A data breach does not end when access is blocked. That moment only stops the bleeding. What happens next determines whether the incident becomes a short disruption or a long-term business failure.
At Mindcore Technologies, we see the same pattern repeatedly. Organizations that follow a structured post-breach process recover faster, face less regulatory exposure, and dramatically reduce the chance of a second incident. Those that rush or improvise usually repeat the breach.
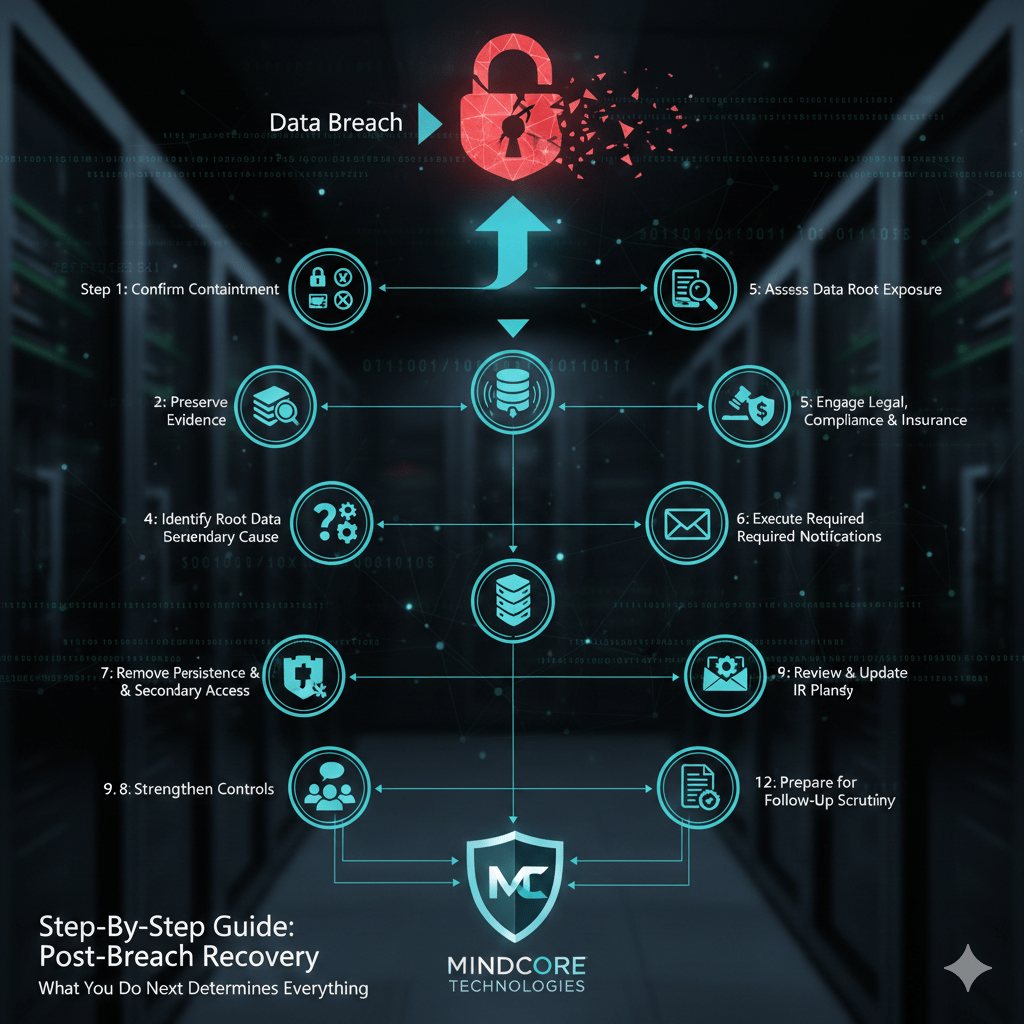
This is the step-by-step process that actually works after containment.
Step 1: Confirm Containment Is Real
Before doing anything else, verify the attacker no longer has access.
Validate immediately:
- All compromised accounts are disabled or reset
- All active sessions, tokens, and API keys are revoked
- No new suspicious logins appear
- Affected devices are isolated if needed
If access still exists, everything else is premature.
Step 2: Preserve Evidence and Logs
Evidence determines legal exposure, insurance coverage, and remediation accuracy.
Preserve without altering:
- Authentication and access logs
- Cloud and SaaS audit logs
- Firewall, VPN, and gateway logs
- Endpoint activity records
Do not wipe, reimage, or restore yet. Destruction of evidence creates risk.
Step 3: Identify the Root Cause
This is not about blame. It is about control failure.
Answer with evidence:
- How did initial access occur?
- Why was that access possible?
- Which control failed or was missing?
- How long did access exist before detection?
If you cannot explain the “why,” remediation will be superficial.
Step 4: Assess Data Exposure Accurately
Do not guess. Do not minimize.
Determine:
- What data could have been accessed
- Whether data was viewed, modified, or exported
- Which systems and users were involved
- Whether regulated data is in scope (PII, PHI, PCI)
If you cannot prove data was not accessed, assume potential exposure.
Step 5: Engage Legal, Compliance, and Insurance
A data breach is a business and legal event.
Coordinate early with:
- Legal counsel for disclosure guidance
- Compliance teams for regulatory interpretation
- Cyber insurance providers per policy requirements
Notification timing and wording matter. Incorrect handling increases liability.
Step 6: Execute Required Notifications
Once facts are validated and legal guidance is clear:
You may need to notify:
- Regulators
- Affected individuals
- Customers or partners
- Payment processors or platforms
All notifications should be accurate, consistent, and documented.
Step 7: Remove Persistence and Secondary Access
Attackers rarely leave cleanly.
Check for:
- New admin or service accounts
- Inbox rules and email forwarding
- OAuth apps or API integrations
- Scheduled tasks or startup scripts
- Configuration changes
Failure to remove persistence leads to re-compromise.
Step 8: Restore Systems Safely
Restoration must follow remediation, not precede it.
Before restoring:
- Patch exploited vulnerabilities
- Reduce excessive permissions
- Update security configurations
- Validate backup integrity
During restoration:
- Monitor closely
- Restore in phases
- Watch for repeated indicators
Speed without security creates repeat incidents.
Step 9: Strengthen the Controls That Failed
Most breaches succeed because trust is too broad.
Typical post-breach improvements include:
- Enforcing phishing-resistant MFA
- Reducing session lifetimes
- Implementing least-privilege access
- Segmenting networks and data
- Tightening cloud sharing rules
- Improving logging and alerting
Fix the architecture, not just the symptom.
Step 10: Review and Update Incident Response Plans
Treat the breach as a real-world test.
Review honestly:
- Detection speed
- Escalation clarity
- Role ownership
- Communication effectiveness
Update playbooks, contacts, and procedures based on what actually happened.
Step 11: Communicate Internally With Clarity
Employees need guidance, not speculation.
Internal communication should:
- Explain what happened at a high level
- Clarify changes and expectations
- Reinforce security behaviors
- Avoid blame or technical overload
Confusion increases future risk.
Step 12: Prepare for Follow-Up Scrutiny
Expect:
- Regulatory follow-ups
- Insurance audits
- Customer due diligence
- Executive and board review
Documentation and timelines will be examined closely.
Common Post-Breach Mistakes to Avoid
- Declaring the breach “over” too early
- Restoring systems before fixing root cause
- Ignoring cloud and identity logs
- Treating the breach as an IT-only issue
- Failing to redesign access controls
Breaches repeat when lessons are skipped.
How Mindcore Technologies Supports Post-Breach Recovery
Mindcore helps organizations move from incident to resilience through:
- Post-breach validation and investigation
- Identity and access redesign
- Endpoint and network hardening
- Cloud and data access governance
- Long-term detection and monitoring improvements
Our focus is preventing recurrence, not just restoring operations.
Final Takeaway
What you do after a data breach matters more than how it started. A disciplined, step-by-step response reduces damage, protects legal position, and prevents repeat incidents. Organizations that rush back to normal often invite the same breach again.