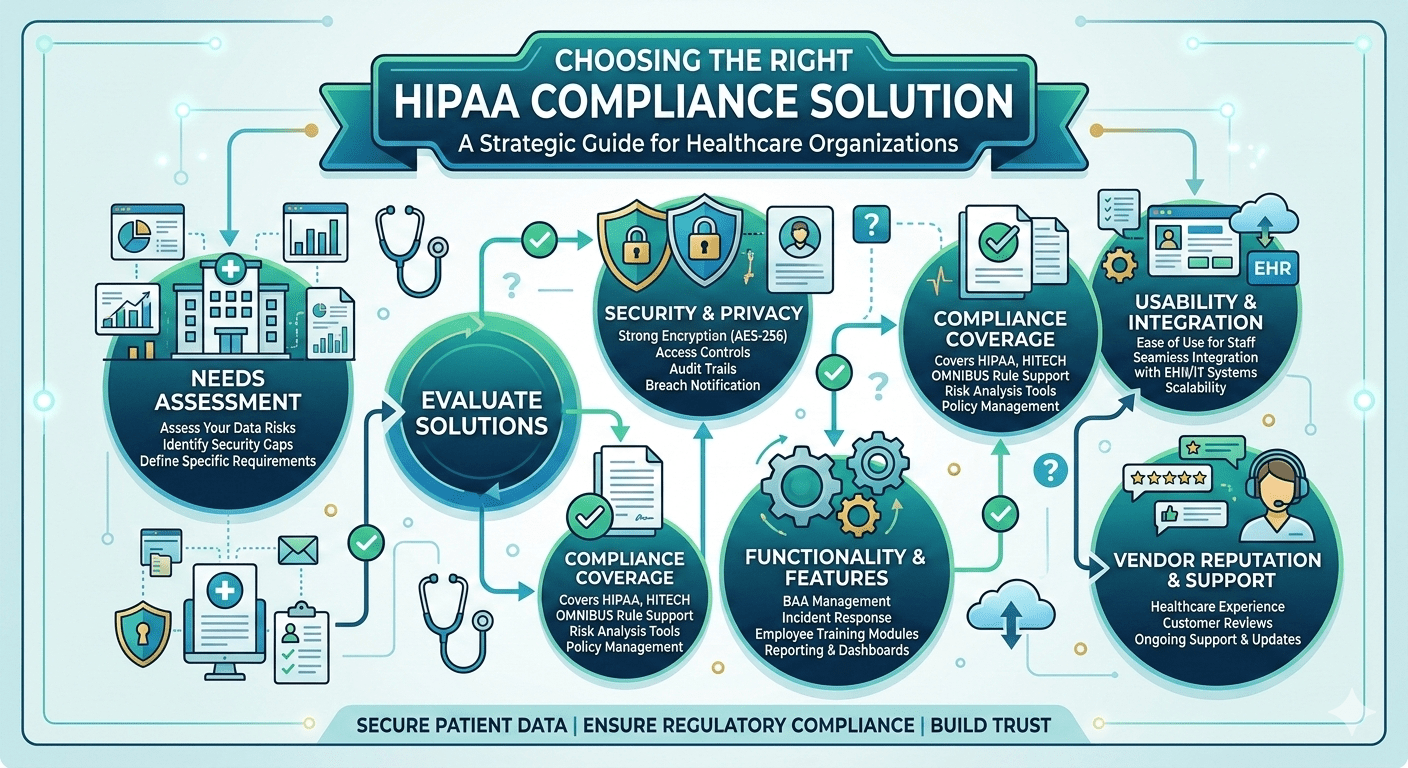
Healthcare organizations evaluating a HIPAA compliance solutions often focus on policy templates and surface-level controls. That approach fails at enterprise scale. The right solution must integrate security enforcement into infrastructure architecture, automate monitoring, and produce structured documentation continuously.
Selecting the correct platform directly impacts the sustainability of your broader Healthcare Compliance Solutions strategy.
Step 1: Conduct a Comprehensive Infrastructure Risk Assessment
Before evaluating vendors, understand your environment.
• Map all PHI systems
Identify servers, cloud platforms, endpoints, and storage repositories.
• Document data flows
Determine how PHI moves between departments and vendors.
• Assess authentication methods
Evaluate credential strength and MFA enforcement.
• Review encryption coverage
Confirm protection at rest and in transit.
Risk mapping aligns with enforcement standards detailed in The Ultimate HIPAA Compliance Checklist for Healthcare Executives.
Step 2: Evaluate Access Control Enforcement
HIPAA Compliance solutions ensure automated access controls, role-based permissions, and real-time monitoring to protect PHI and maintain regulatory compliance.
• Confirm RBAC deployment
Ensure permissions align with job roles.
• Verify automated access revocation
Remove privileges immediately upon role change.
• Assess phishing-resistant authentication
Reduce credential compromise risk.
• Review login monitoring capabilities
Detect abnormal access patterns.
Access control enforcement strengthens segmentation strategies outlined in Enterprise Healthcare Cybersecurity: A Comprehensive Guide for 500+ Employee Organizations.
Step 3: Validate Monitoring and Documentation Automation
Effective HIPAA Compliance solutions provide AI-driven anomaly detection, centralized log aggregation, and automated compliance dashboards, surpassing traditional manual logging practices.
• Deploy centralized SIEM integration
Aggregate logs across systems.
• Confirm AI-driven anomaly detection
Identify suspicious behavior in real time.
• Automate compliance dashboards
Provide executive visibility.
• Ensure timestamped log retention
Strengthen audit defensibility.
These monitoring requirements support the audit-readiness standards described in How Enterprise Healthcare Organizations Build Audit-Ready Infrastructure.
Step 4: Evaluate Vendor Governance Capabilities
HIPAA Compliance solutions integrate vendor governance, structured Business Associate Agreement tracking, and annual security reviews to minimize third-party compliance risks.
• Maintain structured Business Associate Agreement tracking
Ensure contractual compliance alignment.
• Limit vendor network access privileges
Reduce PHI exposure.
• Conduct annual vendor security reviews
Reassess risk posture.
Vendor oversight must integrate directly into compliance architecture.
Step 5: Compare Architectural Models
HIPAA Compliance solutions include architectural assessments, AI-driven containment, and segmented secure enclaves to prevent lateral movement and ensure PHI protection across healthcare networks.
• Traditional perimeter models
Rely on outer defenses but allow internal lateral movement.
• Segmented secure enclave models
Isolate sensitive systems.
• Reactive monitoring platforms
Detect after damage occurs.
• AI-driven containment solutions
Identify and isolate threats early.
Architectural evaluation is critical when comparing options such as those explored in ShieldHQ vs Traditional Healthcare Security: Comparing Enterprise Solutions.
Common Selection Mistakes
Organizations frequently undermine their compliance posture by choosing documentation tools without embedded enforcement capabilities, creating policies that are not technically validated. Many overlook vendor access exposure, failing to segment or continuously monitor third-party connectivity pathways. Segmentation requirements are often ignored, leaving flat network architectures that allow lateral movement across PHI environments. Executive reporting needs are underestimated, resulting in fragmented dashboards that do not provide board-level risk visibility. Additionally, selecting platforms without AI monitoring integration limits the organization’s ability to detect anomalous behavior in real time.
A HIPAA compliance solution must strengthen both cybersecurity enforcement and governance visibility simultaneously.
Frequently Asked Questions
What should healthcare organizations look for in a HIPAA compliance solution?
Healthcare organizations should look for automated access controls, centralized monitoring, AI-driven threat detection, audit-ready documentation, encryption enforcement, and strong governance capabilities. Effective HIPAA compliance solutions should integrate directly into infrastructure and operational workflows.
Why is automated monitoring important for HIPAA compliance?
Automated monitoring helps healthcare organizations detect suspicious activity, unauthorized access, and compliance risks in real time. Continuous visibility improves audit readiness and reduces the likelihood of undetected security incidents.
How does role-based access control support HIPAA compliance?
Role-based access control limits PHI access based on job responsibilities and operational requirements. This reduces unnecessary exposure to sensitive data and strengthens identity governance across healthcare environments.
Why is vendor governance important for HIPAA compliance?
Third-party vendors often have access to healthcare systems and PHI, creating additional compliance and cybersecurity risks. Structured vendor reviews, limited access permissions, and Business Associate Agreement management help reduce exposure.
What are common mistakes when selecting HIPAA compliance solutions?
Common mistakes include relying only on policy documentation tools, failing to segment networks, overlooking vendor access risks, neglecting executive reporting visibility, and choosing platforms without real-time monitoring capabilities.
HIPAA Compliance and Healthcare Security Expertise from Matt Rosenthal
Matt Rosenthal, CEO of Mindcore Technologies, has extensive experience helping healthcare organizations strengthen HIPAA compliance, cybersecurity resilience, and operational governance across complex healthcare environments. His expertise in identity governance, secure infrastructure architecture, centralized monitoring, AI-driven threat detection, and healthcare cybersecurity helps organizations protect PHI while improving audit readiness and operational visibility. His leadership focuses on implementing proactive healthcare security frameworks that align cybersecurity enforcement, governance oversight, and long-term compliance sustainability.