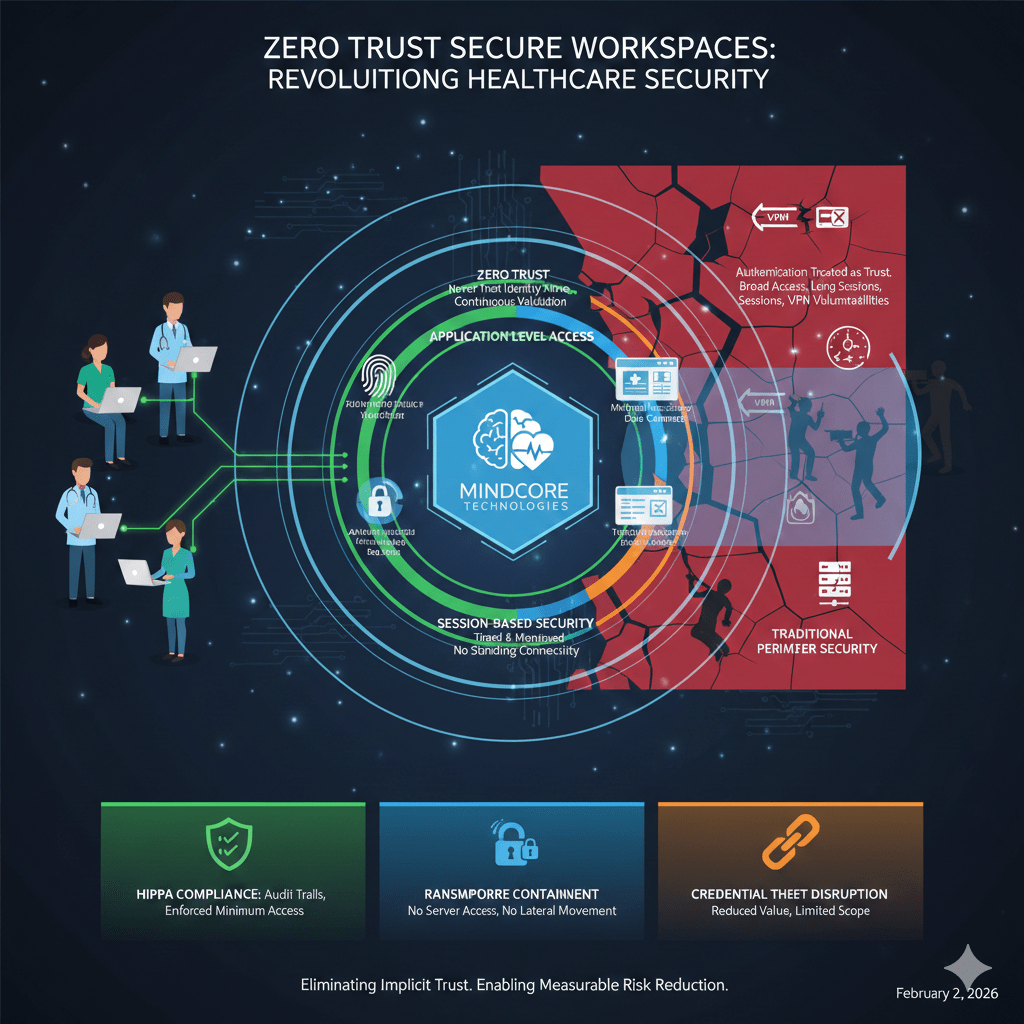
Healthcare security fails most often after authentication, not before it. Credentials are stolen, sessions are hijacked, and once access is granted, attackers move freely through environments that assume trust instead of enforcing it continuously.
That is why zero trust secure workspaces are replacing perimeter-based security models in healthcare.
At Mindcore Technologies, healthcare breach reviews consistently show the same root cause: identity compromise instantly becomes broad system access. Zero trust secure workspaces exist to break that chain by redesigning how access, data, and sessions are controlled.
Why Traditional Healthcare Security Models Fall Short
Healthcare security has historically focused on protecting networks.
That approach breaks down because:
- Authentication is treated as a trust event
Once users log in, systems assume continued legitimacy, even if conditions change. - VPNs extend trust to unmanaged endpoints
Clinicians, administrators, and vendors effectively join the internal network from uncontrolled environments. - Sessions persist indefinitely
Long-lived access increases the value of stolen credentials and sessions. - Access is broader than necessary
Users often inherit visibility into systems and data they do not need.
Security tools then attempt to monitor misuse rather than prevent exposure.
What Zero Trust Actually Means in Healthcare
Zero trust is not a product. It is an operating principle.
In healthcare, zero trust means:
- Never trust identity alone
Every access request is verified, not assumed. - Never trust network location
Internal and external connections are treated the same. - Continuously validate sessions
Access is reassessed throughout the session lifecycle. - Limit access to the minimum necessary
Users see only what they are explicitly authorized to use.
Secure workspaces are how zero trust becomes enforceable in daily healthcare operations.
What a Zero Trust Secure Workspace Changes
A zero trust secure workspace removes network trust from the access equation entirely.
Instead of extending the network outward, it:
- Contains applications and data inside a protected workspace
Systems are not directly reachable from user devices. - Delivers access at the application level
Users interact only with approved applications, not networks or servers. - Enforces identity-driven, session-based access
Each session is scoped, monitored, and continuously evaluated. - Eliminates standing network connectivity
Network paths exist only during active, approved sessions.
This architecture prevents small failures from becoming large incidents.
How Zero Trust Secure Workspaces Reduce Healthcare Attack Surface
Attack surface shrinks when systems are no longer visible.
Secure workspaces reduce exposure by:
- Making infrastructure invisible until identity is verified
Unauthorized users cannot scan or enumerate systems. - Eliminating exposed entry points
VPN gateways and listening services are removed rather than hardened. - Removing lateral movement paths
Compromised access does not reveal additional targets. - Limiting reachability by design
Access is tightly scoped to specific applications.
If attackers cannot see systems, they cannot attack them.
Stopping Credential-Based Attacks and Session Abuse
Most healthcare breaches involve legitimate access that is misused.
Zero trust secure workspaces disrupt these attacks by:
- Reducing the value of stolen credentials
Credentials alone do not provide network access. - Limiting session duration and scope
Sessions expire automatically and cannot be reused broadly. - Monitoring behavior continuously
Abnormal access patterns can trigger immediate revocation. - Preventing pivoting after compromise
Attackers cannot move laterally once inside.
This directly addresses the most common healthcare breach vectors.
Containing Ransomware by Design
Ransomware relies on visibility, access, and movement.
Secure workspaces break this model:
- No access to underlying servers or file systems
Ransomware cannot encrypt infrastructure it cannot reach. - No lateral movement paths
Spread across the environment is blocked by architecture. - PHI remains inside the workspace
Data is not exposed to endpoints where it can be encrypted or exfiltrated. - Immediate session termination
Access can be revoked instantly without password resets or network changes.
Containment replaces cleanup as the primary defense.
Why Zero Trust Secure Workspaces Improve HIPAA Compliance
HIPAA requires organizations to prove control, not intent.
Secure workspaces support this by:
- Enforcing minimum necessary access automatically
Permissions are tied directly to role and purpose. - Providing application-level audit trails
Logs show exactly which systems containing PHI were accessed. - Reducing unnecessary PHI exposure
Data remains contained within controlled environments. - Simplifying evidence collection
Audit data is centralized and consistent.
Compliance becomes an architectural outcome, not a manual process.
Zero Trust Secure Workspaces vs Traditional Zero Trust Implementations
Many zero trust initiatives fail because they are layered onto existing networks.
Secure workspaces succeed because they:
- Remove network trust entirely
- Eliminate VPN dependency
- Contain access instead of monitoring misuse
- Reduce complexity rather than adding controls
Zero trust works best when it is built into how access is delivered, not bolted on.
How Mindcore Technologies Deploys Zero Trust Secure Workspaces in Healthcare
Mindcore implements zero trust secure workspaces by:
- Mapping clinical and administrative workflows
Security aligns with real healthcare operations. - Defining role-based access to PHI
Access reflects responsibility, not convenience. - Replacing VPN-based access models
Network exposure is removed from the access path. - Enforcing device and session posture checks
Access adapts dynamically to risk. - Providing centralized visibility and governance
Security and compliance teams share a single source of truth.
The objective is measurable risk reduction without disrupting care delivery.
A Simple Healthcare Security Check
Your environment is not operating on zero trust if:
- VPNs are still required for core access
- Sessions persist indefinitely
- Users can see systems beyond their role
- Infrastructure is discoverable after login
- Breach response depends on manual intervention
These are architectural weaknesses, not awareness issues.
Final Takeaway
Zero trust secure workspaces improve healthcare security by removing implicit trust, eliminating unnecessary exposure, and containing access by design. Instead of assuming users remain trustworthy after login, every session is verified, limited, and observable.
For healthcare organizations facing ransomware, credential theft, and regulatory pressure, zero trust secure workspaces are no longer aspirational. They are the most practical path to sustainable security.