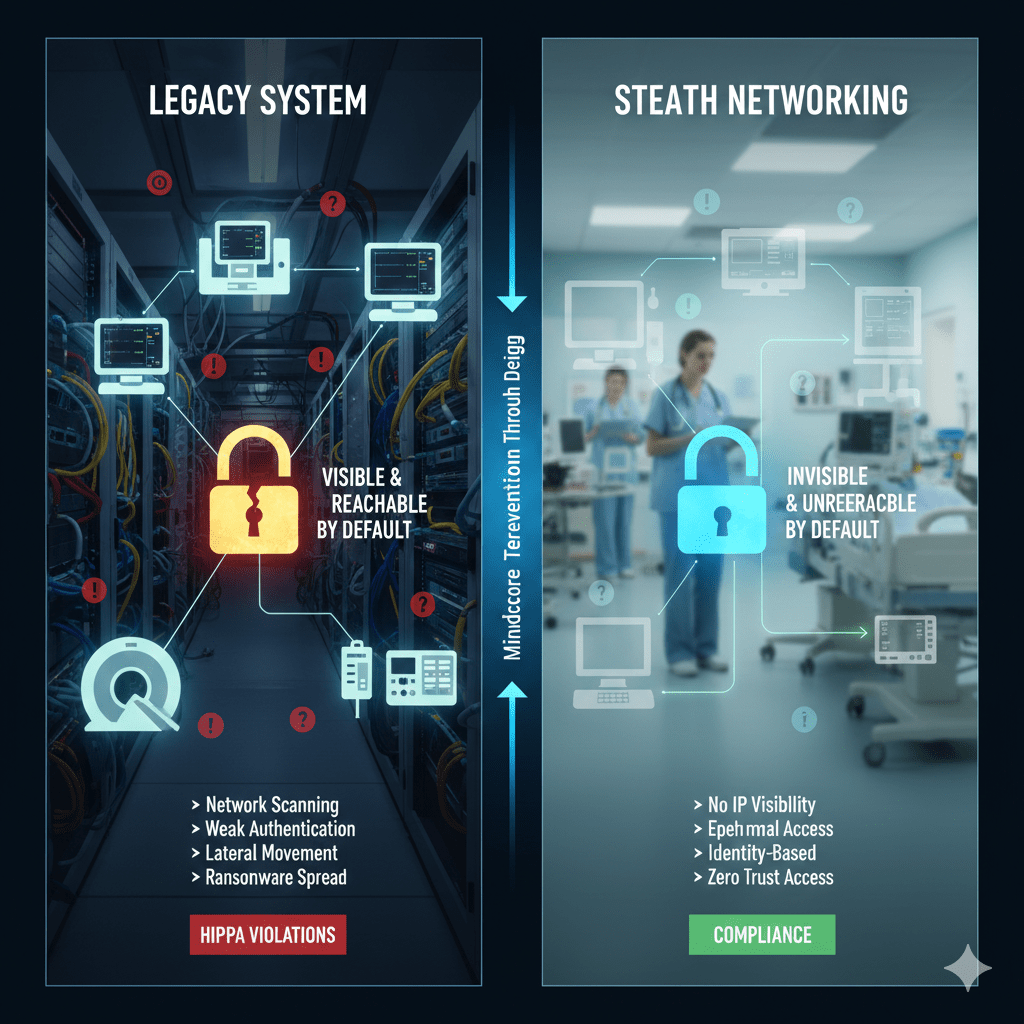
Medical devices are rarely compromised because attackers defeat their security controls. They are compromised because the devices are visible, reachable, and trusted by default inside healthcare networks.
Once a device can be discovered, scanned, or accessed, it becomes a pivot point. Stealth networking exists to remove that visibility entirely.
At Mindcore Technologies, healthcare security reviews repeatedly show that medical devices are not the initial target, they are the amplifier. Attackers use them to move laterally, disrupt care, and expand ransomware impact.
Why Medical Devices Are High-Risk by Design
Most medical devices were built for clinical reliability, not modern cyber threats.
They are high-risk because:
- They run outdated or unpatchable operating systems
Many devices cannot be patched without vendor involvement or regulatory approval. - They require persistent network connectivity
Imaging systems, monitors, and infusion pumps must stay online to function. - They trust the internal network implicitly
Devices often assume anything on the local network is safe. - They are difficult to monitor deeply
Endpoint agents and EDR tools are rarely supported.
These constraints make traditional security controls ineffective.
How Attackers Exploit Medical Devices
Medical devices are rarely exploited directly. They are used.
Attackers commonly:
- Discover devices through network scanning
Flat networks expose device IPs and services immediately. - Leverage weak authentication or default services
Many devices expose management interfaces internally. - Use devices as lateral movement bridges
Devices often sit between clinical and administrative networks. - Disrupt availability to create pressure
Downtime directly impacts patient care and operations.
Visibility equals vulnerability.
Why Segmentation Alone Is Not Enough
Network segmentation helps, but it does not solve the core problem.
Segmentation fails when:
- Devices are still discoverable within segments
- VPN users inherit visibility into device networks
- Management access remains broadly reachable
- Exceptions accumulate over time
Segmentation limits traffic paths. Stealth networking removes reachability entirely.
What Stealth Networking Actually Does
Stealth networking secures medical devices by making them invisible unless identity and authorization are verified.
It works by:
- Removing IP-level visibility
Devices do not respond to scans or probes. - Eliminating always-on network trust
Connectivity exists only when explicitly approved. - Creating ephemeral access paths
Access disappears when sessions end. - Separating access from physical location
Trust is not based on being “inside” the network.
If attackers cannot see devices, they cannot target them.
Protecting Medical Devices from Lateral Movement
Lateral movement is the biggest risk to medical devices.
Stealth networking prevents it by:
- Blocking network discovery entirely
Devices cannot be enumerated or mapped. - Restricting access to approved applications or workflows
Users never touch device networks directly. - Isolating devices from each other
One compromised system cannot reach others. - Preventing pivoting into clinical systems
Devices cannot be used as bridges.
This containment dramatically reduces ransomware spread.
Securing Remote and Vendor Access to Devices
Vendor and biomedical access is unavoidable, but dangerous.
Stealth networking secures it by:
- Eliminating VPN-based access
Vendors do not join internal networks. - Enforcing identity-verified, session-based access
Access exists only when approved. - Scoping access to specific devices
Vendors cannot explore the environment. - Providing full session auditability
Every action is traceable.
Access becomes controlled instead of persistent.
Why Stealth Networking Is Ideal for Legacy Devices
Medical devices cannot be modernized quickly.
Stealth networking works because it:
- Requires no agents on devices
No software changes are needed. - Does not rely on patching or hardening
Risk is reduced externally. - Respects regulatory constraints
Device integrity remains unchanged. - Protects devices without interfering with operation
Clinical workflows are preserved.
This makes it practical for real healthcare environments.
HIPAA Alignment Through Device Invisibility
HIPAA expects healthcare organizations to minimize exposure and control access intentionally.
Stealth networking supports this by:
- Reducing unnecessary access to PHI-adjacent systems
Devices are reachable only when needed. - Improving audit clarity
Access sessions are logged and reviewable. - Limiting breach scope
Fewer systems are exposed during incidents.
HIPAA compliance improves when devices are unreachable by default.
How Stealth Networking Reduces Ransomware Impact
Ransomware thrives on visibility and reach.
Stealth networking disrupts both by:
- Preventing device discovery
Attackers cannot find targets. - Blocking lateral spread
Compromised systems cannot pivot. - Protecting availability-critical devices
Downtime risk is reduced. - Supporting rapid containment
Access paths can be shut down instantly.
Containment replaces recovery as the strategy.
How Mindcore Technologies Secures Medical Devices with Stealth Networking
Mindcore secures medical devices by:
- Identifying device exposure and access paths
Understanding where visibility exists today. - Removing network trust from device access
Devices are hidden by default. - Implementing identity-driven, session-based connectivity
Access is deliberate and temporary. - Securing vendor and remote workflows
Without VPNs or standing access. - Centralizing visibility and audit readiness
Security and compliance teams gain clarity.
The objective is protecting devices without disrupting care delivery.
A Simple Medical Device Security Reality Check
Your medical devices remain high-risk if:
- Devices are discoverable on the network
- VPN users can reach device subnets
- Vendor access is persistent
- Devices can communicate broadly
- Security relies on patching alone
These are architectural risks, not device failures.
Final Takeaway
Medical devices do not need more security software. They need less visibility. Stealth networking secures devices by removing reachability, eliminating lateral movement, and enforcing access only when explicitly required.
For healthcare organizations balancing patient safety, uptime, and compliance, stealth networking is the most effective way to protect devices that cannot protect themselves.