Traditional healthcare security models were built for centralized facilities, perimeter firewalls, and limited remote access. That environment no longer exists. Enterprise healthcare organizations now operate across multiple facilities, hybrid cloud environments, telehealth systems, and distributed workforces. The perimeter has dissolved. Lateral movement risk has increased. Credential compromise spreads faster than legacy systems can contain it.
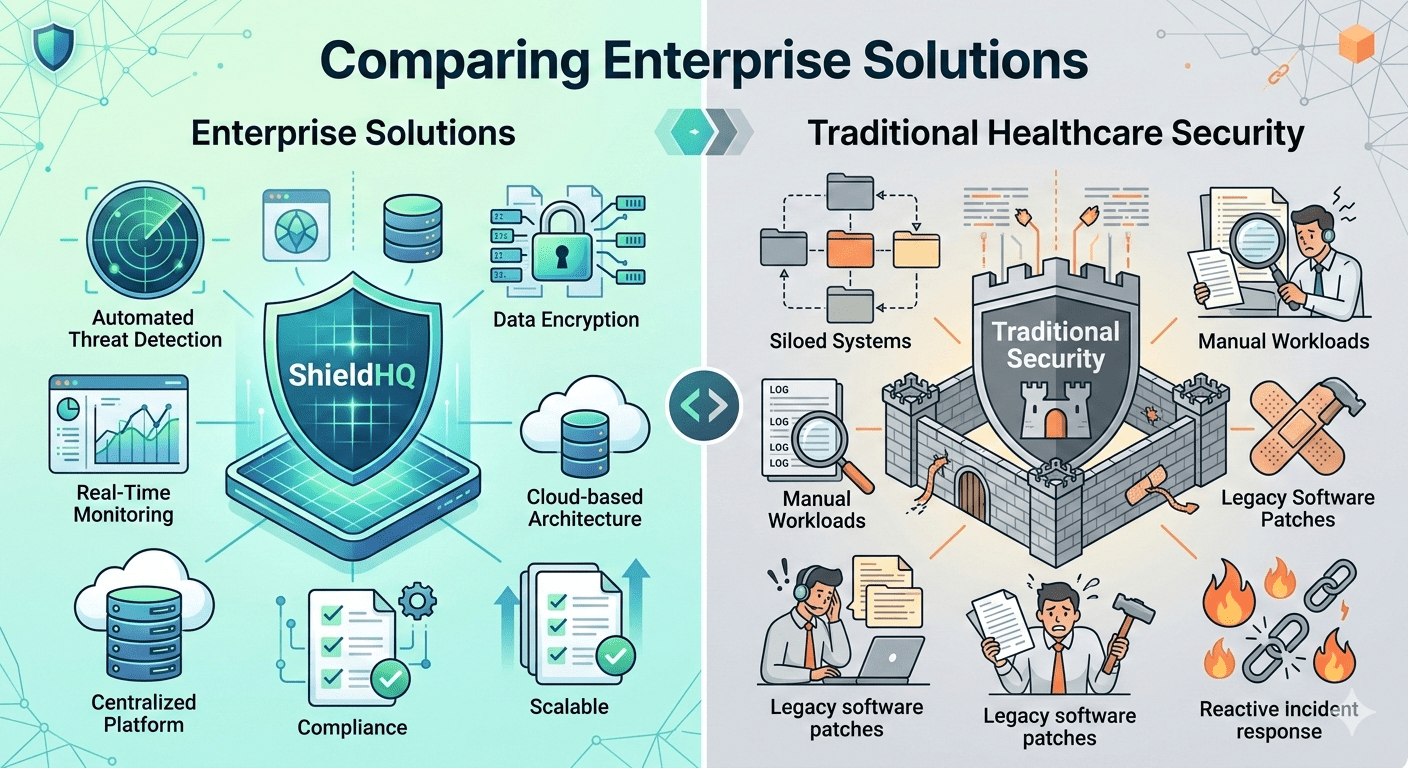
Modern containment architecture is required to support sustainable Healthcare Compliance Solutions, as outlined in The Complete Guide to Healthcare Compliance Solutions for Enterprise Organizations. When evaluating security strategies, leaders must understand the structural difference between perimeter-based models and segmented, zero-trust containment frameworks.
This comparison is not about tools. It is about architecture.
Traditional Healthcare Security Model
Traditional security approaches rely heavily on perimeter defenses.
• Firewall-based perimeter protection
Focuses on blocking external threats at network boundaries.
• Flat internal network architecture
Allows internal lateral movement once breached.
• VPN-based remote access
Extends internal network access to remote users.
• Reactive monitoring systems
Detect suspicious activity after compromise.
• Manual compliance reporting
Relies on spreadsheets and fragmented logs.
While these models were once sufficient, they struggle at enterprise scale.
Modern Segmented and Secure Enclave Architecture
Modern enterprise solutions prioritize containment.
• Network segmentation by function
Isolates clinical, administrative, and vendor systems.
• Zero-trust access enforcement
Validates every connection continuously.
• Secure enclave isolation for sensitive workloads
Limits breach blast radius.
• AI-driven anomaly detection systems
Identify suspicious behavior in real time.
• Centralized monitoring dashboards
Provide structured executive visibility.
Containment architecture significantly strengthens cybersecurity resilience, especially in large environments described in Enterprise Healthcare Cybersecurity: A Comprehensive Guide for 500+ Employee Organizations.
Containment vs Lateral Exposure
Flat networks increase systemic risk.
• Traditional flat networks
Allow compromised credentials to move across departments.
• Segmented architectures
Restrict access between defined zones.
• Unrestricted vendor access in legacy systems
Expands PHI exposure.
• Restricted vendor enclaves in modern models
Contain third-party risk.
Containment reduces regulatory fallout during investigations and aligns with governance expectations discussed in Healthcare Compliance Challenges Facing Executive Leaders Today.
Authentication and Identity Enforcement Comparison
Credential compromise remains the dominant breach vector.
Traditional approach:
• Password-based authentication
Vulnerable to phishing.
• Static access privileges
Encourage privilege creep.
Modern approach:
• Phishing-resistant MFA
Strengthens authentication integrity.
• Automated Role-Based Access Control (RBAC)
Dynamically adjusts permissions.
• Continuous login monitoring
Detects anomalous behavior.
These identity controls are operationalized in The Ultimate HIPAA Compliance Checklist for Healthcare Executives.
Monitoring and Compliance Reporting
Traditional systems often suffer from decentralized logging.
• Logs stored across multiple platforms
Complicate audit preparation.
• Manual aggregation of reports
Introduces errors and delays.
Modern containment-driven systems:
• Centralized SIEM integration
Consolidates all logs.
• AI-driven anomaly detection
Reduces manual oversight gaps.
• Automated compliance dashboards
Provide real-time reporting.
These monitoring capabilities strengthen audit-readiness standards outlined in How Enterprise Healthcare Organizations Build Audit-Ready Infrastructure.
Vendor Risk Comparison
Third-party exposure is a major enterprise risk.
Traditional model:
• Broad VPN access
Grants vendors wide internal visibility.
• Limited vendor activity monitoring
Reduces accountability.
Modern model:
• Segmented vendor enclaves
Restrict system access.
• Continuous vendor log monitoring
Detect unusual activity.
• Structured Business Associate Agreement tracking
Ensure contractual alignment.
Vendor governance integration also supports evaluation criteria in How to Choose the Right HIPAA Compliance Solution for Your Healthcare Organization.
Operational Impact and Compliance Sustainability
Traditional security often requires manual enforcement cycles.
Modern architecture:
• Automates monitoring and documentation
Reduces compliance fatigue.
• Improves incident containment speed
Limits breach severity.
• Enhances executive reporting visibility
Strengthens board confidence.
• Reduces systemic exposure
Improves regulatory defensibility.
Technical leadership must align architecture with governance, as emphasized in Healthcare Compliance Solutions: What CTOs and CIOs Need to Know.
Common Misconceptions
• “Firewalls are enough.”
Perimeter defenses do not prevent internal lateral movement.
• “VPN equals security.”
VPNs often expand exposure.
• “Compliance documentation equals security.”
Enforcement must be architectural.
• “Flat networks are manageable.”
Enterprise environments demand segmentation.
Strategic Takeaways
Containment architecture reduces systemic exposure by isolating sensitive workloads and limiting breach propagation across interconnected healthcare environments. Zero-trust access strengthens identity governance by continuously validating users, devices, and session context before granting access to PHI. AI-driven monitoring improves detection speed by identifying behavioral anomalies and abnormal data movement in real time. Centralized dashboards enhance executive visibility by consolidating compliance metrics, risk indicators, and control validation into structured reporting frameworks. Vendor segmentation limits third-party risk by restricting external connectivity to tightly controlled, monitored pathways.
Enterprise healthcare organizations must modernize infrastructure architecture to sustain long-term compliance integrity and cybersecurity resilience.