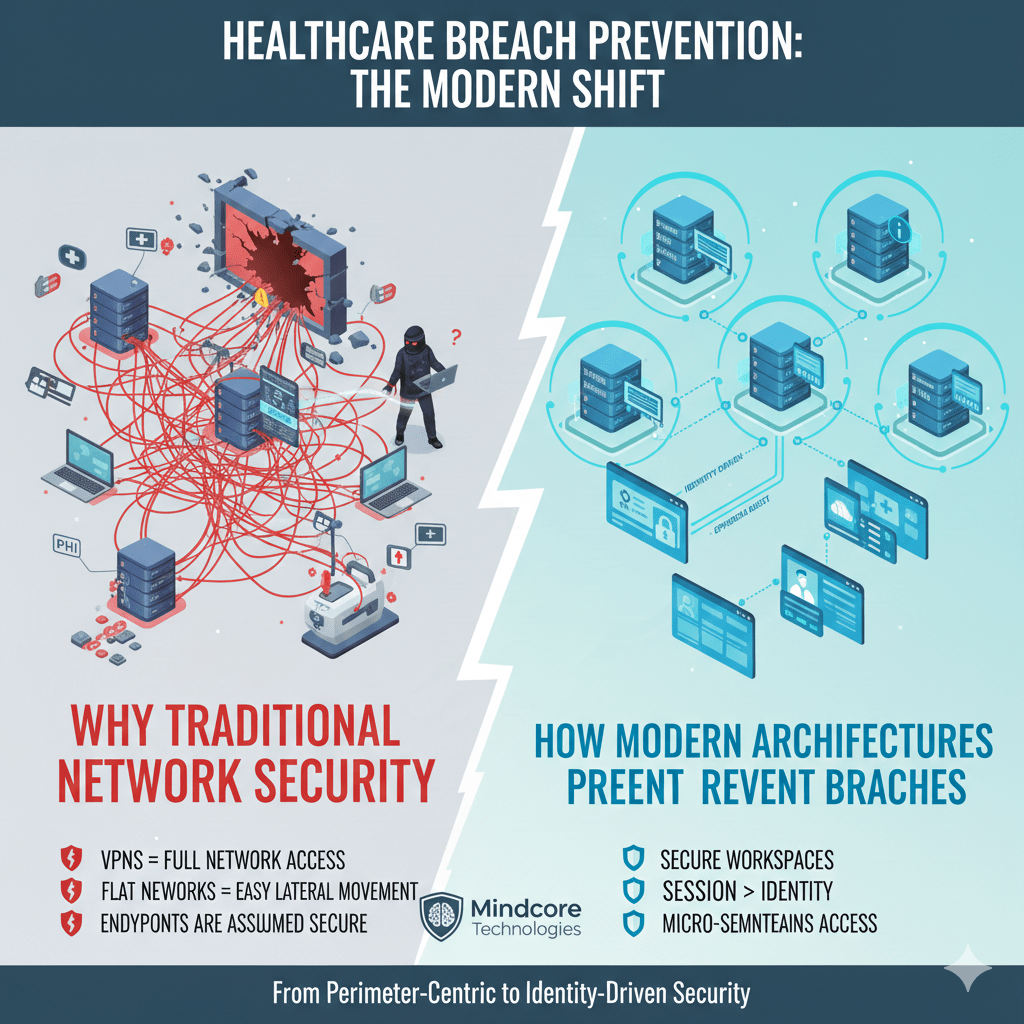
Traditional network security assumes a simple idea that no longer holds true: if you protect the perimeter, everything inside can be trusted. In healthcare, that assumption is now one of the biggest sources of risk.
Breaches are not happening because firewalls fail. They are happening because networks still grant trust too broadly, for too long, and with too little visibility.
At Mindcore Technologies, healthcare incident analysis shows a clear trend: organizations relying primarily on network-based security experience wider breach impact, slower containment, and higher HIPAA exposure than those that redesign access around identity and containment.
What Traditional Network Security Was Designed to Do
Traditional network security focuses on:
- Perimeter defense
Firewalls, intrusion prevention, and filtering stop external threats. - Internal trust zones
Once inside, users and systems are assumed to be legitimate. - Static segmentation
Network boundaries separate broad groups of systems. - Persistent connectivity
Access remains active until manually revoked.
This model worked when users, devices, and systems were centralized and predictable. Healthcare no longer operates that way.
Why the Model Breaks Down in Modern Healthcare
Healthcare environments now include remote clinicians, telehealth platforms, cloud systems, vendors, and unmanaged devices. Traditional networks cannot handle this complexity safely.
They fail because:
- VPNs extend full network trust remotely
One stolen credential exposes internal systems. - Flat or loosely segmented networks enable lateral movement
Attackers pivot quickly once inside. - Identity is secondary to location
Being “on the network” matters more than who the user is. - Endpoints are assumed to be secure
Compromised devices undermine all controls.
The result is rapid breach escalation instead of containment.
How Attackers Exploit Network-Based Trust
Attackers no longer need to break in aggressively. They log in.
Once access exists, they:
- Scan internal networks for targets
File servers, EHR systems, and backups are quickly discovered. - Move laterally using legitimate protocols
Activity blends into normal traffic. - Escalate privileges quietly
Admin tools and shared credentials accelerate spread. - Deploy ransomware or exfiltrate PHI at scale
Network reach determines damage.
The network becomes the attack surface.
Why Detection Alone Is Not Enough
Many healthcare organizations respond by adding more monitoring.
That approach fails because:
- Alerts trigger after access already exists
- Attackers blend into normal user behavior
- Response speed determines damage, not prevention
Detection helps with investigation. It does not stop attackers from reaching systems.
Healthcare organizations are realizing they need prevention through design, not faster reaction.
What Replaces Traditional Network Security
Healthcare organizations are moving toward access architectures that remove implicit trust entirely.
Key shifts include:
- Identity-driven access control
Access decisions are based on who the user is and what they need, not where they connect from. - Secure workspace models
Users access applications inside controlled environments instead of joining networks. - Stealth networking principles
Systems are invisible and unreachable unless explicitly authorized. - Session-based access instead of standing trust
Access expires automatically.
The network becomes less relevant as a trust boundary.
How Secure Workspaces Change the Security Model
Secure workspaces break the link between users and infrastructure.
They work by:
- Isolating applications and data from endpoints
PHI stays inside protected environments. - Eliminating internal network visibility
Users cannot scan or explore systems. - Preventing lateral movement by default
Access is scoped to exact workflows. - Allowing instant session termination
Compromised access is revoked immediately.
Breaches shrink from enterprise-wide events to isolated sessions.
Reducing Ransomware Impact Through Architectural Change
Ransomware thrives in network-centric environments.
Modern architectures reduce impact by:
- Blocking discovery of encryption targets
Attackers cannot find file systems or backups. - Limiting access scope for compromised accounts
One credential cannot reach everything. - Protecting critical systems from endpoint compromise
Devices no longer equal access. - Enabling rapid isolation without shutdowns
Operations continue while incidents are contained.
This turns ransomware into a manageable incident instead of a crisis.
Why This Shift Improves HIPAA Outcomes
HIPAA expects healthcare organizations to minimize exposure and enforce access intentionally.
Moving beyond network security supports this by:
- Enforcing minimum necessary access automatically
Users see only what they need. - Containing PHI inside controlled environments
Data sprawl is reduced. - Providing clear audit evidence
Access is identity-verified and session-based. - Reducing breach scope and notification complexity
Fewer systems and records are affected.
Compliance improves when architecture limits reach.
Operational Benefits Beyond Security
Healthcare organizations are not making this shift for security alone.
They also gain:
- Simpler remote access
No VPN troubleshooting or network complexity. - Faster onboarding and offboarding
Access is provisioned and revoked centrally. - Consistent access across locations
Users work the same way everywhere. - Lower operational friction
Security stops blocking care delivery.
Security and productivity stop competing.
How Mindcore Technologies Helps Healthcare Move Beyond Network Security
Mindcore helps healthcare organizations modernize security by:
- Identifying where network trust still exists
Mapping hidden exposure. - Replacing VPN and perimeter-based access models
Removing implicit trust. - Implementing secure workspace and stealth access architectures
Containing users and systems. - Aligning access controls with real healthcare workflows
Protecting care delivery. - Centralizing visibility and audit readiness
Supporting security and compliance teams.
The goal is safer access without operational disruption.
A Simple Network Security Reality Check
Your healthcare environment is still network-dependent if:
- VPN access exposes internal systems
- Users can scan or browse networks
- Compromised credentials enable lateral movement
- Access permissions rarely expire
- Breach response requires shutdowns
These are signs the model no longer fits reality.
Final Takeaway
Healthcare organizations are moving beyond traditional network security because it was never designed to handle modern access patterns, ransomware tactics, or compliance expectations.
The future belongs to architectures that remove implicit trust, hide systems by default, and grant access only when identity, purpose, and context are verified. Organizations that make this shift contain breaches faster, protect patient data more effectively, and maintain operations under pressure. Those that do not remain exposed through assumptions attackers already exploit.