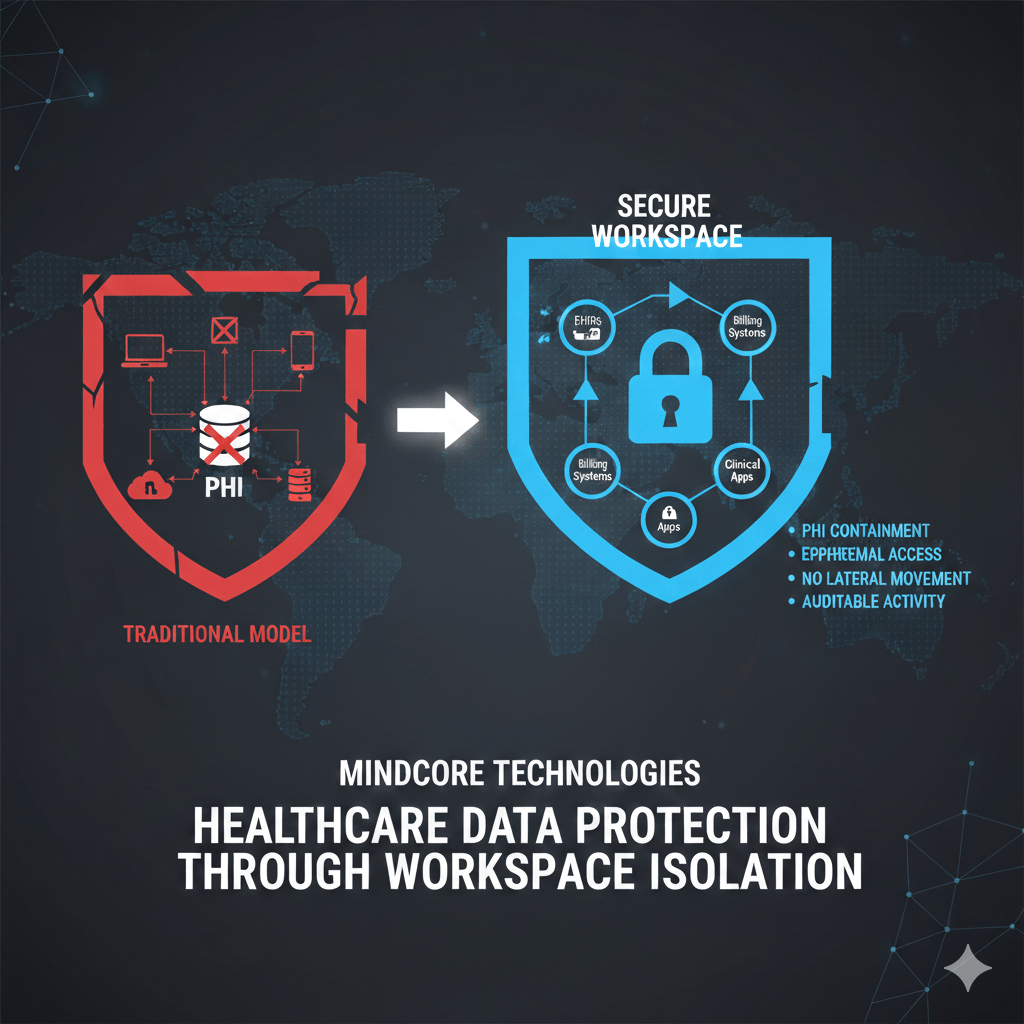
Healthcare data is rarely lost because encryption fails or firewalls break. It is lost because PHI is reachable from too many places, by too many users, for too long. Once access is granted, traditional environments offer attackers and insiders far more opportunity than healthcare regulations ever intended.
Workspace isolation exists to fix that structural failure.
At Mindcore Technologies, healthcare breach investigations consistently show that data exposure happens after successful authentication, not before it. Workspace isolation protects healthcare data by redesigning how access, sessions, and data boundaries work together.
What Workspace Isolation Actually Means
Workspace isolation is not virtualization for convenience. It is a security architecture that deliberately separates users from direct access to healthcare systems and data.
In practice, workspace isolation means:
- Applications and data run inside a controlled environment
EHRs, billing platforms, and clinical systems are accessed through a secure workspace rather than directly from endpoints. - Endpoints never directly touch PHI systems
User devices act as access terminals, not data endpoints. - Network paths are not exposed
Systems are not routable or discoverable from user networks. - Access exists only for approved sessions
Connectivity is ephemeral and tightly scoped.
This removes the assumption that endpoints can be trusted.
Why Traditional Healthcare Data Protection Falls Short
Most healthcare environments still protect data by securing the network around it.
That approach fails because:
- PHI becomes reachable from endpoints
Once connected via VPN or internal access, data can be copied, cached, or exfiltrated. - Access is broader than necessary
Users often see systems and data unrelated to their role. - Sessions persist too long
Standing access increases the value of stolen credentials and sessions. - Monitoring focuses on malware, not misuse
Legitimate access abuse blends into normal activity.
Workspace isolation removes these failure points by design.
How Workspace Isolation Shrinks Healthcare Data Exposure
Workspace isolation protects healthcare data by limiting where data can exist and how it can be reached.
It achieves this by:
- Containing PHI inside the workspace
Data is not downloaded, synced, or stored on local devices. - Restricting access to specific applications
Users cannot browse networks or file systems. - Eliminating lateral movement paths
Compromised access cannot pivot across systems. - Reducing attack surface visibility
Systems are invisible until identity and authorization are verified.
Exposure becomes minimal and intentional.
Protecting Against Credential Theft and Session Abuse
Most healthcare breaches involve valid credentials.
Workspace isolation reduces their value by:
- Preventing network-level access
Credentials do not grant visibility into infrastructure. - Limiting session scope and duration
Sessions are short-lived and purpose-specific. - Monitoring session behavior continuously
Abnormal activity can trigger immediate revocation. - Containing access to one workspace at a time
Compromise does not cascade across the environment.
This breaks the most common healthcare breach patterns.
Ransomware Containment Through Isolation
Ransomware depends on access to file systems, servers, and network visibility.
Workspace isolation stops this by:
- Blocking access to underlying infrastructure
Ransomware cannot encrypt what it cannot reach. - Removing lateral movement entirely
There are no flat networks to traverse. - Keeping PHI off endpoints
Even compromised devices cannot encrypt protected data. - Allowing instant session termination
Access can be revoked without network reconfiguration.
Containment replaces recovery as the primary defense.
Workspace Isolation and HIPAA Alignment
HIPAA expects healthcare organizations to minimize exposure and prove control.
Workspace isolation supports this by:
- Enforcing minimum necessary access automatically
Users see only what their role requires. - Preventing uncontrolled data duplication
PHI remains in approved environments. - Providing clear, application-level audit trails
Logs show exactly which systems were accessed and when. - Reducing reliance on endpoint security assumptions
Compliance does not depend on perfect devices.
HIPAA safeguards become architectural outcomes.
Why Workspace Isolation Works Better Than Hardening Alone
Traditional strategies focus on:
- Hardening endpoints
- Adding monitoring tools
- Improving detection
Workspace isolation focuses on:
- Removing trust from endpoints
- Containing access by default
- Eliminating unnecessary exposure
It is easier to protect data when it never leaves controlled boundaries.
How ShieldHQ Implements Workspace Isolation for Healthcare
ShieldHQ Powered by Dispersive® Stealth Networking operationalizes workspace isolation by:
- Delivering application access through secure workspaces
Users never connect directly to healthcare systems. - Keeping PHI inside controlled environments
Data does not reach unmanaged devices. - Eliminating VPNs and network trust
Infrastructure remains hidden and unreachable. - Enforcing identity-driven, session-based access
Every session is verified and scoped. - Providing centralized visibility and governance
Security and compliance teams gain consistent oversight.
This makes workspace isolation practical for daily healthcare operations.
How Mindcore Technologies Deploys Workspace Isolation
Mindcore deploys workspace isolation for healthcare organizations by:
- Mapping clinical and administrative workflows
Access models reflect real operational needs. - Defining role-based access to PHI systems
Permissions align with responsibility. - Replacing VPN-based access paths
Network exposure is removed from data access entirely. - Enforcing device and session posture controls
Access adapts dynamically to risk. - Providing centralized monitoring and audit readiness
Security and compliance teams share a single source of truth.
The objective is measurable data protection without disrupting care.
A Simple Data Exposure Reality Check
Your healthcare data remains overexposed if:
- PHI can be accessed directly from endpoints
- VPNs are required for EHR access
- Users can browse systems beyond their role
- Sessions persist indefinitely
- Breach response depends on cleanup
These are architectural risks, not awareness gaps.
Final Takeaway
Healthcare data protection is no longer about defending every endpoint and network segment. It is about containing PHI inside environments designed to be accessed safely, temporarily, and intentionally.
Workspace isolation delivers this by removing unnecessary trust, eliminating lateral movement, and keeping sensitive data where it belongs. For healthcare organizations facing ransomware, credential theft, and regulatory pressure, workspace isolation is not an enhancement. It is the most effective way to protect patient data moving forward.