Healthcare cybersecurity does not fail because teams lack tools. It fails because most environments were architected for a threat model that no longer exists. Perimeters, VPNs, and flat internal trust zones were built for a time when users, devices, and data lived in predictable places. Modern threats exploit that mismatch relentlessly.
Attackers no longer fight defenses. They log in, move quietly, and abuse trust.
At Mindcore Technologies, healthcare incident analysis shows a clear pattern. Organizations with modern, access-contained architectures limit damage and recover quickly. Those relying on legacy network-centric models experience widespread disruption, prolonged downtime, and elevated HIPAA exposure.
What Defines “Modern Threats” in Healthcare
Modern healthcare threats are defined less by sophistication and more by how efficiently they exploit trust.
They include:
- Credential-based attacks
Phishing, MFA fatigue, infostealers, and session hijacking provide valid access without triggering alarms. - Ransomware with lateral movement
Attackers prioritize speed and reach over stealth. - Third-party and vendor compromise
Trusted external access becomes an internal breach path. - Living-off-the-land techniques
Legitimate tools are used to blend into normal operations.
These threats assume access will eventually happen. Architecture must assume the same.
Why Legacy Healthcare Architectures Collapse Under These Threats
Traditional healthcare cybersecurity architecture is built around network trust.
It fails because:
- VPNs extend full internal visibility
One compromised account exposes broad infrastructure. - Flat or loosely segmented networks enable spread
Lateral movement is easy and fast. - Endpoints are treated as trusted security boundaries
Compromised devices undermine all controls. - Detection is prioritized over containment
Alerts arrive after attackers already moved.
This model amplifies breaches instead of containing them.
What Modern Healthcare Cybersecurity Architecture Requires
Architecture built for modern threats must assume:
- Credentials will be compromised
- Devices will fail
- Third parties will be targeted
- Attackers will blend in
Modern architecture is designed to limit what happens next.
That requires four core principles.
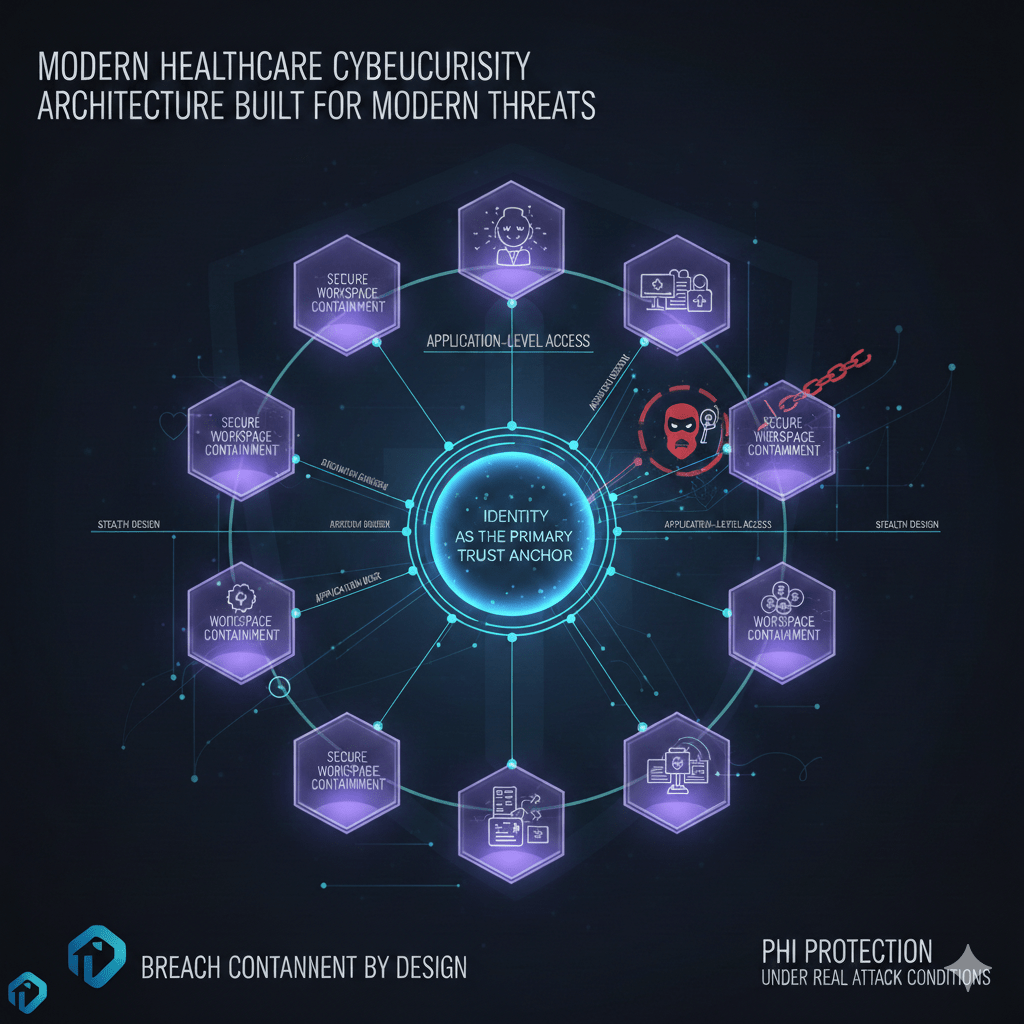
1. Identity as the Primary Trust Anchor
Modern architecture replaces network trust with identity trust.
This means:
- Access decisions are based on verified identity and role
Not location, IP address, or device ownership. - Every session is explicitly authorized
Trust is not inherited. - Access expires automatically
Standing privileges are eliminated.
Identity becomes the control plane, not the network.
2. Application-Level Access Instead of Network Access
Modern threats thrive on network visibility.
Modern architecture removes it by:
- Delivering access to applications, not infrastructure
Users never see internal networks. - Eliminating internal scanning and discovery
Systems are invisible unless explicitly allowed. - Blocking lateral movement by design
One application does not lead to another.
Access is precise, scoped, and contained.
3. Secure Workspace Containment
Secure workspaces are the execution layer of modern architecture.
They provide:
- Isolation between users and systems
Compromise does not spread. - PHI containment inside controlled environments
Data does not reach endpoints. - Session-based control and instant revocation
Access can be terminated immediately. - Consistent enforcement across locations
Clinic, home, and vendor access behave the same.
Workspaces turn breaches into isolated events.
4. Invisibility Through Stealth Design
You cannot attack what you cannot see.
Modern architecture reduces exposure by:
- Hiding systems from unauthorized discovery
No response to scans or probes. - Creating access paths only after authorization
Connectivity is ephemeral. - Eliminating always-on connectivity
Systems are unreachable by default.
Stealth design removes reconnaissance as an attack stage.
How This Architecture Stops Ransomware
Ransomware relies on reach and speed.
Modern architecture disrupts both by:
- Preventing discovery of file systems and backups
Attackers cannot locate targets. - Limiting encryption scope
Compromised credentials affect one workspace, not the environment. - Blocking lateral spread
Movement paths do not exist. - Allowing fast containment without shutdowns
Operations continue while access is revoked.
Ransomware becomes survivable, not catastrophic.
Protecting PHI Under Real Attack Conditions
PHI protection fails when access is broad.
Modern architecture protects PHI by:
- Containing data within secure workspaces
No endpoint storage or syncing. - Restricting data movement actions
Copy, export, and download paths are controlled. - Reducing reliance on endpoint compliance
Data protection does not depend on device hygiene. - Providing clear audit trails
Every PHI interaction is attributable.
PHI remains protected even during active compromise.
Third-Party Risk Reduction Through Architecture
Third-party access is unavoidable in healthcare.
Modern architecture reduces its risk by:
- Eliminating VPN-based vendor access
Vendors never join internal networks. - Scoping access to specific systems only
No exploration or lateral movement. - Enforcing time-bound access automatically
Access expires without manual action. - Centralizing visibility and accountability
Vendor actions are always auditable.
Vendor enablement no longer equals inherited risk.
Why This Architecture Improves HIPAA Outcomes
HIPAA compliance improves when exposure is minimized continuously.
Modern architecture supports this by:
- Enforcing minimum necessary access automatically
Access scope is narrow and provable. - Reducing breach scope
Fewer systems and records are affected. - Producing audit-ready evidence by default
No reconstruction required. - Aligning security with real workflows
Compliance does not disrupt care.
Compliance becomes a byproduct of good design.
How Mindcore Technologies Designs Healthcare Cybersecurity for Modern Threats
Mindcore builds healthcare cybersecurity architecture by:
- Identifying implicit trust and exposure points
Mapping where legacy assumptions exist. - Replacing network-centric access with identity-driven models
Removing inherited trust. - Implementing secure workspace and stealth access architectures
Containing users and systems. - Designing for breach containment, not breach avoidance alone
Limiting impact when incidents occur. - Aligning architecture with HIPAA and operational realities
Protecting care delivery and compliance simultaneously.
The focus is resilience through design.
A Simple Architecture Reality Check
Your healthcare environment is not built for modern threats if:
- VPNs expose internal networks
- Compromised credentials enable lateral movement
- PHI exists on endpoints
- Vendor access is persistent
- Breach response requires shutdowns
These are architectural gaps, not tool deficiencies.
Final Takeaway
Modern healthcare threats exploit trust, not vulnerabilities. Architectures built on perimeter defense and internal trust zones cannot keep up.
Healthcare cybersecurity architecture built for modern threats removes implicit trust, hides systems by default, and limits access scope automatically. Organizations that adopt this model contain attacks early, protect PHI under pressure, and maintain operations during incidents. Those that do not remain dependent on assumptions attackers already know how to abuse.