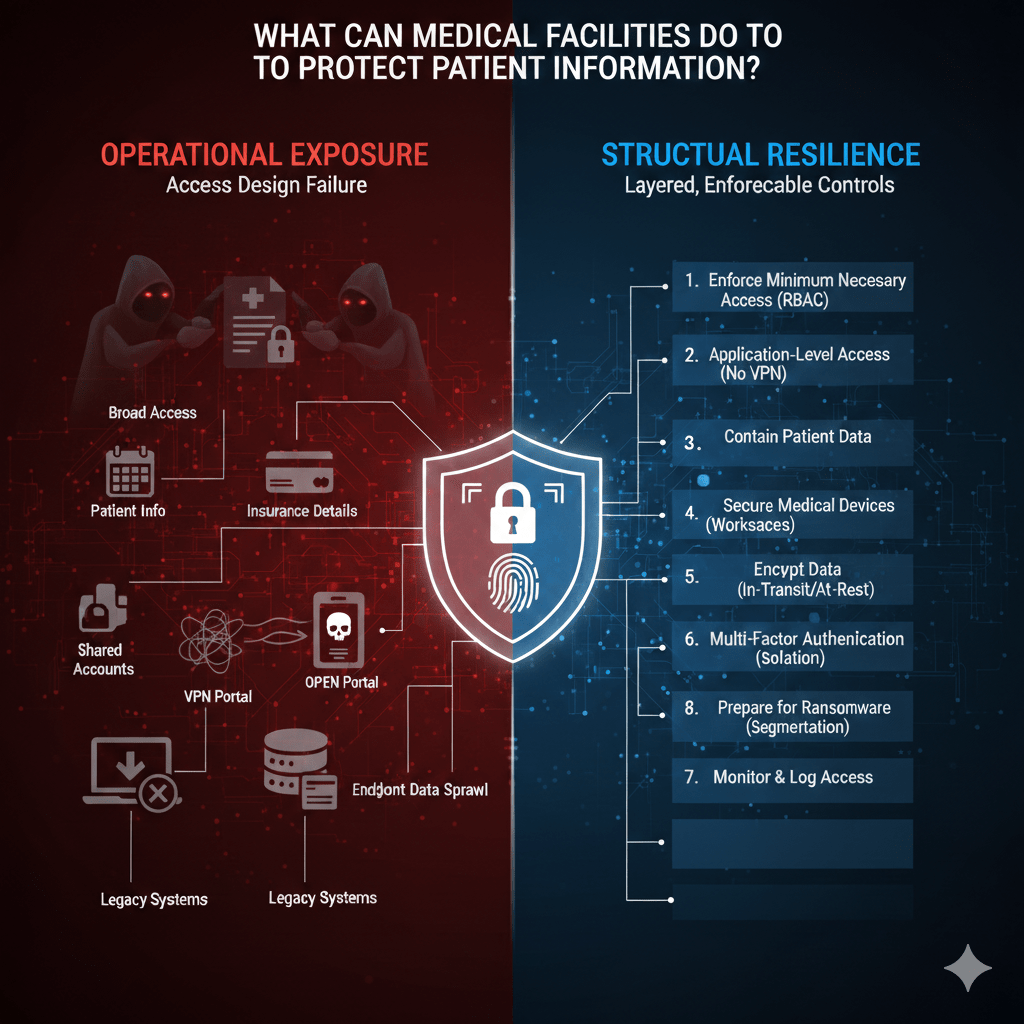
Most medical facilities do not lose patient information because they lack tools. They lose it because access is too broad, trust is assumed, and architecture was never designed for modern attack patterns.
Patient information is targeted because it carries financial value, regulatory consequences, and operational leverage. Ransomware groups know that hospitals cannot tolerate downtime. That reality must shape how protection is built.
At Mindcore Technologies, healthcare assessments consistently show that protecting patient information is less about buying another security platform and more about correcting structural exposure.
1. Enforce Minimum Necessary Access Everywhere
The most common patient data failure is excessive access.
Medical facilities must:
- Implement strict role-based access control (RBAC)
Users should only access the specific patient data required for their role, not entire departments or databases. - Eliminate shared accounts
Every user must have a unique identity to preserve accountability and audit traceability. - Review access quarterly
Permissions drift over time, especially with staff changes and workflow shifts. - Automatically expire temporary access
Contractors and temporary staff should never retain long-term privileges.
If everyone can see everything, patient privacy is already compromised.
2. Replace VPN-Based Access with Application-Level Control
VPNs extend internal network visibility and amplify breach scope.
Medical facilities should:
- Remove network-level remote access
Users should access applications, not internal networks. - Adopt identity-driven, session-based access models
Access exists only during active, verified sessions. - Limit third-party access to specific systems only
Vendors should never browse the environment. - Terminate sessions instantly during incidents
Containment must not require full system shutdown.
Reducing internal visibility dramatically limits breach impact.
3. Contain Patient Data Within Controlled Environments
Patient information should not live on endpoints.
Facilities must:
- Prevent unnecessary downloads of PHI
Restrict export capabilities to controlled workflows. - Use secure workspace models for remote access
Keeping data inside protected environments rather than local devices. - Segment EHR, billing, and backup systems
Preventing lateral movement between critical systems. - Disable legacy protocols that enable file sprawl
Many older configurations still allow broad internal access.
Containment reduces exposure even if credentials are stolen.
4. Secure Medical Devices and Legacy Systems
Medical devices are frequently overlooked but often vulnerable.
Facilities should:
- Isolate medical devices from general networks
Preventing compromise from spreading across systems. - Restrict device communication paths
Devices should only communicate with required systems. - Avoid exposing device management interfaces externally
Administrative ports must never be internet-facing. - Monitor anomalous device behavior
Unexpected traffic patterns can indicate compromise.
Many ransomware campaigns spread through poorly segmented device networks.
5. Encrypt Data in Transit and at Rest
Encryption remains foundational.
Medical facilities must ensure:
- Encrypted communication channels for all PHI transmission
Including telehealth, email gateways, and API integrations. - Encrypted storage systems and backups
Backup repositories are common ransomware targets. - Secure configuration of cloud services
Misconfigured storage buckets frequently expose patient records.
Encryption is not optional, but it must be paired with access discipline.
6. Strengthen Identity and Authentication Controls
Compromised credentials remain the dominant attack vector.
Facilities should:
- Enforce multi-factor authentication (MFA) everywhere
Especially for remote and privileged access. - Implement conditional access policies
Evaluating context such as device posture and location. - Limit administrative privileges aggressively
Reducing the number of users with elevated access. - Monitor authentication anomalies
Repeated login attempts or unusual timing patterns should trigger review.
Identity is the control plane of modern healthcare security.
7. Monitor, Log, and Review Patient Data Access
Audit readiness depends on visibility.
Medical facilities must:
- Log every PHI access event
Including user identity, timestamp, and system accessed. - Retain logs securely and centrally
Fragmented logs undermine investigations. - Review logs regularly for anomalies
Large exports, off-hours access, or unusual access patterns require scrutiny. - Test audit retrieval processes periodically
Evidence must be accessible during regulatory review.
If you cannot trace access, you cannot defend compliance.
8. Prepare for Ransomware Before It Happens
Ransomware planning must be architectural, not reactive.
Facilities should:
- Segment backups from primary systems
Backup deletion is a common ransomware tactic. - Test recovery procedures under pressure scenarios
Downtime tolerance must be realistic. - Design for breach containment, not just detection
Assume compromise and limit spread automatically. - Avoid over-reliance on endpoint antivirus alone
Ransomware frequently bypasses signature-based defenses.
Preparation determines survivability.
9. Control Third-Party and Vendor Risk
Vendor access expands exposure significantly.
Medical facilities should:
- Assign unique vendor identities
No shared service accounts. - Scope vendor access narrowly
Vendors should reach only the systems they support. - Enforce time-bound vendor access windows
Access should expire automatically. - Audit vendor activity regularly
Third-party interactions must be defensible.
Third-party convenience cannot override patient protection.
10. Align Architecture With HIPAA Requirements
HIPAA requires administrative, physical, and technical safeguards. For IT teams, this translates to:
- Enforced minimum necessary access
- Transmission security
- Audit controls
- Integrity protection
- Incident response readiness
Compliance must be built into the access model, not layered afterward.
How Mindcore Technologies Helps Medical Facilities Protect Patient Information
Mindcore supports healthcare organizations by:
- Conducting technical risk assessments focused on PHI exposure
Identifying architectural weaknesses. - Redesigning access models to enforce least privilege structurally
Removing implicit trust. - Implementing secure workspace and stealth networking strategies
Reducing attack surface dramatically. - Strengthening vendor access controls
Preventing inherited risk. - Centralizing visibility and audit readiness
Making patient data interaction defensible.
The focus is reducing breach impact before incidents occur.
A Practical Patient Data Risk Check
Your medical facility is at elevated risk if:
- VPNs provide broad internal access
- PHI is stored on unmanaged endpoints
- Access permissions rarely expire
- Vendor access is persistent and broad
- Audit logs require manual reconstruction
- Ransomware containment requires shutting down operations
These are architectural exposure points.
Final Takeaway
Medical facilities protect patient information not through policies alone, but through disciplined access control, containment, segmentation, identity enforcement, and continuous visibility.
Organizations that redesign access around least privilege and structural containment significantly reduce breach scope, ransomware impact, and regulatory exposure. Those that rely solely on perimeter defenses and reactive monitoring remain vulnerable to the credential-based attacks that dominate healthcare today.