VPNs are no longer a secure access solution for healthcare. They were never designed to protect PHI against credential theft, ransomware, or modern lateral movement techniques. Today, VPNs act less like a safeguard and more like a trusted tunnel attackers are eager to exploit.
Healthcare breaches rarely start with firewall failures. They start when attackers log in through VPNs using valid credentials.
At Mindcore Technologies, healthcare incident analysis consistently shows that VPN access is one of the most common enablers of large-scale breaches, prolonged downtime, and HIPAA exposure.
Why VPNs Create Risk in Healthcare Environments
VPNs are fundamentally built on network trust, not access control.
They introduce risk because:
- VPNs grant broad internal network visibility
Once connected, users can often reach far more than their role requires, increasing blast radius if credentials are compromised. - Access is persistent, not contextual
VPN sessions remain active longer than needed, creating unnecessary exposure. - VPN trust is location-based, not identity-based
Being “connected” matters more than who the user is or what they are authorized to do. - Endpoints become part of the security boundary
Infected or unmanaged devices undermine all VPN protections.
VPNs assume trusted users on trusted devices. Modern healthcare cannot make that assumption.
How Attackers Exploit VPN Access
Attackers no longer brute-force VPNs. They log in legitimately.
Common attack paths include:
- Credential theft through phishing and infostealers
Valid VPN credentials bypass perimeter defenses entirely. - MFA fatigue and push bombing attacks
Users approve access under pressure. - Session hijacking
Attackers steal active VPN sessions without triggering reauthentication. - Exploitation of unpatched VPN appliances
Vulnerabilities expose entire environments instantly.
Once connected, attackers inherit internal trust.
Why VPN-Based Security Fails Against Ransomware
Ransomware thrives in VPN-enabled environments.
VPNs enable ransomware by:
- Allowing network reconnaissance
Attackers can scan file servers, backups, and EHR systems. - Enabling rapid lateral movement
Flat or loosely segmented networks accelerate spread. - Providing access to administrative systems
Backup deletion and security disablement occur early. - Expanding encryption scope
Network reach determines damage.
VPNs turn ransomware into enterprise-wide incidents.
The Hidden Compliance Risk of VPN Access
VPNs complicate HIPAA compliance more than most organizations realize.
They increase compliance risk because:
- Minimum necessary access is difficult to enforce
VPN users often see systems they do not need. - Audit trails are unclear
Network access does not map cleanly to application activity. - Third-party access is overly broad
Vendors often inherit internal visibility. - PHI sprawl increases
Endpoints become data exposure points.
Auditors care less about VPN presence and more about what VPN access allows.
Why VPNs Persist Despite the Risk
VPNs remain in healthcare because they feel familiar.
Organizations keep them because:
- They were the fastest way to enable remote access
- They appear simple to deploy
- They solved yesterday’s problems
- They are deeply embedded in workflows
But familiarity does not equal safety.
What Replaces VPNs in Modern Healthcare Security
Healthcare organizations are eliminating VPNs by redesigning access entirely.
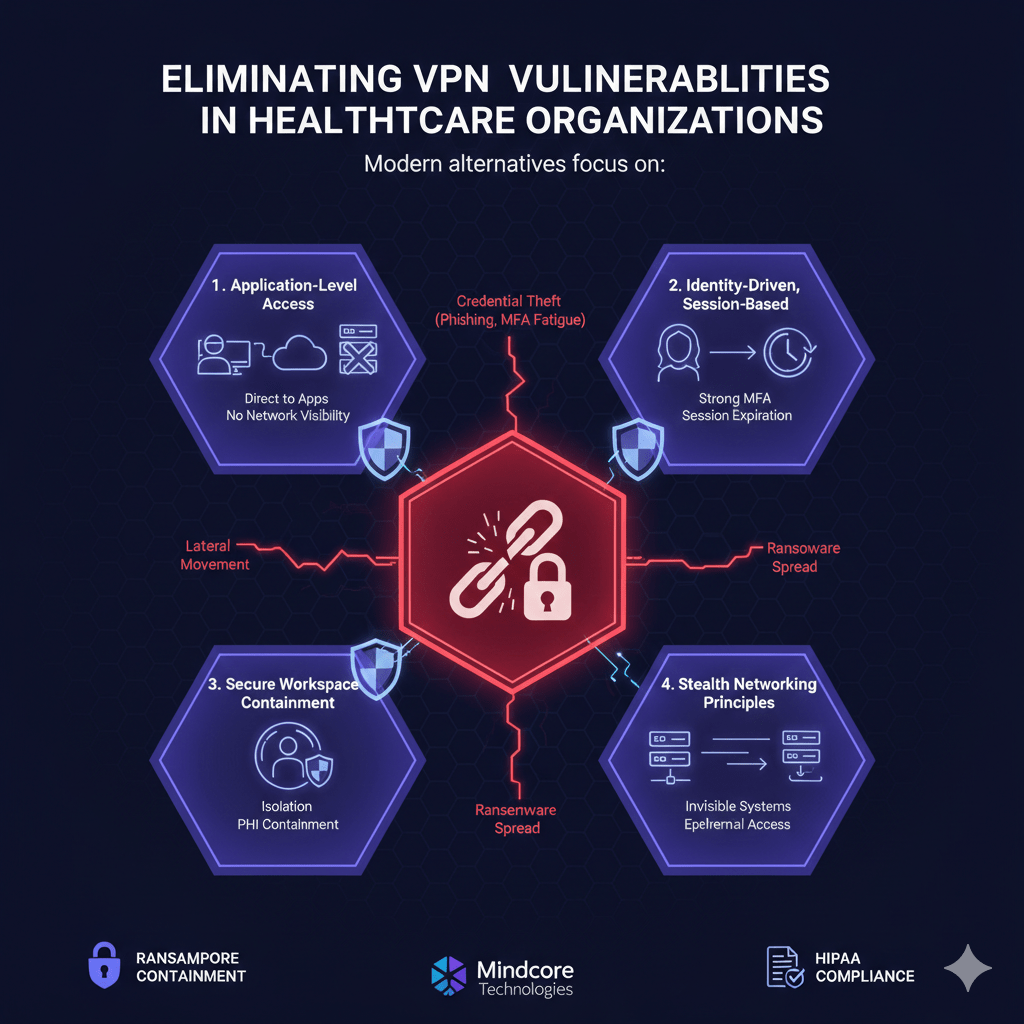
Modern alternatives focus on:
1. Application-Level Access Instead of Network Access
Users do not need network visibility.
Modern access delivers:
- Direct access to approved applications only
No browsing, scanning, or discovery. - No internal IP exposure
Systems remain invisible. - No inherited trust
Each session is explicitly authorized.
This removes the network from the trust equation.
2. Identity-Driven, Session-Based Access
Access should be tied to identity and purpose.
Modern models enforce:
- Strong identity verification
Every user is uniquely identifiable. - Role-based access scope
Permissions align with job function. - Automatic session expiration
Access ends when work ends.
Stolen credentials no longer unlock the environment.
3. Secure Workspace Containment
Secure workspaces replace VPN tunnels.
They provide:
- Isolation between users and systems
Compromise does not spread. - PHI containment inside controlled environments
Data does not reach endpoints. - Consistent enforcement across locations
Home, clinic, and vendor access behave the same.
Workspaces remove lateral movement paths entirely.
4. Stealth Networking Principles
VPNs expose networks. Stealth hides them.
Stealth access ensures:
- Systems are unreachable by default
No response to unauthorized probes. - Access paths exist only during approved sessions
Connectivity disappears automatically. - Attackers cannot map internal infrastructure
Reconnaissance fails.
You cannot attack what you cannot see.
How Eliminating VPNs Improves Ransomware Defense
Removing VPNs dramatically reduces ransomware impact by:
- Blocking network discovery
Attackers cannot locate encryption targets. - Preventing lateral movement
One compromised account cannot spread. - Protecting backups and infrastructure
Admin systems remain unreachable. - Allowing instant access revocation
Sessions can be terminated without downtime.
Ransomware becomes containable instead of catastrophic.
Operational Benefits Beyond Security
Healthcare organizations that eliminate VPNs also gain:
- Simpler remote access for clinicians
No VPN troubleshooting or connectivity issues. - Faster onboarding and offboarding
Access is granted and revoked centrally. - Consistent access across locations
Security does not depend on geography. - Lower IT operational overhead
Fewer appliances, patches, and emergency fixes.
Security and productivity stop competing.
How Mindcore Technologies Eliminates VPN Risk in Healthcare
Mindcore helps healthcare organizations move beyond VPNs by:
- Identifying where VPN trust creates exposure
Mapping current access paths. - Replacing VPN-based access with secure workspace architecture
Removing network visibility. - Implementing identity-driven, session-limited access
Access is precise and temporary. - Containing PHI inside controlled environments
Preventing data sprawl. - Aligning access design with HIPAA requirements
Making compliance structural.
The objective is secure access without inherited trust.
A Simple VPN Risk Reality Check
Your healthcare environment remains VPN-dependent if:
- Remote users join internal networks
- VPN credentials unlock multiple systems
- Vendors use persistent VPN access
- PHI exists on endpoints
- Breach response requires VPN shutdowns
These are design flaws, not configuration issues.
Final Takeaway
VPNs are no longer a secure foundation for healthcare access. They were built for a different threat model and now serve as a primary attack path.
Healthcare organizations that eliminate VPNs and adopt identity-driven, workspace-based access dramatically reduce breach impact, ransomware spread, and HIPAA exposure. Those that continue relying on VPNs remain vulnerable through trust assumptions attackers already exploit.