IT, security, and operations teams share a structural challenge: the volume of routine work that requires technical capability but not expert judgment consistently exceeds the capacity to handle it at the speed and consistency the business expects.
Ticket triage that should route in minutes waits for hours. Security alerts that need investigation queue behind higher-priority work. Operational workflows that should run automatically require manual triggering. The work is not hard. There is just too much of it for the available time.
Claude Agents are built for exactly that structure — autonomous execution of the routine, high-volume work that does not require expert judgment, with escalation to the right person at the right time when expert judgment is what the situation actually needs.
Overview
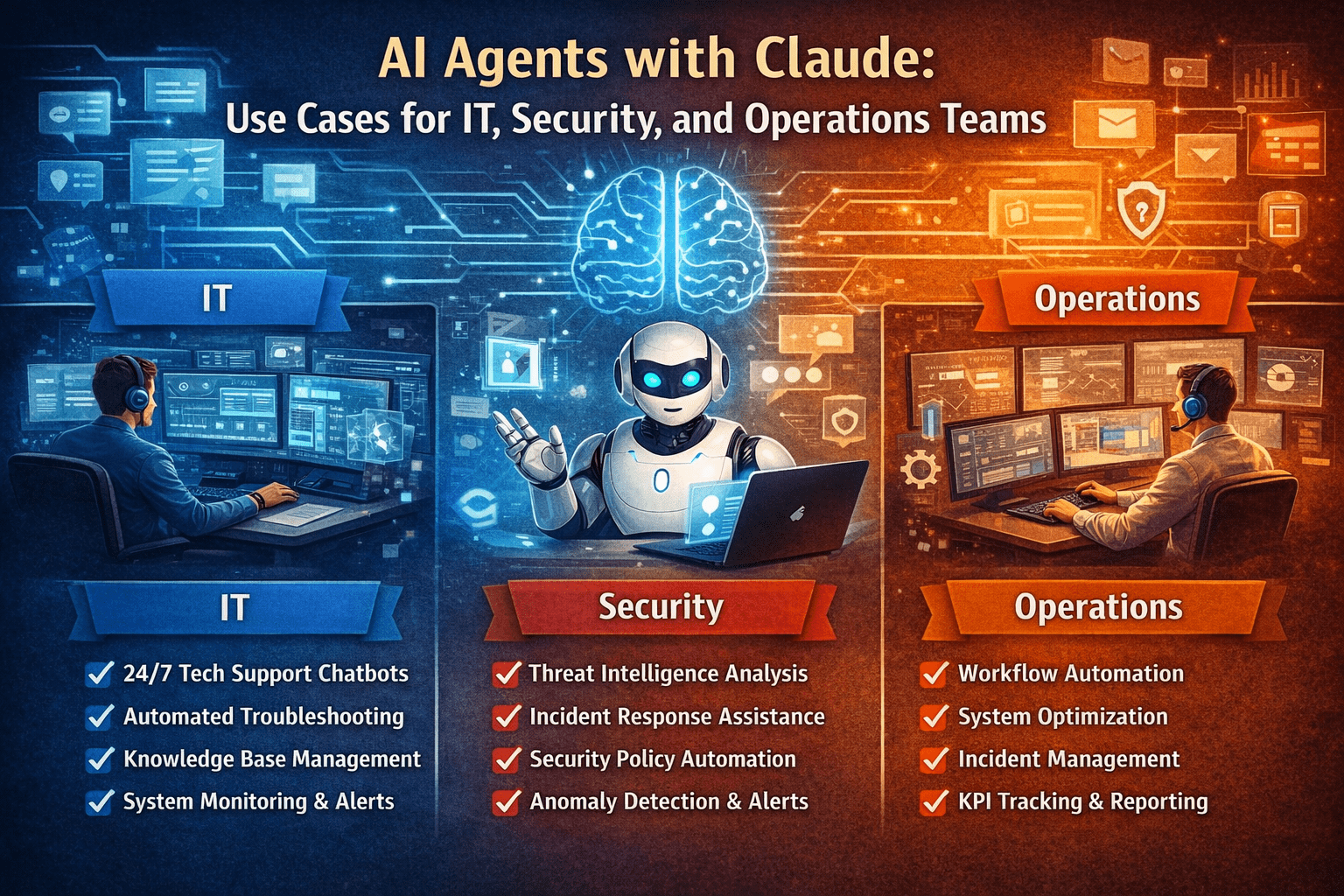
The highest-value Claude Agent use cases for IT, security, and operations teams are the workflows where volume exceeds available expert time, where the execution steps are consistent enough to be handled autonomously, and where correct routing to human experts for the minority of cases that require them is as important as autonomous execution of the majority. Agents handle the volume. Experts handle the judgment. Both are required. Only one scales with demand.
- IT service management agents handle the ticket lifecycle from intake through resolution for defined issue types
- Security operations agents handle alert triage, initial investigation, and escalation with context for issues requiring analyst review
- Operations agents handle workflow execution, monitoring, and exception routing for defined operational processes
- Each use case retains human accountability for the decisions that require it while automating everything that does not
- Governance architecture defines the boundary between autonomous execution and human escalation for each use case
The 5 Why’s
- Why are IT, security, and operations teams the highest-priority agent deployment targets? These teams operate under the highest ratio of routine, high-volume work to available expert time. The automation opportunity is large, the work characteristics are well-suited for agent execution, and the productivity gains from autonomous execution of routine work are immediately measurable.
- Why does the escalation quality matter as much as the autonomous execution quality? An agent that handles routine work well but escalates to human experts without context forces the expert to reconstruct the situation from scratch — consuming the time the agent was supposed to save. Escalation with full context — what the agent found, what it did, what it could not determine — makes expert time efficient rather than consuming it on reconstruction.
- Why does autonomous execution at high volume require governance architecture that is operationally specific, not general? “Use judgment” is not a governance instruction an agent can implement. Specific governance for IT, security, and operations agents defines: what issue types the agent resolves autonomously, what issue types it escalates immediately, what information it gathers before escalation, and what it never touches regardless of confidence level. That specificity is what makes autonomous operation trustworthy in technical environments.
- Why do security operations agents require more restrictive authorization design than IT or operational agents? Security operations involve the most consequential action types — blocking network access, isolating systems, revoking credentials. The authorization tier for those actions must be designed conservatively. Autonomous execution of routine alert triage is appropriate. Autonomous execution of network isolation actions is not, regardless of how clear the signal appears.
- Why does agent deployment for these teams produce compounding returns rather than one-time efficiency gains? Each workflow handled autonomously frees expert time for work that requires expertise. Expert time freed from routine work is available for threat hunting, proactive operations improvement, and complex problem-solving — work that makes the environment more resilient over time. The productivity gain compounds because it enables the higher-value work that the routine volume was previously crowding out.
IT Service Management Agent Use Cases
Tier 1 Ticket Handling
The majority of IT service requests — password resets, software access requests, common configuration issues, standard hardware requests — follow defined resolution paths that do not require expert judgment. An IT service management agent handles:
- Intake classification and priority assignment
- Knowledge base search and automated resolution attempt for defined issue types
- Resolution execution for access requests, password resets, and defined configuration issues
- Full-context escalation to Tier 2 for issues outside automated resolution scope
- Ticket closure with resolution documentation and user satisfaction follow-up
Change Management Support
Change management workflows require documentation completeness, approval routing, and implementation coordination that is structured enough for agent handling:
- Change request completeness verification against defined documentation requirements
- Approval routing to the correct stakeholder tier based on change type and risk classification
- Implementation window scheduling against defined change freeze and risk windows
- Post-implementation verification checklist generation and follow-up routing
Security Operations Agent Use Cases
Alert Triage and Initial Investigation
Security operations teams receive high volumes of alerts, the majority of which are low-severity, low-confidence signals that require initial triage before analyst review. A security operations agent handles:
- Alert intake and severity/confidence classification
- Initial investigation — log retrieval, asset context lookup, threat intelligence enrichment
- Correlation with recent alerts to identify patterns
- Low-confidence and low-severity alert closure with investigation documentation
- High-confidence or high-severity alert escalation to analyst with full investigation context pre-assembled
Vulnerability Management Triage
Vulnerability scan outputs require prioritization against asset criticality, exploitability, and remediation capacity. A vulnerability management agent handles:
- Scan result ingestion and asset criticality cross-referencing
- Exploitability assessment against current threat intelligence
- Remediation priority scoring and assignment routing
- SLA tracking and escalation for overdue remediations
Operations Agent Use Cases
Operational Workflow Monitoring and Response
Defined operational workflows require monitoring for exception conditions and response when exceptions occur. An operations agent handles:
- Continuous monitoring of defined operational metrics and workflow states
- Exception detection against defined threshold and condition criteria
- Automated response for defined exception types within authorized scope
- Escalation with context for exceptions outside automated response scope
- Operational reporting generation on defined schedules
Onboarding and Offboarding Workflow Execution
Employee onboarding and offboarding involve multi-system, multi-step workflows that are well-defined but time-consuming to execute manually:
- System access provisioning against role-based access matrices
- Equipment procurement and configuration request generation
- Training enrollment and compliance requirement assignment
- Offboarding access revocation across connected systems
- Equipment return and access termination verification
A Simple Use Case Prioritization Assessment
The highest-priority Claude Agent use cases for IT, security, and operations teams meet these criteria:
- The workflow has high volume relative to available expert time
- The majority of workflow instances follow defined resolution or handling paths
- The minority that require expert judgment can be identified with high confidence at intake
- Escalation context requirements can be defined — the agent knows what to deliver when escalating
- Action authorization can be defined specifically — not “sensitive actions require approval” but exactly which action types for which issue categories
Final Takeaway
IT, security, and operations teams are where Claude Agent deployment produces the most immediate and measurable return — because the gap between routine work volume and expert time is the most acute, the use cases are the most clearly defined, and the compounding effect of freeing expert time is the most operationally consequential.
The agents handle the volume. The experts handle the judgment. The governance architecture defines exactly where the boundary between them sits — and holds it there reliably, at scale, across every workflow instance that the agent encounters.
Deploy Claude Agents for IT, Security, and Operations With Mindcore Technologies
Mindcore Technologies works with IT, security, and operations teams to identify agent use cases, design the workflow and governance architecture, and deploy Claude Agents that handle routine operational volume — freeing expert time for the work that only experts can do.
Talk to Mindcore Technologies About Claude Agents for Your Operations Teams →
Contact our team to identify your highest-value agent deployment opportunities and build the architecture that makes them operational.