Most healthcare breaches do not start deep inside the environment. They start at the front door, the place where users, clinicians, vendors, and partners first request access. The problem is that in many healthcare organizations, that “front door” is still a VPN, a flat network, or a legacy login page that grants far more access than intended.
A secure digital front door is not a login screen. It is an access architecture that decides, with precision, who gets in, what they can reach, and how long access exists.
At Mindcore Technologies, healthcare security assessments consistently show that organizations with a defined digital front door experience fewer large-scale incidents, faster containment, and significantly lower HIPAA exposure than those relying on traditional network entry points.
What a “Digital Front Door” Really Means in Healthcare
A digital front door is the single, controlled entry point for all access to healthcare systems, regardless of user location or role.
In a modern healthcare environment, it governs access for:
- Clinicians and care teams
Accessing EHR, imaging, and clinical applications. - Administrative and billing staff
Working with PHI-adjacent systems and financial data. - Remote and hybrid employees
Connecting from homes, clinics, and partner sites. - Vendors and third parties
Supporting applications, devices, and infrastructure.
If these users enter through different mechanisms, security fragments immediately.
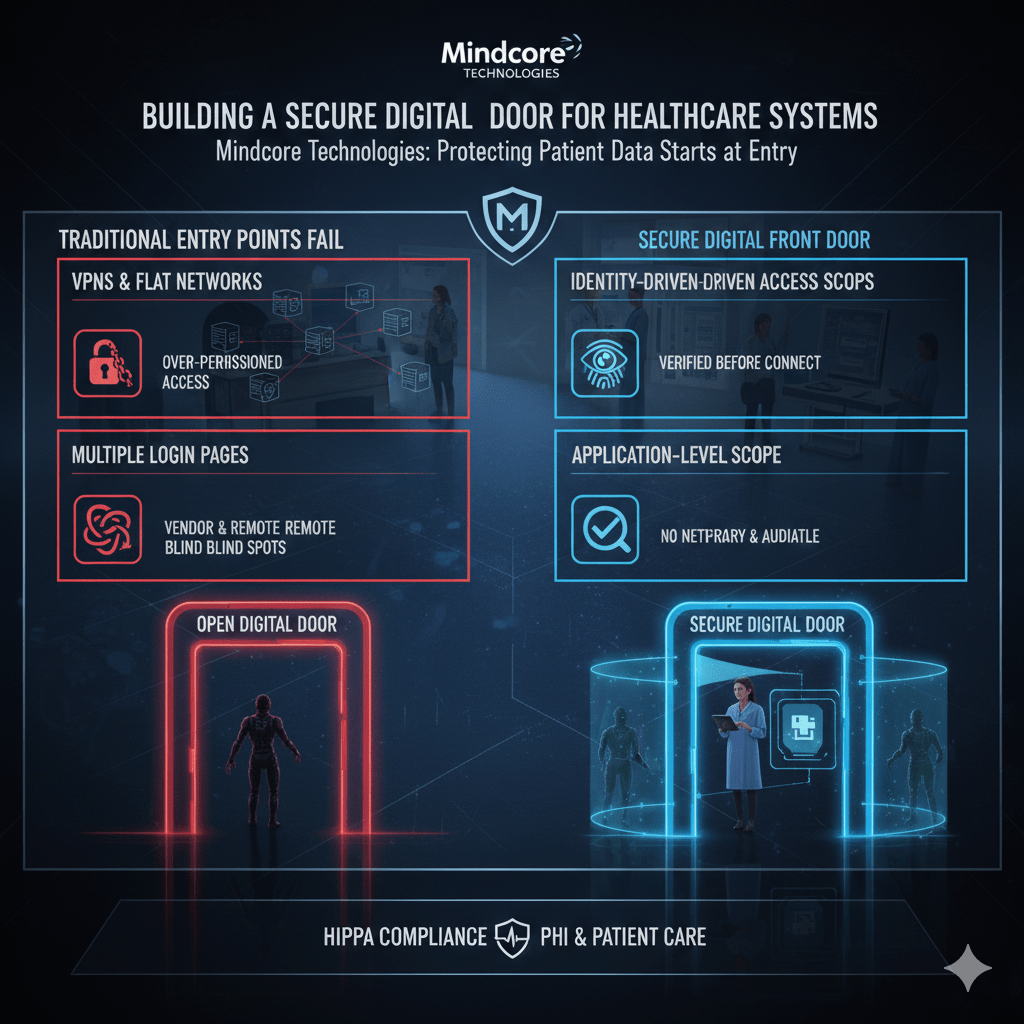
Why Traditional Healthcare “Front Doors” Fail
Most healthcare organizations never intentionally designed a front door. It evolved.
Common failures include:
- VPNs acting as universal entry points
One login provides internal network visibility. - Network-based trust models
Being “inside” equals access. - Multiple, inconsistent access paths
Different tools for different users create blind spots. - Static permissions that never expire
Temporary access becomes permanent exposure.
These approaches prioritize connectivity over control.
How Attackers Exploit Weak Front Doors
Attackers focus on entry points because they are efficient.
They exploit weak front doors by:
- Stealing credentials through phishing or infostealers
Valid logins bypass perimeter defenses. - Abusing VPN and remote access portals
Network trust is inherited immediately. - Leveraging third-party access paths
Vendors often have broader access than internal staff. - Blending into normal login activity
Detection tools struggle to distinguish abuse.
Once inside, the environment does the rest of the work for them.
What a Secure Digital Front Door Must Enforce
A secure digital front door enforces access discipline before any connection is established.
It must ensure:
- Identity is verified before access exists
Not after a network connection is made. - Access is scoped to specific applications
Users never receive network visibility. - Trust is temporary and session-based
Access expires automatically. - All access is centrally visible and auditable
No blind spots or exceptions.
Anything less is an unlocked door.
Replacing Network Entry with Application-Level Access
The most important shift is removing the network from the entry process.
A secure digital front door delivers:
- Application-level access only
Users connect to systems, not subnets. - No internal IP exposure
Infrastructure remains invisible. - No lateral movement paths
One application does not lead to another. - Consistent behavior for all users
Internal, remote, and vendor access work the same way.
This alone collapses many common attack paths.
Containing PHI at the Point of Entry
PHI exposure often begins the moment access is granted.
A secure digital front door protects PHI by:
- Keeping PHI inside controlled environments
Data does not land on endpoints. - Restricting copy, download, and export actions
Data movement is deliberate and logged. - Reducing dependence on endpoint security posture
Protection does not rely on perfect devices. - Preventing shadow IT access paths
All access flows through the same control plane.
PHI protection starts before the first click.
Eliminating VPN Risk at the Front Door
VPNs are one of the weakest healthcare entry mechanisms.
A secure digital front door eliminates VPN risk by:
- Removing network-level access entirely
Users never “join” the environment. - Reducing credential blast radius
Compromised accounts affect one session, not the network. - Eliminating appliance vulnerabilities and patch pressure
No exposed VPN infrastructure. - Simplifying access for clinicians and staff
Fewer connection failures and support tickets.
The front door becomes smaller, stronger, and easier to defend.
Securing Third-Party Access at the Entry Point
Third-party access should never bypass the front door.
A secure digital front door enforces vendor discipline by:
- Assigning unique identities to every vendor user
No shared accounts. - Scoping access to exact systems or devices
No browsing or exploration. - Enforcing time-bound access automatically
Access expires without manual cleanup. - Logging every session centrally
Activity is always auditable.
Vendor enablement no longer means inherited risk.
Improving Ransomware Defense Before Entry
Ransomware prevention starts before attackers move laterally.
A secure digital front door reduces ransomware impact by:
- Blocking internal reconnaissance
Attackers cannot see what to encrypt. - Preventing lateral movement from compromised accounts
Access is isolated per session. - Protecting backup and infrastructure systems
Critical systems are unreachable. - Allowing instant access termination
Sessions can be revoked without shutdowns.
Ransomware loses speed, scale, and leverage.
Supporting HIPAA Compliance by Design
HIPAA expects controlled, minimum necessary access.
A secure digital front door supports this by:
- Enforcing minimum necessary access automatically
Permissions are narrow and role-aligned. - Providing clear identity-to-access mapping
Auditors see who accessed what and why. - Reducing breach scope
Fewer systems and records are involved. - Making audit readiness continuous
Evidence exists without reconstruction.
Compliance improves when entry is controlled.
How Mindcore Technologies Designs Secure Digital Front Doors for Healthcare
Mindcore helps healthcare organizations build secure digital front doors by:
- Identifying all existing access entry points
Revealing hidden and inconsistent paths. - Replacing VPN and network-based entry models
Removing inherited trust. - Implementing identity-driven, application-level access
Access is precise and temporary. - Containing PHI inside secure workspaces
Data protection is structural. - Centralizing visibility and audit readiness
Security and compliance teams share clarity.
The objective is one front door, built to withstand modern threats.
A Simple Digital Front Door Reality Check
Your healthcare front door is still weak if:
- VPNs are the primary entry method
- Users gain network visibility after login
- Vendor access bypasses standard controls
- Access permissions rarely expire
- Audit evidence is manual
These are entry-point failures, not user errors.
Final Takeaway
Healthcare security does not begin with firewalls or monitoring tools. It begins at the digital front door.
Organizations that build a secure, identity-driven front door control access before risk enters the environment. They reduce ransomware impact, protect PHI by design, and simplify compliance across distributed teams. Organizations that do not remain exposed at the very place attackers target first.