Most organizations invest in data security tools and assume data governance is “handled.” That assumption is why sensitive data keeps getting exposed without any systems being hacked.
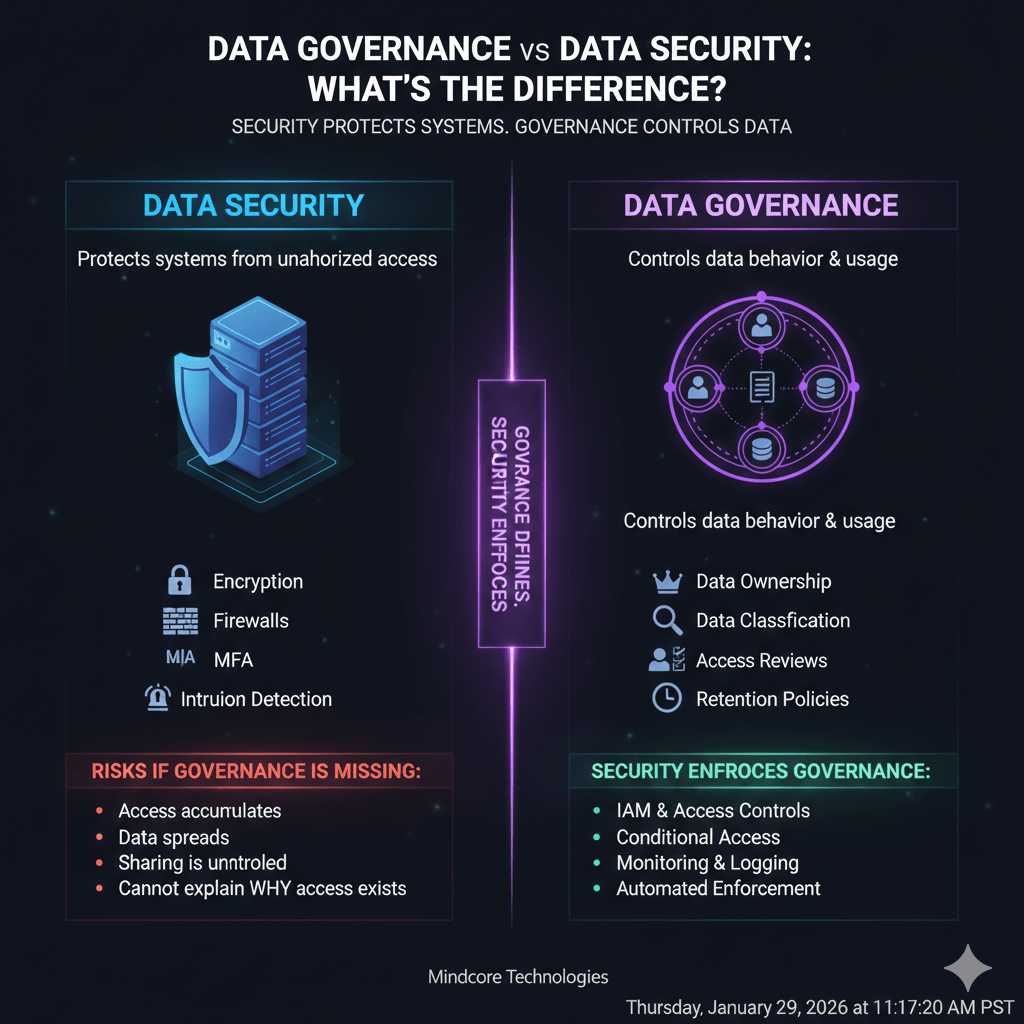
Data security protects systems.
Data governance controls data behavior.
Confusing the two creates blind spots attackers and auditors exploit.
At Mindcore Technologies, breach investigations repeatedly show the same pattern: security tools were present, but governance was absent. Access was legitimate, activity was allowed, and exposure was inevitable.
This guide explains the difference in practical terms and why you need both.
The One-Sentence Difference
- Data security answers: How do we protect systems from unauthorized access?
- Data governance answers: Who should access which data, how, and under what conditions?
Security enforces controls.
Governance defines what those controls should enforce.
Why This Confusion Matters
Most data breaches today occur:
- Inside authenticated environments
- Through valid credentials
- Using approved tools
- During normal business hours
That means security worked. Governance failed.
What Data Security Actually Covers
Data security focuses on technical protection mechanisms, including:
- Encryption at rest and in transit
- Firewalls and network controls
- Endpoint protection
- MFA and authentication
- Intrusion detection and prevention
- Backup and recovery systems
These controls protect infrastructure and access paths.
What security does well:
It blocks outsiders and detects technical attacks.
What it does not do:
It does not decide who should access data or whether access still makes sense.
What Data Governance Actually Covers
Data governance defines rules, ownership, and accountability for data, including:
- Data ownership and accountability
- Data classification and sensitivity levels
- Access rules tied to job roles
- Data sharing and usage policies
- Retention and deletion requirements
- Auditability and reporting
Governance controls how data is used after access is granted.
A Real-World Example (Where Security Succeeds and Governance Fails)
Scenario:
An employee with valid credentials accesses a shared drive containing sensitive customer data they no longer need.
- MFA is enabled
- Firewall rules are correct
- Endpoint protection is active
- No malware is present
Result:
No security alerts trigger.
But sensitive data is exposed unnecessarily.
Conclusion:
Security worked. Governance failed.
Why Data Security Alone Is Not Enough
Security assumes:
- Access decisions are correct
- Permissions are intentional
- Data placement is controlled
Governance challenges those assumptions.
Without governance:
- Access accumulates over time
- Data spreads across platforms
- Sharing links bypass controls
- No one knows who owns what
Security tools enforce access. Governance determines whether access should exist.
Governance Without Security Also Fails
Governance alone is not sufficient.
Policies without enforcement result in:
- Manual processes ignored under pressure
- Inconsistent application
- No real protection against misuse
Security is how governance becomes enforceable.
How Data Governance and Data Security Work Together
Think of the relationship like this:
- Governance defines intent
- Security enforces execution
Examples:
- Governance defines who can access financial data
- Security enforces that rule through identity and access controls
- Governance defines retention periods
- Security enforces deletion and protection
- Governance defines sharing rules
- Security monitors and blocks violations
One without the other fails.
Common Signs You Have Security Without Governance
You likely lack governance if:
- No one owns critical datasets
- Access reviews are rare or manual
- Sensitive data lives everywhere
- Sharing links are uncontrolled
- Data is retained indefinitely
- You cannot explain why someone has access
These are governance failures, not security failures.
Common Signs You Have Governance Without Security
You likely lack security enforcement if:
- Policies exist but are not automated
- Access depends on trust instead of controls
- Logs are not centralized
- Violations are detected too late
Governance without enforcement is advisory, not protective.
Why Growing Businesses Feel This First
As organizations scale:
- SaaS platforms multiply
- Data volume explodes
- Roles change frequently
- Vendors gain access
- Compliance pressure increases
Security tools scale faster than governance discipline. That gap creates exposure.
How Breaches Happen at the Governance Layer
Most modern breaches involve:
- Legitimate credentials
- Approved platforms
- Excessive access
- Poor visibility
Attackers don’t break security. They abuse governance gaps.
How Mindcore Technologies Aligns Governance and Security
Mindcore helps organizations close the gap by:
- Defining data ownership and classification
- Designing identity-based access models
- Enforcing least privilege with automation
- Securing cloud and SaaS data flows
- Implementing audit visibility and monitoring
- Aligning governance decisions with security controls
We treat governance and security as a single operating model, not separate projects.
A Quick Decision Test
Ask one question:
“If this person accesses this data today, can we explain exactly why?”
If the answer is unclear, governance is missing.
Final Takeaway
Data security protects systems. Data governance controls data behavior. One without the other fails quietly and predictably. Most organizations do not suffer data breaches because security tools are missing. They suffer because access decisions were never governed.
Organizations that align governance with security reduce exposure, simplify compliance, and respond to incidents faster. Those that treat governance as paperwork eventually learn its value through exposure.