maximized across systems.
Traditional networks accelerate every step of this process.
Why Detection Alone Cannot Stop Ransomware
Many healthcare organizations invest heavily in detection.
This fails because:
- Alerts trigger after lateral movement begins
- Ransomware uses legitimate credentials and tools
- Response speed determines damage, not prevention
By the time alerts fire, attackers already have reach.
Stealth networking prevents ransomware by removing the conditions that allow spread, not by chasing alerts.
What Stealth Networking Actually Does
Stealth networking is not just segmentation. It is network invisibility enforced by identity.
In a stealth network:
- Systems do not respond to unauthorized scans
Attackers cannot map internal infrastructure. - Connectivity is created only after identity verification
Access is explicit and deliberate. - Access paths are ephemeral
Sessions disappear when work ends. - Network location provides no trust
Being “inside” grants nothing.
You cannot encrypt what you cannot find.
How Stealth Networking Stops Ransomware Spread
Stealth networking disrupts ransomware at every stage.
It stops:
- Reconnaissance
File servers, backups, and EHR systems are invisible. - Lateral movement
Compromised accounts cannot pivot to other systems. - Mass encryption events
Attackers lack reach beyond a single session. - Backup targeting
Recovery systems remain unreachable.
Containment happens automatically, not during crisis response.
Protecting PHI During Active Ransomware Events
PHI exposure often follows ransomware.
Stealth networking protects PHI by:
- Keeping PHI systems unreachable by default
Access exists only when explicitly authorized. - Separating users from infrastructure
Applications are accessed without exposing networks. - Preventing data discovery and scraping
Attackers cannot locate repositories. - Reducing dependency on endpoint security
Even compromised devices cannot reach sensitive systems.
Data remains protected even when credentials are stolen.
Securing Medical Devices from Ransomware
Medical devices are common ransomware amplifiers.
Stealth networking protects them by:
- Hiding devices from network scans
Devices do not advertise their presence. - Preventing device-to-device communication
Compromise cannot spread laterally. - Avoiding agents or patches
Device integrity and certification remain intact. - Isolating devices from administrative systems
Devices cannot be used as pivot points.
Legacy systems become far less dangerous when invisible.
Eliminating VPN-Based Ransomware Entry Points
VPNs are one of the most exploited ransomware paths.
Stealth networking eliminates this risk by:
- Removing network-level VPN access entirely
Users never join internal networks. - Delivering application-specific access only
No internal visibility is granted. - Reducing credential blast radius
Compromised accounts affect one session. - Allowing instant access revocation
Sessions can be terminated without downtime.
Ransomware loses its fastest entry path.
Why Stealth Networking Improves HIPAA Outcomes
HIPAA exposure increases dramatically during ransomware incidents.
Stealth networking reduces compliance risk by:
- Limiting breach scope
Fewer systems and records are affected. - Enforcing minimum necessary access
Systems are unreachable unless required. - Providing clear audit evidence
Access is identity-verified and session-based. - Reducing incident reporting complexity
Impact is easier to define and defend.
Containment protects both patients and regulatory standing.
Operational Benefits During Ransomware Response
Healthcare organizations using stealth networking benefit operationally by:
- Avoiding full environment shutdowns
Only affected sessions are isolated. - Maintaining clinical access during response
Care delivery continues safely. - Reducing recovery scope and time
Not everything requires rebuilding. - Lowering ransom leverage
Attackers cannot demonstrate widespread control.
Resilience improves without sacrificing availability.
How Mindcore Technologies Uses Stealth Networking to Defend Against Ransomware
Mindcore helps healthcare organizations defend against ransomware by:
- Identifying where ransomware spread is currently possible
Mapping visibility and trust gaps. - Removing network reachability by default
Systems are hidden unless authorized. - Implementing identity-driven, session-based access
Access is precise and temporary. - Securing clinical, administrative, and vendor workflows
Without VPNs or standing trust. - Aligning architecture with HIPAA and operational realities
Protection without disruption.
The goal is stopping ransomware before it can move.
A Simple Ransomware Risk Reality Check
Your healthcare environment remains ransomware-prone if:
- Internal systems are discoverable
- VPNs provide network-level access
- Lateral movement is possible
- Medical devices are reachable
- Response requires shutdowns
These are architectural risks, not tooling gaps.
Final Takeaway
Ransomware succeeds in healthcare because networks are visible and trusted by default. Stealth networking removes that advantage by hiding systems, blocking movement, and enforcing access only when explicitly authorized.
Healthcare organizations that adopt stealth networking reduce ransomware impact, protect PHI under pressure, and maintain clinical operations during attacks. Those that do not remain vulnerable through access models ransomware operators already understand and exploit.
Frequently Asked Questions
What is stealth networking in healthcare cybersecurity?
Stealth networking is a cybersecurity approach that makes systems and applications invisible to unauthorized users by requiring identity verification before access is even possible, reducing exposure to ransomware and external threats through identity-driven secure workspace architecture.
Why is healthcare a major target for ransomware attacks?
Healthcare organizations manage sensitive patient data, critical clinical systems, and time-sensitive operations, making them attractive targets for cybercriminals seeking financial leverage through operational disruption and large-scale ransomware attacks.
How does stealth networking reduce ransomware risk?
Stealth networking limits attack surface by hiding systems from unauthorized discovery, enforcing identity-based access controls, reducing lateral movement opportunities, and isolating access to only approved applications and sessions using zero-trust security principles.
Why is lateral movement dangerous during ransomware attacks?
Lateral movement allows attackers to spread across networks after gaining initial access, increasing operational disruption, exposing additional systems, and expanding the scope of ransomware infections.
How can healthcare organizations strengthen ransomware defense?
Healthcare organizations can improve ransomware resilience through zero-trust architecture, stealth networking, multi-factor authentication, network segmentation, continuous monitoring, endpoint protection, and proactive incident response planning using layered healthcare cybersecurity strategies.
Healthcare Cybersecurity and Stealth Networking Expertise from Matt Rosenthal
Matt Rosenthal, CEO of Mindcore Technologies, has extensive experience helping healthcare organizations strengthen ransomware defense, cybersecurity resilience, and operational continuity through zero-trust and stealth networking strategies. His expertise in identity governance, secure workspace architecture, session-based access controls, threat monitoring, compliance readiness, and healthcare cybersecurity infrastructure helps organizations reduce attack surface while protecting sensitive patient information and critical healthcare systems. Matt’s leadership focuses on building proactive healthcare security frameworks that improve visibility, strengthen operational resilience, reduce enterprise risk, and support long-term protection against evolving cyber threats.