Most organizations overcomplicate CMMC. They treat it like a long checklist or a documentation exercise. The reality is more direct. Certification comes down to three things: knowing your scope, enforcing the required controls, and passing an assessment.
We see companies stall because they try to solve everything at once. That leads to delays, higher costs, and incomplete implementation. The organizations that succeed focus on structure first, then execution.
If you break CMMC down correctly, the path becomes clear.
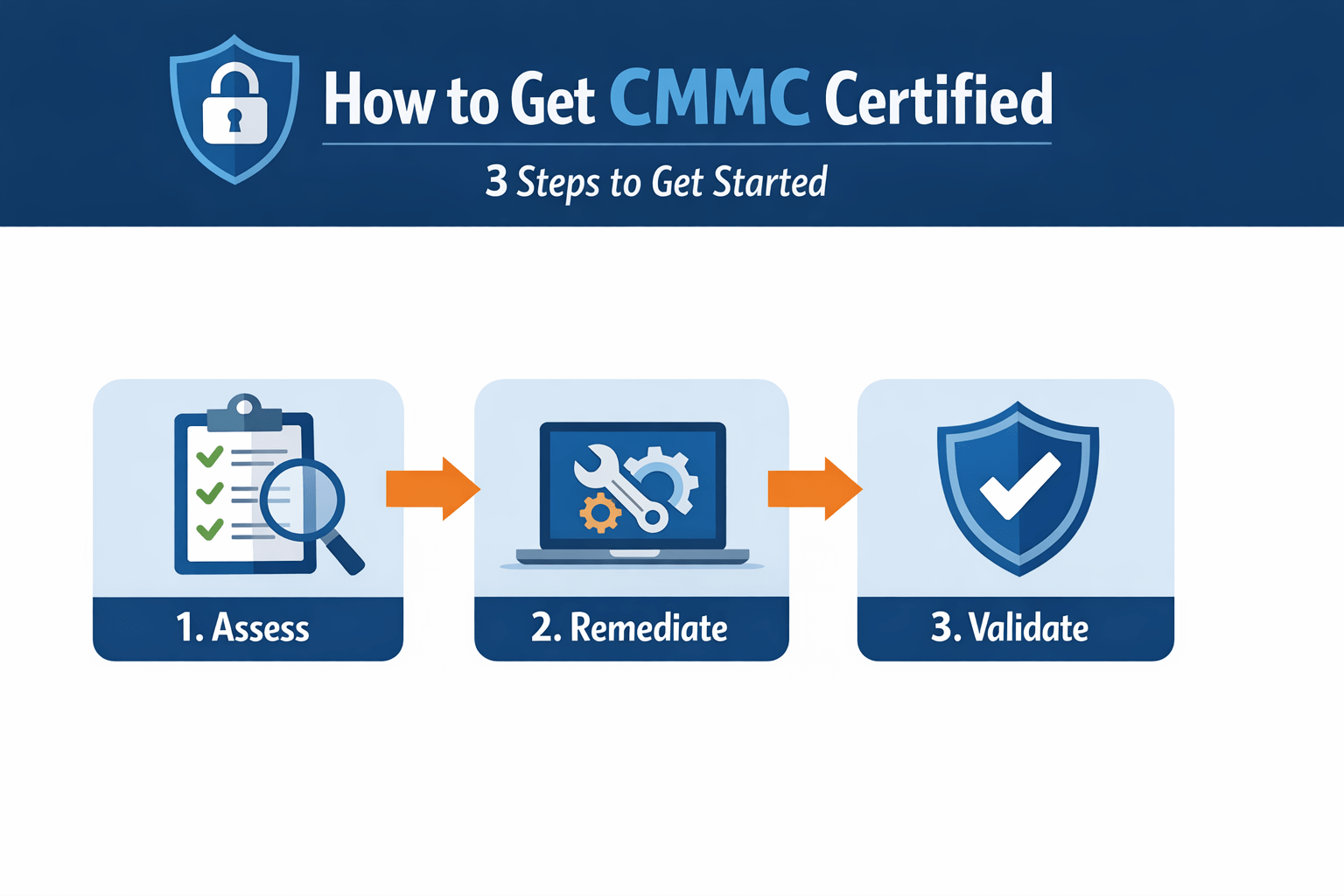
Overview: The 3-Step Path to CMMC Certification
CMMC certification can be approached through three structured steps.
• Define scope and required level, identifying what data and systems are in scope
• Implement and enforce controls, aligning systems with CMMC requirements
• Prepare for and pass assessment, validating that controls are operational
Each step builds on the previous one. Skipping any step creates gaps that will surface during assessment.
Step 1: Define Your Scope and Required CMMC Level
You cannot implement CMMC without knowing what applies to your organization.
What This Step Involves
• Identify whether you handle FCI or CUI, determining your compliance level
• Map data flows, understanding where sensitive information is stored and processed
• Define system boundaries, identifying which systems are in scope
Why This Step Matters
• Prevents over-scoping, avoiding unnecessary cost and complexity
• Ensures correct level alignment, reducing risk of under-preparation
• Establishes a clear foundation, guiding all future implementation
What We See in Practice
Organizations often misidentify their scope. They either include too much or overlook critical systems. Both lead to failure during assessment.
Step 2: Implement and Enforce CMMC Controls
Once scope is defined, controls must be applied and enforced across systems.
Core Control Areas
• Access control, restricting users to only what they need and enforcing least privilege
• Identification and authentication, ensuring strong identity verification across all systems
• Data protection, securing FCI and CUI in transit and at rest
• Monitoring and logging, capturing all activity for visibility and audit readiness
• Incident response, enabling detection and containment of security events
What This Step Requires
• Technical implementation, applying controls across systems and environments
• Policy alignment, ensuring documentation reflects actual enforcement
• Continuous validation, confirming controls operate consistently
Why Most Organizations Fail Here
We see controls implemented partially or inconsistently.
• Access is too broad, increasing risk and failing least privilege requirements
• Monitoring is fragmented, reducing visibility into system activity
• Systems remain exposed, creating gaps in protection
CMMC assessors are not evaluating intent. They are evaluating execution.
Step 3: Prepare for and Pass the CMMC Assessment
Certification requires validation by an assessor, depending on your level.
Assessment Types
• Level 1, self-assessment, requiring internal validation of controls
• Level 2, third-party assessment, conducted by a C3PAO for most contractors
• Level 3, government assessment, involving direct DoD evaluation
What This Step Involves
• Evidence collection, demonstrating that controls are implemented and enforced
• Control validation, ensuring systems operate as required
• Audit readiness, preparing documentation and logs for review
What We See in Practice
Organizations that treat assessment as a final step often fail.
• Controls are not fully operational
• Evidence is incomplete or inconsistent
• Gaps are identified during assessment instead of before
Preparation must happen before the audit begins.
Common Mistakes That Delay Certification
Most delays are caused by avoidable issues.
• Starting without defining scope, leading to rework and confusion
• Focusing on documentation instead of enforcement, creating audit gaps
• Underestimating Level 2 requirements, especially around monitoring and access control
• Waiting for contract deadlines, compressing timelines and increasing cost
These mistakes increase both risk and effort.
Infrastructure Requirements for Successful Certification
CMMC certification requires enforceable architecture, not just controls.
Identity-Centered Access Control
• Multi-factor authentication, ensuring strong user verification
• Role-based access control, limiting access based on job function
• Least privilege enforcement, reducing unnecessary permissions
Controlled and Isolated Environments
• Protects sensitive data, keeping it within secure systems
• Limits lateral movement, reducing breach impact
• Improves containment, isolating incidents effectively
Centralized Monitoring and Visibility
• Consolidates logs, providing a single source of truth
• Improves detection, identifying threats faster
• Supports compliance, enabling audit-ready reporting
How ShieldHQ Accelerates the Certification Process
ShieldHQ Powered by Dispersive® Stealth Networking aligns your environment with CMMC requirements from the start.
• Secure workspaces isolate FCI and CUI, ensuring controlled access and reducing scope complexity
• Stealth networking removes infrastructure from discovery, minimizing attack surface
• Identity-driven access enforces strict authentication, aligning with compliance requirements
• Centralized monitoring provides audit-ready visibility, simplifying evidence collection
This reduces the time and effort required to achieve certification.
How Mindcore Technologies Helps You Get Certified Faster
Mindcore Technologies provides structured guidance and execution support.
• Define scope and required level, ensuring correct alignment from the start
• Identify gaps in controls, focusing on enforcement rather than documentation
• Design secure architecture, aligning systems with CMMC requirements
• Implement ShieldHQ, reducing exposure and improving compliance
• Prepare for assessment, ensuring audit readiness
• Provide ongoing support, maintaining certification over time
Execution determines whether certification is achieved efficiently.
Final Takeaway
Getting CMMC certified comes down to three steps, defining your scope and required level, implementing and enforcing the necessary controls, and preparing for and passing the assessment, but success depends on execution rather than documentation alone. Organizations that approach CMMC as a checklist often fail due to incomplete enforcement, while those that align their architecture with compliance requirements achieve certification more efficiently and with fewer gaps. Starting early, focusing on enforceable controls, and structuring the process correctly are the key factors that determine success.
If your organization is preparing for CMMC certification and needs a clear, structured path forward, schedule a free strategy call with Mindcore Technologies to assess your current environment and define a path to certification.