CMMC 2.0 is not designed to validate intent. It is designed to validate enforcement. Most organizations fail not because they lack policies, but because their architecture cannot consistently enforce the controls those policies describe.
We see this across DoD contractors. Identity controls exist, monitoring tools are deployed, and documentation is complete, yet systems remain exposed, access is too broad, and enforcement varies across environments. During assessment, these gaps become findings.
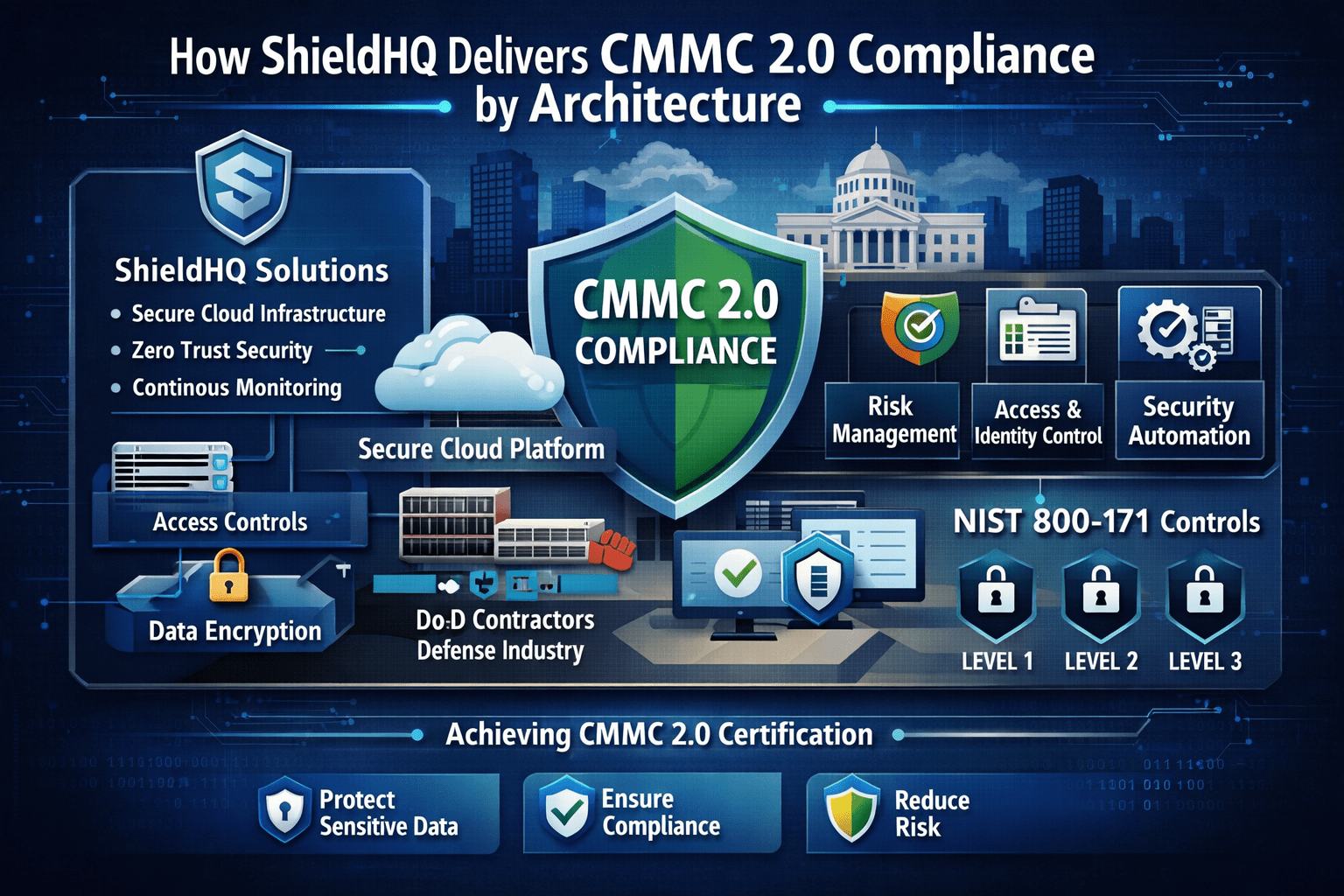
ShieldHQ Powered by Dispersive® Stealth Networking addresses this at the architectural level. Instead of layering controls on top of exposed infrastructure, it removes visibility, enforces identity-driven access, and centralizes monitoring within controlled environments.
CMMC 2.0 compliance becomes a byproduct of how the environment operates, not a separate initiative.
What CMMC 2.0 Actually Requires
CMMC 2.0 simplifies the model but strengthens enforcement expectations.
• Protection of Federal Contract Information, FCI, requiring baseline safeguards against unauthorized access
• Protection of Controlled Unclassified Information, CUI, requiring full alignment with NIST SP 800-171 controls
• Demonstrable control enforcement, requiring proof that controls are active and consistently applied
• Continuous compliance posture, requiring organizations to maintain readiness at all times
These requirements shift the focus from documentation to operational execution.
Why Traditional Compliance Models Fail Under CMMC 2.0
Most organizations approach CMMC 2.0 through policy and tooling.
We see environments where controls are implemented inconsistently across systems.
This results in:
• Over-permissioned access, allowing users broader access than required and increasing risk
• Fragmented monitoring, creating gaps in visibility across cloud, on-prem, and endpoints
• Exposed infrastructure, making systems discoverable and vulnerable to targeting
• Inconsistent enforcement, leading to audit findings despite documented controls
CMMC 2.0 assessors evaluate whether controls are enforced in practice.
Compliance by Documentation vs Compliance by Architecture
Documentation-Based Compliance (Traditional Approach)
Organizations rely on policies and procedures.
This creates a framework but does not ensure consistent enforcement.
Tool-Based Compliance (Layered Controls)
Organizations deploy multiple tools to meet requirements.
This improves coverage but introduces gaps between systems.
Architecture-Driven Compliance (ShieldHQ Approach)
ShieldHQ enforces compliance through controlled environments.
This ensures controls are active, consistent, and continuously applied.
How ShieldHQ Delivers CMMC 2.0 Compliance
ShieldHQ aligns directly with the core control domains required for CMMC 2.0.
Access Control Enforcement
• Enforces least privilege, ensuring users only access systems necessary for their role
• Restricts access to controlled environments, eliminating direct exposure to infrastructure
• Supports role-based access policies, aligning permissions with job responsibilities
Identity and Authentication
• Enforces multi-factor authentication, strengthening identity verification across all access points
• Provides session-based access control, ensuring access is continuously validated
• Tracks user identity across all interactions, improving accountability and traceability
Data Protection and System Security
• Encrypts data in transit, protecting information during communication
• Secures data at rest, preventing unauthorized access to stored data
• Removes infrastructure from discovery, reducing attack surface and exposure
Audit and Accountability
• Captures all user and system activity, creating complete audit trails for compliance
• Centralizes logging, ensuring consistent visibility across all environments
• Protects log integrity, preventing tampering and ensuring reliable audit evidence
Incident Response and Monitoring
• Provides real-time visibility, enabling faster detection of potential threats
• Supports containment through isolation, limiting the spread of incidents
• Enables structured response workflows, improving incident handling and recovery
Architecture Requirements for CMMC 2.0 Compliance
CMMC 2.0 requires enforceable architecture, not just control definitions.
Identity-Centered Security Architecture
• Multi-factor authentication, ensuring strong and consistent user verification
• Role-based access control, limiting access based on job function
• Least privilege enforcement, reducing unnecessary permissions and exposure
Controlled and Isolated Environments
• Protects sensitive data, keeping it within secure and controlled systems
• Limits lateral movement, preventing attackers from moving across environments
• Improves containment, isolating incidents and reducing impact
Centralized Monitoring and Visibility
• Consolidates logs, providing a unified and reliable source of activity data
• Improves detection, enabling faster identification of anomalies and threats
• Supports compliance, ensuring audit-ready reporting and traceability
How ShieldHQ Reduces CMMC 2.0 Complexity
ShieldHQ simplifies compliance by aligning architecture with requirements.
• Secure workspaces isolate FCI and CUI, reducing scope and improving control over sensitive data
• Stealth networking removes infrastructure from discovery, minimizing exposure and attack surface
• Identity-driven access enforces strict authentication, aligning with Zero Trust and CMMC principles
• Centralized monitoring provides audit-ready visibility, simplifying evidence collection and reporting
This reduces the operational burden of maintaining compliance.
How Mindcore Technologies Delivers CMMC 2.0 by Design
Mindcore Technologies helps organizations implement compliance through architecture.
• Assess current environment, identifying gaps in enforcement and exposure
• Map CMMC 2.0 requirements to systems, ensuring alignment with NIST SP 800-171
• Design secure architecture, enforcing controls across all environments
• Implement ShieldHQ, enabling continuous and enforceable compliance
• Prepare for assessments, ensuring audit readiness and validation
• Provide ongoing support, maintaining compliance as requirements evolve
Execution determines whether compliance is sustainable.
Final Takeaway
CMMC 2.0 requires organizations to demonstrate that security controls are actively enforced across access, identity, data protection, and monitoring, with a focus on continuous compliance rather than periodic validation. ShieldHQ delivers this by removing infrastructure from discovery, enforcing identity-driven access, and centralizing monitoring within controlled environments, which ensures that controls are consistently applied and audit-ready at all times. Organizations that rely on documentation and layered tools will continue facing gaps during assessment, while those that adopt architecture-driven compliance align their environment with CMMC 2.0 requirements by design.
If your organization is preparing for CMMC 2.0 and needs to move from policy-based compliance to enforceable architecture, schedule a free strategy call with Mindcore Technologies to assess your current systems and define a path forward.