Zero Trust architecture assumes no entity — user, device, or system — is trusted by default. Every access request is verified. Every session is scoped. Every action is attributable. That model creates an obvious question when autonomous AI agents are introduced into the environment: how does an agent that takes actions across enterprise systems fit within an architecture that trusts nothing by default?
The answer is that agents fit into Zero Trust architecture the same way any other system entity does — through verified identity, explicit access authorization, scoped session-level trust, and continuous audit. What makes agents different is not that they require a different security model. It is that they require the existing security model to be applied rigorously, with specific attention to the agent-specific risk surface that autonomous action execution introduces.
Overview
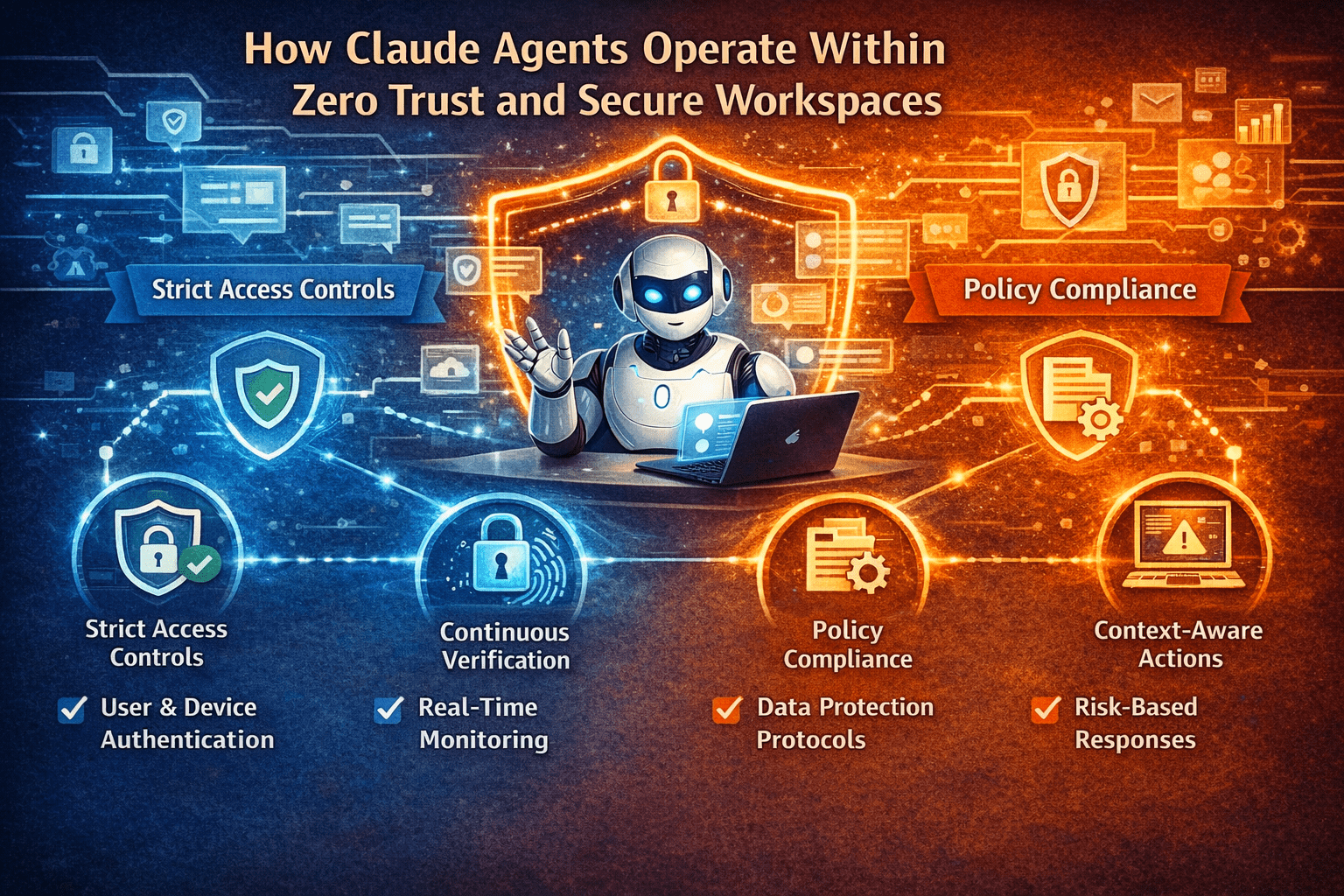
Claude Agents in Zero Trust and secure workspace environments operate under the same principles that govern all other access in those environments — verified identity, least-privilege access, session-scoped authorization, and complete auditability. The agent-specific design considerations are extensions of those principles, not exceptions to them: agent identities are explicitly provisioned and governed, agent access is scoped to the workflows they execute, agent sessions are bounded and auditable, and agent actions are subject to authorization controls that match the risk level of each action type.
- Agent identity is an explicit provisioned identity with defined access scope — not inherited from a user session
- Least-privilege access for agents is scoped to the specific systems and data the defined workflows require
- Session-scoped authorization means agent access does not persist beyond the session that authorized it
- Action authorization tiers align agent autonomy with Zero Trust’s continuous verification principle
- Secure workspaces provide the execution environment that keeps agent data access within defined boundaries
The 5 Why’s
- Why does Zero Trust architecture require agents to have explicit provisioned identities rather than borrowing user credentials? An agent that operates under a user’s credentials inherits all of that user’s access — including access beyond what the agent’s specific workflows require. Explicit agent identities scoped to minimum necessary access apply the Zero Trust principle correctly — trust is granted to what the agent needs, not to the user it is acting on behalf of.
- Why does least-privilege access for agents require workflow-specific scoping rather than role-based scoping? Role-based access grants all the permissions associated with a role. An agent handling one workflow within a role’s scope does not need all the permissions that role carries for other workflows. Workflow-specific scoping grants exactly the access the agent’s defined workflows require — no more. That is the correct application of least-privilege in agent access design.
- Why do session-scoped access grants align agent operations with Zero Trust better than standing permissions? Zero Trust requires that access grants be continuously validated rather than standing indefinitely. Session-scoped access grants for agent operations — issued for a specific workflow execution and expiring when the session ends — implement that principle correctly. Standing agent permissions that persist regardless of active sessions create the standing trust assumptions that Zero Trust architecture is designed to eliminate.
- Why do secure workspaces provide the right execution environment for agents that process sensitive data? Secure workspaces enforce that data accessed during agent execution stays within the workspace boundary — it does not reach uncontrolled endpoints, is not cached outside the controlled environment, and generates audit trails for every data interaction. For agents that retrieve sensitive records from enterprise systems, the secure workspace is the boundary that prevents that data from spreading beyond the workflow that required it.
- Why is auditability a Zero Trust requirement for agent operations, not just a governance best practice? Zero Trust’s continuous verification principle requires that every access event and every action is verifiable after the fact. Agent operations that produce incomplete or inconsistent audit trails create unverifiable gaps in the Zero Trust posture — the same gaps that Zero Trust architecture was designed to eliminate from human access patterns.
Implementing Zero Trust Principles for Claude Agents
Identity and Authentication
- Provisioned agent identities — each agent deployment has a dedicated identity in the enterprise identity provider, distinct from user identities and from other agent deployments
- Short-lived credentials — agent authentication uses short-lived tokens rather than long-lived API keys; credential lifetime is bounded to the session or workflow execution duration
- Multi-factor authentication for agent provisioning — the human who provisions agent identities and access scope requires multi-factor authentication; the provisioning event is logged as a high-privilege action
- Identity governance inclusion — agent identities are included in the enterprise identity governance process — reviewed, recertified, and deprovisioned on the same lifecycle as user identities
Least-Privilege Access Design
- Workflow access mapping — every data access requirement of every defined workflow is documented before agent access is provisioned
- Access scope provisioning — agent access is provisioned against the documented workflow access map — no more, no less
- Read/write separation — read access and write access are provisioned separately; agents that need to read data for workflow context do not inherit write permissions unless a specific write action is also required
- Access review triggers — workflow changes trigger access scope review; agent access that no longer maps to current workflow requirements is revoked
Session Governance
- Session initiation logging — every agent session initiation is logged with the triggering event, initiating identity, and intended workflow scope
- Session time limits — agent sessions are bounded by maximum duration limits; sessions that exceed defined duration limits are terminated and logged as anomalies
- Session state auditing — the state of every agent session — what was accessed, what was done, what decisions were made — is logged continuously, not just at session start and end
- Session termination verification — session termination is verified, not assumed; resources held by the session are confirmed released
Action Authorization in Zero Trust Context
The Zero Trust principle of continuous verification applies to agent actions through tiered authorization:
- Tier 1 actions are continuously authorized through the session credential — no additional verification required per action
- Tier 2 actions trigger re-verification — the session credential is re-validated before the action executes
- Tier 3 actions require out-of-band human approval — the agent queues the action and does not execute until approval is received through a separate authorization channel
- Tier 4 actions are outside agent authorization scope — any attempt triggers session termination and security team alert
Secure Workspace Integration for Agents
Secure workspaces provide the execution boundary that Zero Trust requires for data access within agent sessions:
- Sensitive data retrieved by agents during workflow execution remains within the workspace
- Agent outputs that contain sensitive data are delivered only to authorized destinations
- Workspace session termination clears agent context — sensitive data does not persist between sessions
- Every data interaction within the workspace generates an audit record
Final Takeaway
Claude Agents do not require a different security model than Zero Trust. They require Zero Trust applied correctly to an entity that takes actions autonomously — with explicit identity provisioning, workflow-specific least-privilege access, session-scoped authorization, and continuous auditability designed as the conditions for agent operation rather than as controls applied afterward.
The organizations that build Zero Trust-aligned agent architecture from the start deploy agents that are defensible in regulated environments, auditable in compliance examinations, and trustworthy in the operational contexts where autonomous action execution requires that standard.
Deploy Zero Trust-Aligned Claude Agents With Mindcore Technologies
Mindcore Technologies works with enterprise security and IT teams to design and deploy Claude Agents within Zero Trust architecture — identity provisioning, least-privilege access design, session governance, action authorization frameworks, and secure workspace integration that align autonomous agent operation with enterprise security standards.
Talk to Mindcore Technologies About Zero Trust-Aligned Claude Agent Deployment →
Contact our team to assess your Zero Trust architecture’s readiness for agent deployment and design the security controls that make it complete.