Healthcare cyber defense no longer fails because teams miss alerts. It fails because access is too broad, trust is implicit, and compromise spreads faster than response. Secure workspaces exist to correct that imbalance. They are not an endpoint tool or a remote access feature. They are a defensive control that reshapes how healthcare environments absorb attacks.
At Mindcore Technologies, breach investigations consistently show that organizations using secure workspace architecture experience contained incidents instead of enterprise-wide failures. The difference is not detection quality. It is architectural discipline.
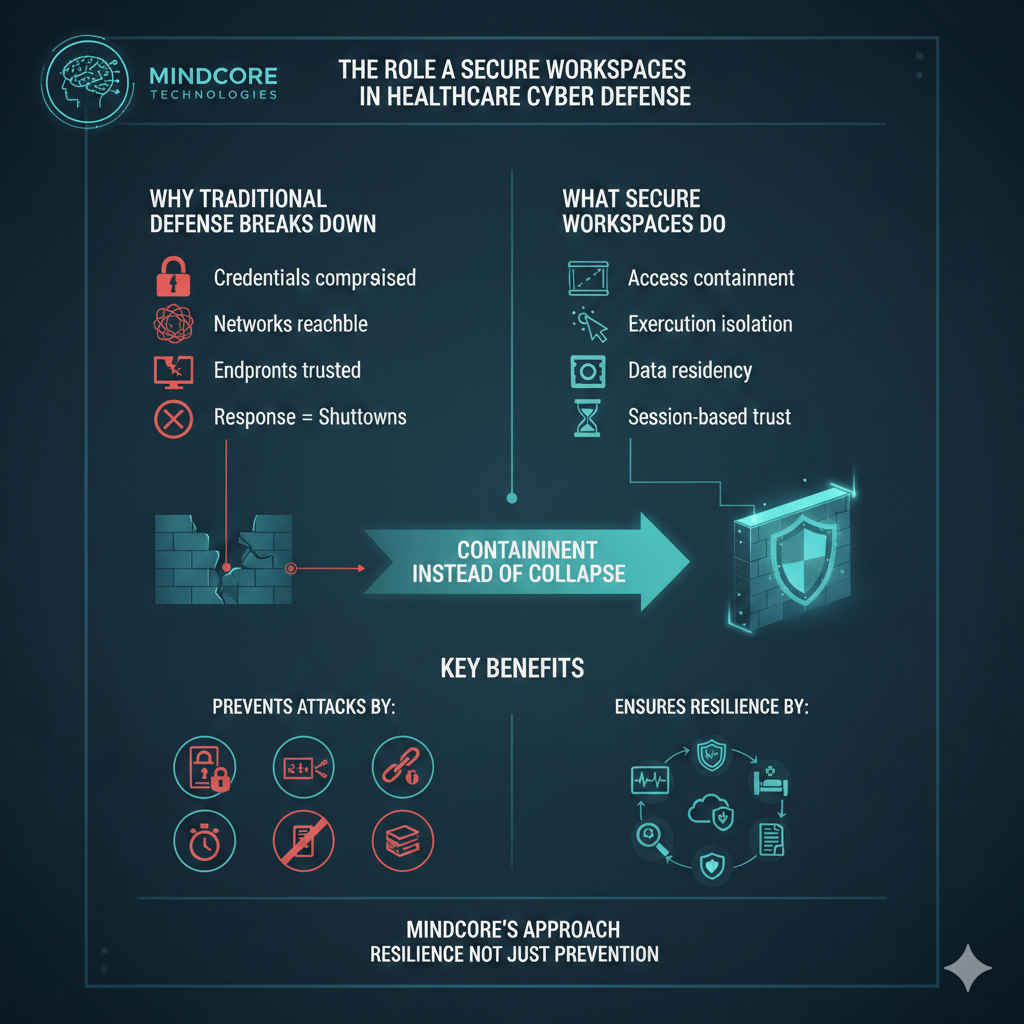
Why Traditional Healthcare Cyber Defense Breaks Down
Most healthcare security programs were built around prevention and detection. That approach breaks under modern conditions.
It fails because:
- Credentials are routinely compromised
Phishing, infostealers, and MFA fatigue attacks bypass perimeter defenses. - Networks are reachable once access is granted
Internal visibility enables rapid lateral movement. - Endpoints are treated as trusted execution zones
Compromised devices undermine all downstream controls. - Response depends on shutdowns
Security actions disrupt care delivery.
Traditional defenses assume compromise is rare. Secure workspaces assume compromise is inevitable.
What Secure Workspaces Actually Do in Cyber Defense
Secure workspaces change cyber defense by containing access, execution, and data interaction inside controlled environments.
They enforce four defensive outcomes:
- Access containment
Users interact with systems without joining networks. - Execution isolation
Work happens inside controlled environments, not endpoints. - Data residency control
PHI remains inside governed systems. - Session-based trust
Access expires automatically.
This transforms breaches from crises into manageable events.
Containing Credential-Based Attacks
Credential theft is the dominant healthcare attack vector.
Secure workspaces limit credential abuse by:
- Scoping access to specific applications
Compromised credentials do not unlock infrastructure. - Eliminating network discovery
Attackers cannot scan or enumerate systems. - Restricting session duration
Access ends without manual intervention. - Blocking privilege escalation paths
One identity cannot pivot to others.
Stolen credentials lose their value quickly.
Stopping Lateral Movement by Design
Lateral movement is what turns access into catastrophe.
Secure workspaces stop it by:
- Removing shared network spaces
Users never coexist on the same internal network. - Isolating sessions from each other
One compromise cannot spread. - Eliminating trust inheritance
Access to one system does not imply access to others. - Blocking east-west traffic entirely
Movement paths simply do not exist.
Attackers cannot move where no path is available.
Reducing Ransomware Impact Without Downtime
Ransomware depends on reach and speed.
Secure workspaces disrupt both by:
- Preventing access to file systems and backups
Attackers cannot locate encryption targets. - Limiting encryption scope
Only the compromised session is affected. - Allowing instant session termination
Access can be revoked without system shutdowns. - Preserving clinical access
Care delivery continues during containment.
Ransomware becomes survivable instead of devastating.
Protecting PHI Under Real Attack Conditions
PHI exposure often occurs after initial compromise.
Secure workspaces protect PHI by:
- Keeping data inside controlled environments
No endpoint storage or syncing. - Restricting copy, download, and export actions
Data movement is intentional and logged. - Reducing reliance on endpoint hygiene
Protection does not depend on perfect devices. - Maintaining session-level accountability
Every interaction is attributable.
PHI remains protected even when users or devices fail.
Securing Medical and Legacy Systems
Healthcare environments depend on systems that cannot be hardened traditionally.
Secure workspaces protect these systems by:
- Hiding them from network scans
Systems are invisible unless explicitly accessed. - Preventing direct device-to-device communication
Compromise does not propagate. - Avoiding agents or software changes
Certification and stability remain intact. - Isolating access paths
Systems are never exposed broadly.
Legacy systems become far less dangerous when isolated.
Eliminating VPN Risk from Cyber Defense
VPNs expand the attack surface.
Secure workspaces remove VPN risk by:
- Eliminating network-level access entirely
Users never join internal networks. - Reducing credential blast radius
Compromise affects one workspace, not everything. - Removing exposed VPN infrastructure
No appliances to exploit or patch urgently. - Simplifying access workflows
Fewer failures and support tickets.
Defense becomes simpler and stronger simultaneously.
Improving Incident Response Speed and Precision
Secure workspaces improve response by design.
They enable:
- Immediate session termination
Access is revoked instantly. - Granular containment
Only affected users or sessions are isolated. - Clear forensic visibility
Activity is scoped and traceable. - No forced operational shutdowns
Clinical systems remain available.
Response becomes surgical instead of disruptive.
Supporting HIPAA Compliance as a Defensive Outcome
HIPAA compliance improves when access is controlled structurally.
Secure workspaces support this by:
- Enforcing minimum necessary access automatically
Permissions are narrow and role-aligned. - Reducing breach scope
Fewer systems and records are involved. - Producing audit-ready access records
Evidence exists without reconstruction. - Aligning security controls with care workflows
Compliance does not slow operations.
Compliance becomes a side effect of good architecture.
How Mindcore Technologies Uses Secure Workspaces in Healthcare Cyber Defense
Mindcore integrates secure workspaces into healthcare cyber defense by:
- Identifying where access trust creates exposure
Mapping implicit trust paths. - Replacing network-based access with workspace-based models
Removing lateral movement potential. - Containing PHI within controlled environments
Preventing data sprawl. - Designing response workflows that preserve care delivery
Security without disruption. - Aligning architecture with HIPAA and operational realities
Defense that auditors and clinicians both accept.
The objective is resilience, not just prevention.
A Simple Cyber Defense Reality Check
Your healthcare cyber defense is still fragile if:
- VPNs expose internal networks
- Credentials unlock multiple systems
- Lateral movement is possible
- PHI exists on endpoints
- Response requires shutdowns
These are architectural weaknesses.
Final Takeaway
Secure workspaces are not an add-on to healthcare cyber defense. They are the mechanism that allows healthcare organizations to absorb attacks without collapsing operations or compliance posture.
Organizations that deploy secure workspace architecture contain breaches early, protect PHI under pressure, and maintain care delivery during incidents. Those that do not remain dependent on trust models attackers already know how to exploit.