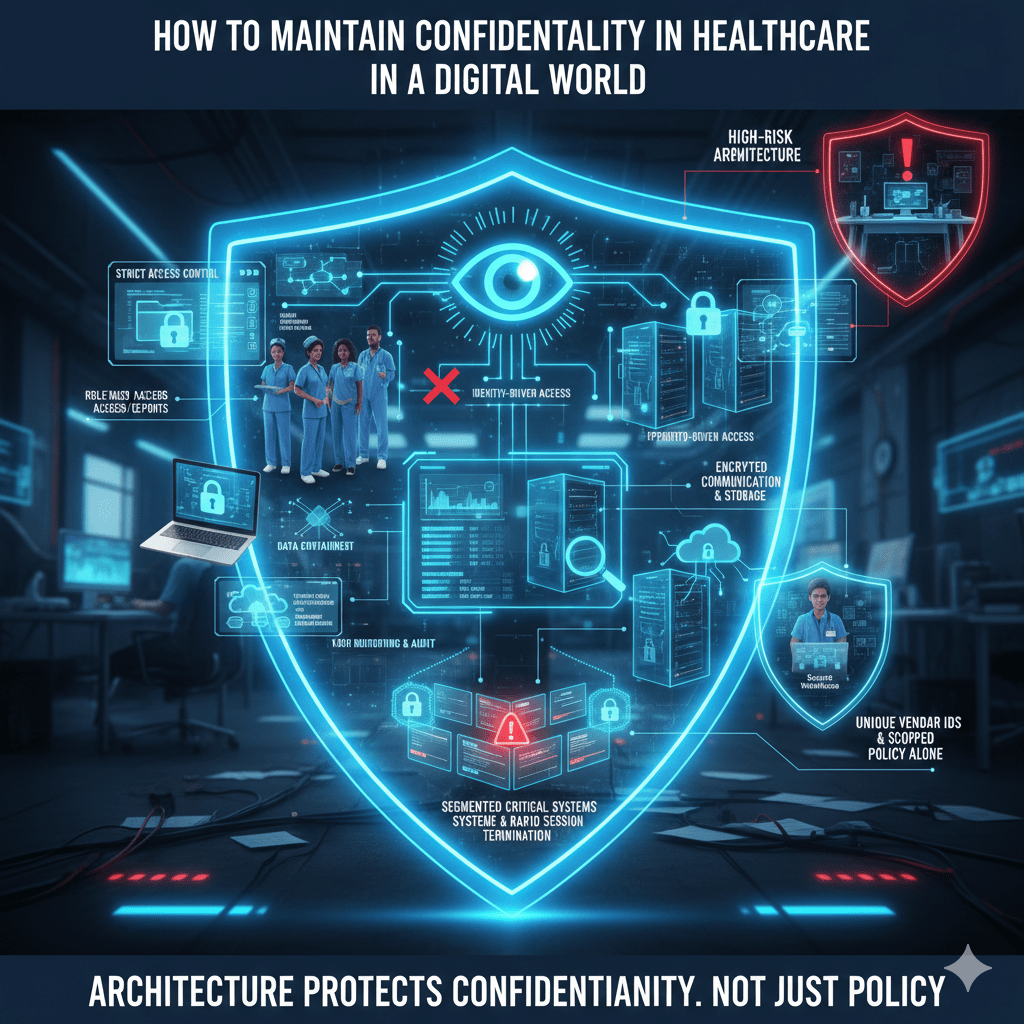
Confidentiality in healthcare used to mean locked filing cabinets and controlled chart access. Today, it means controlling identity, access scope, data movement, and architectural trust assumptions across digital systems.
The digital world did not eliminate confidentiality. It made it easier to violate at scale.
At Mindcore Technologies, healthcare security assessments consistently reveal that confidentiality failures are rarely about malicious insiders alone. They are about overexposed systems, excessive access permissions, unmanaged endpoints, and poorly designed remote access models.
Maintaining confidentiality today requires structural discipline, not just staff training.
1. Enforce Minimum Necessary Access Everywhere
Confidentiality collapses when access is broad.
Healthcare organizations must:
- Implement strict role-based access control (RBAC)
Clinicians, billing staff, administrators, and IT personnel must have clearly defined and limited access scopes. - Eliminate shared user accounts
Shared credentials destroy accountability and weaken audit integrity. - Conduct regular access reviews
Permissions often persist long after job roles change. - Automatically expire temporary or elevated privileges
Standing privileges increase long-term risk.
Confidentiality begins with disciplined identity control.
2. Replace Network Trust with Identity-Based Access
Traditional models assume that once a user connects, they are trusted.
To maintain confidentiality:
- Remove network-level access models such as broad VPN exposure
Users should access applications, not internal infrastructure. - Adopt identity-driven, session-based access
Access should be validated continuously, not granted permanently. - Limit internal system visibility
Compromised credentials should not reveal the environment. - Enforce multi-factor authentication universally
Especially for remote and administrative users.
Trust must be earned per session, not inherited through connectivity.
3. Contain PHI Within Controlled Environments
Confidentiality is most at risk when PHI spreads beyond secure systems.
Healthcare organizations should:
- Restrict downloads and exports of patient data
Preventing unnecessary copies on local devices. - Use secure workspace or isolated access models
Ensuring PHI remains inside governed environments. - Segment clinical, billing, and administrative systems
Preventing lateral access between departments. - Disable legacy file-sharing mechanisms that encourage sprawl
Older protocols often bypass modern controls.
Containment reduces breach scope automatically.
4. Protect Data in Transit and at Rest
Digital confidentiality requires strong encryption discipline.
Organizations must ensure:
- Encrypted communications for all patient data exchanges
Including telehealth, email gateways, and API integrations. - Encrypted storage across servers and backups
Backup repositories are frequent ransomware targets. - Secure configuration of cloud services
Misconfigured storage frequently exposes sensitive records.
Encryption is foundational but ineffective without access control.
5. Monitor and Audit Patient Data Access Continuously
Confidentiality must be observable.
Healthcare IT teams should:
- Log every access to patient records
Including identity, timestamp, and system interaction. - Centralize log storage securely
Disconnected logs undermine investigations. - Review abnormal access patterns
Such as large record exports or off-hours activity. - Test audit retrieval processes regularly
Ensuring compliance evidence is defensible.
If you cannot see access clearly, you cannot protect confidentiality.
6. Secure Remote and Hybrid Work Environments
The digital world extends beyond hospital walls.
To maintain confidentiality remotely:
- Avoid broad VPN-based network exposure
Replace with scoped, application-level access. - Enforce endpoint encryption and device management
Lost laptops remain a common exposure source. - Isolate remote sessions from internal networks
Preventing lateral movement. - Limit clipboard, download, and print functions where appropriate
Reducing data leakage risks.
Remote work should not weaken confidentiality controls.
7. Strengthen Vendor and Third-Party Controls
Vendors often require system access but introduce confidentiality risk.
Healthcare organizations must:
- Assign unique vendor identities
No shared or generic accounts. - Limit vendor access to specific systems only
No internal network browsing. - Enforce time-bound access automatically
Access should expire after engagement. - Audit vendor session activity regularly
Vendor interactions must be traceable.
Third-party convenience cannot override confidentiality.
8. Prepare for Breach Containment
Maintaining confidentiality requires planning for compromise.
Organizations should:
- Design systems that limit lateral movement
So exposure does not cascade. - Protect backups separately from primary systems
Preventing simultaneous encryption. - Enable rapid session termination capabilities
Compromised identities must be isolated instantly. - Test incident response procedures under realistic scenarios
Response speed affects regulatory impact.
Containment determines how much confidentiality is lost.
9. Align Confidentiality Controls with HIPAA Requirements
HIPAA’s Security Rule reinforces confidentiality through:
- Administrative safeguards
- Physical safeguards
- Technical safeguards
For IT teams, this translates to:
- Enforced access control
- Transmission security
- Audit logging
- Integrity monitoring
- Incident response readiness
Compliance and confidentiality are inseparable.
How Mindcore Technologies Strengthens Digital Confidentiality
Mindcore supports healthcare organizations by:
- Mapping where confidential patient data exists and moves
Identifying hidden exposure paths. - Redesigning access models to eliminate implicit trust
Replacing network-level access with identity-based controls. - Implementing secure workspace containment strategies
Keeping PHI inside controlled environments. - Centralizing audit visibility and reporting workflows
Making confidentiality defensible under review. - Building ransomware-resistant architectures
Protecting care delivery and patient trust simultaneously.
The objective is structural confidentiality, not reactive patching.
A Practical Confidentiality Risk Check
Your organization faces elevated confidentiality risk if:
- VPN access exposes internal systems
- PHI can be freely downloaded
- Access permissions rarely expire
- Vendor access is broad and persistent
- Audit logs are fragmented or incomplete
- Incident response requires shutting down entire departments
These are architectural exposure points.
Final Takeaway
Maintaining confidentiality in healthcare in a digital world requires disciplined identity enforcement, controlled access, data containment, continuous monitoring, and architectural design that assumes compromise is possible.
Organizations that redesign their access and network models around least privilege and structural containment significantly reduce breach scope, ransomware impact, and regulatory exposure. Those that rely solely on encryption and policy remain vulnerable to the credential-based attacks that define modern healthcare risk.