Most healthcare breaches are not about “data.” They are about PHI, and the organizations that misunderstand where it lives or how it moves are the ones that fail audits and suffer ransomware fallout.
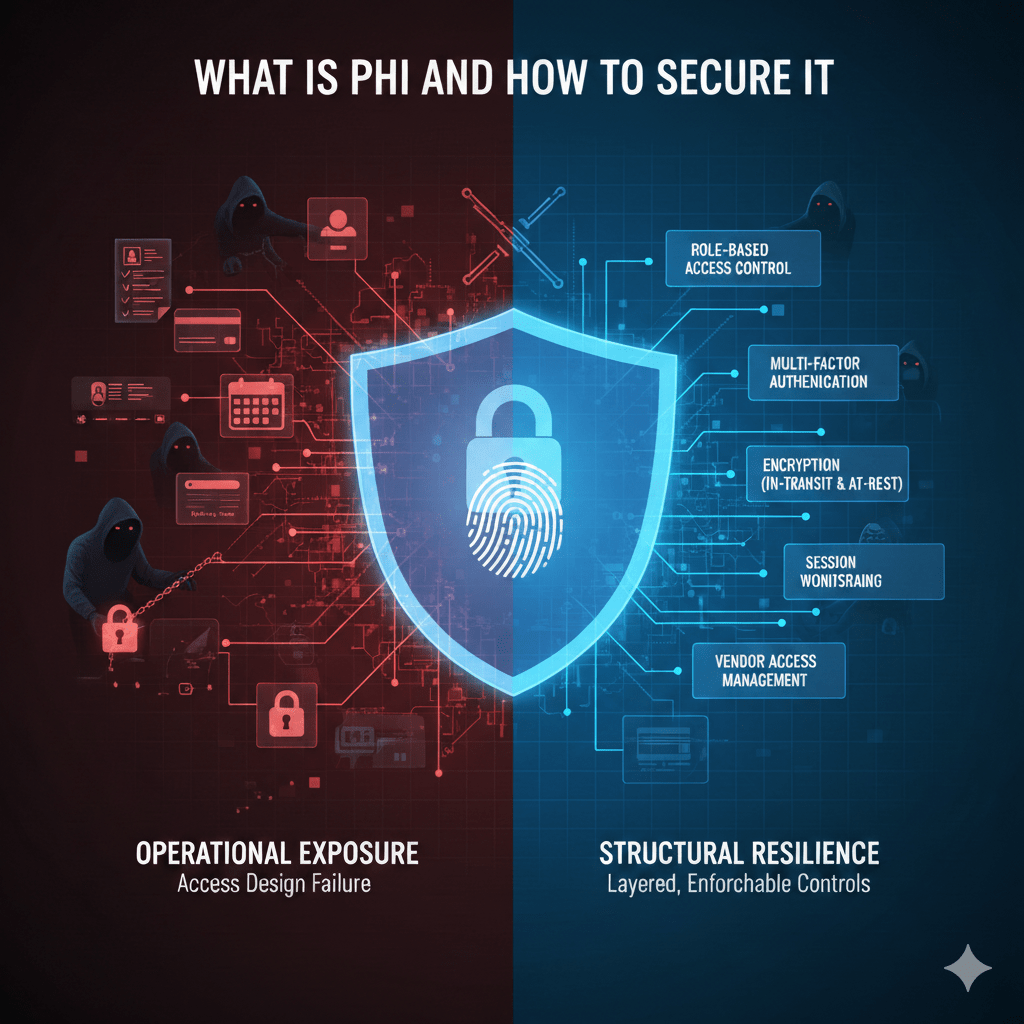
Protected Health Information, or PHI, is not just medical charts. It is any individually identifiable health information that can be tied to a specific person and relates to their condition, treatment, or payment. The security failure is rarely encryption. It is exposure through access design.
At Mindcore Technologies, healthcare risk assessments repeatedly show that PHI is often technically protected but operationally exposed.
What Is PHI Exactly?
PHI includes:
- Medical records and clinical notes
Diagnoses, lab results, imaging, prescriptions, and physician documentation tied to an identifiable individual. - Billing and payment information
Insurance details, claim history, and payment records connected to care. - Demographic identifiers linked to health data
Name, address, birth date, Social Security number, medical record number, when tied to medical context. - Appointment and scheduling records
Visit history connected to a patient identity. - Digital traces within systems
Portal logins, telehealth sessions, and patient communications.
PHI exists anywhere health-related data intersects with personal identifiers.
Where PHI Actually Lives (And Where Organizations Miss It)
Most IT teams focus on EHR systems. That is only part of the picture.
PHI commonly exists in:
- Electronic Health Record (EHR) platforms
The primary repository, but not the only one. - Email systems
Referral communications, patient forms, lab reports. - Cloud storage platforms
Shared folders used for collaboration. - Billing and revenue cycle software
Insurance and payment data. - Telehealth platforms
Video sessions and documentation. - Backup systems
Often overlooked but frequently targeted in ransomware. - Endpoints and downloads
Temporary exports that become permanent exposure.
PHI sprawl increases compliance risk exponentially.
Why PHI Is a Prime Target for Attackers
PHI is valuable because:
- It cannot be reset like a password
Medical histories are permanent. - It enables identity theft and insurance fraud
Combining health and identity data is lucrative. - It creates regulatory leverage
Breach disclosure obligations increase ransom pressure. - It affects care continuity
Healthcare organizations are more likely to pay to restore access.
Attackers do not need all systems. They need reachable PHI.
The Most Common PHI Security Failures
Technical controls often exist. Architectural discipline does not.
Frequent failures include:
- Overly broad access permissions
Users can access more patient data than necessary. - VPN-based network exposure
Compromised credentials unlock internal systems. - PHI stored on endpoints
Downloads, screenshots, exports left unmanaged. - Persistent vendor access
Third parties retain unnecessary system reach. - Lack of session visibility
Access cannot be traced clearly to individuals.
These are structural problems.
How To Secure PHI Properly
Securing PHI requires layered, enforceable controls.
1. Enforce Minimum Necessary Access
PHI security begins with limiting who can see what.
This requires:
- Role-based access control (RBAC)
Permissions strictly aligned with job function. - Elimination of shared accounts
Every user must be uniquely identifiable. - Automatic access expiration
Temporary access must end automatically. - Regular access reviews
Privileges validated quarterly or after role changes.
Access sprawl is the fastest path to breach escalation.
2. Replace Network-Based Trust with Identity-Based Access
Network-level trust amplifies compromise.
Stronger protection requires:
- Application-level access instead of network access
Users connect to systems, not internal subnets. - Session-based authorization
Access exists only during active use. - Multi-factor authentication enforced consistently
Especially for remote and vendor users. - Immediate session revocation capability
Access terminated without shutdown.
Identity must control access, not location.
3. Contain PHI Within Controlled Environments
PHI should not travel freely.
Containment requires:
- Preventing downloads to unmanaged devices
Restricting data export paths. - Isolating execution environments
Secure workspace models limit endpoint exposure. - Segmenting critical systems
EHR, billing, and backup systems isolated from each other. - Blocking lateral movement paths
Compromised accounts cannot pivot across systems.
Containment limits breach scope.
4. Protect PHI in Transit and at Rest
Encryption remains foundational.
IT teams must ensure:
- Encryption in transit for all PHI communications
Secure channels for email, portals, and telehealth. - Encryption at rest across storage systems
Including backups. - Secure API integrations
Third-party connections properly authenticated and encrypted.
Encryption alone does not solve access risk, but it is mandatory.
5. Monitor and Log PHI Access
Audit readiness requires visibility.
Organizations should:
- Log user identity and session activity
Including time, system accessed, and action type. - Retain logs securely
For investigative and compliance use. - Review anomalous behavior proactively
Large exports, off-hours access, unusual patterns.
If you cannot trace PHI interaction, you cannot defend it.
6. Secure Third-Party Access
Vendors are often the weakest link.
PHI protection requires:
- Unique vendor identities
No shared service accounts. - Scoped access to specific systems only
No internal browsing. - Time-bound access windows
Access automatically expires. - Continuous session visibility
Vendor actions are auditable.
Vendor enablement must not equal inherited trust.
How PHI Security Aligns with HIPAA
HIPAA’s Security Rule reinforces PHI protection through:
- Administrative safeguards
- Physical safeguards
- Technical safeguards
For IT teams, this translates to:
- Enforced access control
- Audit logging
- Integrity protection
- Secure transmission
- Incident response readiness
HIPAA compliance and PHI security are inseparable.
How Mindcore Technologies Secures PHI Structurally
Mindcore helps healthcare organizations secure PHI by:
- Mapping where PHI exists and moves
Identifying hidden exposure points. - Redesigning access architecture to enforce least privilege
Removing implicit trust. - Implementing secure workspace containment models
Preventing endpoint data sprawl. - Eliminating VPN-based internal exposure
Reducing credential blast radius. - Centralizing visibility and audit readiness
Making PHI interaction defensible.
The goal is structural resilience, not reactive patching.
A Simple PHI Security Reality Check
Your organization is at elevated risk if:
- PHI is downloadable to personal devices
- VPN access exposes internal systems
- Access permissions rarely expire
- Vendor access is persistent
- Audit logs are incomplete or fragmented
These are preventable architectural weaknesses.
Final Takeaway
PHI is more than medical data. It is identifiable, regulated, and operationally critical information that attackers target because it carries financial and regulatory leverage.
Securing PHI requires disciplined access control, containment, visibility, and architectural design that assumes credentials will be compromised. Organizations that build PHI protection into their access model reduce breach impact, protect patient trust, and remain defensible under audit. Those that rely solely on encryption and policies remain exposed through trust assumptions attackers routinely exploit.
Frequently Asked Questions
What is PHI in healthcare?
PHI, or Protected Health Information, refers to sensitive patient information related to medical records, treatment details, insurance data, billing information, and personally identifiable healthcare information protected under HIPAA.
Why is securing PHI important?
Securing PHI is critical to protecting patient privacy, maintaining regulatory compliance, preventing unauthorized access, and reducing the risk of data breaches and healthcare cyberattacks. Healthcare organizations using secure healthcare IT strategies improve operational resilience and long-term compliance readiness.
What are common threats to PHI security?
Common threats include ransomware attacks, phishing scams, insider threats, weak access controls, unsecured remote access, misconfigured cloud systems, and unauthorized data sharing. Organizations implementing proactive cybersecurity controls can reduce exposure to these evolving healthcare threats.
How can healthcare organizations secure PHI?
Healthcare organizations can secure PHI through encryption, identity governance, multi-factor authentication, secure remote access, continuous monitoring, endpoint protection, and zero-trust security architecture. Strong containment and visibility strategies help reduce unauthorized access and breach impact.
Why is identity-based access control important for PHI protection?
Identity-based access controls ensure only authorized users can access sensitive healthcare information, helping reduce unauthorized exposure and limiting lateral movement during cyber incidents. Organizations implementing Zero Trust security frameworks strengthen PHI containment and audit visibility.
Healthcare Data Protection and PHI Security Expertise from Matt Rosenthal
Matt Rosenthal, CEO of Mindcore Technologies, has extensive experience helping healthcare organizations strengthen PHI protection, cybersecurity resilience, and operational continuity across modern healthcare environments. His expertise in zero-trust architecture, identity governance, secure remote access, threat monitoring, compliance readiness, and healthcare cybersecurity infrastructure helps organizations reduce exposure to evolving cyber threats while protecting sensitive patient information. Matt’s leadership focuses on building proactive healthcare security frameworks that improve operational visibility, strengthen compliance alignment, reduce enterprise risk, and support long-term secure digital healthcare operations.